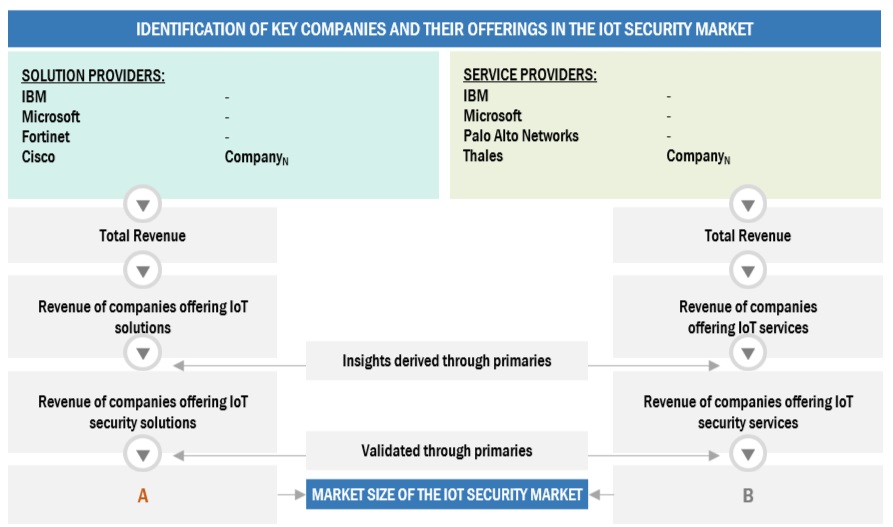
The study involved major activities in estimating the current market size for the IoT security market. Exhaustive secondary research was done to collect information on the IoT security industry. The next step was to validate these findings, assumptions, and sizing with industry experts across the value chain using primary research. Different approaches, such as top-down and bottom-up, were employed to estimate the total market size. After that, the market breakdown and data triangulation procedures were used to estimate the market size of the segments and subsegments of the market segments and subsegments of the IoT security market.
Secondary Research
The market for the companies offering IoT security solutions is determined by secondary data available through paid and unpaid sources, analyzing the product portfolios of the major companies in the ecosystem, and rating the companies by their performance and quality. Various sources were referred to in the secondary research process to identify and collect information for this study. The secondary sources include annual reports, press releases, investor presentations of companies, white papers, journals, certified publications, and articles from recognized authors, directories, and databases.
In the secondary research process, various secondary sources were referred to for identifying and collecting information related to the study. Secondary sources included annual reports, press releases, investor presentations of IoT security vendors, forums, certified publications, and whitepapers. The secondary research was used to obtain critical information on the industry’s value chain, the total pool of key players, market classification, and segmentation from market and technology-oriented perspectives and segmentation from market and technology-oriented perspectives.
Primary Research
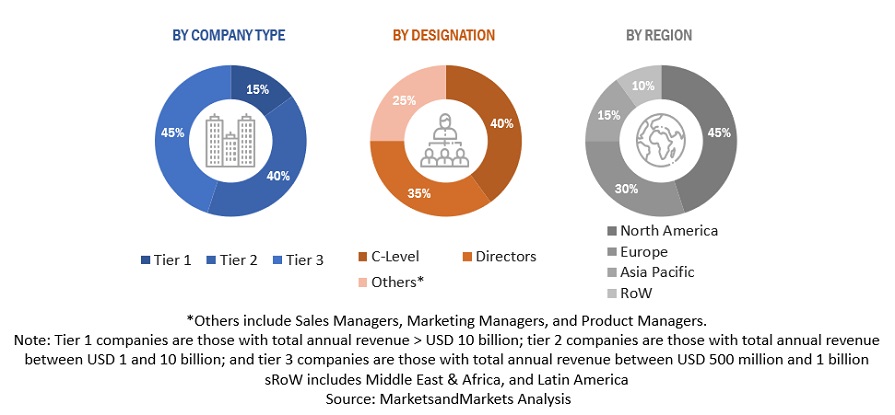
In the primary research process, various primary sources from both the supply and demand sides were interviewed to obtain qualitative and quantitative information for this report. The primary sources from the supply side included industry experts, such as Chief Executive Officers (CEOs), Vice Presidents (VPs), marketing directors, technology and innovation directors, and related key executives from various key companies and organizations operating in the IoT security market.
After the complete market engineering (calculations for market statistics, market breakdown, market size estimations, market forecasting, and data triangulation), extensive primary research was conducted to gather information and verify and validate the critical numbers arrived at. Primary research was also conducted to identify the segmentation types, industry trends, competitive landscape of IoT security solutions offered by various market players, and key market dynamics, such as drivers, restraints, opportunities, challenges, industry trends, and key player strategies.
In the complete market engineering process, the top-down and bottom-up approaches were extensively used, along with several data triangulation methods, to perform the market estimation and market forecasting for the overall market segments and subsegments listed in this report. Extensive qualitative and quantitative analysis was performed on the complete market engineering process to list the key information and insights throughout the report to list the key information/insights throughout the report.
Following is the breakup of the primary study:
To know about the assumptions considered for the study, download the pdf brochure
Market Size Estimation
Top-down and bottom-up approaches were used to estimate and validate the size of the global IoT security market and estimate the size of various other dependent sub-segments in the overall IoT security market.
The research methodology used to estimate the market size includes the following details:
-
Key players in the market were identified through secondary research, and their market shares in the respective regions were determined through primary and secondary research. This entire procedure included the study of the annual and financial reports of the top market players, and extensive interviews were conducted for key insights from the industry leaders, such as CEOs, VPs, directors, and marketing executives.
-
All percentage splits and breakdowns were determined using secondary sources and verified through primary sources. All possible parameters that affect the market covered in this research study have been accounted for, viewed in extensive detail, verified through primary research, and analyzed to get the final quantitative and qualitative data. This data is consolidated and added to detailed inputs and analysis from MarketsandMarkets.
INFOGRAPHIC DEPICTING MARKET SIZE ESTIMATION METHODOLOGY - APPROACHES
Data Triangulation
After arriving at the overall market size using the market size estimation processes explained above, the market was split into several segments and subsegments. The data triangulation and market breakup procedures were employed, wherever applicable, to complete the overall market engineering process and arrive at the exact statistics of each market segment and subsegment. The data was triangulated by studying various factors and trends from both the demand and supply sides.
Market Definition
IoT security is the practice of securing IoT devices and networks they are connected to. The interconnectedness of IoT presents a substantial challenge to enterprises in terms of security risks arising from shadow devices connected to the network. IoT security solutions and services minimize IoT security concerns and protect organizations, people, processes, and data from threats, thus lowering the losses caused by cyberattacks on connected devices.
Key Stakeholders
-
Global managed service providers
-
Cloud Service Providers (CSPs)
-
Independent Software Vendors (ISVs)
-
System integrators
-
Value-added Resellers (VARs)
-
Chief Financial Officers (CFOs)
-
Information Technology (IT) Directors
-
Small and Medium-sized Enterprises (SMEs)
-
IT strategy consultants
-
Technology partners
-
Research organizations
-
Enterprise users
Report Objectives
-
To define, describe, and forecast the IoT security market based on offering, solution, application, and region.
-
To provide detailed information about the major factors (drivers, opportunities, restraints, and challenges) influencing the growth of the market
-
To analyze opportunities for stakeholders by identifying the high-growth segments of the market
-
To forecast the size of the market segments with respect to five main regions: North America, Europe, Asia Pacific, the Middle East & Africa, and Latin America
-
To analyze subsegments of the market with respect to individual growth trends, prospects, and contributions to the overall market
-
To profile the key players and comprehensively analyze their market sizes and core competencies
-
To track and analyze competitive developments such as product enhancements and new product launches, acquisitions, and partnerships & collaborations in the market globally
Customization Options
With the given market data, MarketsandMarkets offers customizations based on company-specific needs. The following customization options are available for the report:
Company Information
-
Detailed analysis and profiling of additional market players (up to 5)



Growth opportunities and latent adjacency in IoT Security Market