Mobile User Authentication Market by User Type (Small and Medium Enterprises (SME's) and Enterprises), Vertical, and Region (North America, Europe, Asia-Pacific, Middle East and Africa, and Latin America) - Global Forecast and Analysis to 2020
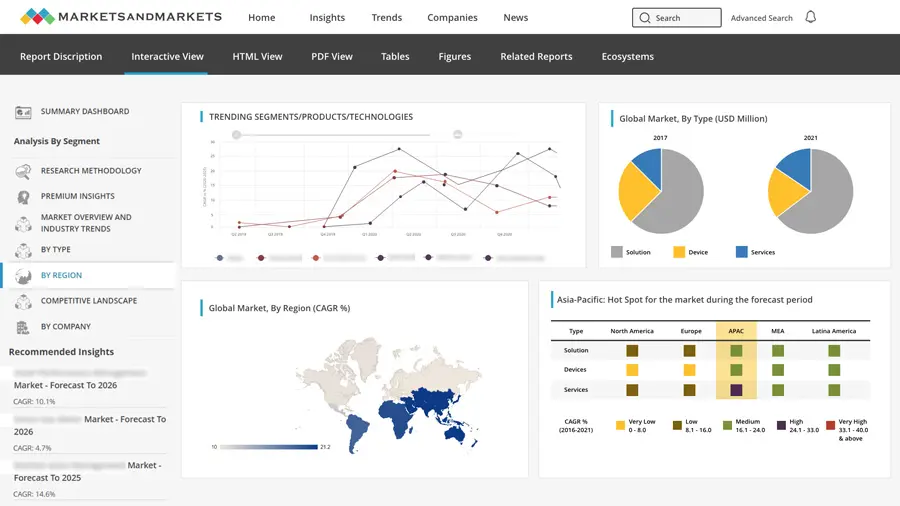
[112 Pages Report] The mobile user authentication market is expected to grow from USD 552.6 Million in 2015 to USD 1,682.0 Million by 2020, at a CAGR of 24.9%.
Virtualization and digitalization of enterprises is gaining impetus and the movement of vital resources such as data, process and employees across geographical boundaries and cross platforms is evident and has become easier than ever. But with huge advantage comes an associated security risk and most of the organizations are facing an uphill task of managing this security of resources to prevent unauthorized usage of sensitive and confidential data. Framing and enforcing a robust and user friendly authentication policy can enhance the competitive strengths and ensure transparency among different business processes of any enterprise. With the advent of globalization and Internet age, the world seems to be a smaller space to live, and it is giving rise to digital connectivity enabling faster information flow. The need to enforce security of organizational data as well as safeguard private and confidential data of individuals has become a need of the hour. The growth of BYOD and online data sharing has been one of the leading drivers in the growth of the deployment of mobile user authentication market solutions globally.
Mobile user authentication is providing authentication primarily to an enterprises customers or employees by using factor based authentication technique in which mobile is what the end user possess. The mobile user authentication is instrumental in managing and framing an enterpriseĺs security policies, procedures, process controls, technologies, and deciding of access control policies. Mobile user authentication can be instrumental in managing the private data of individuals and storing the passwords of end-users in highly encrypted form. The mobile user authentication market is growing at fast pace mainly attributed to concerns from different stakeholders over the security of organizational resources. Mobile user authentication solutions are combining with standalone biometric solutions to provide advanced multi-factor authentication techniques to provide advanced end-user verification by using fingerprinting, face print or voice print.
Mobile user authentication solutions ensures not only in the analysis of the security of business processes, technologies, people, and policies but is also vital in introducing transparency between different business processes and conducting a comprehensive audit trail in case of any cyber-attack or a significant data breach. Mobile user authentication ensures visibility and transparency in the overall IT infrastructure of an enterprise as a vital source of identifying loopholes and analyzing weaknesses and threats in technical aspects as well human resource aspects. Mobile user authentication market seems to increase at a greater pace attributed to the growing need among enterprises to ensure Single Sign-On and collaborating various federated identities to manage the applications used by the end-users.
This report analyzes global adoption trends, future growth potential, key drivers, restraints, opportunities, challenges, and best practices in the market. The report also examines growth potential market sizes and revenue forecasts across different regions.
By User Type:
- Small and Medium Enterprises (SMEs)
- Enterprises
By Vertical:
- Academia and education
- Banking, Financial Services, and Insurance (BFSI)
- Consumer goods and retail
- Energy and power
- Government and defense
- Life sciences and healthcare
- IT and telecom
- Manufacturing
- Others
By Region:
- North America
- Europe
- Asia-Pacific (APAC)
- Middle East and Africa (MEA)
- Latin America
The mobile user authentication market solutions are gaining traction due to the increased demand in disruptive technologies such as BYOD (Bring Your Own Device) and IoT (Internet of Things). The growth of online data sharing and the boom in the usage of different social media platforms in the recent times have increased the need of authenticating the end user on the basis of ôsomething you haveö and ôsomething you knowö. The amount of content generated in inter-organizations and intra-organizations has increased dramatically; therefore, there is a growing need to set proper access and control mechanisms. The advent of globalization and the Internet age has made the world a smaller place and has given rise to digital enterprises, and customers can be quickly won the timeliness and convenience of online and mobile interactions.
Mobile user authentication market can be defined as a security process in which is end user can be authenticated with the help of multiple factors such as biometrics, geographical positioning co-ordinates and timestamps which mobile device being the primary or essential factor. In mobile user authentication, the end user needs to be identified on the basis of separate set of credentials and essentially one set of credential is received through the mode of a mobile device. The mobile user authentication is vital mode of authentication since the smartphone or a mobile device is always in the possession of the user and one time passwords can be sent to smartphones or mobile devices easily. Mobile user authentication can drastically reduce the identity theft and phishing incidents due to two or more levels of authentication mechanism.
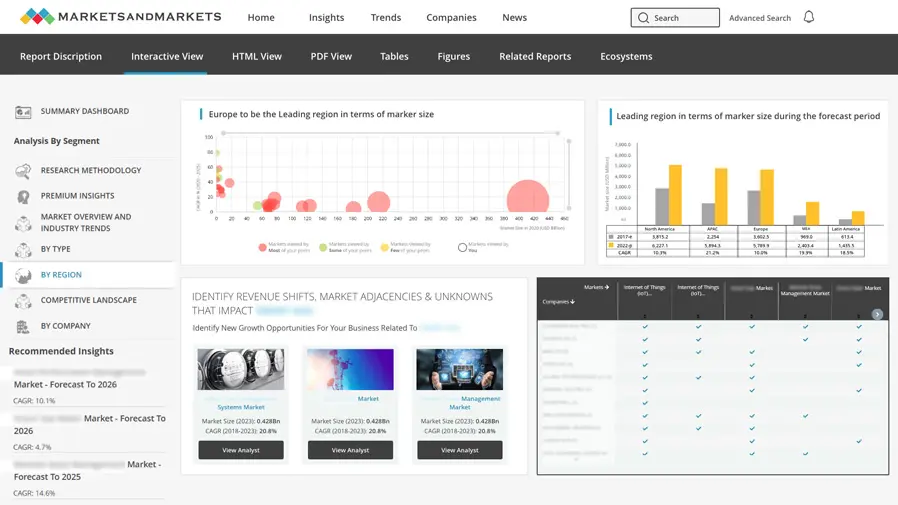
North America is expected to hold the largest market share, followed by Europe, during the forecast period. Mobile user authentication solutions are gaining traction due to increased awareness regarding growth of online data sharing and BYOD, increased frequency of high skilled cyber-attacks, increased traction for vulnerability assessment and management, and also the increasing need for better regulations and legislative compliances. Emerging countries such as Brazil, Russia, China, India, and South Africa (BRICS) are also expecting a growth in the implementation of mobile user authentication market solutions.
The mobile user authentication market has been segmented on the basis of on the basis of user types into SMEs and enterprises; on the basis of verticals into academia & education, Banking, Financial Services, and insurance (BFSI), consumer goods & retail, government & defense, life sciences & healthcare, manufacturing, IT & telecom, and others; and on the basis of regions into North America, Asia-Pacific (APAC), Europe, the Middle East and Africa (MEA), and Latin America. The report also provides insights into the opportunity analysis of specific verticals and business case analysis and roadmaps for the market.
The mobile user authentication market is expected to grow from USD 552.6 Million in 2015 to USD 1,682.0 Million by 2020, at a CAGR of 24.9%. The market was expected to exhibit a Y-o-Y growth rate of 12.06% during 2014ľ2015.

Table of Contents
1 Introduction (Page No. - 13)
1.1 Objectives of the Study
1.2 Market Definition
1.3 Market Scope
1.3.1 Markets Covered
1.3.2 Years Considered for the Study
1.4 Limitations
1.5 Currency
1.6 Stakeholders
2 Research Methodology (Page No. - 16)
2.1 Research Data
2.1.1 Secondary Data
2.1.1.1 Key Data From Secondary Sources
2.1.2 Primary Data
2.1.2.1 Key Data From Primary Sources
2.1.2.2 Key Industry Insights
2.1.2.3 Breakdown of Primary Interviews: By Company Type, Designation, and Region
2.2 Market Size Estimation
2.2.1 Bottom-Up Approach
2.2.2 Top-Down Approach
2.3 Market Breakdown and Data Triangulation
2.4 Research Assumptions
3 Executive Summary (Page No. - 23)
4 Premium Insights (Page No. - 26)
4.1 Attractive Market Opportunities in the Market
4.2 Mobile User Authentication Market
4.3 Market Potential
4.4 Mobile User Authentication Regional Market
4.5 Market: Vertical Growth Matrix
4.6 Lifecycle Analysis, By Region, 2015
5 Market Overview (Page No. - 30)
5.1 Introduction
5.1.1 By User Type
5.1.2 By Vertical
5.1.3 By Region
5.2 Market Dynamics
5.2.1 Drivers
5.2.1.1 Growth of Online Data Sharing and Byod
5.2.1.2 Growth in High Profile Cyber Attacks
5.2.1.3 Increase in Regulatory Compliances
5.2.1.4 Increased Traction for Vulnerability Assessment and Management
5.2.2 Restraints
5.2.2.1 Existing Base of Authentication Solutions
5.2.2.2 Shadow IT Risk
5.2.3 Opportunities
5.2.3.1 Growing Impetus to Internet of Things (IoT)
5.2.3.2 Demand for Authentication-As-A-Service (AaaS)
5.2.4 Challenges
5.2.4.1 Educating Consumers About Security and Authentication
5.2.4.2 Security Issues Associated With Cloud and Mobile Technologies
6 Industry Trends (Page No. - 37)
6.1 Introduction
6.2 Mobile User Authentication Market: Value Chain Analysis
6.3 Porterĺs Five Forces Analysis
6.3.1 Threat of New Entrants
6.3.2 Threat of Substitutes
6.3.3 Bargaining Power of Suppliers
6.3.4 Bargaining Power of Buyers
6.3.5 Intensity of Competitive Rivalry
7 Mobile User Authentication Market Analysis (Page No. - 41)
7.1 Introduction
8 Market Analysis, By User Type (Page No. - 44)
8.1 Introduction
8.2 SMES
8.3 Enterprises
9 Mobile User Authentication Market Analysis, By Vertical (Page No. - 48)
9.1 Introduction
9.2 Academia and Education
9.3 Banking, Financial Services and Insurance (BFSI)
9.4 Consumer Goods and Retail
9.5 Energy and Power
9.6 Government and Defense
9.7 Life Sciences and Healthcare
9.8 IT and Telecom
9.9 Manufacturing
9.10 Others
10 Geographic Analysis (Page No. - 60)
10.1 Introduction
10.2 North America
10.3 Europe
10.4 Asia-Pacific
10.5 Middle East and Africa
10.6 Latin America
11 Competitive Landscape (Page No. - 70)
11.1 Overview
11.2 Competitive Situation and Trends
11.2.1 New Product Developments
11.2.2 Partnerships, Agreements and Collaborations
11.2.3 Mergers and Acquisitions
11.2.4 New Contracts
11.2.5 Delivery Models
12 Company Profiles (Page No. - 76)
12.1 Introduction
(Overview, Financials, Products & Services, Strategy, and Developments)*
12.2 CA Technologies Inc.
12.3 EMC Corporation
12.4 GemaltoNV
12.5 Symantec Corporation
12.6 Vasco Data Security International Inc.
12.7 Authentify Inc.
12.8 Entrust Datacard Corporation
12.9 Secureauth Corporation
12.10 Securenvoy PLC
12.11 Telesign
*Details on Overview, Financials, Product & Services, Strategy, and Developments Might Not Be Captured in Case of Unlisted Companies.
13 Key Innovator Profiles (Page No. - 102)
13.1 Deepnet Security
13.1.1 Business Overview
13.1.2 Solutions Offered
13.2 SMS Passcode A/S
13.2.1 Business Overview
13.2.2 Solutions Offered
14 Appendix (Page No. - 104)
14.1 Industry Excerpts
14.1.1 New Product Developments, 2013ľ2015
14.1.2 Partnerships, Agreements and Collaborations
14.1.3 New Contracts
14.2 Discussion Guide
14.3 Introducing RT: Real-Time Market Intelligence
14.4 Available Customizations
14.5 Related Reports
List of Tables (45 Tables)
Table 1 Mobile User Authentication Market Size and Growth Rate, 2013ľ2020 (USD Million, Y-O-Y %)
Table 2 Market: Analysis of Drivers
Table 3 Market: Analysis of Restraints
Table 4 Market: Analysis of Opportunities
Table 5 Market: Analysis of Challenges
Table 6 Market Size, 2013ľ2020 (USD Million)
Table 7 Market Size, By User Type, 2013ľ2020 (USD Million)
Table 8 SMES: Market Size, By Region, 2013ľ2020 (USD Million)
Table 9 Enterprises: Market Size, By Region, 2013ľ2020 (USD Million)
Table 10 Mobile User Authentication Market Size, By Vertical, 2013ľ2020 (USD Million)
Table 11 Academia and Education: Market Size, By Region, 2013ľ2020 (USD Million)
Table 12 Academia and Education: Market Size, By User Type, 2013ľ2020 (USD Million)
Table 13 BFSI: Market Size, By Region, 2013ľ2020 (USD Million)
Table 14 BFSI: Market Size, By User Type, 2013ľ2020 (USD Million)
Table 15 Consumer Goods and Retail: Market Size, By Region, 2013ľ2020 (USD Million)
Table 16 Consumer Goods and Retail: Market Size, By User Type, 2013ľ2020 (USD Million)
Table 17 Energy and Power: Market Size, By Region, 2013ľ2020 (USD Million)
Table 18 Energy and Power: Market Size, By User Type, 2013ľ2020 (USD Million)
Table 19 Government and Defense: Market Size, By Region, 2013ľ2020 (USD Million)
Table 20 Government and Defense: Market Size, By User Type, 2013ľ2020 (USD Million)
Table 21 Life Sciences and Healthcare: Market Size, By Region, 2013ľ2020 (USD Million)
Table 22 Life Sciences and Healthcare: Market Size, By User Type, 2013ľ2020 (USD Million)
Table 23 IT and Telecom: Market Size, By Region, 2013ľ2020 (USD Million)
Table 24 IT and Telecom: Market Size, By User Type, 2013ľ2020 (USD Million)
Table 25 Manufacturing: Market Size, By Region, 2013ľ2020 (USD Million)
Table 26 Manufacturing: Market Size, By User Type, 2013ľ2020 (USD Million)
Table 27 Others: Market Size, By Region, 2013ľ2020 (USD Million)
Table 28 Others: Market Size, By User Type, 2013ľ2020 (USD Million)
Table 29 Mobile User Authentication Market Size, By Region, 2013ľ2020 (USD Million)
Table 30 North America: Market Size, By Vertical, 2013ľ2020 (USD Million)
Table 31 North America: Market Size, By User Type, 2013ľ2020 (USD Million)
Table 32 Europe: Market Size, By Vertical, 2013ľ2020 (USD Million)
Table 33 Europe: Market Size, By User Type, 2013ľ2020 (USD Million)
Table 34 Asia-Pacific: Market Size, By Vertical, 2013ľ2020 (USD Million)
Table 35 Asia-Pacific: Market Size, By User Type, 2013ľ2020 (USD Million)
Table 36 Middle East and Africa: Market Size, By Vertical, 2013ľ2020 (USD Million)
Table 37 Middle East and Africa: Market Size, By User Type, 2013ľ2020 (USD Million)
Table 38 Latin America: Market Size, By Vertical, 2013ľ2020 (USD Million)
Table 39 Latin America: Mobile User Authentication Market Size, By User Type, 2013ľ2020 (USD Million)
Table 40 New Product Developments, 2013ľ2015
Table 41 Partnerships, Agreements and Collaborations, 2013ľ2015
Table 42 Mergers and Acquisitions, 2013ľ2015
Table 43 New Contracts, 2013ľ2015
Table 44 Partnerships, Agreements and Collaborations, 2013ľ2015
Table 45 New Contracts, 2013ľ2015
List of Figures (39 Figures)
Figure 1 Research Design
Figure 2 Market Size Estimation Methodology: Bottom-Up Approach
Figure 3 Market Size Estimation Methodology: Top-Down Approach
Figure 4 Data Triangulation
Figure 5 Mobile User Authentication Market Size, User Type Snapshot (2015ľ2020): SME Market is Expected to Quadruple By 2020
Figure 6 Market Share: North America is Expected to Hold the Largest Market Share in 2015
Figure 7 Growth in Online Data Sharing and Increased Adoption of Byod is Driving the Market
Figure 8 North America is Expected to Exhibit the Highest Market Share in the Mobile User Authentication Market (2015)
Figure 9 Asia-Pacific and Middle East & Africa are Expected to Have the Highest Market Growth Potential During the Forecast Period
Figure 10 Asia-Pacific is Expected to Grow With Higher CAGR Than Middle East & Africa and Latin America
Figure 11 Mobile User Authentication Vertical Growth Matrix
Figure 12 Regional Lifecycle: Asia-Pacific is in the Growth Phase in 2015
Figure 13 Market Segmentation: By User Type
Figure 14 Market Segmentation: By Vertical
Figure 15 Market Segmentation: By Region
Figure 16 Mobile User Authentication: Drivers, Restraints, Opportunities, and Challenges
Figure 17 Value Chain Analysis
Figure 18 Porterĺs Five Forces Analysis: Mobile User Authentication Market
Figure 19 SMES Will Exhibit Higher Growth Rate in the Market During the Forecast Period
Figure 20 Government and Defense Vertical is Expected to Have the Largest Market Size in the Market By 2020
Figure 21 North America Will Continue to Have the Largest Market Size in the Market During the Forecast Period 2015ľ2020
Figure 22 Geographic Snapshot: Asia-Pacific is Emerging as A New Hotspot in the Mobile User Authentication Market
Figure 23 Asia-Pacific is the Fastest Growing Market in the Market
Figure 24 North America Market Snapshot: Increased Traction Among Verticals Will Drive the Market
Figure 25 Asia-Pacific Market Snapshot: Increased Traction Among Growing Economies Will Drive the Market
Figure 26 Companies Adopted, Acquisitions, New Product Developments, and Partnership Agreements and Collaborations as the Key Growth Strategies for the -Period 2013-2015
Figure 27 Market Evaluation Framework
Figure 28 Battle for Market Share: New Product Launches Was the Key Strategy Adopted By Players During the Last 3 Years
Figure 29 Geographic Revenue Mix of Top Five Players
Figure 30 CA Technologies Inc.: Company Snapshot
Figure 31 CA Technologies Inc.: SWOT Analysis
Figure 32 EMC Corporation: Company Snapshot
Figure 33 EMC Corporation: SWOT Analysis
Figure 34 Gemalto NV: Company Snapshot
Figure 35 Gemalto NV: SWOT Analysis
Figure 36 Symantec Corporation: Company Snapshot
Figure 37 Symantec Corporation: SWOT Analysis
Figure 38 Vasco Data Security International Inc.: Company Snapshot
Figure 39 Vasco Data Security International, Inc: SWOT Analysis













Growth opportunities and latent adjacency in Mobile User Authentication Market
Detailed understanding of the Network Packet Brokers
Interested in the mobile app authentication and customer care solution.
Understand the market sizing and segmentation of authentication/ verification products for North America region.