Vendor Comparison in Application Control � 2016: MnM DIVE Matrix
In today�s technology environment, cyber threats and vulnerabilities have become a boardroom discussion in organizations across the globe. The need to mitigate IT security risks and protect data, applications, and various endpoints against threats are still the primary goal of organizations. Application control refers to the security of endpoint applications to safeguard them against advanced persistent threats (APTs) and targeted attacks.
MarketsandMarkets defines application control as the solution that blocks the unwanted and unauthorized applications from executing on various enterprise endpoints such as desktops, smartphones, servers, Point-of-Sale (POS) systems, and other fixed function devices.
The need to enforce enterprise-wide application usage and data security policies has fueled the growth of application control solutions within the organizations. In the era of rapid adoption of Bring Your Own Device (BYOD) trends among organizations, application control and data security is of utmost importance. The acceptable use policy has contributed to BYOD success with application control and security.
This report on vendor comparison in application control based on MNM DIVE methodology analyzes and evaluates the key vendors in the application control market.
Vendor Inclusion Criteria
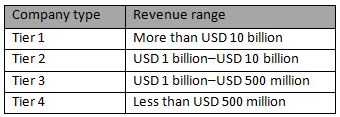
We have selected 10 vendors for evaluations based on their breadth of product offering and robust business strategy. The focus of our vendor evaluation is based on the product they offer in the application control market. A comprehensive list of all the vendors in this market was created through a product mapping strategy and MarketsandMarkets analysis. Based on their capabilities, innovations, and breadth of product offering, vendors were shortlisted. Our selected vendor mix includes companies from Tier 1 to Tier 4 and covers the whole market comprehensively. The below table describes the company type with their revenue range:
To know about the assumptions considered for the study, download the pdf brochure
Vendors Evaluated
The report covers the comprehensive study of the key vendors offering solutions for mobile application security. We have evaluated the following 10 vendors: Symantec Corporation, Intel Security (McAfee), Trend Micro, Inc., CyberArk Software Ltd., Carbon Black, Inc., Digital Guardian, Check Point Software Technologies Ltd., LANDESK Software (AppSense), Thycotic (Arellia). and HEAT Software USA Ltd., (Lumension Security, Inc.)
Application control is a security practice to restrict unauthorized and unwanted applications from executing on endpoints to guard the organization�s endpoint environment. Application control solution protect corporate endpoints such as desktops, laptops, smartphones, tablets, servers, Point-of-Sale (POS) systems, virtual machines, and other fixed functioning devices. These solutions safeguard the enterprise data and endpoints against viruses, Trojans, and malwares as well as advanced threats such as Advanced Persistent Threats (APTs), zero-day malwares, and targeted attacks.
Traditional security solutions are proving to be ineffective with the increasing number of sophisticated threats on multiple endpoints. This is encouraging enterprises to deploy application control solutions for improved security measures and special protection at multiple endpoints against potential threats. Also, the lack of awareness of end users regarding security is a significant challenge faced by the security vendors these days. Educating them about multi-level security solutions will ensure proper enforcement of application control policies, which is vital for reducing the potential risks on endpoints and for the growth of the application control market.
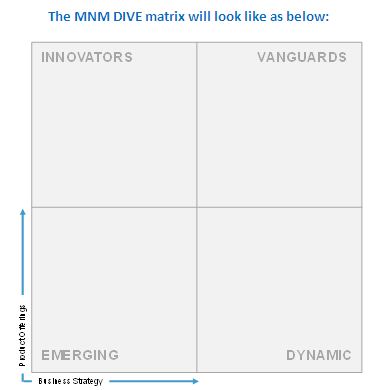
The report on Vendor Comparison in Application Control based on MarketsandMarkets DIVE methodology reviews major players that offer application control solutions and outlines the findings and analysis on the basis of two broad categories: Product Offerings and Business Strategies. Each category carries various criteria, based on which the vendors are evaluated. The criteria are provided below:

Based on the extensive secondary and primary research, key information about the vendors� product offerings and business strategies was gathered. After the completion of data gathering and verification process, the scores and weightage for shortlisted vendors against each parameter were finalized. A comparison scorecard was prepared after evaluating all the vendors and each vendor was placed in the MNM DIVE matrix based on their product offering and business strategy scores.
This report is instrumental in helping the stakeholders, such as application control vendors, system integrators, value-added resellers, and technology partners, to make business decisions on application control solution deployments.
The report covers the comprehensive study of key application control vendors, including Symantec Corporation, Intel Security (McAfee), Trend Micro, Inc., CyberArk Software Ltd., Carbon Black, Inc., Digital Guardian, Check Point Software Technologies Ltd., LANDESK Software (AppSense), Thycotic (Arellia), and HEAT Software USA Ltd., (Lumension Security, Inc.).
To speak to our analyst for a discussion on the above findings, click Speak to Analyst

Table of Contents
1 Introduction
1.1 About the Document
1.2 Market Definition
1.3 Stakeholders
2 Premium Insights
3 MnM Dive Overview
3.1 Dive Evaluation Criteria
3.2 Vendor Inclusion Criteria
3.3 Vendors Evaluated
4 MnM Voice: Application Control
4.1 Application Control: A Proactive Security Approach to Protect Data, Applications, and Endpoints
4.2 Application Control: Best Practices
5 Application Control: Vendor Comparison
5.1 MnM Dive Vendor Comparison Scorecard
5.2 MnM View
6 Vendor Profiles
6.1 Symantec Corporation
6.2 Intel Security (Mcafee)
6.3 Trend Micro, Inc.
6.4 Cyberark Software Ltd.
6.5 Carbon Black, Inc.
6.6 Digital Guardian
6.7 Check Point Software Technologies Ltd.
6.8 Landesk Software (Appsense)
6.9 Thycotic (Arellia)
6.10 Heat Software USA, Inc. (Lumension Security, Inc.)
7 Appendix
7.1 MnM Dive: Vendor Comparison Methodology
7.2 Matrix Description
7.3 List of Abbreviations
7.4 Related Research
7.5 Endnotes/References










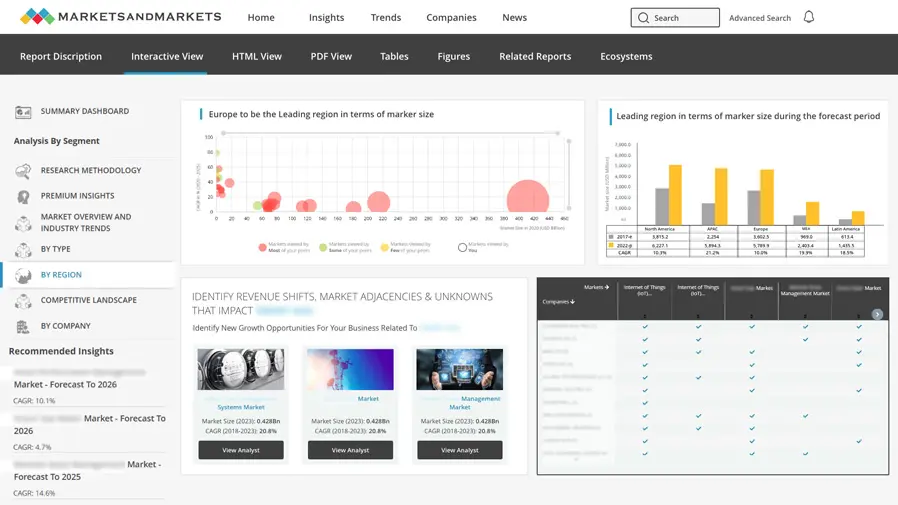
Growth opportunities and latent adjacency in Vendor Comparison in Application Control