Security and Vulnerability Management Market by Component (Software and Services), Target, Deployment Mode (Cloud and On-premises), Organization Size (SMEs and Large Enterprises), Vertical, and Region - Global Forecast to 2026
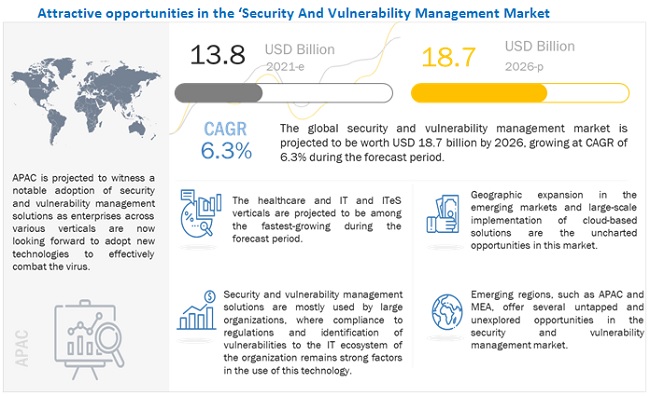
[305 Pages Report] The global Security and Vulnerability Management Market size is projected to grow from USD 13.8 billion in 2021 to USD 18.7 billion by 2026, at a Compound Annual Growth Rate (CAGR) of 6.3% during the forecast period. The major driving factors contributing to the high growth rate of the security and vulnerability management market include an increase in vulnerabilities across globe, high monetary losses due to the absence of security and vulnerability management solutions, stringent regulatory standard and data privacy compliances, surge in the adoption of IoT and cloud trends, and integration of advanced technologies such as AI and ML with security and vulnerability management solutions.
To know about the assumptions considered for the study, Request for Free Sample Report
COVID-19 Impact
The COVID-19 pandemic has affected every segment of society, including individuals and businesses. The internet ecosystem has been playing a pivotal role all over the globe. Due to the COVID-19 pandemic, the dependency on online businesses has increased significantly. BFSI, healthcare and life sciences, manufacturing, retail, transport and logistics, among others, are leveraging the internet to provide necessary services to consumers. Vendors have experienced an increased demand for a security and vulnerability management system. Amidst the COVID-19 pandemic crisis, various governments and regulatory authorities have mandated both public and private enterprises to embrace new practices of teleworking and maintaining social distance. Since then, digital ways of doing business and usage of emails with home servers became the new business continuity plan (BCP) for various organizations. With the widespread use of mobile devices and internet penetration across the globe, individuals are progressively inclined towards the use of security and vulnerability management. These changing trends and distributed IT environments have made organizations susceptible to cyber-attacks and data breaches, further fueling the demand for security and vulnerability management solutions.
Market Dynamics
Driver: High monetary losses and loss of critical data due to the absence of vulnerability management solutions
Organizations increasingly adopt diverse technological developments such as enterprise mobility, virtualization, and cloud storage to boost business productivity. These progressions have helped organizations function efficiently and in real-time since the business data can be easily accessed on mobile devices from the cloud and virtual storage. However, this access to critical business information on mobile devices augments the data loss and theft risk. Vulnerability management solutions help organizations in detecting misconfigurations with regards to strong password policy, firewall port access, web server hardening, Windows Defender, and several other antivirus detection solutions, as well as administrative authorization privileges. Various organizations, while implementing a security strategy or deploying any security solution, pay a huge amount of money in case of a security lapse.
Due to the increasing cases of COVID-19, businesses are sending employees home to work remotely, and students are moving to online classes. As organizations rush to shift their businesses and classes online, cybercriminals are ramping up their tactics to take advantage of those who may have inadequate or naive security postures as a result. The pandemic was being used to trick users into opening malicious emails. Hence, to avoid the loss of confidential information communicated, security and vulnerability management is a safe choice for industries to choose. According to IBM, the average cost of a successful phishing campaign globally costs approximately USD 3.86 million, while in the US alone, the cost of a phishing attack climbed to USD 7.9 million. Such financial implications urge organizations to deploy security and vulnerability management solutions to protect their secure environments.
Restraint: Security breaches due to internal vulnerabilities
Internal vulnerabilities include insider threats, careless workers, employees recruited by competitors for corrupting company data, disgruntled employees, and employees who deliberately use data for personal gains. Structured Query Language (SQL) injection, email phishing, and Man-in-The-Middle (MiTM) are the major attacks due to which cybercriminals accomplish financially motivated goals. Most often, internal vulnerabilities and breaches go undetected; companies do not even report these losses due to their reputation in the ecosystem as they perceive such cases as embarrassing incidents. According to Verizon, 48% of malicious email attachments are office files; 34% of data breaches involve internal actors, such as employees; and 94% of malware is delivered by emails.
According to a recent Endera survey, reviewed responses from 200 security executives, with an average of 1,000 employees stated that companies deal with at least three workforce-related incidents every week, which comprise frauds, cybersecurity risks, workplace violence, and device thefts or losses. Several key trends from this report also highlight the need for security executives to dig deeper and be more proactive. With security and vulnerability management in place, companies can test their networks, applications, and IoT devices. Internal vulnerabilities play a massive role in the execution of security breaches across organizations. According to Ekran System, the average cost incurred by enterprises due to internal vulnerabilities rose from USD 1.4 million in 2018 to USD 1.6 million in 2019.
Opportunity: Integration of advanced technologies with vulnerability management solutions for real-time risk-based security vulnerability prioritization and remediation
The infusion of AI and ML in vulnerability management supports IT experts with deep risk insights based on the most critical and legitimate vulnerabilities. The AI platform clubbed with the security and vulnerability management platform helps in quick remediation of vulnerabilities based on real-time and predictive threat intelligence assessment to minimize the occurrences of data breaches.
The VM solution vendors leverage the power of AI, ML, and threat analytical capabilities to provide end users with deep visibility into their IT infrastructures supported by real-time threat prioritization and remediation. The Qualys VMDR solution uses advanced ML, correlation, and threat intelligence analysis to automatically prioritize and remediate risky vulnerabilities across on-premises, cloud, containers, OT, and endpoint environments. Another VM enterprise solution, Skybox Security�s risk-based vulnerability management solution, uses context-aware prioritization with network modeling, attack simulation, and threat intelligence, highlighting the most critical vulnerabilities. In addition, Tenable�s solutions provide a 360-degree view of the risk attack surface through a single console with AI-derived risk and contextual information.
Challenge: High initial installation, maintenance, and deployment cost
The Qualys VMDR solutions are available for a free trial; enterprise VMDR starts from USD 6,368 (USD 199 per asset, minimum 32 assets). Tenable Nessus Pro (commercial) from USD 3,000/year. Tenable.sc pricing starts at around USD 13,000 for between 500-1,000 IP assets. Tenable.io pricing starts at USD 2,380 for 1 year per 65 assets. Rapid7 InsightVM is available for a free 30-day trial; licensing fee for InsightVM is USD 25/year for 250 assets and USD 19.56/year for 1,000 assets. The financial institutions hold extremely critical data, and these are major end users of vulnerability management solutions; also, they do not compromise on price. At the same time, other small and medium industries lack the financial resources to adopt costly security and vulnerability solutions. Among the top security and vulnerability management vendors, Rapid7�s solutions are available at the most affordable rate.
Based on vertical, the healthcare segment to grow at the highest CAGR during the forecast period
The healthcare segment is projected to witness the fastest growth rate of 7.6% during the forecast period. As data and identity breaches in the healthcare vertical are increasing, the need for a robust security system to detect risks, maintain logs of users accessing confidential data, and access control for the investigation of cyber threats is also required. This requirement is fulfilled with security and vulnerability management solutions. The healthcare industry comprises a global infrastructure that deals with continuous health-related data exchange. There has been an increase in the number of cyberattacks, such as ransomware and misinformation campaigns on healthcare organizations with electronic protected health information (ePHI), personally identifiable information (PII), and electronic health records (EHR) with the COVID-19 outbreak. Email phishing attacks have spiked due to COVID-19, more so, across the healthcare sector. Healthcare organizations face several challenges, such as maintaining the privacy of Electronic Health Records (EHRs) and meeting various compliances, set by HIPAA, which has helped the IT departments of the healthcare sector to upgrade and put manage security policies and procedures to PHI. With the adoption of technologies such as BYOD and centralized patient information, the vertical has become highly susceptible to cyber-attacks. The need to secure data retrieving process from clinical databases is expected to increase the deployment of security and vulnerability management solutions. Nowadays, security and vulnerability management as a service gaining momentum in healthcare industry as it is reliable and cost-efficient solution.

To know about the assumptions considered for the study, download the pdf brochure
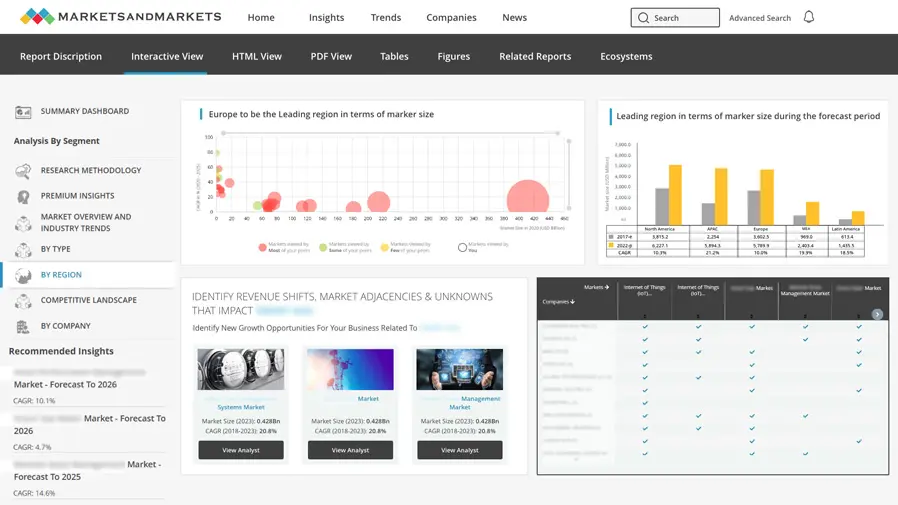
North America is expected to hold the largest market size during the forecast period
North America is estimated to account for the highest market share in the security and vulnerability management market. Early adoption of security and vulnerability management and the presence of several vendors that provide security and vulnerability management solutions are expected to drive market growth in the region. Businesses in this region are increasingly implementing security and vulnerability management solution for enabling data security, preventing cyber-attacks and commercial espionage, and ensuring security and privacy of data to facilitate business continuity.
Key Market Players
This research study outlines the market potential, market dynamics, and key and innovative vendors in the security and vulnerability management market include IBM (US), AT&T (US), Qualys (US), Rapid7 (US), Tenable (US), RSA Security (US), McAfee (US), Foreseeti (Sweden), F-Secure (Finland), Acunetix (US), Skybox Security (US), SecPod (India), Tripwire (US), Kenna Security (US), Check Point (US), Expanse (US), Digital Defense (US), Positive Technologies (Russia), Outpost24 (Sweden), Brinqa (US), NopSec (US), RiskIQ (US), RiskSense (US), Claroty (US), Holm Security (Sweden), Balbix (US), Intruder (UK), BreachLock (US), and Nucleus Security (US).
The study includes an in-depth competitive analysis of these key players in the security and vulnerability management market with their company profiles, recent developments, and key market strategies.
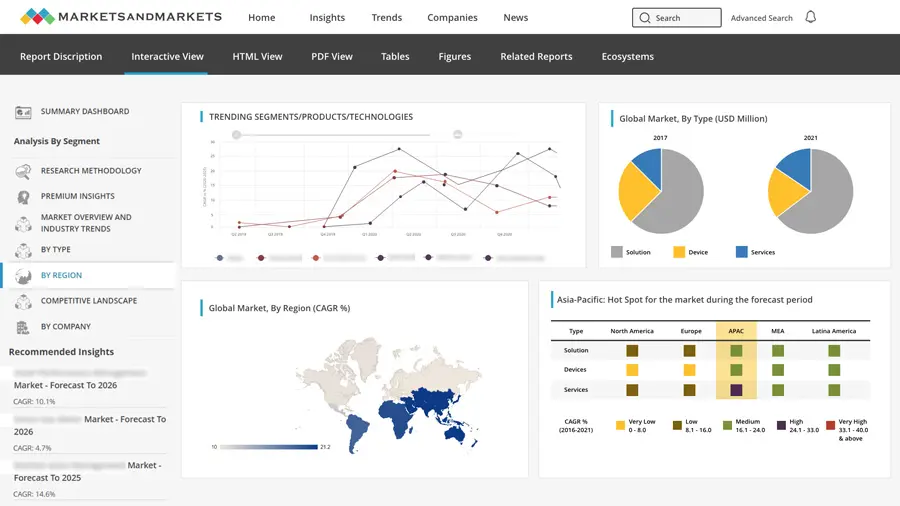
Get online access to the report on the World's First Market Intelligence Cloud
- Easy to Download Historical Data & Forecast Numbers
- Company Analysis Dashboard for high growth potential opportunities
- Research Analyst Access for customization & queries
- Competitor Analysis with Interactive dashboard
- Latest News, Updates & Trend analysis
Request Sample Scope of the Report
Get online access to the report on the World's First Market Intelligence Cloud
- Easy to Download Historical Data & Forecast Numbers
- Company Analysis Dashboard for high growth potential opportunities
- Research Analyst Access for customization & queries
- Competitor Analysis with Interactive dashboard
- Latest News, Updates & Trend analysis
|
Report Metrics |
Details |
|
Market size available for years |
2016�2026 |
|
Base year considered |
2020 |
|
Forecast period |
2021�2026 |
|
Forecast units |
Value (USD) |
|
Segments covered |
Component, Target, Deployment Mode, Organization Size, Vertical, and Regions. |
|
Geographies covered |
North America, Europe, APAC, Middle East and Africa (MEA), and Latin America. |
|
Major companies covered |
IBM (US), AT&T (US), Qualys (US), Rapid7 (US), Tenable (US), RSA Security (US), McAfee (US), Foreseeti (Sweden), F-Secure (Finland), Acunetix (US), Skybox Security (US), SecPod (India), Tripwire (US), Kenna Security (US), Check Point (US), Expanse (US), Digital Defense (US), Positive Technologies (Russia), Outpost24 (Sweden), Brinqa (US), NopSec (US), RiskIQ (US), RiskSense (US), Claroty (US), Holm Security (Sweden), Balbix (US), Intruder (UK), BreachLock (US), and Nucleus Security (US). |
This research report categorizes the security and vulnerability management to forecast revenues and analyze trends in each of the following submarkets:
Based on component:
- Software
- Services
Based on target:
- Content Management Systems Vulnerabilities
- IoT Vulnerabilities
- API Vulnerabilities
- Other Target Vulnerabilities
Based on deployment mode:
- Cloud
- On-Premises
Based on organization size:
- Large Enterprises
- SMEs
Based on the vertical:
- IT and ITeS
- BFSI
- Healthcare
- Retail
- Manufacturing
- Energy and Utility
- Other Verticals
Based on the region:
- North America
- United States (US)
- Canada
- Europe
- Germany
- Sweden
- Denmark
- Rest of Europe
- APAC
- Australia
- South Korea
- Rest of APAC
- Middle East and Africa (MEA)
- Middle East
- Africa
- Latin America
- Brazil
- Mexico
- Rest of Latin America
Recent Developments:
- In July 2021, Rapid7 acquired IntSights Cyber Intelligence, a pioneer in threat intelligence and proactive threat remediation, for approximately USD 335 million in cash. With IntSights� external threat intelligence capabilities, Rapid7 will be able to provide its customers with a unified view into threats, attack surface monitoring, actionable insights, and proactive threat mitigation.
- In March 2021, IBM expanded its suite of IBM Security Services for Cloud to help companies adopt a consistent security strategy across their hybrid cloud environments. IBM introduced enhancements in its services such as cloud native security services, CSPM, container security, and cloud security. The enhancements included the integration of its cloud security services with IBM Security X-Force Red vulnerability management, which would help in the identification, investigation, and prioritization of vulnerabilities within client environments.
- In February 2021, Qualys extended the power of Qualys VMDR to Android and iOS/iPadOS mobile devices. Qualys� all-in-one VMDR solution provides in-depth mobile device visibility, data security insights, vulnerability assessment, posture monitoring, and automated response for all iOS and Android devices and installed apps. Qualys VMDR for mobile provides comprehensive mobile device and app inventory, continuous vulnerability assessment, real-time misconfiguration monitoring, and built-in response and patch orchestration.
- In October 2020, McAfee launched MVISION XDR, the industry�s first proactive, data-aware, and open-extended detection and response platform. MVISION XDR improves SOC effectiveness with quick risk mitigation and delivers Total Cost of Ownership (TCO) for threat response with the inclusion of MVISION XDR�s proactive threat analytics.
- In December 2019, Tenable acquired Indegy, an industrial security start-up, for USD 78 million. The combination of Tenable and Indegy delivered the industry�s first unified and risk-based view of IT and OT security. Indegy's cybersecurity suite could be integrated with Tenable.sc, Tenable.io, and Tenable Lumin. Together, Tenable and Indegy delivered capabilities such as risk-based measurement by leveraging the power of Tenable Lumin; a unified view of IT and OT vulnerabilities; depth of intelligence into OT environments; IT and OT vulnerability assessment; and OT-specific process management.
- In July 2019, AT&T introduced managed threat detection and response services. The new service was based on the AlienVault Unified Security Management (USM) platform, which could be deployed more quickly and offered as cloud-hosted managed services.
Frequently Asked Questions (FAQ):
What is the projected market value of the global security and vulnerability management market?
The global security and vulnerability management market size is projected to grow from USD 13.8 billion in 2021 to USD 18.7 billion by 2026, at a Compound Annual Growth Rate (CAGR) of 6.3% during the forecast period.
Which region has the highest market share in the security and vulnerability management market?
North America is estimated to hold the highest market share in the security and vulnerability management market.
What is the definition of security and vulnerability management?
Security and vulnerability management is a continuous process that includes identifying and assessing security postures, internal and external threats, along with formulating policies to shield assets and critical infrastructures of any organization. This process further includes mitigating risks and vulnerabilities, particularly with the use of patch management and configuration management, to eliminate the root cause of cyberattacks. Consequently, the process also involves security configuration processes that are based on industry-recognized or federal-recognized best practices, such as the National Institute of Standards and Technology (NIST) recommendations, the Center for Internet Security (CIS) benchmarks, Federal Financial and Institutions Examination Council (FFIEC), and the European Union Data Protection Directive (EU DPD).
Who are the major vendors in the security and vulnerability management market?
Key and innovative vendors in the security and vulnerability management market include IBM (US), AT&T (US), Qualys (US), Rapid7 (US), Tenable (US), RSA Security (US), McAfee (US), Foreseeti (Sweden), F-Secure (Finland), Acunetix (US), Skybox Security (US), SecPod (India), Tripwire (US), Kenna Security (US), Check Point (US), Expanse (US), Digital Defense (US), Positive Technologies (Russia), Outpost24 (Sweden), Brinqa (US), NopSec (US), RiskIQ (US), RiskSense (US), Claroty (US), Holm Security (Sweden), Balbix (US), Intruder (UK), BreachLock (US), and Nucleus Security (US).
What are the major drivers in the security and vulnerability management market?
The major driving factors contributing to the high growth rate of the security and vulnerability management market include an increase in vulnerabilities across globe, high monetary losses due to the absence of security and vulnerability management solutions, stringent regulatory standard and data privacy compliances, surge in the adoption of IoT and cloud trends, and integration of advanced technologies such as AI and ML with security and vulnerability management solutions. .
To speak to our analyst for a discussion on the above findings, click Speak to Analyst
TABLE OF CONTENTS
1 INTRODUCTION (Page No. - 31)
1.1 INTRODUCTION TO COVID-19
1.2 COVID-19 HEALTH ASSESSMENT
1.3 COVID-19 ECONOMIC ASSESSMENT
1.3.1 COVID-19 ECONOMIC IMPACT�SCENARIO ASSESSMENT
1.4 OBJECTIVES OF THE STUDY
1.5 MARKET DEFINITION
1.5.1 INCLUSIONS AND EXCLUSIONS
1.6 MARKET SCOPE
1.6.1 MARKET SEGMENTATION
1.6.2 REGIONS COVERED
1.7 PERIODIZATION CONSIDERED FOR THE STUDY
1.8 CURRENCY CONSIDERED
1.9 STAKEHOLDERS
1.10 SUMMARY OF CHANGES
2 RESEARCH METHODOLOGY (Page No. - 41)
2.1 RESEARCH DATA
2.1.1 SECONDARY DATA
2.1.2 PRIMARY DATA
2.1.2.1 Breakup of primary profiles
2.1.2.2 Key industry insights
2.2 DATA TRIANGULATION
2.3 MARKET SIZE ESTIMATION
2.3.1 REVENUE ESTIMATES
2.3.2 BOTTOM-UP APPROACH
2.3.3 TOP-DOWN APPROACH
2.4 MARKET FORECAST
2.5 ASSUMPTIONS FOR THE STUDY
2.6 LIMITATIONS OF THE STUDY
3 EXECUTIVE SUMMARY (Page No. - 50)
4 PREMIUM INSIGHTS (Page No. - 55)
4.1 ATTRACTIVE MARKET OPPORTUNITIES IN THE SECURITY AND VULNERABILITY MANAGEMENT MARKET
4.2 MARKET, BY COMPONENT
4.3 MARKET, BY ORGANIZATION SIZE
4.4 MARKET, MARKET SHARE OF THE TOP THREE VERTICALS AND REGIONS
4.5 MARKET INVESTMENT SCENARIO
5 MARKET OVERVIEW AND INDUSTRY TRENDS (Page No. - 58)
5.1 INTRODUCTION
5.2 MARKET DYNAMICS
5.2.1 DRIVERS
5.2.1.1 Increase in vulnerabilities across the globe
5.2.1.2 Growth in the deployment of third-party applications
5.2.1.3 High monetary losses and loss of critical data due to the absence of vulnerability management solutions
5.2.1.4 Stringent regulatory standards and data privacy compliances
5.2.2 RESTRAINTS
5.2.2.1 Security breaches due to internal vulnerabilities
5.2.3 OPPORTUNITIES
5.2.3.1 Widespread adoption of the industrial revolution
5.2.3.2 Integration of advanced technologies with vulnerability management solutions for real-time risk-based security vulnerability prioritization and remediation
5.2.3.3 Integration of vulnerability management and patch management solutions
5.2.4 CHALLENGES
5.2.4.1 High initial installation, maintenance, and deployment cost
5.2.4.2 Lack of appropriate parameters to prioritize risks
5.2.4.3 Regularizing organizations� vulnerability management program
5.3 IMPACT OF COVID-19 ON MARKET DYNAMICS
5.3.1 DRIVERS AND OPPORTUNITIES
5.3.2 RESTRAINTS AND CHALLENGES
5.3.3 CUMULATIVE GROWTH ANALYSIS
5.4 ECOSYSTEM
5.5 SUPPLY CHAIN ANALYSIS
5.5.1 COMPONENT/HARDWARE SUPPLIERS
5.5.2 TECHNOLOGY PROVIDERS
5.5.3 SECURITY SOLUTION AND SERVICE PROVIDERS
5.5.4 SYSTEM INTEGRATORS
5.5.5 SALES AND DISTRIBUTION CHANNELS
5.5.6 END USERS
5.6 PATENT ANALYSIS
5.7 PRICING ANALYSIS
5.8 TECHNOLOGY ANALYSIS
5.8.1 SECURITY AND VULNERABILITY MANAGEMENT AND AI/ML
5.8.2 SECURITY AND VULNERABILITY MANAGEMENT AND CLOUD
5.8.3 SECURITY AND VULNERABILITY MANAGEMENT AND INTERNET OF THINGS
5.9 USE CASES
5.9.1 USE CASE: SCENARIO 1
5.9.2 USE CASE: SCENARIO 2
5.9.3 USE CASE: SCENARIO 3
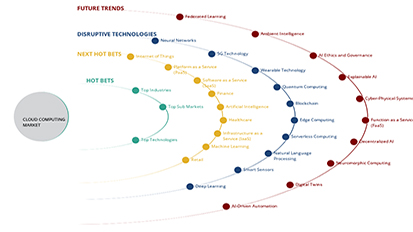
5.10 TRENDS AND DISRUPTIONS IMPACTING CUSTOMERS
5.11 PORTER�S FIVE FORCES ANALYSIS
5.11.1 THREAT FROM NEW ENTRANTS
5.11.2 THREAT FROM SUBSTITUTES
5.11.3 BARGAINING POWER OF SUPPLIERS
5.11.4 BARGAINING POWER OF BUYERS
5.11.5 DEGREE OF COMPETITION
5.12 REGULATORY COMPLIANCES
5.12.1 GENERAL DATA PROTECTION REGULATION
5.12.2 HEALTH INSURANCE PORTABILITY AND ACCOUNTABILITY ACT
5.12.3 HEALTH INFORMATION TECHNOLOGY FOR ECONOMIC AND CLINICAL HEALTH
5.12.4 GOVERNANCE, RISK AND COMPLIANCE
5.12.5 FEDERAL INFORMATION SECURITY MANAGEMENT ACT
5.12.6 SARBANES�OXLEY ACT
5.12.7 GRAMM�LEACH�BLILEY ACT
5.12.8 PAYMENT CARD INDUSTRY DATA SECURITY STANDARD
5.12.9 FEDERAL INFORMATION PROCESSING STANDARDS
5.12.10 INTERNATIONAL ORGANIZATION FOR STANDARDIZATION 27001
6 SECURITY AND VULNERABILITY MANAGEMENT MARKET, BY COMPONENT (Page No. - 85)
6.1 INTRODUCTION
6.2 MARKET ESTIMATES AND FORECASTS, BY COMPONENT, 2016�2025
6.3 SOFTWARE
6.3.1 SOFTWARE: MARKET DRIVERS
6.3.2 SOFTWARE: COVID-19 IMPACT
6.4 SERVICES
6.4.1 SERVICES: MARKET DRIVERS
6.4.2 SERVICES: COVID-19 IMPACT
7 MARKET, BY TARGET (Page No. - 91)
7.1 INTRODUCTION
7.2 MARKET ESTIMATES AND FORECASTS, BY TARGET
7.3 CONTENT MANAGEMENT SYSTEM VULNERABILITIES
7.3.1 CONTENT MANAGEMENT SYSTEM VULNERABILITIES: SMARKET DRIVERS
7.3.2 CONTENT MANAGEMENT SYSTEM VULNERABILITIES: COVID-19 IMPACT
7.4 IOT VULNERABILITIES
7.4.1 IOT VULNERABILITIES: MARKET DRIVERS
7.4.2 IOT VULNERABILITIES: COVID-19 IMPACT
7.5 APPLICATION PROGRAMMING INTERFACE VULNERABILITIES
7.5.1 APPLICATION PROGRAMMING INTERFACE VULNERABILITIES: MARKET DRIVERS
7.5.2 APPLICATION PROGRAMMING INTERFACE VULNERABILITIES: COVID-19 IMPACT
7.6 OTHER TARGET VULNERABILITIES
8 SECURITY AND VULNERABILITY MANAGEMENT MARKET, BY DEPLOYMENT MODE (Page No. - 101)
8.1 INTRODUCTION
8.2 MARKET ESTIMATES AND FORECASTS, BY DEPLOYMENT MODE
8.3 ON-PREMISES
8.3.1 ON-PREMISES: MARKET DRIVERS
8.3.2 ON-PREMISES: COVID-19 IMPACT
8.4 CLOUD
8.4.1 CLOUD: MARKET DRIVERS
8.4.2 CLOUD: COVID-19 IMPACT
9 MARKET, BY ORGANIZATION SIZE (Page No. - 107)
9.1 INTRODUCTION
9.2 MARKET ESTIMATES AND FORECASTS, BY ORGANIZATION SIZE
9.3 LARGE ENTERPRISES
9.3.1 LARGE ENTERPRISES: MARKET DRIVERS
9.3.2 LARGE ENTERPRISES: COVID-19 IMPACT
9.4 SMALL AND MEDIUM-SIZED ENTERPRISES
9.4.1 SMALL AND MEDIUM-SIZED ENTERPRISES: MARKET DRIVERS
9.4.2 SMALL AND MEDIUM-SIZED ENTERPRISES: COVID-19 IMPACT
10 SECURITY AND VULNERABILITY MANAGEMENT MARKET, BY VERTICAL (Page No. - 113)
10.1 INTRODUCTION
10.2 MARKET ESTIMATES AND FORECASTS, BY VERTICAL
10.3 INFORMATION TECHNOLOGY AND INFORMATION TECHNOLOGY-ENABLED SERVICES
10.3.1 INFORMATION TECHNOLOGY AND INFORMATION TECHNOLOGY-ENABLED SERVICES: MARKET DRIVERS
10.3.2 INFORMATION TECHNOLOGY AND INFORMATION TECHNOLOGY-ENABLED SERVICES: COVID-19 IMPACT
10.4 BANKING, FINANCIAL SERVICES, AND INSURANCE (BFSI)
10.4.1 BANKING, FINANCIAL SERVICES AND INSURANCE: MARKET DRIVERS
10.4.2 BANKING, FINANCIAL SERVICES, AND INSURANCE: COVID-19 IMPACT
10.5 HEALTHCARE
10.5.1 HEALTHCARE: MARKET DRIVERS
10.5.2 HEALTHCARE: COVID-19 IMPACT
10.6 RETAIL
10.6.1 RETAIL: MARKET DRIVERS
10.6.2 RETAIL: COVID-19 IMPACT
10.7 MANUFACTURING
10.7.1 MANUFACTURING: MARKET DRIVERS
10.7.2 MANUFACTURING: COVID-19 IMPACT
10.8 ENERGY AND UTILITY
10.8.1 ENERGY AND UTILITY: MARKET DRIVERS
10.8.2 ENERGY AND UTILITY: COVID-19 IMPACT
10.9 OTHER VERTICALS
11 SECURITY AND VULNERABILITY MANAGEMENT MARKET, BY REGION (Page No. - 129)
11.1 INTRODUCTION
11.2 NORTH AMERICA
11.2.1 NORTH AMERICA: MARKET DRIVERS
11.2.2 NORTH AMERICA: COVID-19 IMPACT
11.2.3 NORTH AMERICA: REGULATORY LANDSCAPE
11.2.4 UNITED STATES
11.2.5 CANADA
11.3 EUROPE
11.3.1 EUROPE: MARKET DRIVERS
11.3.2 EUROPE: COVID-19 IMPACT
11.3.3 EUROPE: REGULATORY LANDSCAPE
11.3.4 GERMANY
11.3.5 SWEDEN
11.3.6 DENMARK
11.3.7 REST OF EUROPE
11.4 ASIA PACIFIC
11.4.1 ASIA PACIFIC: SECURITY AND VULNERABILITY MANAGEMENT MARKET DRIVERS
11.4.2 ASIA PACIFIC: COVID-19 IMPACT
11.4.3 ASIA PACIFIC: REGULATORY LANDSCAPE
11.4.4 AUSTRALIA
11.4.5 SOUTH KOREA
11.4.6 REST OF ASIA PACIFIC
11.5 MIDDLE EAST AND AFRICA
11.5.1 MIDDLE EAST AND AFRICA: MARKET DRIVERS
11.5.2 MIDDLE EAST AND AFRICA: COVID-19 IMPACT
11.5.3 MIDDLE EAST AND AFRICA: REGULATORY LANDSCAPE
11.5.4 MIDDLE EAST
11.5.5 AFRICA
11.6 LATIN AMERICA
11.6.1 LATIN AMERICA: SECURITY AND VULNERABILITY MANAGEMENT MARKET DRIVERS
11.6.2 LATIN AMERICA: COVID-19 IMPACT
11.6.3 LATIN AMERICA: REGULATORY LANDSCAPE
11.6.4 BRAZIL
11.6.5 MEXICO
11.6.6 REST OF LATIN AMERICA
12 COMPETITIVE LANDSCAPE (Page No. - 220)
12.1 OVERVIEW
12.2 MARKET STRUCTURE
12.3 HISTORICAL REVENUE ANALYSIS
12.4 MARKET EVALUATION FRAMEWORK
12.5 REVENUE ANALYSIS OF LEADING PLAYERS
12.6 RANKING OF KEY PLAYERS
12.7 COMPANY EVALUATION QUADRANT
12.7.1 COMPANY EVALUATION QUADRANT DEFINITIONS AND METHODOLOGY
12.8 COMPETITIVE LEADERSHIP MAPPING
12.8.1 STARS
12.8.2 EMERGING LEADERS
12.8.3 PERVASIVE PLAYERS
12.8.4 PARTICIPANTS
12.9 COMPETITIVE BENCHMARKING
12.9.1 COMPANY FOOTPRINT
12.10 STARTUP/SME EVALUATION QUADRANT
12.10.1 PROGRESSIVE COMPANIES
12.10.2 RESPONSIVE COMPANIES
12.10.3 DYNAMIC COMPANIES
12.10.4 STARTING BLOCKS
12.11 COMPETITIVE SCENARIO
12.11.1 RECENT DEVELOPMENTS
13 COMPANY PROFILES (Page No. - 236)
13.1 INTRODUCTION
13.2 MAJOR PLAYERS
13.2.1 IBM
13.2.1.1 Business Overview
13.2.1.2 Solutions and Services Offered
13.2.1.3 Recent Developments
13.2.1.4 COVID-19-related Developments
13.2.1.5 MnM View
13.2.1.5.1 Key strengths/right to win
13.2.1.5.2 Strategic choices made
13.2.1.5.3 Weaknesses and competitive threats
13.2.2 AT&T
13.2.2.1 Business Overview
13.2.2.2 Solutions
13.2.2.3 Recent Developments
13.2.2.4 COVID-19-related Developments
13.2.2.5 MNM View
13.2.2.5.1 Key strengths/Right to win
13.2.2.5.2 Strategic choices made
13.2.2.5.3 Weaknesses and competitive threats
13.2.3 QUALYS
13.2.3.1 Business Overview
13.2.3.2 Solutions Offered
13.2.3.3 Recent Developments
13.2.3.4 COVID-19-related Developments
13.2.3.5 MNM view
13.2.3.5.1 Key strengths/Right to win
13.2.3.5.2 Strategic choices
13.2.3.5.3 Weaknesses and competitive threats
13.2.4 RAPID7
13.2.4.1 Business Overview
13.2.4.2 Solutions and Services Offered
13.2.4.3 Recent Developments
13.2.4.4 COVID-19-related Developments
13.2.4.5 MNM View
13.2.4.5.1 Key strengths/right to win
13.2.4.5.2 Strategic choices made
13.2.4.5.3 Weaknesses and competitive threats
13.2.5 TENABLE
13.2.5.1 Business Overview
13.2.5.2 Solutions Offered
13.2.5.3 Recent Developments
13.2.5.4 MNM view
13.2.5.4.1 Key strengths/Right to win
13.2.5.4.2 Strategic choices made
13.2.5.4.3 Weaknesses and competitive threats
13.2.5.5 COVID-19-related Developments
13.2.6 RSA SECURITY
13.2.6.1 Business Overview
13.2.6.2 Solutions Offered
13.2.6.3 Recent Developments
13.2.6.4 COVID-19-related Development
13.2.7 MCAFEE
13.2.7.1 Business Overview
13.2.7.2 Solutions and Services Offered
13.2.7.3 Recent Developments
13.2.7.4 COVID-19-related Developments
13.2.8 FORESEETI
13.2.8.1 Business Overview
13.2.8.2 Solutions and Services Offered
13.2.8.3 Recent Developments
13.2.9 F-SECURE
13.2.9.1 Business Overview
13.2.9.2 Solutions Offered
13.2.9.3 Recent Developments
13.2.10 SKYBOX SECURITY
13.2.10.1 Business Overview
13.2.10.2 Solutions Offered
13.2.10.3 Recent Developments
13.2.11 SECPOD
13.2.11.1 Business Overview
13.2.11.2 Solutions Offered
13.2.11.3 Recent Developments
13.2.11.4 COVID-19-related Developments
13.3 OTHER PLAYERS
13.3.1 TRIPWIRE
13.3.2 KENNA SECURITY
13.3.3 CHECK POINT
13.3.4 EXPANSE
13.3.5 DIGITAL DEFENSE
13.3.6 POSITIVE TECHNOLOGIES
13.3.7 OUTPOST24
13.3.8 ACUNETIX
13.3.9 BRINQA
13.3.10 NOPSEC
13.3.11 RISKIQ
13.3.12 RISKSENSE
13.4 START-UP PROFILES
13.4.1 CLAROTY
13.4.2 HOLM SECURITY
13.4.3 BALBIX
13.4.4 INTRUDER
13.4.5 BREACHLOCK
13.4.6 NUCLEUS SECURITY
14 ADJACENT MARKETS (Page No. - 287)
14.1 INTRODUCTION TO ADJACENT MARKETS
14.2 LIMITATIONS
14.3 CYBERSECURITY MARKET
14.4 SECURITY INFORMATION AND EVENT MANAGEMENT MARKET
15 APPENDIX (Page No. - 299)
15.1 DISCUSSION GUIDE
15.2 KNOWLEDGE STORE: MARKETSANDMARKETS� SUBSCRIPTION PORTAL
15.3 AVAILABLE CUSTOMIZATIONS
15.4 RELATED REPORTS
15.5 AUTHOR DETAILS
LIST OF TABLES (351 Tables)
TABLE 1 USD EXCHANGE RATES, 2018�2020
TABLE 2 FACTOR ANALYSIS
TABLE 3 KEY ARGUMENTS RELATED TO IT AND OT ENVIRONMENTS THAT IMPACT THE SCOPE OF SECURITY AND VULNERABILITY MANAGEMENT
TABLE 4 SECURITY AND VULNERABILITY MANAGEMENT MARKET SIZE AND GROWTH, 2021�2026 (USD MILLION AND Y-O-Y GROWTH)
TABLE 5 MARKET: DRIVERS AND OPPORTUNITIES
TABLE 6 MARKET: RESTRAINTS AND CHALLENGES
TABLE 7 MARKET: CUMULATIVE GROWTH AND IMPACT
TABLE 8 MARKET ECOSYSTEM
TABLE 9 PATENTS INFORMATION, 2021
TABLE 10 MARKET: AVERAGE SELLING PRICES
TABLE 11 PORTER�S FIVE FORCES ANALYSIS: MARKET
TABLE 12 MARKET SIZE, BY COMPONENT, 2016�2020 (USD MILLION)
TABLE 13 MARKET SIZE, BY COMPONENT, 2021�2026 (USD MILLION)
TABLE 14 SOFTWARE: MARKET SIZE, BY REGION, 2016�2020 (USD MILLION)
TABLE 15 SOFTWARE: MARKET SIZE, BY REGION, 2021�2026 (USD MILLION)
TABLE 16 SERVICES: MARKET SIZE, BY REGION, 2016�2020 (USD MILLION)
TABLE 17 SERVICES: MARKET SIZE, BY REGION, 2021�2026 (USD MILLION)
TABLE 18 PAIR OF POPULAR SOFTWARE CATEGORIES AND WEAKNESSES
TABLE 19 MARKET SIZE, BY TARGET, 2016�2020 (USD MILLION)
TABLE 20 MARKET SIZE, BY TARGET, 2021�2026 (USD MILLION)
TABLE 21 CONTENT MANAGEMENT SYSTEM VULNERABILITIES: MARKET SIZE, BY REGION, 2016�2020 (USD MILLION)
TABLE 22 CONTENT MANAGEMENT SYSTEM VULNERABILITIES: MARKET SIZE, BY REGION, 2021�2026 (USD MILLION)
TABLE 23 IOT VULNERABILITIES: SECURITY AND VULNERABILITY MANAGEMENT MARKET SIZE, BY REGION, 2016�2020 (USD MILLION)
TABLE 24 IOT VULNERABILITIES: MARKET SIZE, BY REGION, 2021�2026 (USD MILLION)
TABLE 25 APPLICATION PROGRAMMING INTERFACE VULNERABILITIES: MARKET SIZE, BY REGION, 2016�2020 (USD MILLION)
TABLE 26 APPLICATION PROGRAMMING INTERFACE VULNERABILITIES: MARKET SIZE, BY REGION, 2021�2026 (USD MILLION)
TABLE 27 OTHER TARGET VULNERABILITIES: MARKET SIZE, BY REGION, 2016�2020 (USD MILLION)
TABLE 28 OTHER TARGET VULNERABILITIES: MARKET SIZE, BY REGION, 2021�2026 (USD MILLION)
TABLE 29 MARKET SIZE, BY DEPLOYMENT MODE, 2016�2020 (USD MILLION)
TABLE 30 MARKET SIZE, BY DEPLOYMENT MODE, 2021�2026 (USD MILLION)
TABLE 31 ON-PREMISES: MARKET SIZE, BY REGION, 2016�2020 (USD MILLION)
TABLE 32 ON-PREMISES: MARKET SIZE, BY REGION, 2021�2026 (USD MILLION)
TABLE 33 CLOUD: MARKET SIZE, BY REGION, 2016�2020 (USD MILLION)
TABLE 34 CLOUD: MARKET SIZE, BY REGION, 2021�2026 (USD MILLION)
TABLE 35 MARKET SIZE, BY ORGANIZATION SIZE, 2016�2020 (USD MILLION)
TABLE 36 MARKET SIZE, BY ORGANIZATION SIZE, 2021�2026 (USD MILLION)
TABLE 37 LARGE ENTERPRISES: MARKET SIZE, BY REGION, 2016�2020 (USD MILLION)
TABLE 38 LARGE ENTERPRISES: MARKET SIZE, BY REGION, 2021�2026 (USD MILLION)
TABLE 39 SMALL AND MEDIUM-SIZED ENTERPRISES: MARKET SIZE, BY REGION, 2016�2020 (USD MILLION)
TABLE 40 SMALL AND MEDIUM-SIZED ENTERPRISES: MARKET SIZE, BY REGION, 2021�2026 (USD MILLION)
TABLE 41 SECURITY AND VULNERABILITY MANAGEMENT MARKET SIZE, BY VERTICAL, 2016�2020 (USD MILLION)
TABLE 42 MARKET SIZE, BY VERTICAL, 2021�2026 (USD MILLION)
TABLE 43 INFORMATION TECHNOLOGY AND INFORMATION TECHNOLOGY-ENABLED SERVICES: MARKET SIZE, BY REGION, 2016�2020 (USD MILLION)
TABLE 44 INFORMATION TECHNOLOGY AND INFORMATION TECHNOLOGY-ENABLED SERVICES: MARKET SIZE, BY REGION, 2021�2026 (USD MILLION)
TABLE 45 BANKING, FINANCIAL SERVICES, AND INSURANCE: MARKET SIZE, BY REGION, 2016�2020 (USD MILLION)
TABLE 46 BANKING, FINANCIAL SERVICES, AND INSURANCE: MARKET SIZE, BY REGION, 2021�2026 (USD MILLION)
TABLE 47 HEALTHCARE: MARKET SIZE, BY REGION, 2016�2020 (USD MILLION)
TABLE 48 HEALTHCARE: MARKET SIZE, BY REGION, 2021�2026 (USD MILLION)
TABLE 49 RETAIL: MARKET SIZE, BY REGION, 2016�2020 (USD MILLION)
TABLE 50 RETAIL: MARKET SIZE, BY REGION, 2021�2026 (USD MILLION)
TABLE 51 MANUFACTURING: MARKET SIZE, BY REGION, 2016�2020 (USD MILLION)
TABLE 52 MANUFACTURING: MARKET SIZE, BY REGION, 2021�2026 (USD MILLION)
TABLE 53 ENERGY AND UTILITY: MARKET SIZE, BY REGION, 2016�2020 (USD MILLION)
TABLE 54 ENERGY AND UTILITY: MARKET SIZE, BY REGION, 2021�2026 (USD MILLION)
TABLE 55 OTHER VERTICALS: MARKET SIZE, BY REGION, 2016�2020 (USD MILLION)
TABLE 56 OTHER VERTICALS: MARKET SIZE, BY REGION, 2021�2026 (USD MILLION)
TABLE 57 MARKET SIZE, BY REGION, 2016�2020 (USD MILLION)
TABLE 58 MARKET SIZE, BY REGION, 2021�2026 (USD MILLION)
TABLE 59 NORTH AMERICA: SECURITY AND VULNERABILITY MANAGEMENT MARKET REGULATIONS/ASSOCIATIONS
TABLE 60 NORTH AMERICA: MARKET COMPLIANCE AND DESCRIPTION
TABLE 61 NORTH AMERICA: MARKET SIZE, BY COMPONENT, 2016�2020 (USD MILLION)
TABLE 62 NORTH AMERICA: MARKET SIZE, BY COMPONENT, 2021�2026 (USD MILLION)
TABLE 63 NORTH AMERICA: MARKET SIZE, BY TARGET, 2016�2020 (USD MILLION)
TABLE 64 NORTH AMERICA: MARKET SIZE, BY TARGET, 2021�2026 (USD MILLION)
TABLE 65 NORTH AMERICA: MARKET SIZE, BY DEPLOYMENT MODE, 2016�2020 (USD MILLION)
TABLE 66 NORTH AMERICA: MARKET SIZE, BY DEPLOYMENT MODE, 2021�2026 (USD MILLION)
TABLE 67 NORTH AMERICA: MARKET SIZE, BY ORGANIZATION SIZE, 2016�2020 (USD MILLION)
TABLE 68 NORTH AMERICA: MARKET SIZE, BY ORGANIZATION SIZE, 2021�2026 (USD MILLION)
TABLE 69 NORTH AMERICA: MARKET SIZE, BY VERTICAL, 2016�2020 (USD MILLION)
TABLE 70 NORTH AMERICA: MARKET SIZE, BY VERTICAL, 2021�2026 (USD MILLION)
TABLE 71 NORTH AMERICA: MARKET SIZE, BY COUNTRY, 2016�2020 (USD MILLION)
TABLE 72 NORTH AMERICA: MARKET SIZE, BY COUNTRY, 2021�2026 (USD MILLION)
TABLE 73 UNITED STATES: MARKET SIZE, BY COMPONENT, 2016�2020 (USD MILLION)
TABLE 74 UNITED STATES: MARKET SIZE, BY COMPONENT, 2021�2026 (USD MILLION)
TABLE 75 UNITED STATES: MARKET SIZE, BY TARGET, 2016�2020 (USD MILLION)
TABLE 76 UNITED STATES: MARKET SIZE, BY TARGET, 2021�2026 (USD MILLION)
TABLE 77 UNITED STATES: MARKET SIZE, BY DEPLOYMENT MODE, 2016�2020 (USD MILLION)
TABLE 78 UNITED STATES: MARKET SIZE, BY DEPLOYMENT MODE, 2021�2026 (USD MILLION)
TABLE 79 UNITED STATES: MARKET SIZE, BY ORGANIZATION SIZE, 2016�2020 (USD MILLION)
TABLE 80 UNITED STATES: MARKET SIZE, BY ORGANIZATION SIZE, 2021�2026 (USD MILLION)
TABLE 81 UNITED STATES: MARKET SIZE, BY VERTICAL, 2016�2020 (USD MILLION)
TABLE 82 UNITED STATES: MARKET SIZE, BY VERTICAL, 2021�2026 (USD MILLION)
TABLE 83 CANADA: SECURITY AND VULNERABILITY MANAGEMENT MARKET SIZE, BY COMPONENT, 2016�2020 (USD MILLION)
TABLE 84 CANADA: MARKET SIZE, BY COMPONENT, 2021�2026 (USD MILLION)
TABLE 85 CANADA: MARKET SIZE, BY TARGET, 2016�2020 (USD MILLION)
TABLE 86 CANADA: MARKET SIZE, BY TARGET, 2021�2026 (USD MILLION)
TABLE 87 CANADA: MARKET SIZE, BY DEPLOYMENT MODE, 2016�2020 (USD MILLION)
TABLE 88 CANADA: MARKET SIZE, BY DEPLOYMENT MODE, 2021�2026 (USD MILLION)
TABLE 89 CANADA: MARKET SIZE, BY ORGANIZATION SIZE, 2016�2020 (USD MILLION)
TABLE 90 CANADA: MARKET SIZE, BY ORGANIZATION SIZE, 2021�2026 (USD MILLION)
TABLE 91 CANADA: MARKET SIZE, BY VERTICAL, 2016�2020 (USD MILLION)
TABLE 92 CANADA: MARKET SIZE, BY VERTICAL, 2021�2026 (USD MILLION)
TABLE 93 EUROPE: MARKET REGULATIONS/ASSOCIATIONS
TABLE 94 EUROPE: MARKET COMPLIANCE AND DESCRIPTION
TABLE 95 EUROPE: MARKET SIZE, BY COMPONENT, 2016�2020 (USD MILLION)
TABLE 96 EUROPE: MARKET SIZE, BY COMPONENT, 2021�2026 (USD MILLION)
TABLE 97 EUROPE: MARKET SIZE, BY TARGET, 2016�2020 (USD MILLION)
TABLE 98 EUROPE: MARKET SIZE, BY TARGET, 2021�2026 (USD MILLION)
TABLE 99 EUROPE: MARKET SIZE, BY DEPLOYMENT MODE, 2016�2020 (USD MILLION)
TABLE 100 EUROPE: MARKET SIZE, BY DEPLOYMENT MODE, 2021�2026 (USD MILLION)
TABLE 101 EUROPE: MARKET SIZE, BY ORGANIZATION SIZE, 2016�2020 (USD MILLION)
TABLE 102 EUROPE: MARKET SIZE, BY ORGANIZATION SIZE, 2021�2026 (USD MILLION)
TABLE 103 EUROPE: MARKET SIZE, BY VERTICAL, 2016�2020 (USD MILLION)
TABLE 104 EUROPE: MARKET SIZE, BY VERTICAL, 2021�2026 (USD MILLION)
TABLE 105 EUROPE: MARKET SIZE, BY COUNTRY, 2016�2020 (USD MILLION)
TABLE 106 EUROPE: MARKET SIZE, BY COUNTRY, 2021�2026 (USD MILLION)
TABLE 107 GERMANY: SECURITY AND VULNERABILITY MANAGEMENT MARKET SIZE, BY COMPONENT, 2016�2020 (USD MILLION)
TABLE 108 GERMANY: MARKET SIZE, BY COMPONENT, 2021�2026 (USD MILLION)
TABLE 109 GERMANY: MARKET SIZE, BY TARGET, 2016�2020 (USD MILLION)
TABLE 110 GERMANY: MARKET SIZE, BY TARGET, 2021�2026 (USD MILLION)
TABLE 111 GERMANY: MARKET SIZE, BY DEPLOYMENT MODE, 2016�2020 (USD MILLION)
TABLE 112 GERMANY: MARKET SIZE, BY DEPLOYMENT MODE, 2021�2026 (USD MILLION)
TABLE 113 GERMANY: MARKET SIZE, BY ORGANIZATION SIZE, 2016�2020 (USD MILLION)
TABLE 114 GERMANY: MARKET SIZE, BY ORGANIZATION SIZE, 2021�2026 (USD MILLION)
TABLE 115 GERMANY: MARKET SIZE, BY VERTICAL, 2016�2020 (USD MILLION)
TABLE 116 GERMANY: MARKET SIZE, BY VERTICAL, 2021�2026 (USD MILLION)
TABLE 117 SWEDEN: MARKET SIZE, BY COMPONENT, 2016�2020 (USD MILLION)
TABLE 118 SWEDEN: MARKET SIZE, BY COMPONENT, 2021�2026 (USD MILLION)
TABLE 119 SWEDEN: MARKET SIZE, BY TARGET, 2016�2020 (USD MILLION)
TABLE 120 SWEDEN: MARKET SIZE, BY TARGET, 2021�2026 (USD MILLION)
TABLE 121 SWEDEN: MARKET SIZE, BY DEPLOYMENT MODE, 2016�2020 (USD MILLION)
TABLE 122 SWEDEN: MARKET SIZE, BY DEPLOYMENT MODE, 2021�2026 (USD MILLION)
TABLE 123 SWEDEN: MARKET SIZE, BY ORGANIZATION SIZE, 2016�2020 (USD MILLION)
TABLE 124 SWEDEN: MARKET SIZE, BY ORGANIZATION SIZE, 2021�2026 (USD MILLION)
TABLE 125 SWEDEN: MARKET SIZE, BY VERTICAL, 2016�2020 (USD MILLION)
TABLE 126 SWEDEN: SECURITY AND VULNERABILITY MANAGEMENT MARKET SIZE, BY VERTICAL, 2021�2026 (USD MILLION)
TABLE 127 DENMARK: MARKET SIZE, BY COMPONENT, 2016�2020 (USD MILLION)
TABLE 128 DENMARK: MARKET SIZE, BY COMPONENT, 2021�2026 (USD MILLION)
TABLE 129 DENMARK: MARKET SIZE, BY TARGET, 2016�2020 (USD MILLION)
TABLE 130 DENMARK: MARKET SIZE, BY TARGET, 2021�2026 (USD MILLION)
TABLE 131 DENMARK: MARKET SIZE, BY DEPLOYMENT MODE, 2016�2020 (USD MILLION)
TABLE 132 DENMARK: MARKET SIZE, BY DEPLOYMENT MODE, 2021�2026 (USD MILLION)
TABLE 133 DENMARK: MARKET SIZE, BY ORGANIZATION SIZE, 2016�2020 (USD MILLION)
TABLE 134 DENMARK: MARKET SIZE, BY ORGANIZATION SIZE, 2021�2026 (USD MILLION)
TABLE 135 DENMARK: MARKET SIZE, BY VERTICAL, 2016�2020 (USD MILLION)
TABLE 136 DENMARK: MARKET SIZE, BY VERTICAL, 2021�2026 (USD MILLION)
TABLE 137 REST OF EUROPE: MARKET SIZE, BY COMPONENT, 2016�2020 (USD MILLION)
TABLE 138 REST OF EUROPE: MARKET SIZE, BY COMPONENT, 2021�2026 (USD MILLION)
TABLE 139 REST OF EUROPE: MARKET SIZE, BY TARGET, 2016�2020 (USD MILLION)
TABLE 140 REST OF EUROPE: MARKET SIZE, BY TARGET, 2021�2026 (USD MILLION)
TABLE 141 REST OF EUROPE: MARKET SIZE, BY DEPLOYMENT MODE, 2016�2020 (USD MILLION)
TABLE 142 REST OF EUROPE: MARKET SIZE, BY DEPLOYMENT MODE, 2021�2026 (USD MILLION)
TABLE 143 REST OF EUROPE: MARKET SIZE, BY ORGANIZATION SIZE, 2016�2020 (USD MILLION)
TABLE 144 REST OF EUROPE: MARKET SIZE, BY ORGANIZATION SIZE, 2021�2026 (USD MILLION)
TABLE 145 REST OF EUROPE: MARKET SIZE, BY VERTICAL, 2016�2020 (USD MILLION)
TABLE 146 REST OF EUROPE: MARKET SIZE, BY VERTICAL, 2021�2026 (USD MILLION)
TABLE 147 ASIA PACIFIC: SECURITY AND VULNERABILITY MANAGEMENT MARKET REGULATIONS/ASSOCIATIONS
TABLE 148 ASIA PACIFIC: SECURITY AND VULNERABILITY MANAGEMENT COMPLIANCE AND DESCRIPTION
TABLE 149 ASIA PACIFIC: MARKET SIZE, BY COMPONENT, 2016�2020 (USD MILLION)
TABLE 150 ASIA PACIFIC: MARKET SIZE, BY COMPONENT, 2021�2026 (USD MILLION)
TABLE 151 ASIA PACIFIC: MARKET SIZE, BY TARGET, 2016�2020 (USD MILLION)
TABLE 152 ASIA PACIFIC: MARKET SIZE, BY TARGET, 2021�2026 (USD MILLION)
TABLE 153 ASIA PACIFIC: MARKET SIZE, BY DEPLOYMENT MODE, 2016�2020 (USD MILLION)
TABLE 154 ASIA PACIFIC: MARKET SIZE, BY DEPLOYMENT MODE, 2021�2026 (USD MILLION)
TABLE 155 ASIA PACIFIC: MARKET SIZE, BY ORGANIZATION SIZE, 2016�2020 (USD MILLION)
TABLE 156 ASIA PACIFIC: MARKET SIZE, BY ORGANIZATION SIZE, 2021�2026 (USD MILLION)
TABLE 157 ASIA PACIFIC: MARKET SIZE, BY VERTICAL, 2016�2020 (USD MILLION)
TABLE 158 ASIA PACIFIC: MARKET SIZE, BY VERTICAL, 2021�2026 (USD MILLION)
TABLE 159 ASIA PACIFIC: MARKET SIZE, BY COUNTRY, 2016�2020 (USD MILLION)
TABLE 160 ASIA PACIFIC: MARKET SIZE, BY COUNTRY, 2021�2026 (USD MILLION)
TABLE 161 AUSTRALIA: SECURITY AND VULNERABILITY MANAGEMENT MARKET SIZE, BY COMPONENT, 2016�2020 (USD MILLION)
TABLE 162 AUSTRALIA: MARKET SIZE, BY COMPONENT, 2021�2026 (USD MILLION)
TABLE 163 AUSTRALIA: MARKET SIZE, BY TARGET, 2016�2020 (USD MILLION)
TABLE 164 AUSTRALIA: MARKET SIZE, BY TARGET, 2021�2026 (USD MILLION)
TABLE 165 AUSTRALIA: MARKET SIZE, BY DEPLOYMENT MODE, 2016�2020 (USD MILLION)
TABLE 166 AUSTRALIA: MARKET SIZE, BY DEPLOYMENT MODE, 2021�2026 (USD MILLION)
TABLE 167 AUSTRALIA: MARKET SIZE, BY ORGANIZATION SIZE, 2016�2020 (USD MILLION)
TABLE 168 AUSTRALIA: MARKET SIZE, BY ORGANIZATION SIZE, 2021�2026 (USD MILLION)
TABLE 169 AUSTRALIA: MARKET SIZE, BY VERTICAL, 2016�2020 (USD MILLION)
TABLE 170 AUSTRALIA: MARKET SIZE, BY VERTICAL, 2021�2026 (USD MILLION)
TABLE 171 SOUTH KOREA: MARKET SIZE, BY COMPONENT, 2016�2020 (USD MILLION)
TABLE 172 SOUTH KOREA: MARKET SIZE, BY COMPONENT, 2021�2026 (USD MILLION)
TABLE 173 SOUTH KOREA: MARKET SIZE, BY TARGET, 2016�2020 (USD MILLION)
TABLE 174 SOUTH KOREA: MARKET SIZE, BY TARGET, 2021�2026 (USD MILLION)
TABLE 175 SOUTH KOREA: MARKET SIZE, BY DEPLOYMENT MODE, 2016�2020 (USD MILLION)
TABLE 176 SOUTH KOREA: MARKET SIZE, BY DEPLOYMENT MODE, 2021�2026 (USD MILLION)
TABLE 177 SOUTH KOREA: MARKET SIZE, BY ORGANIZATION SIZE, 2016�2020 (USD MILLION)
TABLE 178 SOUTH KOREA: MARKET SIZE, BY ORGANIZATION SIZE, 2021�2026 (USD MILLION)
TABLE 179 SOUTH KOREA: MARKET SIZE, BY VERTICAL, 2016�2020 (USD MILLION)
TABLE 180 SOUTH KOREA: MARKET SIZE, BY VERTICAL, 2021�2026 (USD MILLION)
TABLE 181 REST OF ASIA PACIFIC: SECURITY AND VULNERABILITY MANAGEMENT MARKET SIZE, BY COMPONENT, 2016�2020 (USD MILLION)
TABLE 182 REST OF ASIA PACIFIC: MARKET SIZE, BY COMPONENT, 2021�2026 (USD MILLION)
TABLE 183 REST OF ASIA PACIFIC: MARKET SIZE, BY TARGET, 2016�2020 (USD MILLION)
TABLE 184 REST OF ASIA PACIFIC: MARKET SIZE, BY TARGET, 2021�2026 (USD MILLION)
TABLE 185 REST OF ASIA PACIFIC: MARKET SIZE, BY DEPLOYMENT MODE, 2016�2020 (USD MILLION)
TABLE 186 REST OF ASIA PACIFIC: MARKET SIZE, BY DEPLOYMENT MODE, 2021�2026 (USD MILLION)
TABLE 187 REST OF ASIA PACIFIC: MARKET SIZE, BY ORGANIZATION SIZE, 2016�2020 (USD MILLION)
TABLE 188 REST OF ASIA PACIFIC: MARKET SIZE, BY ORGANIZATION SIZE, 2021�2026 (USD MILLION)
TABLE 189 REST OF ASIA PACIFIC: MARKET SIZE, BY VERTICAL, 2016�2020 (USD MILLION)
TABLE 190 REST OF ASIA PACIFIC: MARKET SIZE, BY VERTICAL, 2021�2026 (USD MILLION)
TABLE 191 MIDDLE EAST AND AFRICA: MARKET REGULATIONS/ASSOCIATIONS
TABLE 192 MIDDLE EAST AND AFRICA: MARKET COMPLIANCE AND DESCRIPTION
TABLE 193 MIDDLE EAST AND AFRICA: MARKET SIZE, BY COMPONENT, 2016�2020 (USD MILLION)
TABLE 194 MIDDLE EAST AND AFRICA: MARKET SIZE, BY COMPONENT, 2021�2026 (USD MILLION)
TABLE 195 MIDDLE EAST AND AFRICA: MARKET SIZE, BY TARGET, 2016�2020 (USD MILLION)
TABLE 196 MIDDLE EAST AND AFRICA: MARKET SIZE, BY TARGET, 2021�2026 (USD MILLION)
TABLE 197 MIDDLE EAST AND AFRICA: MARKET SIZE, BY DEPLOYMENT MODE, 2016�2020 (USD MILLION)
TABLE 198 MIDDLE EAST AND AFRICA: MARKET SIZE, BY DEPLOYMENT MODE, 2021�2026 (USD MILLION)
TABLE 199 MIDDLE EAST AND AFRICA: MARKET SIZE, BY ORGANIZATION SIZE, 2016�2020 (USD MILLION)
TABLE 200 MIDDLE EAST AND AFRICA: MARKET SIZE, BY ORGANIZATION SIZE, 2021�2026 (USD MILLION)
TABLE 201 MIDDLE EAST AND AFRICA: MARKET SIZE, BY VERTICAL, 2016�2020 (USD MILLION)
TABLE 202 MIDDLE EAST AND AFRICA: MARKET SIZE, BY VERTICAL, 2021�2026 (USD MILLION)
TABLE 203 MIDDLE EAST AND AFRICA: MARKET SIZE, BY REGION, 2016�2020 (USD MILLION)
TABLE 204 MIDDLE EAST AND AFRICA: MARKET SIZE, BY REGION, 2021�2026 (USD MILLION)
TABLE 205 MIDDLE EAST: SECURITY AND VULNERABILITY MANAGEMENT MARKET SIZE, BY COMPONENT, 2016�2020 (USD MILLION)
TABLE 206 MIDDLE EAST: MARKET SIZE, BY COMPONENT, 2021�2026 (USD MILLION)
TABLE 207 MIDDLE EAST: MARKET SIZE, BY TARGET, 2016�2020 (USD MILLION)
TABLE 208 MIDDLE EAST: MARKET SIZE, BY TARGET, 2021�2026 (USD MILLION)
TABLE 209 MIDDLE EAST: MARKET SIZE, BY DEPLOYMENT MODE, 2016�2020 (USD MILLION)
TABLE 210 MIDDLE EAST: MARKET SIZE, BY DEPLOYMENT MODE, 2021�2026 (USD MILLION)
TABLE 211 MIDDLE EAST: MARKET SIZE, BY ORGANIZATION SIZE, 2016�2020 (USD MILLION)
TABLE 212 MIDDLE EAST: MARKET SIZE, BY ORGANIZATION SIZE, 2021�2026 (USD MILLION)
TABLE 213 MIDDLE EAST: MARKET SIZE, BY VERTICAL, 2016�2020 (USD MILLION)
TABLE 214 MIDDLE EAST: MARKET SIZE, BY VERTICAL, 2021�2026 (USD MILLION)
TABLE 215 AFRICA: MARKET SIZE, BY COMPONENT, 2016�2020 (USD MILLION)
TABLE 216 AFRICA: MARKET SIZE, BY COMPONENT, 2021�2026 (USD MILLION)
TABLE 217 AFRICA: MARKET SIZE, BY TARGET, 2016�2020 (USD MILLION)
TABLE 218 AFRICA: MARKET SIZE, BY TARGET, 2021�2026 (USD MILLION)
TABLE 219 AFRICA: MARKET SIZE, BY DEPLOYMENT MODE, 2016�2020 (USD MILLION)
TABLE 220 AFRICA: MARKET SIZE, BY DEPLOYMENT MODE, 2021�2026 (USD MILLION)
TABLE 221 AFRICA: MARKET SIZE, BY ORGANIZATION SIZE, 2016�2020 (USD MILLION)
TABLE 222 AFRICA: MARKET SIZE, BY ORGANIZATION SIZE, 2021�2026 (USD MILLION)
TABLE 223 AFRICA: MARKET SIZE, BY VERTICAL, 2016�2020 (USD MILLION)
TABLE 224 AFRICA: MARKET SIZE, BY VERTICAL, 2021�2026 (USD MILLION)
TABLE 225 LATIN AMERICA: SECURITY AND VULNERABILITY MANAGEMENT MARKET REGULATIONS/ASSOCIATIONS
TABLE 226 LATIN AMERICA: MARKET COMPLIANCE AND DESCRIPTION
TABLE 227 LATIN AMERICA: MARKET SIZE, BY COMPONENT, 2016�2020 (USD MILLION)
TABLE 228 LATIN AMERICA: MARKET SIZE, BY COMPONENT, 2021�2026 (USD MILLION)
TABLE 229 LATIN AMERICA: MARKET SIZE, BY TARGET, 2016�2020 (USD MILLION)
TABLE 230 LATIN AMERICA: MARKET SIZE, BY TARGET, 2021�2026 (USD MILLION)
TABLE 231 LATIN AMERICA: MARKET SIZE, BY DEPLOYMENT MODE, 2016�2020 (USD MILLION)
TABLE 232 LATIN AMERICA: MARKET SIZE, BY DEPLOYMENT MODE, 2021�2026 (USD MILLION)
TABLE 233 LATIN AMERICA: MARKET SIZE, BY ORGANIZATION SIZE, 2016�2020 (USD MILLION)
TABLE 234 LATIN AMERICA: MARKET SIZE, BY ORGANIZATION SIZE, 2021�2026 (USD MILLION)
TABLE 235 LATIN AMERICA: MARKET SIZE, BY VERTICAL, 2016�2020 (USD MILLION)
TABLE 236 LATIN AMERICA: MARKET SIZE, BY VERTICAL, 2021�2026 (USD MILLION)
TABLE 237 LATIN AMERICA: MARKET SIZE, BY COUNTRY, 2016�2020 (USD MILLION)
TABLE 238 LATIN AMERICA: MARKET SIZE, BY COUNTRY, 2021�2026 (USD MILLION)
TABLE 239 BRAZIL: SECURITY AND VULNERABILITY MANAGEMENT MARKET SIZE, BY COMPONENT, 2016�2020 (USD MILLION)
TABLE 240 BRAZIL: MARKET SIZE, BY COMPONENT, 2021�2026 (USD MILLION)
TABLE 241 BRAZIL: MARKET SIZE, BY TARGET, 2016�2020 (USD MILLION)
TABLE 242 BRAZIL: MARKET SIZE, BY TARGET, 2021�2026 (USD MILLION)
TABLE 243 BRAZIL: MARKET SIZE, BY DEPLOYMENT MODE, 2016�2020 (USD MILLION)
TABLE 244 BRAZIL: MARKET SIZE, BY DEPLOYMENT MODE, 2021�2026 (USD MILLION)
TABLE 245 BRAZIL: MARKET SIZE, BY ORGANIZATION SIZE, 2016�2020 (USD MILLION)
TABLE 246 BRAZIL: MARKET SIZE, BY ORGANIZATION SIZE, 2021�2026 (USD MILLION)
TABLE 247 BRAZIL: MARKET SIZE, BY VERTICAL, 2016�2020 (USD MILLION)
TABLE 248 BRAZIL: MARKET SIZE, BY VERTICAL, 2021�2026 (USD MILLION)
TABLE 249 MEXICO: MARKET SIZE, BY COMPONENT, 2016�2020 (USD MILLION)
TABLE 250 MEXICO: MARKET SIZE, BY COMPONENT, 2021�2026 (USD MILLION)
TABLE 251 MEXICO: MARKET SIZE, BY TARGET, 2016�2020 (USD MILLION)
TABLE 252 MEXICO: MARKET SIZE, BY TARGET, 2021�2026 (USD MILLION)
TABLE 253 MEXICO: MARKET SIZE, BY DEPLOYMENT MODE, 2016�2020 (USD MILLION)
TABLE 254 MEXICO: MARKET SIZE, BY DEPLOYMENT MODE, 2021�2026 (USD MILLION)
TABLE 255 MEXICO: MARKET SIZE, BY ORGANIZATION SIZE, 2016�2020 (USD MILLION)
TABLE 256 MEXICO: MARKET SIZE, BY ORGANIZATION SIZE, 2021�2026 (USD MILLION)
TABLE 257 MEXICO: MARKET SIZE, BY VERTICAL, 2016�2020 (USD MILLION)
TABLE 258 MEXICO: MARKET SIZE, BY VERTICAL, 2021�2026 (USD MILLION)
TABLE 259 REST OF LATIN AMERICA: SECURITY AND VULNERABILITY MANAGEMENT MARKET SIZE, BY COMPONENT, 2016�2020 (USD MILLION)
TABLE 260 REST OF LATIN AMERICA: MARKET SIZE, BY COMPONENT, 2021�2026 (USD MILLION)
TABLE 261 REST OF LATIN AMERICA: MARKET SIZE, BY TARGET, 2016�2020 (USD MILLION)
TABLE 262 REST OF LATIN AMERICA: MARKET SIZE, BY TARGET, 2021�2026 (USD MILLION)
TABLE 263 REST OF LATIN AMERICA: MARKET SIZE, BY DEPLOYMENT MODE, 2016�2020 (USD MILLION)
TABLE 264 REST OF LATIN AMERICA: MARKET SIZE, BY DEPLOYMENT MODE, 2021�2026 (USD MILLION)
TABLE 265 REST OF LATIN AMERICA: MARKET SIZE, BY ORGANIZATION SIZE, 2016�2020 (USD MILLION)
TABLE 266 REST OF LATIN AMERICA: MARKET SIZE, BY ORGANIZATION SIZE, 2021�2026 (USD MILLION)
TABLE 267 REST OF LATIN AMERICA: MARKET SIZE, BY VERTICAL, 2016�2020 (USD MILLION)
TABLE 268 REST OF LATIN AMERICA: MARKET SIZE, BY VERTICAL, 2021�2026 (USD MILLION)
TABLE 269 SECURITY AND VULNERABILITY MANAGEMENT MARKET: DEGREE OF COMPETITION
TABLE 270 EVALUATION CRITERIA
TABLE 271 COMPANY FOOTPRINT
TABLE 272 MARKET: PRODUCT LAUNCHES
TABLE 273 MARKET: DEALS
TABLE 274 IBM: BUSINESS OVERVIEW
TABLE 275 IBM: SOLUTIONS OFFERED
TABLE 276 IBM: SERVICES OFFERED
TABLE 277 IBM: PRODUCT LAUNCHES AND ENHANCEMENTS
TABLE 278 IBM: DEALS
TABLE 279 AT&T: BUSINESS OVERVIEW
TABLE 280 AT&T: SOLUTIONS OFFERED
TABLE 281 AT&T: SERVICES OFFERED
TABLE 282 AT&T: PRODUCT LAUNCHES AND ENHANCEMENTS
TABLE 283 AT&T: DEALS
TABLE 284 QUALYS: BUSINESS OVERVIEW
TABLE 285 QUALYS: SOLUTIONS OFFERED
TABLE 286 QUALYS: PRODUCT LAUNCHES AND ENHANCEMENTS
TABLE 287 QUALYS: DEALS
TABLE 288 RAPID7: BUSINESS OVERVIEW
TABLE 289 RAPID7: SOLUTIONS OFFERED
TABLE 290 RAPID 7: SERVICES OFFERED
TABLE 291 RAPID7: PRODUCT LAUNCHES AND ENHANCEMENTS
TABLE 292 RAPID7: DEALS
TABLE 293 TENABLE: BUSINESS OVERVIEW
TABLE 294 TENABLE: SOLUTIONS OFFERED
TABLE 295 TENABLE: PRODUCT LAUNCHES
TABLE 296 TENABLE: DEALS
TABLE 297 RSA SECURITY: BUSINESS OVERVIEW
TABLE 298 RSA SECURITY: SOLUTIONS OFFERED
TABLE 299 RSA SECURITY: PRODUCT LAUNCHES AND ENHANCEMENTS
TABLE 300 MCAFEE: BUSINESS OVERVIEW
TABLE 301 MCAFEE: SOLUTIONS OFFERED
TABLE 302 MCAFEE: PRODUCT LAUNCHES
TABLE 303 MCAFEE: DEALS
TABLE 304 FORESEETI: BUSINESS OVERVIEW
TABLE 305 FORESEETI: SOLUTIONS OFFERED
TABLE 306 FORESEETI: PRODUCT LAUNCHES AND ENHANCEMENTS
TABLE 307 FORESEETI: DEALS
TABLE 308 F-SECURE: BUSINESS OVERVIEW
TABLE 309 F-SECURE: SOLUTIONS OFFERED
TABLE 310 F-SECURE: PRODUCT LAUNCHES AND ENHANCEMENTS
TABLE 311 F-SECURE: DEALS
TABLE 312 SKYBOX SECURITY: BUSINESS OVERVIEW
TABLE 313 SKYBOX SECURITY: SOLUTIONS OFFERED
TABLE 314 SKYBOX SECURITY: PRODUCT LAUNCHES AND ENHANCEMENTS
TABLE 315 SKYBOX SECURITY: DEALS
TABLE 316 SECPOD: BUSINESS OVERVIEW
TABLE 317 SECPOD: SOLUTIONS OFFERED
TABLE 318 SECPOD: PRODUCT LAUNCHES AND ENHANCEMENTS
TABLE 319 SECPOD: DEALS
TABLE 320 ADJACENT MARKETS AND FORECASTS
TABLE 321 CYBERSECURITY MARKET SIZE FOR ADVANCED THREAT PROTECTION, BY REGION, 2015�2020 (USD MILLION)
TABLE 322 CYBERSECURITY MARKET SIZE FOR ADVANCED THREAT PROTECTION, BY REGION, 2020�2026 (USD MILLION)
TABLE 323 CYBERSECURITY MARKET SIZE FOR THREAT INTELLIGENCE PLATFORM, BY REGION, 2015�2020 (USD MILLION)
TABLE 324 CYBERSECURITY MARKET SIZE FOR THREAT INTELLIGENCE PLATFORM, BY REGION, 2020�2026 (USD MILLION)
TABLE 325 CYBERSECURITY MARKET SIZE FOR SECURITY AND INFORMATION EVENT MANAGEMENT, BY REGION, 2015�2020 (USD MILLION)
TABLE 326 CYBERSECURITY MARKET SIZE FOR SECURITY AND INFORMATION EVENT MANAGEMENT, BY REGION, 2020�2026 (USD MILLION)
TABLE 327 CYBERSECURITY MARKET SIZE FOR SECURITY AND VULNERABILITY MANAGEMENT, BY REGION, 2015�2020 (USD MILLION)
TABLE 328 CYBERSECURITY MARKET SIZE FOR SECURITY AND VULNERABILITY MANAGEMENT, BY REGION, 2020�2026 (USD MILLION)
TABLE 329 CYBERSECURITY MARKET SIZE FOR NETWORK ACCESS CONTROL, BY REGION, 2015�2020 (USD MILLION)
TABLE 330 CYBERSECURITY MARKET SIZE FOR NETWORK ACCESS CONTROL, BY REGION, 2020�2026 (USD MILLION)
TABLE 331 CYBERSECURITY MARKET SIZE FOR ANTIVIRUS/ANTIMALWARE, BY REGION, 2015�2020 (USD MILLION)
TABLE 332 CYBERSECURITY MARKET SIZE FOR ANTIVIRUS/ANTIMALWARE, BY REGION, 2020�2026 (USD MILLION)
TABLE 333 CYBERSECURITY MARKET SIZE FOR FIREWALL, BY REGION, 2015�2020 (USD MILLION)
TABLE 334 CYBERSECURITY MARKET SIZE FOR FIREWALL, BY REGION, 2020�2026 (USD MILLION)
TABLE 335 CYBERSECURITY MARKET SIZE FOR SECURE WEB GATEWAY, BY REGION, 2015�2020 (USD MILLION)
TABLE 336 CYBERSECURITY MARKET SIZE FOR SECURE WEB GATEWAY, BY REGION, 2020�2026 (USD MILLION)
TABLE 337 CYBERSECURITY MARKET SIZE FOR SECURITY ORCHESTRATION AUTOMATION AND RESPONSE, BY REGION, 2015�2020 (USD MILLION)
TABLE 338 CYBERSECURITY MARKET SIZE FOR SECURITY ORCHESTRATION AUTOMATION AND RESPONSE, BY REGION, 2020�2026 (USD MILLION)
TABLE 339 CYBERSECURITY MARKET SIZE FOR IDENTITY AND ACCESS MANAGEMENT, BY REGION, 2015�2020 (USD MILLION)
TABLE 340 CYBERSECURITY MARKET SIZE FOR IDENTITY AND ACCESS MANAGEMENT, BY REGION, 2020�2026 (USD MILLION)
TABLE 341 CYBERSECURITY MARKET SIZE FOR ENCRYPTION, BY REGION, 2015�2020 (USD MILLION)
TABLE 342 CYBERSECURITY MARKET SIZE FOR ENCRYPTION, BY REGION, 2020�2026 (USD MILLION)
TABLE 343 CYBERSECURITY MARKET SIZE FOR DISASTER RECOVERY, BY REGION, 2015�2020 (USD MILLION)
TABLE 344 CYBERSECURITY MARKET SIZE FOR DISASTER RECOVERY, BY REGION, 2020�2026 (USD MILLION)
TABLE 345 CYBERSECURITY MARKET SIZE FOR INTRUSION DETECTION AND PREVENTION SYSTEM, BY REGION, 2015�2020 (USD MILLION)
TABLE 346 CYBERSECURITY MARKET SIZE FOR INTRUSION DETECTION AND PREVENTION SYSTEM, BY REGION, 2020�2026 (USD MILLION)
TABLE 347 CYBERSECURITY MARKET SIZE FOR RISK AND COMPLIANCE MANAGEMENT, BY REGION, 2015�2020 (USD MILLION)
TABLE 348 CYBERSECURITY MARKET SIZE FOR RISK AND COMPLIANCE MANAGEMENT, BY REGION, 2020�2026 (USD MILLION)
TABLE 349 LOG MANAGEMENT AND REPORTING: SECURITY INFORMATION AND EVENT MANAGEMENT MARKET SIZE, BY REGION, 2018�2025 (USD MILLION)
TABLE 350 THREAT INTELLIGENCE: SECURITY INFORMATION AND EVENT MANAGEMENT MARKET SIZE, BY REGION, 2018�2025 (USD MILLION)
TABLE 351 SECURITY ANALYTICS: SECURITY INFORMATION AND EVENT MANAGEMENT MARKET SIZE, BY REGION, 2018�2025 (USD MILLION)
LIST OF FIGURES (45 Figures)
FIGURE 1 COVID-19: GLOBAL PROPAGATION
FIGURE 2 COVID-19 PROPAGATION: SELECT COUNTRIES
FIGURE 3 REVISED GROSS DOMESTIC PRODUCT FORECASTS FOR SELECT G20 COUNTRIES IN 2020
FIGURE 4 CRITERIA IMPACTING GLOBAL ECONOMY
FIGURE 5 SCENARIOS IN TERMS OF RECOVERY OF GLOBAL ECONOMY
FIGURE 6 SECURITY AND VULNERABILITY MANAGEMENT MARKET: RESEARCH DESIGN
FIGURE 7 MARKET SIZE ESTIMATION METHODOLOGY�APPROACH 1 (SUPPLY SIDE): REVENUE OF SECURITY AND VULNERABILITY MANAGEMENT VENDORS
FIGURE 8 MARKET SIZE ESTIMATION METHODOLOGY�APPROACH 2 BOTTOM-UP (DEMAND-SIDE ANALYSIS)
FIGURE 9 MATURITY AND EVOLUTION OF VULNERABILITY MANAGEMENT FROM REACTIVE TO PROACTIVE APPROACH
FIGURE 10 MARKET TO WITNESS A SIGNIFICANT GROWTH DURING THE FORECAST PERIOD
FIGURE 11 NORTH AMERICA TO ACCOUNT FOR THE HIGHEST MARKET SHARE IN 2021
FIGURE 12 FASTEST-GROWING SEGMENTS OF THE MARKET
FIGURE 13 GROWING COMPLIANCE TO CYBERSECURITY STANDARDS TO FUEL GROWTH OF MARKET
FIGURE 14 SECURITY AND VULNERABILITY MANAGEMENT SOFTWARE TO ACCOUNT FOR A LARGER MARKET SHARE DURING THE FORECAST PERIOD
FIGURE 15 LARGE ENTERPRISES TO ACCOUNT FOR A LARGER MARKET SHARE DURING THE FORECAST PERIOD
FIGURE 16 IT AND ITES VERTICAL AND NORTH AMERICA TO ACCOUNT FOR THE LARGEST MARKET SHARES IN 2021
FIGURE 17 ASIA PACIFIC TO EMERGE AS THE BEST MARKET FOR INVESTMENT IN THE NEXT FIVE YEARS
FIGURE 18 DRIVERS, RESTRAINTS, OPPORTUNITIES, AND CHALLENGES: MARKET
FIGURE 19 OCCURRENCE OF CRITICAL RISK ISSUES (2020)
FIGURE 20 AVERAGE COST INCURRED BY DATA BREACHES, 2014�2020 (USD MILLION)
FIGURE 21 SECURITY AND VULNERABILITY MANAGEMENT MARKET: ECOSYSTEM
FIGURE 22 MARKET: SUPPLY CHAIN
FIGURE 23 MARKET: PATENT ANALYSIS
FIGURE 24 MARKET: TRENDS AND DISRUPTIONS IMPACTING CUSTOMERS
FIGURE 25 PORTER�S FIVE FORCES ANALYSIS: MARKET
FIGURE 26 SOFTWARE SEGMENT TO ACCOUNT FOR A LARGER MARKET SIZE DURING THE FORECAST PERIOD
FIGURE 27 NUMBER AND DISTRIBUTION OF COMMON VULNERABILITIES AND EXPOSURES , BY TYPE, 2019
FIGURE 28 API VULNERABILITIES TO BE THE FASTEST-GROWING SEGMENT DURING THE FORECAST PERIOD
FIGURE 29 CLOUD SEGMENT TO ACCOUNT FOR A LARGER MARKET SIZE DURING THE FORECAST PERIOD
FIGURE 30 LARGE ENTERPRISES SEGMENT TO ACCOUNT FOR A LARGER MARKET SIZE DURING THE FORECAST PERIOD
FIGURE 31 HEALTHCARE SEGMENT TO ACCOUNT FOR THE FASTEST-GROWING MARKET DURING THE FORECAST PERIOD
FIGURE 32 NORTH AMERICA: MARKET SNAPSHOT
FIGURE 33 ASIA PACIFIC: MARKET SNAPSHOT
FIGURE 34 REVENUE ANALYSIS OF TOP MARKET PLAYERS, 2018�2020 (USD MILLION)
FIGURE 35 MARKET EVALUATION FRAMEWORK: EXPANSIONS AND CONSOLIDATIONS IN THE SECURITY AND VULNERABILITY MANAGEMENT MARKET BETWEEN 2018 AND 2021
FIGURE 36 MARKET: REVENUE ANALYSIS
FIGURE 37 RANKING OF KEY MARKET PLAYERS
FIGURE 38 MARKET, COMPANY EVALUATION QUADRANT
FIGURE 39 COMPANY FOOTPRINT OF MAJOR PLAYERS IN THE MARKET
FIGURE 40 SECURITY AND VULNERABILITY MANAGEMENTMARKET, STARTUP/SME EVALUATION QUADRANT
FIGURE 41 IBM: COMPANY SNAPSHOT
FIGURE 42 AT&T: COMPANY SNAPSHOT
FIGURE 43 QUALYS: COMPANY SNAPSHOT
FIGURE 44 RAPID7: COMPANY SNAPSHOT
FIGURE 45 TENABLE: COMPANY SNAPSHOT
The study involved four major activities in estimating the current size of the security and vulnerability management market. Exhaustive secondary research was done to collect information related to the market. The next step was to validate these findings, assumptions, and sizing with industry experts across the value chain using primary research. Both top-down and bottom-up approaches were employed to estimate the complete market size. Thereafter, the market breakup and data triangulation procedures were used to estimate the size of the market segments and subsegments.
Secondary Research
The market size of companies offering security and vulnerability management solutions and services to various segments is based on the secondary data available through paid and unpaid sources and by analyzing the product portfolios of the major companies in the ecosystem and rating the companies based on their performance and quality. In the secondary research process, various sources were referred to, for identifying and collecting information for the study. The secondary sources included annual reports, press releases, and investor presentations of companies; white papers, journals, and certified publications; articles from recognized authors; directories; and databases.
Secondary research was mainly used to obtain key information about the industry�s supply chain, the total pool of key players, market classification and segmentation according to industry trends to the bottom-most level, regional markets, and key developments from both market- and technology-oriented perspectives, all of which were further validated by the primary sources.
Primary Research
In the primary research process, various primary sources were interviewed to obtain qualitative and quantitative information about the market. The primary sources from the supply side included various industry experts, including Chief Executive Officers (CEOs); Vice Presidents (VPs); directors from business development, marketing, product development/innovation teams, and corporate communications; and related key executives from cybersecurity vendors, such as Tenable, foreseeti, Pure Storage, Illusive Networks, and Ivanti; SIs; professional service providers and MSPs; industry associations; distributors; and key opinion leaders.
Primary interviews were conducted to gather insights, such as market statistics, data of revenue collected from products and services, market breakups, market size estimations, market forecasting, and data triangulation. Primary research also helped in understanding various trends related to technology, application, vertical, and region.
Following is the breakup of the primary respondent:

To know about the assumptions considered for the study, download the pdf brochure
Market Size Estimation
Both top-down and bottom-up approaches were used to estimate and validate the total size of the security and vulnerability management. These methods were also used extensively to estimate the size of various segments in the market. The research methodology used to estimate the market size includes the following:
- Key players in the market have been identified through extensive secondary research.
- In terms of value, the industry�s supply chain and market size have been determined through primary and secondary research processes.
- All percentage shares, splits, and breakups have been determined using secondary sources and verified through primary sources.
Data Triangulation
After arriving at the overall market size using the market size estimation processes as explained above, the market was split into several segments and subsegments. To complete the overall market engineering process and arrive at each market segment's exact statistics and subsegment, data triangulation, and market breakup procedures were employed, wherever applicable. The data was triangulated by studying various factors and trends from both the demand and supply sides.
Report Objectives
- To determine and forecast the global security and vulnerability management by component, deployment mode, organization size, vertical, and region from 2021 to 2026, and analyze the various macroeconomic and microeconomic factors that affect the market growth
- To forecast the market segments' size with respect to five main regions: North America, Europe, Asia Pacific (APAC), Middle East and Africa (MEA), and Latin America.
- To analyze each submarket with respect to individual growth trends, prospects, and contributions to the overall security and vulnerability management
- To provide detailed information about the major factors (drivers, restraints, opportunities, and challenges) influencing the growth of the security and vulnerability management
Available Customizations
With the given market data, MarketsandMarkets offers customizations as per the company�s specific needs. The following customization options are available for the report:
Geographic Analysis
- Further breakup of the APAC market into countries contributing 75% to the regional market size
- Further breakup of the North American market into countries contributing 75% to the regional market size
- Further breakup of the Latin American market into countries contributing 75% to the regional market size
- Further breakup of the MEA market into countries contributing 75% to the regional market size
- Further breakup of the European market into countries contributing 75% to the regional market size



 Generating Response ...
Generating Response ...





Growth opportunities and latent adjacency in Security and Vulnerability Management Market