Access Control as a Service Market (ACaaS) by Access Control Models(RBAC, DAC), Service Type (Hosted, Managed, Hybrid), Cloud Deployment (Public Cloud, Private Cloud), Vertical (Commercial, Residential, Government, Retail) Region - Global Forecast to 2027
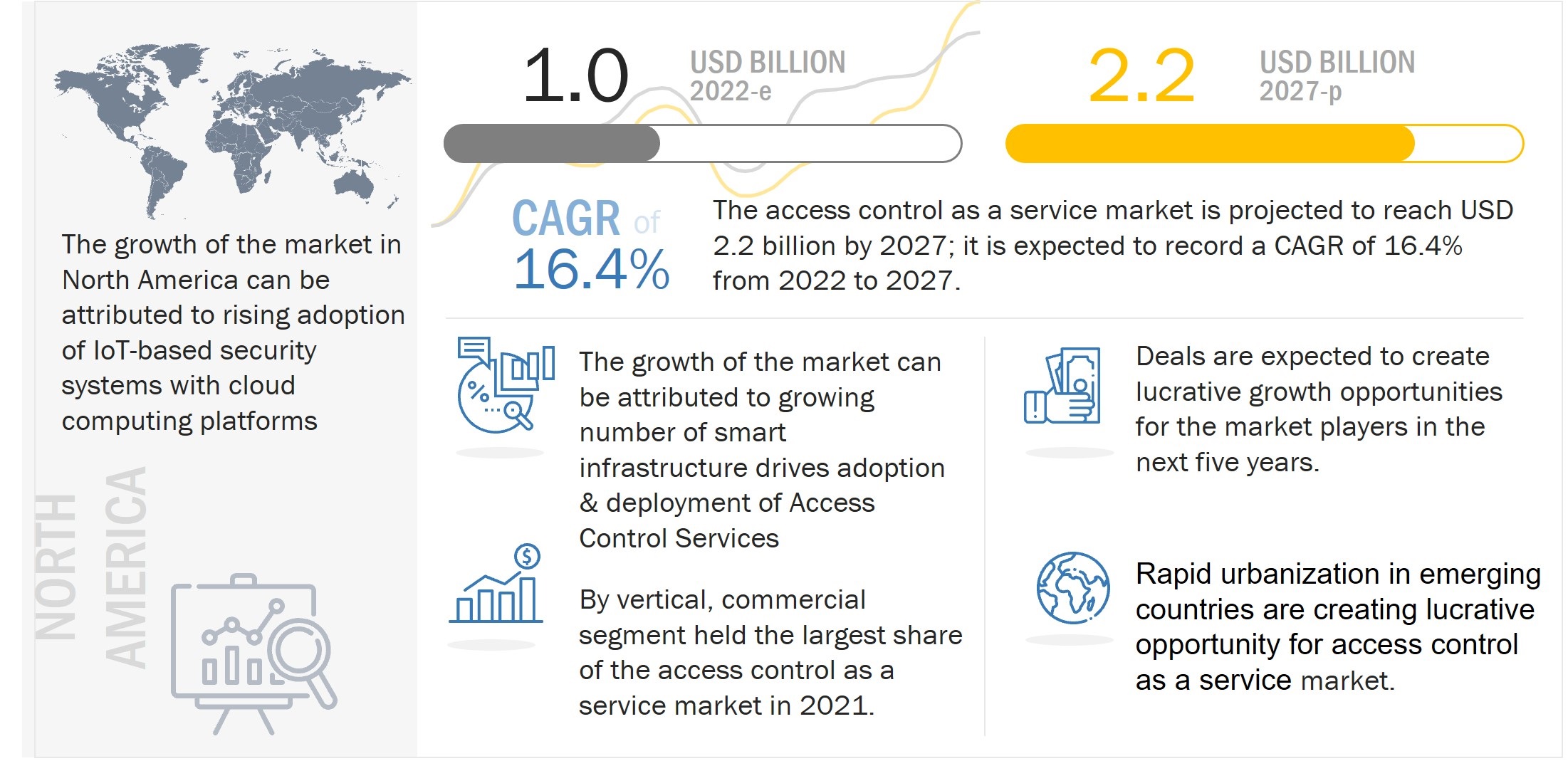
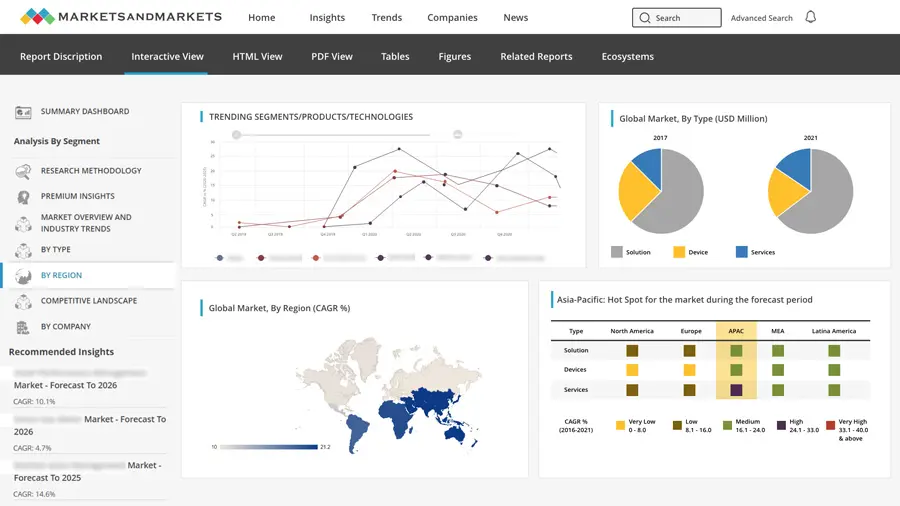
The access control as a service market was valued at USD 0.9 billion in 2021 and is projected to reach USD 2.2 billion by 2027, registering a CAGR of 16.4% during the forecast period. Growing number of smart infrastructure drives adoption & deployment of Access Control Services and Rising adoption of IoT-based security systems with cloud computing platforms are among the factors driving the growth of the access control as a service industry.
Access Control as a Service Market Forecast to 2027
To know about the assumptions considered for the study, Request for Free Sample Report
Market Dynamics:
Driver: Increased adoption of IoT-based security systems and cloud computing platforms
Cloud computing technology analyzes and stores data efficiently. This computing technology has servers that are connected to cloud platforms. This enables sharing of resources, which can be accessed at any place and time using the internet. Cloud Computing is an essential part of IoT which analyzes information obtained from the sensors, increases processing power, unites the servers, and provides good storage capacity. Cloud computing is integrated with smart objects which use many sensors and helps IoT for large-scale development. IoT depends on cloud computing and both computing technologies face security threats.
Restraint: Security and privacy concerns related to unauthorized access and data breach in access control environment
An inadequate access control causes intruders to gain unauthorized access to organizational data. Intruder breaching can be attributed directly to a lack of proper access control service. This breaching can be a cause of poor monitoring of the admin privileges within an organization. Also, the third-party applications used inside the organization can introduce vulnerabilities and security breaches. An attacker can easily utilize these loopholes to breach critical organizational data. In most industries, physical and logical security are separate departments as their requirements and approaches are different. An access control service is always prone to threats from anyone with an intention to breach either physical or logical security. Even in the case of integrated IT and security systems, cyberattacks are common. Moreover, ACaaS being a completely cloud-based solution is prone to data breaches and cyberattacks. Any security concern, such as data breach and unauthorized access to resources, can lead to significant monetary and reputational losses. Weak authentication and abuse of access authority are the major reasons behind data breaches in ACaaS.
Opportunity: Adoption of ACaaS as a cost-effective and flexible solution
Access control as a service enhances end-user privacy, eliminates the need for developing complex implementation protocols, and offers data owners flexibility to switch among cloud providers or use multiple cloud providers concurrently. It relieves cloud providers from the burden of implementing complex security solutions and enables enterprises to deploy their specific access control mechanisms. Various organizations have adopted cloud-based ACaaS as there is an increase in businesses, staff, and devices. The shift from full security systems to cloud-based ACaaS has been highly successful for many organizations. According to a recent study published in January 2021 by Cynet, the cloud is the number one preferred security technology deployment strategy.
Challenge: Availability of free Access Control Services
Cloud service providers offer security as a service to organizations for managing their infrastructure and resources, helping them in cutting costs, and delivering services quickly and efficiently. A wide range of cloud services are offered by various vendors at discount prices and sometimes as bundled services for free. Additionally, free access control services are open to risks such as account or service hijacking, data loss or theft, insecure interfaces & APIs, and technology vulnerabilities, especially in shared environments. Owing to this, the availability of free access control services hampers the growth rate in access control as a service market.
By service type, hybrid service segment is expected to grow with the second highest CAGR during the forecast period
The hybrid service segment is anticipated to record the second highest CAGR of 17.3% during the forecast period. In this model, the permissions are not associated directly to the attributes or the roles. These attributes are adopted for authentication purposes and assigning the roles to users according to attributes provided by the user through dynamic role assignment. Hybrid access controls service helps to improve threat visibility and help swiftly respond to attacks is an effective way to minimize cyber security risk and ensure compliance with the latest regulations and standards.
By cloud deployment model, CHP plant segment is expected to grow with the highest CAGR during the forecast period
The private cloud segment of the ACaaS market is expected to grow at the second highest CAGR of 15.4% during the forecast period. Public clouds are the most common type of cloud computing deployment. With a public cloud, all hardware, software, and other supporting infrastructure are owned and managed by the cloud provider. The public cloud makes it possible for anybody to access systems and services. The public cloud may be less secure as it is open for everyone. The public cloud is one in which cloud infrastructure services are provided over the internet to the general people or major industry groups. It is a type of cloud hosting that allows customers and users to easily access systems and services.
By vertical, retail segment is expected to grow with the second highest CAGR during the forecast period
The retail segment is expected to witness the highest CAGR of 18.0% during the forecast period. In retail sector, it is crucial to ensure workplace safety, prevent business interruption, and avoid financial loss. The number of retail stores and malls in urban areas has increased drastically over the last few years. Investing in access control as a service to meet the security needs provides numerous long-term benefits, such as a reduction in retail losses, maximization of store profits, and, most importantly, curtailment of threats. Retail shops and malls are more prone to security risks, such as theft and inventory loss, compared to other business properties or facilities.
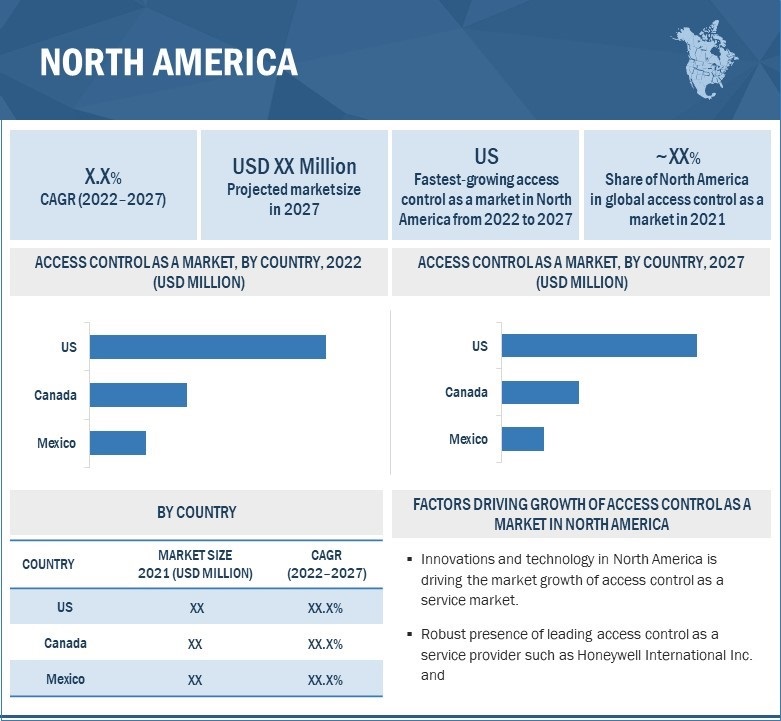
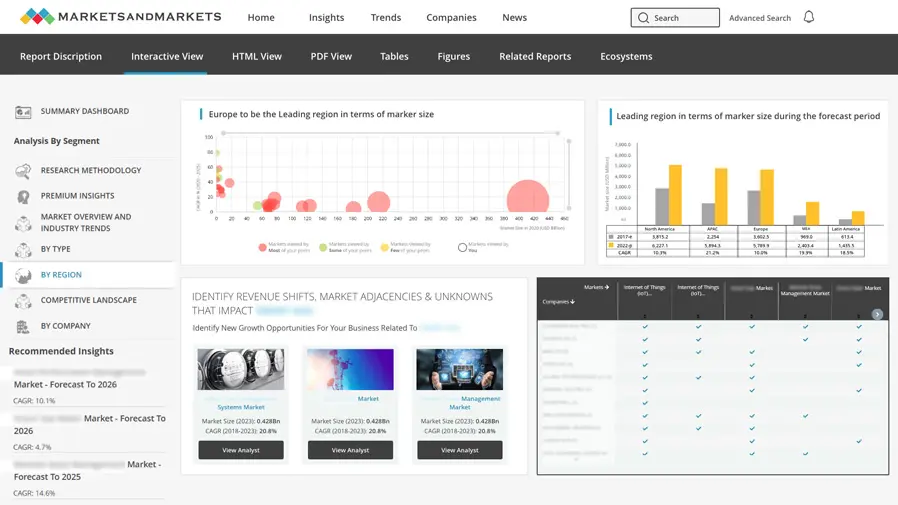
In 2027, North America is projected to hold the largest share of the overall access control as a service market
Access Control as a Service Market by Region
To know about the assumptions considered for the study, download the pdf brochure
North America is expected to hold the largest share of ~58% in the access control as a service market in 2027. The market growth in this region is at peak due to the strong presence of key ACaaS ecosystem players such as Honeywell International Inc., Identiv, Inc., Kastle Systems, AMAG Technology, Inc., Brivo Inc., and Cloudastructure, Inc. In North America, organizations use ACaaS owing to its inherent cyber-risk management capabilities. This enables organizations to focus on their core business goals and reduce unnecessary expenditures, while all risk management responsibilities are handled by ACaaS solutions. This provides them with a greater competitive advantage to increase their share in the ACaaS market in the region. The market growth in this region is attributed to the increasing constructions and demand for security products across the region.
Key Market Players
The access control as a service companies such as Johnson Controls (Ireland), Honeywell Security (US), Thales (France), Assa ABLOY AB (Sweden), and dormakaba Holding AG (Switzerland) Identiv, Inc. (US), Kastle Systems (US), AMAG Technology, Inc. (US), Brivo Inc. (US), Cloudastructure Inc. (US) are some of the key players in the access control as a service market.
Get online access to the report on the World's First Market Intelligence Cloud
- Easy to Download Historical Data & Forecast Numbers
- Company Analysis Dashboard for high growth potential opportunities
- Research Analyst Access for customization & queries
- Competitor Analysis with Interactive dashboard
- Latest News, Updates & Trend analysis
Request Sample Scope of the Report
Get online access to the report on the World's First Market Intelligence Cloud
- Easy to Download Historical Data & Forecast Numbers
- Company Analysis Dashboard for high growth potential opportunities
- Research Analyst Access for customization & queries
- Competitor Analysis with Interactive dashboard
- Latest News, Updates & Trend analysis
|
Report Metric |
Details |
| Estimated Value | USD 0.9 billion in 2021 |
| Projected Value | USD 2.2 billion by 2027 |
| Growth Rate | CAGR of 16.4% |
|
Market Size Availability for Years |
2018–2027 |
|
Base Year |
2021 |
|
Forecast Period |
2022–2027 |
|
Forecast Units |
Value (USD) |
|
Segments Covered |
Access control models, by service type, by cloud deployment model, vertical, and region |
|
Geographies Covered |
North America, Europe, Asia Pacific, and RoW |
|
Companies Covered |
Johnson Controls (Ireland), Honeywell Security (US), Thales (France), Assa ABLOY AB (Sweden), and dormakaba Holding AG (Switzerland) Identiv, Inc. (US), Kastle Systems (US), AMAG Technology, Inc. (US), Brivo Inc. (US), Cloudastructure Inc. (US) are some of the key players in the access control as a service market. |
Access Control as a Service Market Highlights
This research report categorizes the access control as a service market based on by service type, by cloud deployment model, vertical, and region.
|
Aspect |
Details |
|
Access Control Models |
|
|
By Service Type |
|
|
By Cloud Deployment Model |
|
|
By Vertical |
|
|
By Region |
|
Recent Developments
- In August 2022, ASSA ABLOY acquired Alcea, a provider of security monitoring software and associated access control hardware that provides entire access management solutions in collaboration with system partners. The partnership intends to strengthen its offering in critical infrastructure while also providing complementary development prospects.
- In July 2022, Thales acquired OneWelcome, a provider of cloud-based customer identity and access management solutions for highly regulated industries, empowering them to securely connect customers as well as business partners to their online services. With this acquisition, Thales will add to it digital identity & security product portfolio.
- In September 2021, Kastle Systems launched KastlePark, a cloud-based software that integrates office building and parking garage access management into one synchronized system. KastlePark enables building management, tenants, and office workers to control and simplify both the access control and billing processes of a property’s parking operation.
Frequently Asked Questions (FAQs):
Which are the major companies in the access control as a service market? What are their major strategies to strengthen their market presence?
The major companies in the access control as a service market are – Johnson Controls (Ireland), Honeywell Security (US), Thales (France), Assa Abloy AB (Sweden), and dormakaba Holding AG (Switzerland) Identiv, Inc. (US), Kastle Systems (US), AMAG Technology, Inc. (US), Brivo Inc. (US), Cloudastructure Inc. (US) are some of the key players in the access control as a service market. The major strategies adopted by these players are partnership and acquisitions.
Which is the potential market for ACaaS in terms of the region?
North America region is expected to dominate the access control as a service market owing to the high demand of ACaaS.
Who are the winners in the global access control as a service market?
Companies such as Johnson Controls (Ireland) and Honeywell Security (US), fall under the winner’s category. These companies cater to the requirements of their customers by providing ACaaS. Moreover, these companies are highly adopting inorganic growth strategies to strengthen their market position and customer base worldwide.
What are the drivers and opportunities for the access control as a service market?
Factors such as rising adoption of IoT-based security systems with cloud computing platforms and growing urbanization and growing number of smart infrastructure drives adoption & deployment of Access Control Services.
To speak to our analyst for a discussion on the above findings, click Speak to Analyst
TABLE OF CONTENTS
1 INTRODUCTION (Page No. - 25)
1.1 STUDY OBJECTIVES
1.2 MARKET DEFINITION
1.2.1 INCLUSIONS AND EXCLUSIONS
1.3 STUDY SCOPE
1.3.1 MARKETS COVERED
FIGURE 1 ACCESS CONTROL AS A SERVICE MARKET SEGMENTATION
1.3.2 GEOGRAPHIC SCOPE
1.3.3 YEARS CONSIDERED
1.4 CURRENCY CONSIDERED
1.5 STAKEHOLDERS
1.6 SUMMARY OF CHANGES
2 RESEARCH METHODOLOGY (Page No. - 29)
2.1 RESEARCH DATA
FIGURE 2 ACCESS CONTROL AS A SERVICE MARKET: RESEARCH DESIGN
2.1.1 SECONDARY AND PRIMARY RESEARCH
2.1.2 SECONDARY DATA
2.1.2.1 List of key secondary sources
2.1.2.2 Key data from secondary sources
2.1.3 PRIMARY DATA
2.1.3.1 List of key primary interview participants
2.1.4 BREAKDOWN OF PRIMARIES
FIGURE 3 BREAKDOWN OF PRIMARIES
2.1.4.1 Key data from primary sources
2.1.5 KEY INDUSTRY INSIGHTS
2.2 FACTOR ANALYSIS
2.2.1 SUPPLY-SIDE ANALYSIS
FIGURE 4 MARKET SIZE ESTIMATION METHODOLOGY: APPROACH 1 (SUPPLY-SIDE ANALYSIS) – REVENUES GENERATED BY COMPANIES FROM SALES OF PRODUCTS OFFERED IN ACCESS CONTROL AS A SERVICE MARKET
FIGURE 5 MARKET SIZE ESTIMATION METHODOLOGY: APPROACH 1 (TOP-DOWN, SUPPLY-SIDE) – ILLUSTRATION OF REVENUE ESTIMATION FOR ONE COMPANY IN ACCESS CONTROL AS A SERVICE MARKET
2.3 MARKET SIZE ESTIMATION
FIGURE 6 MARKET SIZE ESTIMATION METHODOLOGY: SUPPLY-SIDE ANALYSIS
2.3.1 BOTTOM-UP APPROACH
2.3.1.1 Approach to estimate market share using bottom-up analysis (demand side)
FIGURE 7 MARKET SIZE ESTIMATION METHODOLOGY: BOTTOM-UP APPROACH
2.3.2 TOP-DOWN APPROACH
2.3.2.1 Approach to estimate market share using top-down analysis (supply side)
FIGURE 8 MARKET SIZE ESTIMATION METHODOLOGY: TOP-DOWN APPROACH
2.3.3 GROWTH PROJECTION AND FORECASTING ASSUMPTIONS
TABLE 1 MARKET GROWTH ASSUMPTIONS
2.4 MARKET BREAKDOWN AND DATA TRIANGULATION
FIGURE 9 ACCESS CONTROL AS A SERVICE MARKET: DATA TRIANGULATION
2.5 RESEARCH ASSUMPTIONS
TABLE 2 KEY ASSUMPTIONS: MACRO AND MICRO-ECONOMIC ENVIRONMENT
2.6 RESEARCH LIMITATIONS
2.7 RISK ASSESSMENT
TABLE 3 RISK ASSESSMENT: ACCESS CONTROL AS A SERVICE MARKET
3 EXECUTIVE SUMMARY (Page No. - 42)
FIGURE 10 RETAIL VERTICAL SEGMENT PROJECTED TO GROW AT HIGHEST CAGR DURING FORECAST PERIOD
FIGURE 11 MANAGED SERVICES SEGMENT TO RECORD HIGHEST CAGR DURING FORECAST PERIOD
FIGURE 12 NORTH AMERICA TO LEAD ACCESS CONTROL AS A SERVICE MARKET FROM 2022 TO 2027
4 PREMIUM INSIGHTS (Page No. - 45)
4.1 ATTRACTIVE GROWTH OPPORTUNITIES FOR PLAYERS IN ACCESS CONTROL AS A SERVICE MARKET
FIGURE 13 GROWING ADOPTION OF ACAAS TO COUNTER THREATS DRIVES MARKET GROWTH
4.2 ACCESS CONTROL AS A SERVICE MARKET, BY APPLICATION
FIGURE 14 PRIVATE CLOUD SEGMENT TO WITNESS HIGHEST CAGR DURING FORECAST PERIOD
4.3 ACCESS CONTROL AS A SERVICE MARKET, BY REGION
FIGURE 15 NORTH AMERICA TO HOLD LARGEST SHARE OF ACCESS CONTROL AS A SERVICE MARKET IN 2022
4.4 ACCESS CONTROL AS A SERVICE MARKET, BY COUNTRY
FIGURE 16 CHINA TO WITNESS HIGHEST GROWTH IN OVERALL ACCESS CONTROL AS A SERVICE MARKET
5 MARKET OVERVIEW (Page No. - 47)
5.1 INTRODUCTION
5.2 MARKET DYNAMICS
FIGURE 17 ACCESS CONTROL AS A SERVICE MARKET: DRIVERS, RESTRAINTS, OPPORTUNITIES, AND CHALLENGES
5.2.1 DRIVERS
5.2.1.1 Increased adoption of IoT-based security systems and cloud computing platforms
5.2.1.2 Rising number of smart infrastructure and smart city projects
5.2.1.3 Adoption of ACaaS for centralized operations by businesses that operate at multiple locations
FIGURE 18 DRIVERS AND THEIR IMPACT ON ACCESS CONTROL AS A SERVICE MARKET
5.2.2 RESTRAINTS
5.2.2.1 Security and privacy concerns related to unauthorized access and data breach in access control environment
FIGURE 19 RESTRAINTS AND THEIR IMPACT ON ACCESS CONTROL AS A SERVICE MARKET
5.2.3 OPPORTUNITIES
5.2.3.1 Rapid urbanization in emerging countries
5.2.3.2 Adoption of ACaaS as cost-effective and flexible solution
FIGURE 20 OPPORTUNITIES AND THEIR IMPACT ON ACCESS CONTROL AS A SERVICE MARKET
5.2.4 CHALLENGES
5.2.4.1 Availability of free access control services
FIGURE 21 CHALLENGES AND THEIR IMPACT ON ACCESS CONTROL AS A SERVICE MARKET
5.3 SUPPLY CHAIN ANALYSIS
FIGURE 22 SUPPLY CHAIN OF ACCESS CONTROL AS A SERVICE MARKET
TABLE 4 ACCESS CONTROL AS A SERVICE MARKET: ECOSYSTEM
5.3.1 REVENUE SHIFT AND NEW REVENUE POCKETS FOR PLAYERS IN ACCESS CONTROL AS A SERVICE MARKET
FIGURE 23 REVENUE SHIFT IN ACCESS CONTROL AS A SERVICE MARKET
5.4 ACCESS CONTROL AS A SERVICE MARKET ECOSYSTEM
FIGURE 24 ECOSYSTEM OF ACCESS CONTROL AS A SERVICE
5.5 AVERAGE SELLING PRICE ANALYSIS
5.5.1 AVERAGE SELLING PRICES OF ACCESS CONTROL AS A SERVICE PRODUCTS, KEY PLAYER
FIGURE 25 AVERAGE SELLING PRICE OF ACCESS CONTROL AS A SERVICE PRODUCTS, BY KEY PLAYER
TABLE 5 AVERAGE SELLING PRICE OF ACCESS CONTROL AS A SERVICE PRODUCTS, BY KEY PLAYER (USD/MONTH)
5.5.2 AVERAGE SELLING PRICE TREND
TABLE 6 AVERAGE PRICES: ACCESS CONTROL AS A SERVICE MARKET, BY SERVICE TYPE (USD/MONTH)
FIGURE 26 AVERAGE PRICE: ACCESS CONTROL AS A SERVICE MARKET, BY SERVICE TYPE (USD/MONTH)
5.6 TECHNOLOGY TRENDS
5.6.1 COMPLEMENTARY TECHNOLOGIES
5.6.2 VIDEO ANALYTICS CAMERAS
5.6.3 CLOUD-BASED CAMERAS IN ACCESS CONTROL SYSTEMS
5.6.4 INTEGRATION OF IOT
5.6.5 EMERGENCE OF CONTACTLESS BIOMETRICS
5.6.6 FACIAL RECOGNITION TECHNOLOGY (FACE RECOGNITION CAMERAS)
5.6.7 ADJACENT TECHNOLOGIES
5.6.7.1 Comprehensive and proactive security systems
5.7 PORTER’S FIVE FORCES ANALYSIS
TABLE 7 ACCESS CONTROL AS A SERVICE MARKET: PORTER’S FIVE FORCES ANALYSIS
FIGURE 27 PORTER’S FIVE FORCES ANALYSIS
5.7.1 THREAT OF NEW ENTRANTS
5.7.2 THREAT OF SUBSTITUTES
5.7.3 BARGAINING POWER OF SUPPLIERS
5.7.4 BARGAINING POWER OF BUYERS
5.7.5 INTENSITY OF COMPETITIVE RIVALRY
5.8 KEY STAKEHOLDERS AND BUYING CRITERIA
5.8.1 KEY STAKEHOLDERS IN BUYING PROCESS
FIGURE 28 INFLUENCE OF STAKEHOLDERS IN BUYING PROCESS FOR TOP SERVICES
TABLE 8 INFLUENCE OF STAKEHOLDERS ON BUYING PROCESS FOR TOP SERVICES (%)
5.8.2 BUYING CRITERIA
FIGURE 29 KEY BUYING CRITERIA FOR TOP THREE VERTICALS
TABLE 9 KEY BUYING CRITERIA FOR TOP THREE VERTICALS
5.9 CASE STUDY ANALYSIS
5.9.1 KASTLE’S CLOUD-BASED VIDEO SURVEILLANCE SYSTEM SECURES WHARF
5.9.2 SYMMETRY ENABLED CITY OF HOBBS TO TAP INTO VIDEO SECURITY SYSTEMS IN SCHOOLS
5.9.3 MONROE COUNTY USED MAXPRO CLOUD FOR BENEFIT OF ITS COMMUNITY WITHOUT COMPROMISING SAFETY
5.9.4 BUSINESS OWNER CONTROLS TWO FLOORS, STAFF OF 80, AND MULTIPLE VENDORS VIA CLOUD-BASED SECURITY SOLUTION
5.10 TRADE ANALYSIS
5.10.1 IMPORT SCENARIO
TABLE 10 IMPORT DATA, BY COUNTRY, 2017–2021 (USD BILLION)
5.10.2 EXPORT SCENARIO
TABLE 11 EXPORT DATA, BY COUNTRY, 2017–2021 (USD BILLION)
5.11 PATENT ANALYSIS, 2012–2022
FIGURE 30 NUMBER OF PATENTS GRANTED FOR ACCESS CONTROL AS A SERVICE PRODUCTS, 2012–2022
FIGURE 31 REGIONAL ANALYSIS OF PATENTS GRANTED FOR ACCESS CONTROL AS A SERVICE SOLUTIONS, 2021
TABLE 12 LIST OF SOME PATENTS PERTAINING TO ACCESS CONTROL AS A SERVICE, 2020–2021
5.12 KEY CONFERENCES AND EVENTS, 2022–2023
TABLE 13 ACCESS CONTROL AS A SERVICE MARKET: DETAILED LIST OF CONFERENCES AND EVENTS
5.13 TARIFF ANALYSIS
TABLE 14 MFN TARIFF FOR HS CODE 854370 - COMPLIANT PRODUCTS EXPORTED BY US
TABLE 15 MFN TARIFF FOR HS CODE 854370 - COMPLIANT PRODUCTS EXPORTED BY CHINA
TABLE 16 MFN TARIFF FOR HS CODE 854370 - COMPLIANT PRODUCTS EXPORTED BY INDIA
5.14 STANDARDS AND REGULATORY LANDSCAPE
5.14.1 REGULATORY BODIES, GOVERNMENT AGENCIES, AND OTHER ORGANIZATIONS
TABLE 17 NORTH AMERICA: LIST OF REGULATORY BODIES, GOVERNMENT AGENCIES, AND OTHER ORGANIZATIONS
TABLE 18 EUROPE: LIST OF REGULATORY BODIES, GOVERNMENT AGENCIES, AND OTHER ORGANIZATIONS
TABLE 19 ASIA PACIFIC: LIST OF REGULATORY BODIES, GOVERNMENT AGENCIES, AND OTHER ORGANIZATIONS
TABLE 20 ROW: LIST OF REGULATORY BODIES, GOVERNMENT AGENCIES, AND OTHER ORGANIZATIONS
5.14.2 REGULATORY STANDARDS
5.14.3 GOVERNMENT REGULATIONS
5.14.3.1 Canada
5.14.3.2 Europe
5.14.3.3 India
6 ACCESS CONTROL MODELS (Page No. - 77)
6.1 INTRODUCTION
6.2 DISCRETIONARY ACCESS CONTROL (DAC)
6.2.1 CONTROLS DEFINED BY USER IDENTIFICATION AND CREDENTIALS
6.3 MANDATORY ACCESS CONTROL (MAC)
6.3.1 MAC IS CONSIDERED MOST SECURE ACCESS CONTROL MODEL
6.4 ROLE-BASED ACCESS CONTROL (RBAC)
6.4.1 RBAC HELPS IN SECURING SENSITIVE DATA AND IMPORTANT APPLICATIONS
6.5 RULE-BASED ACCESS CONTROL
6.5.1 PERSONALIZED ACCESS CAN BE GIVEN BASED ON USER ROLE IN ORGANIZATION
6.6 ATTRIBUTE-BASED ACCESS CONTROL
6.6.1 ABAC CAN CONTROL ACCESS BASED ON THREE DIFFERENT ATTRIBUTE TYPES
6.7 RISK-ADAPTIVE ACCESS CONTROL
6.7.1 MODEL ALLOWS SYSTEM TO ADAPT TO THREATS
6.8 IDENTITY-BASED ACCESS CONTROL (IBAC)
6.8.1 GRANTS ACCESS BASED ON IDENTITY OF USERS
7 ACCESS CONTROL AS A SERVICE MARKET, BY SERVICE TYPE (Page No. - 81)
7.1 INTRODUCTION
FIGURE 32 HOSTED SERVICES PROJECTED TO BE LARGEST TYPE SEGMENT IN 2027
TABLE 21 ACAAS MARKET, BY SERVICE TYPE, 2018–2021 (USD MILLION)
TABLE 22 ACAAS MARKET, BY SERVICE TYPE, 2022–2027 (USD MILLION)
7.2 HOSTED SERVICES
7.2.1 QUICK, EASY, AND EFFICIENT ACCESS CONTROL
TABLE 23 HOSTED SERVICES: ACAAS MARKET, BY VERTICAL, 2018–2021 (USD MILLION)
TABLE 24 HOSTED SERVICES: ACAAS MARKET, BY VERTICAL, 2022–2027 (USD MILLION)
7.3 MANAGED SERVICES
7.3.1 THIRD-PARTY PAID BY END USERS TO MANAGE ACCESS CONTROL PLATFORM
TABLE 25 MANAGED SERVICES: ACAAS MARKET, BY VERTICAL, 2018–2021 (USD MILLION)
TABLE 26 MANAGED SERVICES: ACAAS MARKET, BY VERTICAL, 2022–2027 (USD MILLION)
7.4 HYBRID SERVICES
7.4.1 COMBINATION OF HOSTED AND MANAGED ACCESS CONTROL
TABLE 27 HYBRID SERVICES: ACAAS MARKET, BY VERTICAL, 2018–2021 (USD MILLION)
TABLE 28 HYBRID SERVICES: ACAAS MARKET, BY VERTICAL, 2022–2027 (USD MILLION)
8 ACCESS CONTROL AS A SERVICE MARKET, BY CLOUD DEPLOYMENT MODEL (Page No. - 87)
8.1 INTRODUCTION
FIGURE 33 PUBLIC CLOUD PROJECTED TO BE LARGEST SEGMENT IN 2027
TABLE 29 ACAAS MARKET, BY CLOUD DEPLOYMENT MODEL, 2018–2021 (USD MILLION)
TABLE 30 ACAAS MARKET, BY CLOUD DEPLOYMENT MODEL, 2022–2027 (USD MILLION)
8.2 PUBLIC CLOUD
8.2.1 AUTHORIZATION COMPLETELY CONTROLLED BY DATA OWNER
8.3 PRIVATE CLOUD
8.3.1 SINGLE TENANT CLOUD ARCHITECTURE
8.4 HYBRID CLOUD
8.4.1 PROVIDES FLEXIBILITY OF USING EITHER PRIVATE OR PUBLIC CLOUD, DEPENDING ON COMPUTING NEEDS AND CHANGES IN COST
9 ACCESS CONTROL AS A SERVICE MARKET, BY VERTICAL (Page No. - 91)
9.1 INTRODUCTION
FIGURE 34 ACCESS CONTROL AS A SERVICE MARKET, BY VERTICAL
FIGURE 35 COMMERCIAL EXPECTED TO BE LARGEST VERTICAL SEGMENT DURING FORECAST PERIOD
TABLE 31 ACAAS MARKET, BY VERTICAL, 2018–2021 (USD MILLION)
TABLE 32 ACAAS MARKET, BY VERTICAL, 2022–2027 (USD MILLION)
9.2 COMMERCIAL
9.2.1 ACAAS ENABLES ORGANIZATIONS TO STREAMLINE AND MERGE THEIR SECURITY OPERATIONS SEAMLESSLY
TABLE 33 COMMERCIAL: ACAAS MARKET, BY SERVICE TYPE, 2018–2021 (USD MILLION)
TABLE 34 COMMERCIAL: ACAAS MARKET, BY SERVICE TYPE, 2022–2027 (USD MILLION)
TABLE 35 COMMERCIAL: ACAAS MARKET, BY REGION, 2018–2021 (USD MILLION)
TABLE 36 COMMERCIAL: ACAAS MARKET, BY REGION, 2022–2027 (USD MILLION)
9.3 MANUFACTURING AND INDUSTRIAL
9.3.1 NEED FOR SAFETY AND IMPROVED PRODUCTIVITY IN MANUFACTURING AND INDUSTRIAL VERTICAL CREATING DEMAND FOR ACAAS
TABLE 37 MANUFACTURING AND INDUSTRIAL: ACAAS MARKET, BY SERVICE TYPE, 2018–2021 (USD MILLION)
TABLE 38 MANUFACTURING AND INDUSTRIAL: ACAAS MARKET, BY SERVICE TYPE, 2022–2027 (USD MILLION)
TABLE 39 MANUFACTURING AND INDUSTRIAL: ACAAS MARKET, BY REGION, 2018–2021 (USD MILLION)
TABLE 40 MANUFACTURING AND INDUSTRIAL: ACAAS MARKET, BY REGION, 2022–2027 (USD MILLION)
9.4 GOVERNMENT
9.4.1 ACAAS DEPLOYED TO PROVIDE SECURITY TO GOVERNMENT ASSETS AND VALUABLE INFORMATION
TABLE 41 GOVERNMENT: ACAAS MARKET, BY SERVICE TYPE, 2018–2021 (USD MILLION)
TABLE 42 GOVERNMENT: ACAAS MARKET, BY SERVICE TYPE, 2022–2027 (USD MILLION)
TABLE 43 GOVERNMENT: ACAAS MARKET, BY REGION, 2018–2021 (USD MILLION)
TABLE 44 GOVERNMENT: ACAAS MARKET, BY REGION, 2022–2027 (USD MILLION)
9.5 HEALTHCARE
9.5.1 ACAAS ADOPTED IN HEALTHCARE TO ENSURE PATIENT PRIVACY
TABLE 45 HEALTHCARE: ACAAS MARKET, BY SERVICE TYPE, 2018–2021 (USD MILLION)
TABLE 46 HEALTHCARE: ACAAS MARKET, BY SERVICE TYPE, 2022–2027 (USD MILLION)
TABLE 47 HEALTHCARE: ACAAS MARKET, BY REGION, 2018–2021 (USD MILLION)
TABLE 48 HEALTHCARE: ACAAS MARKET, BY REGION, 2022–2027 (USD MILLION)
9.6 EDUCATION
9.6.1 ACAAS ENABLES EDUCATIONAL PREMISES TO RESTRICT, CONTROL, AND MONITOR MOVEMENT OF PEOPLE AND VEHICLES
TABLE 49 EDUCATION: ACAAS MARKET, BY SERVICE TYPE, 2018–2021 (USD MILLION)
TABLE 50 EDUCATION: ACAAS MARKET, BY SERVICE TYPE, 2022–2027 (USD MILLION)
TABLE 51 EDUCATION: ACAAS MARKET, BY REGION, 2018–2021 (USD MILLION)
TABLE 52 EDUCATION: ACAAS MARKET, BY REGION, 2022–2027 (USD MILLION)
9.7 RESIDENTIAL
9.7.1 ACAAS KEEPS UNKNOWN PARTIES OUT AND SENDS ALERTS TO SECURITY PERSONNEL
TABLE 53 RESIDENTIAL: ACAAS MARKET, BY SERVICE TYPE, 2018–2021 (USD MILLION)
TABLE 54 RESIDENTIAL: ACAAS MARKET, BY SERVICE TYPE, 2022–2027 (USD MILLION)
TABLE 55 RESIDENTIAL: ACAAS MARKET, BY REGION, 2018–2021 (USD MILLION)
TABLE 56 RESIDENTIAL: ACAAS MARKET, BY REGION, 2022–2027 (USD MILLION)
9.8 TRANSPORTATION
9.8.1 ACAAS REDUCES RISK OF ORGANIZED CRIMES
TABLE 57 TRANSPORTATION: ACAAS MARKET, BY SERVICE TYPE, 2018–2021 (USD MILLION)
TABLE 58 TRANSPORTATION: ACAAS MARKET, BY SERVICE TYPE, 2022–2027 (USD MILLION)
TABLE 59 TRANSPORTATION: ACAAS MARKET, BY REGION, 2018–2021 (USD MILLION)
TABLE 60 TRANSPORTATION: ACAAS MARKET, BY REGION, 2022–2027 (USD MILLION)
9.9 RETAIL
9.9.1 RISE IN NUMBER OF RETAIL STORES INCREASES USE OF ACAAS
TABLE 61 RETAIL: ACAAS MARKET, BY SERVICE TYPE, 2018–2021 (USD MILLION)
TABLE 62 RETAIL: ACAAS MARKET, BY SERVICE TYPE, 2022–2027 (USD MILLION)
TABLE 63 RETAIL: ACAAS MARKET, BY REGION, 2018–2021 (USD MILLION)
TABLE 64 RETAIL: ACAAS MARKET, BY REGION, 2022–2027 (USD MILLION)
10 ACCESS CONTROL AS A SERVICE MARKET, BY REGION (Page No. - 107)
10.1 INTRODUCTION
FIGURE 36 NORTH AMERICA PROJECTED TO OCCUPY LARGEST MARKET SHARE IN 2027
TABLE 65 ACCESS CONTROL AS A SERVICE MARKET, BY REGION, 2018–2021 (USD MILLION)
TABLE 66 ACCESS CONTROL AS A SERVICE MARKET, BY REGION, 2022–2027 (USD MILLION)
10.2 NORTH AMERICA
FIGURE 37 NORTH AMERICA: SNAPSHOT OF ACCESS CONTROL AS A MARKET
TABLE 67 NORTH AMERICA: ACCESS CONTROL AS A SERVICE MARKET, BY COUNTRY, 2018–2021 (USD MILLION)
TABLE 68 NORTH AMERICA: ACCESS CONTROL AS A SERVICE MARKET, BY COUNTRY, 2022–2027 (USD MILLION)
TABLE 69 NORTH AMERICA: ACCESS CONTROL AS A SERVICE MARKET, BY VERTICAL, 2018–2021 (USD MILLION)
TABLE 70 NORTH AMERICA: ACCESS CONTROL AS A SERVICE MARKET, BY VERTICAL, 2022–2027 (USD MILLION)
10.2.1 US
10.2.1.1 ACaaS widely adopted for security and maintenance purposes
10.2.2 CANADA
10.2.2.1 ACaaS paving way to advanced security solutions that enable access to confidential data
10.2.3 MEXICO
10.2.3.1 ACaaS used to maintain political stability through integrated security systems
10.3 EUROPE
FIGURE 38 EUROPE: SNAPSHOT OF ACCESS CONTROL AS A MARKET
TABLE 71 EUROPE: ACCESS CONTROL AS A SERVICE MARKET, BY COUNTRY, 2018–2021 (USD MILLION)
TABLE 72 EUROPE: ACCESS CONTROL AS A SERVICE MARKET, BY COUNTRY, 2022–2027 (USD MILLION)
TABLE 73 EUROPE: ACCESS CONTROL AS A SERVICE MARKET, BY VERTICAL, 2018–2021 (USD MILLION)
TABLE 74 EUROPE: ACCESS CONTROL AS A SERVICE MARKET, BY VERTICAL, 2022–2027 (USD MILLION)
10.3.1 UK
10.3.1.1 ACaaS enables remote and effective security of premises
10.3.2 GERMANY
10.3.2.1 Privacy laws have augmented demand for ACaaS
10.3.3 FRANCE
10.3.3.1 ACaaS deployed in aviation and railways
10.3.4 REST OF EUROPE
10.4 ASIA PACIFIC
FIGURE 39 ASIA PACIFIC: SNAPSHOT OF ACCESS CONTROL AS A MARKET
TABLE 75 ASIA PACIFIC: ACCESS CONTROL AS A SERVICE MARKET, BY COUNTRY, 2018–2021 (USD MILLION)
TABLE 76 ASIA PACIFIC: ACCESS CONTROL AS A SERVICE MARKET, BY COUNTRY, 2022–2027 (USD MILLION)
TABLE 77 ASIA PACIFIC: ACCESS CONTROL AS A SERVICE MARKET, BY VERTICAL, 2018–2021 (USD MILLION)
TABLE 78 ASIA PACIFIC: ACCESS CONTROL AS A SERVICE MARKET, BY VERTICAL, 2022–2027 (USD MILLION)
10.4.1 CHINA
10.4.1.1 Large-scale industrialization led to growing need for security systems
10.4.2 JAPAN
10.4.2.1 Adoption of IoT and self-driving cars to drive ACaaS market
10.4.3 SOUTH KOREA
10.4.3.1 Increased incidences of unauthorized access to sensitive data drive market
10.4.4 INDIA
10.4.4.1 Rise in terrorist activities and data security breaches to drive market growth
10.4.5 REST OF ASIA PACIFIC
10.5 ROW
TABLE 79 ROW: ACCESS CONTROL AS A SERVICE MARKET, BY REGION, 2018–2021 (USD MILLION)
TABLE 80 ROW: ACCESS CONTROL AS A SERVICE MARKET, BY REGION, 2022–2027 (USD MILLION)
TABLE 81 ROW: ACCESS CONTROL AS A SERVICE MARKET, BY VERTICAL, 2018–2021 (USD MILLION)
TABLE 82 ROW: ACCESS CONTROL AS A SERVICE MARKET, BY VERTICAL, 2022–2027 (USD MILLION)
10.5.1 MIDDLE EAST & AFRICA (MEA)
10.5.1.1 Rise in government security initiatives to boost market
10.5.2 SOUTH AMERICA
10.5.2.1 High crime rate creates demand
11 COMPETITIVE LANDSCAPE (Page No. - 124)
11.1 OVERVIEW
11.2 MARKET EVALUATION FRAMEWORK
TABLE 83 OVERVIEW OF STRATEGIES DEPLOYED BY KEY ACCESS CONTROL AS A SERVICE COMPANIES
11.2.1 PRODUCT PORTFOLIO
11.2.2 REGIONAL FOCUS
11.2.3 MANUFACTURING FOOTPRINT
11.2.4 ORGANIC/INORGANIC STRATEGIES
11.3 MARKET SHARE ANALYSIS, 2021
TABLE 84 ACCESS CONTROL AS A SERVICE MARKET: MARKET SHARE ANALYSIS (2021)
11.4 FIVE-YEAR COMPANY REVENUE ANALYSIS
FIGURE 40 FIVE-YEAR REVENUE ANALYSIS OF TOP 5 PLAYERS IN ACCESS CONTROL AS A SERVICE MARKET, 2017 TO 2021
11.5 COMPANY EVALUATION QUADRANT
11.5.1 STAR
11.5.2 EMERGING LEADER
11.5.3 PERVASIVE
11.5.4 PARTICIPANT
FIGURE 41 ACCESS CONTROL AS A SERVICE MARKET: COMPANY EVALUATION QUADRANT, 2021
11.6 STARTUP/SMALL AND MEDIUM-SIZED ENTERPRISES (SME) EVALUATION MATRIX
TABLE 85 ACCESS CONTROL AS A SERVICE MARKET: DETAILED LIST OF KEY STARTUP/SMES
TABLE 86 STARTUP/SMES IN ACCESS CONTROL AS A SERVICE MARKET
TABLE 87 ACCESS CONTROL AS A SERVICE MARKET: COMPETITIVE BENCHMARKING OF KEY STARTUP/SMES (APPLICATION FOOTPRINT)
TABLE 88 ACCESS CONTROL AS A SERVICE MARKET: COMPETITIVE BENCHMARKING OF KEY STARTUP/SMES (REGION FOOTPRINT)
11.6.1 PROGRESSIVE COMPANY
11.6.2 RESPONSIVE COMPANY
11.6.3 DYNAMIC COMPANY
11.6.4 STARTING BLOCK
FIGURE 42 STARTUP/SME EVALUATION MATRIX
11.7 COMPANY FOOTPRINT
TABLE 89 COMPANY FOOTPRINT
TABLE 90 COMPANY-WISE SERVICE FOOTPRINT
TABLE 91 COMPANY-WISE APPLICATION FOOTPRINT
TABLE 92 COMPANY-WISE REGIONAL FOOTPRINT
11.8 COMPETITIVE SITUATIONS AND TRENDS
11.8.1 PRODUCT LAUNCHES
TABLE 93 PRODUCT LAUNCHES, JANUARY 2019–AUGUST 2022
11.8.2 DEALS
TABLE 94 DEALS, JANUARY 2019–AUGUST 2022
11.8.3 OTHERS
TABLE 95 OTHERS, JANUARY 2019–AUGUST 2022
12 COMPANY PROFILES (Page No. - 143)
(Business Overview, Solutions/Services Offered, Recent Developments, and MnM View (Key strengths/Right to Win, Strategic Choices Made, and Weaknesses and Competitive Threats))*
12.1 INTRODUCTION
12.2 KEY PLAYERS
12.2.1 JOHNSON CONTROLS
TABLE 96 JOHNSON CONTROLS: BUSINESS OVERVIEW
FIGURE 43 JOHNSON CONTROLS: COMPANY SNAPSHOT
TABLE 97 JOHNSON CONTROLS: SOLUTIONS/SERVICES OFFERINGS
TABLE 98 JOHNSON CONTROLS: PRODUCT LAUNCHES
12.2.2 HONEYWELL INTERNATIONAL INC.
TABLE 99 HONEYWELL INTERNATIONAL INC.: COMPANY SNAPSHOT
FIGURE 44 HONEYWELL INTERNATIONAL INC.: COMPANY SNAPSHOT
TABLE 100 HONEYWELL INTERNATIONAL INC.: SOLUTIONS/SERVICES OFFERINGS
TABLE 101 HONEYWELL INTERNATIONAL INC.: PRODUCT LAUNCHES
TABLE 102 HONEYWELL INTERNATIONAL INC.: DEALS
12.2.3 THALES
TABLE 103 THALES: COMPANY SNAPSHOT
FIGURE 45 THALES: COMPANY SNAPSHOT
TABLE 104 THALES: SOLUTIONS/SERVICES OFFERINGS
TABLE 105 THALES: DEALS
12.2.4 ASSA ABLOY AB
TABLE 106 ASSA ABLOY AB: BUSINESS OVERVIEW
FIGURE 46 ASSA ABLOY AB: COMPANY SNAPSHOT
TABLE 107 ASSA ABLOY AB: SOLUTIONS/SERVICES OFFERINGS
TABLE 108 ASSA ABLOY AB: PRODUCT LAUNCHES
TABLE 109 ASSA ABLOY AB: DEALS
12.2.5 DORMAKABA HOLDING AG
TABLE 110 DORMAKABA HOLDING AG: BUSINESS OVERVIEW
FIGURE 47 DORMAKABA HOLDING AG: COMPANY SNAPSHOT
TABLE 111 DORMAKABA HOLDING AG: SOLUTIONS/SERVICES OFFERINGS
TABLE 112 DORMAKABA HOLDING AG: DEALS
12.2.6 IDENTIV, INC.
TABLE 113 IDENTIV, INC.: BUSINESS OVERVIEW
FIGURE 48 IDENTIV, INC.: COMPANY SNAPSHOT
TABLE 114 IDENTIV, INC.: SOLUTIONS/SERVICES OFFERINGS
TABLE 115 IDENTIV, INC.: PRODUCT LAUNCHES
TABLE 116 IDENTIV, INC.: DEALS
12.2.7 KASTLE SYSTEMS
TABLE 117 KASTLE SYSTEMS: COMPANY SNAPSHOT
TABLE 118 KASTLE SYSTEMS: SOLUTIONS/SERVICES OFFERINGS
TABLE 119 KASTLE SYSTEMS: PRODUCT LAUNCHES
TABLE 120 KASTLE SYSTEMS: DEALS
TABLE 121 KASTLE SYSTEMS: OTHERS
12.2.8 AMAG TECHNOLOGY, INC.
TABLE 122 AMAG TECHNOLOGY, INC.: COMPANY SNAPSHOT
TABLE 123 AMAG TECHNOLOGY, INC.: SOLUTIONS/SERVICES OFFERINGS
12.2.9 BRIVO INC.
TABLE 124 BRIVO INC.: COMPANY SNAPSHOT
TABLE 125 BRIVO INC.: SOLUTIONS/SERVICES OFFERINGS
TABLE 126 BRIVO INC.: PRODUCT LAUNCHES/DEVELOPMENT
TABLE 127 BRIVO INC.: DEALS
12.2.10 CLOUDASTRUCTURE INC.
TABLE 128 CLOUDASTRUCTURE, INC.: COMPANY SNAPSHOT
FIGURE 49 CLOUDASTRUCTURE, INC.: COMPANY SNAPSHOT
TABLE 129 CLOUDASTRUCTURE, INC.: SOLUTIONS/SERVICES OFFERINGS
12.3 OTHER PLAYERS
12.3.1 STANLEY SECURITY (SECURITAS TECHNOLOGY)
12.3.2 DATAWATCH SYSTEMS
12.3.3 TELCRED AB
12.3.4 FORCEFIELD SYSTEMS
12.3.5 VANDERBILT INDUSTRIES
12.3.6 KISI INC.
12.3.7 FEENICS INC.
12.3.8 SERVSYS, INC.
12.3.9 SPECTRA TECHNOVISION (INDIA) PVT. LTD.
12.3.10 M3T CORPORATION
12.3.11 VECTOR SECURITY
12.3.12 CENTRIFY CORPORATION
12.3.13 GALLAGHER SECURITY LTD
12.3.14 DSX ACCESS SYSTEMS, INC.
12.3.15 ZKTECO CO., LIMITED
*Details on Business Overview, Solutions/Services Offered, Recent Developments, and MnM View (Key strengths/Right to Win, Strategic Choices Made, and Weaknesses and Competitive Threats) might not be captured in case of unlisted companies.
13 APPENDIX (Page No. - 184)
13.1 DISCUSSION GUIDE
13.2 KNOWLEDGESTORE: MARKETSANDMARKETS’ SUBSCRIPTION PORTAL
13.3 CUSTOMIZATION OPTIONS
13.4 RELATED REPORTS
13.5 AUTHOR DETAILS
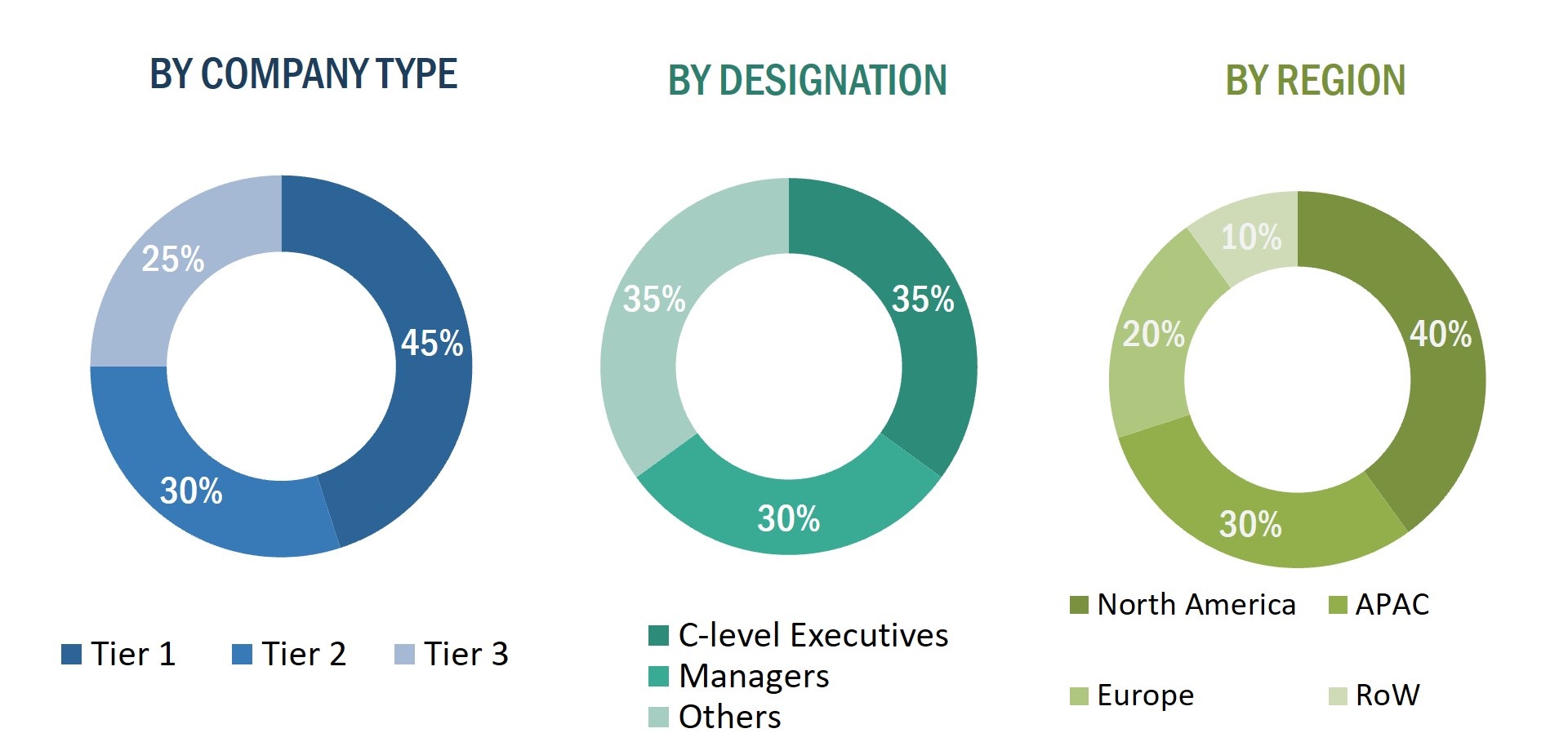
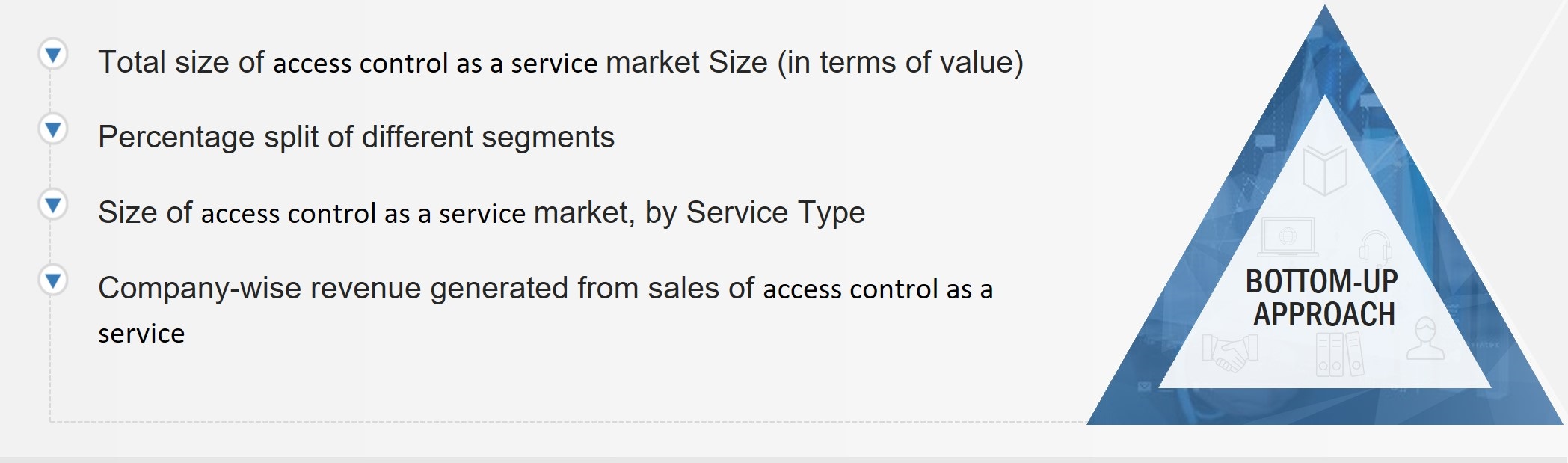
The study involved four major activities in estimating the size of the access control as a service market. Exhaustive secondary research has been carried out to collect information on the market, the peer markets, and the parent market. Both top-down and bottom-up approaches have been employed to estimate the total market size. Market breakdown and data triangulation methods have also been used to estimate the market for segments and subsegments.
Secondary Research
Revenues of companies offering ACaaS have been obtained from the secondary data available through paid and unpaid sources. The revenues have also been derived by analyzing the product portfolio of key companies, and these companies have been rated according to the performance and quality of their products.
In the secondary research process, various sources have been referred to for identifying and collecting information for this study on the access control as a service market. Secondary sources considered for this research study include government sources; corporate filings; and trade, business, and professional associations. Secondary data has been collected and analyzed to arrive at the overall market size, which has been further validated through primary research.
Secondary research has been mainly used to obtain key information about the supply chain of access control as a service to identify key players based on their products and prevailing industry trends in the access control as a service market by access control models, by service type, cloud deployment model, vertical, and region. Secondary research also helped obtain market information- and technology-oriented key developments undertaken by market players to expand their presence and increase their market share.
Primary Research
Extensive primary research has been conducted after understanding and analyzing the current scenario of the access control as a service market through secondary research. Several primary interviews have been conducted with the key opinion leaders from demand and supply sides across four main regions—the Americas, Europe, and Asia Pacific. Approximately 25% of the primary interviews have been conducted with the demand-side respondents, while approximately 75% have been conducted with the supply-side respondents. The primary data has been collected through questionnaires, emails, and telephonic interviews
After interacting with industry experts, brief sessions were conducted with highly experienced independent consultants to reinforce the findings from our primaries. This, along with the in-house subject matter experts’ opinions, has led us to the findings as described in the remainder of this report. The breakdown of primary respondents is as follows:
To know about the assumptions considered for the study, download the pdf brochure
Market Size Estimation
The bottom-up procedure has been employed to arrive at the overall size of the access control as a service market.
- Identifying approximate revenues companies involved in the access control as a service ecosystem
- Identifying different offerings of access control as a service
- Analyzing the global penetration of each offering of access control as a service through secondary and primary research
- Conducting multiple discussion sessions with key opinion leaders to understand the access control as a service and their applications; analyzing the breakup of the work carried out by each key company
- Verifying and crosschecking estimates at every level with key opinion leaders, including chief executive officers (CEO), directors, and operation managers, and then finally, with the domain experts of MarketsandMarkets
- Studying various paid and unpaid sources of information such as press releases, white papers, and databases of the company- and region-specific developments undertaken in the access control as a service market
The top-down approach has been used to estimate and validate the total size of the access control as a service market.
- Focusing initially on the top-line investments and expenditures made in the access control as a service ecosystem; further splitting into offering and listing key developments in key market areas
- Identifying all major players offering a variety of access control as a service, which was verified through secondary research and a brief discussion with industry experts
- Analyzing revenues, product mix and geographic presence for which access control as a service are offered by all identified players to estimate and arrive at the percentage splits for all key segments
- Discussing these splits with industry experts to validate the information and identify key growth domains across all major segments
- Breaking down the total market based on verified splits and key growth domains across all segments
Data Triangulation
After arriving at the overall market size—using the market size estimation processes as explained above—the market has been split into several segments and subsegments. To complete the entire market engineering process and arrive at the exact statistics of each market segment and subsegment, data triangulation, and market breakdown procedures have been employed, wherever applicable. The data has been triangulated by studying various factors and trends from both the demand and supply sides in the access control as a service market.
Report Objectives
- To describe and forecast the size of the access control as a service market, in terms of value, by service type, cloud deployment type, and vertical
- To describe and forecast the market size of various segments across four key regions—North America, Europe, Asia Pacific (APAC), and Rest of World (RoW), in terms of value
- To describe the Access Control Models used for access control as a service
- To provide detailed information regarding the drivers, restraints, opportunities, and challenges influencing the growth of the access control as a service market
- To provide an overview of the value chain pertaining to the access control as a service ecosystem, along with the average selling prices of access control as a service
- To strategically analyze the ecosystem, tariffs and regulations, patent landscape, Porter’s five forces, regulations, import and export scenarios, trade landscape, and case studies pertaining to the market under study
- To strategically analyze micromarkets1 with regard to individual growth trends, prospects, and contributions to the overall market
- To analyze opportunities in the market for stakeholders by identifying high-growth segments
- To provide details of the competitive landscape for market leaders
- To analyze competitive developments such product launches, expansions, investments, partnerships, and acquisitions in the access control as a service market
- To profile key players in the access control as a service market and comprehensively analyze their market ranking on the basis of their revenue, market share, and core competencies2
- Updated market developments of profiled players: The current report includes the market developments from January 2019 to August 2022.
Available customizations:
With the given market data, MarketsandMarkets offers customizations according to the specific requirements of companies. The following customization options are available for the report:
- Detailed analysis and profiling of additional market players based on various blocks of the supply chain




 Generating Response ...
Generating Response ...





Growth opportunities and latent adjacency in Access Control as a Service Market
Hi there. We are developing an innovative access control solution that we intend to offer as a service. Wanted to get some basic market information on things like market size, growth rate, major players of Access Control Market as a Service
Looking into the markets of contractors and worker safety credentials and cloud based access control for industrial and construction markets.
Hi, I�m currently acting as a project manager for Securitas future path towards ACaaS. I would appreciate if you could provide me all types of information about ACaaS.
Trying to understand total market size for the ACaaS space and what drives customer switching behavior.