2
RESEARCH METHODOLOGY
57
5
MARKET OVERVIEW AND INDUSTRY TRENDS
AI-driven cybersecurity is transforming threat detection and response, despite challenges in standardization and liability.
78
5.2.1.1
Rising frequency and sophistication of AI-driven cyberattacks
5.2.1.2
Operational efficiency gains through AI-assisted Security Operations Centers (AI-SOC), reducing alert fatigue and response times
5.2.1.3
Escalating zero-day vulnerabilities, necessitating rapid AI-enabled detection and remediation
5.2.1.4
Growing demand for AI-powered behavioral anomaly detection to combat insider threats
5.2.2.1
Lack of standardized benchmarks for evaluation of AI cybersecurity solutions
5.2.2.2
Uncertainty around liability in AI-led automated security actions
5.2.3.1
Adoption of Zero Trust for AI frameworks to validate AI-generated outputs
5.2.3.2
Leveraging AI for real-time detection of adversarial AI attacks on critical infrastructure
5.2.3.3
Development of AI-driven penetration testing and vulnerability assessment platforms
5.2.4.1
Exploitation of prompt injection and model manipulation techniques to bypass safeguards
5.2.4.2
Proliferation of AI-enabled deepfake fraud targeting enterprises and critical infrastructure
5.3
EVOLUTION OF GENERATIVE AI CYBERSECURITY
5.4
SUPPLY CHAIN ANALYSIS
5.5.1
GENERATIVE AI-BASED CYBERSECURITY PROVIDERS
5.5.2
CYBERSECURITY PROVIDERS FOR GENERATIVE AI
5.5.3
GENERATIVE AI CYBERSECURITY SERVICE PROVIDERS
5.6
INVESTMENT AND FUNDING SCENARIO
5.7.1
ZEROFOX PROVIDES ACTIONABLE INTELLIGENCE TO SHORE UP SIMPLY BUSINESS’S INFORMATION SECURITY
5.7.2
POMELO STAYS SECURE AMIDST RAPID GROWTH WITH SNYK
5.7.3
EVOCABANK HELPS NOKIA PROTECT MILLIONS OF FOLLOWERS
5.7.4
CARNIVAL CORPORATION CHARTS A SAFER COURSE WITH CYBERARK
5.7.5
IBM USES PALO ALTO TO PROTECTS ITS AI SYSTEMS
5.7.6
OPENAI USES OKTA TO SAFEGUARD ITSELF
5.8.1.1
Adversarial machine learning
5.8.1.2
Federated learning security
5.8.1.3
Differential privacy
5.8.1.4
Homomorphic encryption
5.8.1.5
Secure multi-party computation
5.8.2
COMPLEMENTARY TECHNOLOGIES
5.8.2.2
Zero trust architecture
5.8.2.3
Endpoint detection & response
5.8.2.4
Vulnerability management
5.8.3
ADJACENT TECHNOLOGIES
5.8.3.1
Quantum computing
5.8.3.3
Forensics & incident response
5.8.3.4
Big data analytics
5.9.1
REGULATORY BODIES, GOVERNMENT AGENCIES, AND OTHER ORGANIZATIONS
5.9.2.4
Middle East & Africa
5.10.2
PATENTS FILED, BY DOCUMENT TYPE
5.10.3
INNOVATION AND PATENT APPLICATIONS
5.11.1
AVERAGE SELLING PRICE OF KEY PLAYERS, BY OFFERING, 2025
5.11.2
AVERAGE SELLING PRICE, BY SECURITY TYPE, 2025
5.12
KEY CONFERENCES AND EVENTS (2025–2026)
5.13
PORTER’S FIVE FORCES ANALYSIS
5.13.1
THREAT OF NEW ENTRANTS
5.13.2
THREAT OF SUBSTITUTES
5.13.3
BARGAINING POWER OF SUPPLIERS
5.13.4
BARGAINING POWER OF BUYERS
5.13.5
INTENSITY OF COMPETITION RIVALRY
5.14
KEY STAKEHOLDERS & BUYING CRITERIA
5.14.1
KEY STAKEHOLDERS IN BUYING PROCESS
5.15
TRENDS/DISRUPTIONS IMPACTING CUSTOMER BUSINESS
5.15.1
TRENDS/DISRUPTIONS IMPACTING CUSTOMER BUSINESS
6
GENERATIVE AI CYBERSECURITY MARKET, BY OFFERING
Market Size & Growth Rate Forecast Analysis to 2031 in USD Million | 26 Data Tables
117
6.1.1
OFFERING: GENERATIVE AI CYBERSECURITY MARKET DRIVERS
6.2.1
STRENGTHENING OF GENERATIVE AI SECURITY WITH PURPOSE-BUILT SOFTWARE
6.2.2
GENERATIVE AI-BASED CYBERSECURITY SOFTWARE
6.2.3
CYBERSECURITY SOFTWARE FOR GENERATIVE AI
6.3
SOFTWARE, BY DEPLOYMENT MODE
6.3.1
OPTIMIZING CYBER DEFENSE WITH FLEXIBLE DEPLOYMENT MODES
6.4.1
RESILIENT GENERATIVE AI CYBERSECURITY ENABLED THROUGH COMPREHENSIVE SERVICES
6.4.2
PROFESSIONAL SERVICES
6.4.2.1
Training & consulting
6.4.2.2
System integration & implementation
6.4.2.3
Support & maintenance
7
CYBERSECURITY SOFTWARE MARKET FOR GENERATIVE AI, BY TYPE
Market Size & Growth Rate Forecast Analysis to 2031 in USD Million | 10 Data Tables
132
7.1.1
CYBERSECURITY SOFTWARE FOR GENERATIVE AI: MARKET DRIVERS
7.2
GENERATIVE AI TRAINING DATA SECURITY SOFTWARE
7.2.1
ENSURING RELIABILITY AND COMPLIANCE WITH TRAINING DATA SECURITY
7.2.2
DATA INTEGRITY VERIFICATION
7.2.3
SECURE DATA AUGMENTATION
7.2.4
AUTOMATED DATA CLEANING
7.2.5
DATA QUALITY MONITORING
7.3
GENERATIVE AI MODEL SECURITY SOFTWARE
7.3.1
SHIELDING GENERATIVE AI MODELS AGAINST EVOLVING THREATS
7.3.3
ADVERSARIAL TRAINING & TESTING
7.3.4
SECURE MODEL TRAINING ENVIRONMENTS
7.3.5
MODEL DRIFT & BIAS DETECTION
7.4
GENERATIVE AI INFRASTRUCTURE SECURITY SOFTWARE
7.4.1
ENSURING RESILIENT FOUNDATIONS FOR LARGE-SCALE GENERATIVE AI OPERATIONS
7.4.2
CONTINUOUS MONITORING
7.4.3
AUTOMATED SECURITY PATCHING
7.4.4
SECURE API MANAGEMENT
7.4.5
REAL-TIME THREAT DETECTION
7.5
GENERATIVE AI APPLICATION SECURITY SOFTWARE
7.5.1
DEFENDING GENERATIVE AI APPLICATIONS FROM ATTACK VECTORS
7.5.2
PROMPT INJECTION SECURITY
7.5.3
DATA LEAKAGE PREVENTION
7.5.4
USER AUTHENTICATION & ACCESS CONTROL
7.5.5
MONITORING & ANOMALY DETECTION
7.5.6
ETHICAL AI GOVERNANCE
8
GENERATIVE AI CYBERSECURITY MARKET, BY END USER
Market Size & Growth Rate Forecast Analysis to 2031 in USD Million | 42 Data Tables
147
8.1.1
END USERS: GENERATIVE AI CYBERSECURITY MARKET DRIVERS
8.2
END USERS: GENERATIVE AI-BASED CYBERSECURITY
8.2.1
DRIVING ADVANCED THREAT MITIGATION WITH GENERATIVE AI
8.2.2
GOVERNMENT & DEFENSE
8.2.5
HEALTHCARE & LIFE SCIENCES
8.2.10
AUTOMOTIVE, TRANSPORTATION, AND LOGISTICS
8.2.11
MEDIA & ENTERTAINMENT
8.3
END USERS: CYBERSECURITY FOR GENERATIVE AI
8.3.1
PROTECTING GENERATIVE AI SERVICES TO SAFEGUARD END USERS
8.3.3
MANAGED SECURITY SERVICE PROVIDERS
8.3.4
GENERATIVE AI PROVIDERS
8.3.4.1
Foundation model/LLM developers
8.3.4.3
Content creation platform providers
8.3.4.4
Generative AI-as-a-service provider
9
GENERATIVE AI-BASED CYBERSECURITY SOFTWARE MARKET, BY TYPE
Market Size & Growth Rate Forecast Analysis to 2031 in USD Million | 16 Data Tables
170
9.1.1
GENERATIVE AI-BASED CYBERSECURITY SOFTWARE MARKET DRIVERS
9.2
THREAT DETECTION & INTELLIGENCE SOFTWARE
9.2.1
OFFERS ENHANCED CYBERSECURITY PRECISION AND SPEED
9.2.2
AUTOMATED THREAT ANALYSIS
9.2.3
SECURITY INFORMATION & EVENT MANAGEMENT
9.2.4
AI-NATIVE SECURITY ANALYSIS
9.2.6
THREAT INTELLIGENCE
9.3
RISK ASSESSMENT SOFTWARE
9.3.1
PREDICTIVE RISK ASSESSMENT STRENGTHENS GENERATIVE AI CYBERSECURITY POSTURE
9.3.2
AUTOMATED RISK INSIGHTS
9.3.5
COMPLIANCE AUTOMATION
9.3.6
OTHER RISK ASSESSMENT SOFTWARE
9.4
EXPOSURE MANAGEMENT SOFTWARE
9.4.1
OFFERS AI-POWERED VULNERABILITY OVERSIGHT FOR STRONGER CYBERSECURITY
9.4.2
VULNERABILITY ANALYSIS
9.4.3
EXPOSURE PRIORITIZATION
9.4.4
AUTOMATED EXPOSURE DETECTION
9.4.6
OTHER EXPOSURE MANAGEMENT SOFTWARE
9.5
PHISHING SIMULATION & PREVENTION SOFTWARE
9.5.1
SIMULATES REALISTIC PHISHING SCENARIOS WITH GENERATIVE AI
9.5.2
PHISHING SIMULATION CAMPAIGNS
9.5.3
PHISHING ATTACK ANALYSIS
9.5.6
SOCIAL ENGINEERING DETECTION
9.6
REMEDIATION GUIDANCE SOFTWARE
9.6.1
ENABLES QUICK AND INFORMED RESPONSE WITH GENERATIVE AI REMEDIATION GUIDANCE
9.6.2
AUTOMATED REMEDIATION
9.6.3
INTERACTIVE REMEDIATION SUPPORT
9.6.4
PROACTIVE THREAT MANAGEMENT
9.6.5
COMPLIANCE REMEDIATION
9.6.6
OTHER REMEDIATION GUIDANCE SOFTWARE
9.7
THREAT HUNTING PLATFORMS
9.7.1
CYBER DEFENSE ENHANCED BY PREDICTING AND NEUTRALIZING STEALTH ATTACKS
9.7.2
REAL-TIME THREAT ANALYSIS
9.7.3
NATURAL LANGUAGE QUERY INTERFACE
9.7.5
RESPONSE AUTOMATION
9.7.6
OTHER THREAT HUNTING PLATFORMS
9.8
CODE ANALYSIS SOFTWARE
9.8.1
SECURES DEVELOPMENT PIPELINES WITH GENERATIVE AI PRECISION
9.8.2
CODE SNIPPET ANALYSIS
9.8.3
SOURCE CODE PROTECTION
9.8.4
VULNERABILITY DETECTION
9.8.5
AUTOMATED CODE REVIEW
10
GENERATIVE AI CYBERSECURITY MARKET, BY SECURITY TYPE
Market Size & Growth Rate Forecast Analysis to 2031 in USD Million | 50 Data Tables
193
10.1.1
SECURITY TYPE: GENERATIVE AI CYBERSECURITY MARKET DRIVERS
10.2.1
SECURES GENERATIVE AI PIPELINES WITH ADVANCED DATABASE PROTECTION
10.2.2
DATA LOSS PREVENTION
10.2.3
DATA USAGE MONITORING
10.2.4
DATA COMPLIANCE & GOVERNANCE
10.2.6
DATA MASKING & TOKENIZATION
10.3.1
OPTIMIZING SECURE CONNECTIVITY FOR GENERATIVE AI WORKLOADS
10.3.2
NETWORK TRAFFIC ANALYSIS
10.3.3
SECURE ACCESS SERVICE EDGE
10.3.4
ZERO TRUST NETWORK ACCESS
10.3.6
INTRUSION DETECTION/PREVENTION SYSTEMS
10.3.7
VPNS & SECURE TUNNELING
10.4.1
OPTIMIZING THREAT DETECTION AND RESPONSE ACROSS GENERATIVE AI ENDPOINTS
10.4.2
ENDPOINT DETECTION & RESPONSE
10.4.3
ENDPOINT PROTECTION PLATFORMS
10.5
APPLICATION SECURITY
10.5.1
SECURING GENERATIVE AI WORKFLOWS WITH END-TO-END APPLICATION PROTECTION
10.5.2
STATIC APPLICATION SECURITY TESTING
10.5.3
DYNAMIC APPLICATION SECURITY TESTING
10.5.5
RUNTIME PROTECTION
10.5.6
INCIDENT RESPONSE & RECOVERY
10.5.7
GOVERNANCE, RISK, AND COMPLIANCE
11
GENERATIVE AI CYBERSECURITY MARKET, BY REGION
Market Size & Growth Rate Forecast Analysis to 2031 in USD Million | 496 Data Tables
220
11.2.1
NORTH AMERICA: GENERATIVE AI CYBERSECURITY MARKET DRIVERS
11.2.2
NORTH AMERICA: MACROECONOMIC OUTLOOK
11.2.3.1
Market driven by robust technological infrastructure and culture of innovation
11.2.4.1
Recent advancements and presence of leading companies to drive market
11.3.1
EUROPE: GENERATIVE AI CYBERSECURITY MARKET DRIVERS
11.3.2
EUROPE: MACROECONOMIC OUTLOOK
11.3.3.1
Commitment to leveraging AI to tackle evolving cyber threats to fuel growth
11.3.4.1
Active government promotion of AI research to boost market
11.3.5.1
Emphasis on R&D to drive market
11.4.1
ASIA PACIFIC: GENERATIVE AI CYBERSECURITY MARKET DRIVERS
11.4.2
ASIA PACIFIC: MACROECONOMIC OUTLOOK
11.4.3.1
AI-driven cybersecurity solutions that offer robust defense against digital threats – key market driver
11.4.4.1
Market trajectory characterized by significant investment in research and development
11.4.5.1
International regulatory framework and promotion of safe and trustworthy AI usage – key drivers
11.4.6
REST OF ASIA PACIFIC
11.5
MIDDLE EAST & AFRICA
11.5.1
MIDDLE EAST & AFRICA: GENERATIVE AI CYBERSECURITY MARKET DRIVERS
11.5.2
MIDDLE EAST & AFRICA: MACROECONOMIC OUTLOOK
11.5.3.1
Evolving to support growth of generative AI and cybersecurity
11.5.4.1
Focus on establishment of cutting-edge AI and cybersecurity infrastructure
11.5.5
REST OF MIDDLE EAST
11.5.6.1
Development of new AI models and technologies tailored to unique cybersecurity challenges to drive market
11.6.1
LATIN AMERICA: GENERATIVE AI CYBERSECURITY MARKET DRIVERS
11.6.2
LATIN AMERICA: MACROECONOMIC OUTLOOK
11.6.3.1
Companies continue to invest in generative AI solutions and push boundaries of innovation
11.6.4.1
Government proactively addressing data privacy and security concerns
11.6.5
REST OF LATIN AMERICA
12
COMPETITIVE LANDSCAPE
Uncover top players' strategies and market dominance in generative AI-based cybersecurity solutions.
390
12.2
KEY PLAYER STRATEGIES
12.4
MARKET SHARE ANALYSIS
12.4.1
MARKET RANKING ANALYSIS
12.5
PRODUCT COMPARATIVE ANALYSIS
12.5.1
PRODUCT COMPARATIVE ANALYSIS: GENERATIVE AI-BASED CYBERSECURITY
12.5.1.1
Purple AI (SentinelOne)
12.5.1.2
Prevent (Darktrace)
12.5.1.3
ZDX Copilot (Zscaler)
12.5.1.4
FortiAI (Fortinet)
12.5.1.5
Precision AI (Palo Alto)
12.5.2
PRODUCT COMPARATIVE ANALYSIS: CYBERSECURITY FOR GENERATIVE AI
12.5.2.2
AI Runtime Security (Palo Alto)
12.5.2.3
Nitro Enclaves (AWS)
12.5.2.4
Zero Trust Exchange (Zscaler)
12.5.2.5
Nemo LLM Guardrails (NVIDIA)
12.6
COMPANY VALUATION AND FINANCIAL METRICS
12.7
COMPANY EVALUATION MATRIX: KEY PLAYERS, 2024
12.7.1
KEY PLAYERS OFFERING GENERATIVE AI-BASED CYBERSECURITY
12.7.6
COMPANY FOOTPRINT: KEY PLAYERS, 2024
12.7.6.1
Company Footprint
12.7.6.2
Region Footprint
12.7.6.3
Offering footprint
12.7.6.4
Security type footprint
12.7.6.5
End user footprint
12.7.7
KEY PLAYERS OFFERING CYBERSECURITY SOLUTIONS FOR GENERATIVE AI
12.7.10
PERVASIVE PLAYERS
12.7.12
COMPANY FOOTPRINT: KEY PLAYERS, 2024
12.7.12.1
Company Footprint
12.7.12.2
Regional footprint
12.7.12.3
Offering footprint
12.7.12.4
Security type footprint
12.7.12.5
End user footprint
12.8
COMPANY EVALUATION MATRIX: STARTUPS/SMES, 2024
12.8.1
STARTUPS/SMES OFFERING GENERATIVE AI-BASED CYBERSECURITY
12.8.1.1
Progressive companies
12.8.1.2
Responsive companies
12.8.1.3
Dynamic companies
12.8.2
COMPETITIVE BENCHMARKING: STARTUPS/SMES, 2024
12.8.2.1
Detailed List of Key Startups/SMEs
12.8.2.2
Competitive Benchmarking of Key Startups/SMEs
12.8.3
STARTUPS/SMES OFFERING CYBERSECURITY SOLUTIONS FOR GENERATIVE AI
12.8.3.1
Progressive companies
12.8.3.2
Responsive companies
12.8.3.3
Dynamic companies
12.8.4
COMPETITIVE BENCHMARKING: STARTUPS/SMES, 2024
12.8.4.1
Detailed List of Key Startups/SMEs
12.8.4.2
Competitive Benchmarking of Key Startups/SMEs
12.9
COMPETITIVE SCENARIO AND TRENDS
12.9.1
PRODUCT LAUNCHES AND ENHANCEMENTS
13
COMPANY PROFILES
In-depth Company Profiles of Leading Market Players with detailed Business Overview, Product and Service Portfolio, Recent Developments, and Unique Analyst Perspective (MnM View)
426
13.2
GENERATIVE AI-BASED CYBERSECURITY SOLUTION PROVIDERS
13.2.1.1
Business overview
13.2.1.2
Products/Solutions/Services offered
13.2.1.3
Recent developments
13.2.10
SANGFOR TECHNOLOGIES
13.2.13
SECURITYSCORECARD
13.3
PROVIDERS OF CYBERSECURITY SOLUTIONS FOR GENERATIVE AI
13.3.6
PALO ALTO NETWORKS
13.3.13
ABNORMAL SECURITY
14
ADJACENT AND RELATED MARKETS
484
14.2
GENERATIVE AI MARKET – GLOBAL FORECAST TO 2032
14.2.2.1
Generative AI market, by offering
14.2.2.2
Generative AI market, by data modality
14.2.2.3
Generative AI market, by application
14.2.2.4
Generative AI market, by end user
14.2.2.5
Generative AI market, by region
14.3
ARTIFICIAL INTELLIGENCE IN CYBERSECURITY MARKET – GLOBAL FORECAST TO 2028
14.3.2.1
Artificial intelligence in cybersecurity market, by offering
14.3.2.2
Artificial intelligence in cybersecurity market, by security type
14.3.2.3
Artificial intelligence in cybersecurity market, by technology
14.3.2.4
Artificial intelligence in cybersecurity market, by application
14.3.2.5
Artificial intelligence in cybersecurity market, by vertical
14.3.2.6
Artificial intelligence in cybersecurity market, by region
15.2
KNOWLEDGESTORE: MARKETSANDMARKETS’ SUBSCRIPTION PORTAL
15.3
CUSTOMIZATION OPTIONS
TABLE 1
USD DOLLAR EXCHANGE RATE, 2020–2024
TABLE 3
GLOBAL GENERATIVE AI CYBERSECURITY MARKET SIZE AND GROWTH RATE, 2020–2024 (USD MILLION, Y-O-Y %)
TABLE 4
GLOBAL GENERATIVE AI CYBERSECURITY MARKET SIZE AND GROWTH RATE, 2025–2031 (USD MILLION, Y-O-Y %)
TABLE 5
GENERATIVE AI CYBERSECURITY MARKET: ECOSYSTEM
TABLE 6
NORTH AMERICA: REGULATORY BODIES, GOVERNMENT AGENCIES, AND OTHER ORGANIZATIONS
TABLE 7
EUROPE: REGULATORY BODIES, GOVERNMENT AGENCIES, AND OTHER ORGANIZATIONS
TABLE 8
ASIA PACIFIC: REGULATORY BODIES, GOVERNMENT AGENCIES, AND OTHER ORGANIZATIONS
TABLE 9
MIDDLE EAST & AFRICA: REGULATORY BODIES, GOVERNMENT AGENCIES, AND OTHER ORGANIZATIONS
TABLE 10
LATIN AMERICA: REGULATORY BODIES, GOVERNMENT AGENCIES, AND OTHER ORGANIZATIONS
TABLE 11
PATENTS FILED, 2019–2025
TABLE 12
GENERATIVE AI CYBERSECURITY MARKET: KEY PATENTS, 2024–2025
TABLE 13
AVERAGE SELLING PRICE OF KEY PLAYERS, BY OFFERING, 2025
TABLE 14
AVERAGE SELLING PRICE, BY SECURITY TYPE, 2025
TABLE 15
GENERATIVE AI CYBERSECURITY MARKET: KEY CONFERENCES & EVENTS, 2024–2025
TABLE 16
PORTERS’ FIVE FORCES’ IMPACT ON GENERATIVE AI CYBERSECURITY MARKET
TABLE 17
INFLUENCE OF STAKEHOLDERS ON BUYING PROCESS FOR TOP THREE GENERATIVE AI-BASED CYBERSECURITY VERTICALS
TABLE 18
KEY BUYING CRITERIA FOR TOP THREE GENERATIVE AI-BASED CYBERSECURITY VERTICALS
TABLE 19
GENERATIVE AI CYBERSECURITY MARKET, BY OFFERING, 2020–2024 (USD MILLION)
TABLE 20
GENERATIVE AI CYBERSECURITY MARKET, BY OFFERING, 2025–2031 (USD MILLION)
TABLE 21
GENERATIVE AI CYBERSECURITY MARKET, SOFTWARE TYPE, 2020–2024 (USD MILLION)
TABLE 22
GENERATIVE AI CYBERSECURITY MARKET, BY SOFTWARE TYPE, 2025–2031 (USD MILLION)
TABLE 23
GENERATIVE AI-BASED CYBERSECURITY SOFTWARE MARKET, BY REGION, 2020–2024 (USD MILLION)
TABLE 24
GENERATIVE AI-BASED CYBERSECURITY SOFTWARE MARKET, BY REGION, 2025–2031 (USD MILLION)
TABLE 25
CYBERSECURITY SOFTWARE MARKET FOR GENERATIVE AI, BY REGION, 2020–2024 (USD MILLION)
TABLE 26
CYBERSECURITY SOFTWARE MARKET FOR GENERATIVE AI, BY REGION, 2025–2031 (USD MILLION)
TABLE 27
GENERATIVE AI CYBERSECURITY SOFTWARE MARKET, BY DEPLOYMENT MODE, 2020–2024 (USD MILLION)
TABLE 28
GENERATIVE AI CYBERSECURITY SOFTWARE MARKET, BY DEPLOYMENT MODE, 2025–2031 (USD MILLION)
TABLE 29
CLOUD: GENERATIVE AI CYBERSECURITY MARKET, BY REGION, 2020–2024 (USD MILLION)
TABLE 30
CLOUD: GENERATIVE AI CYBERSECURITY MARKET, BY REGION, 2025–2031 (USD MILLION)
TABLE 31
ON-PREMISES: GENERATIVE AI CYBERSECURITY MARKET, BY REGION, 2020–2024 (USD MILLION)
TABLE 32
ON-PREMISES: GENERATIVE AI CYBERSECURITY MARKET, BY REGION, 2025–2031 (USD MILLION)
TABLE 33
GENERATIVE AI CYBERSECURITY MARKET, BY SERVICE, 2020–2024 (USD MILLION)
TABLE 34
GENERATIVE AI CYBERSECURITY MARKET, BY SERVICE, 2025–2031 (USD MILLION)
TABLE 35
GENERATIVE AI CYBERSECURITY MARKET, BY PROFESSIONAL SERVICE, 2020–2024 (USD MILLION)
TABLE 36
GENERATIVE AI CYBERSECURITY MARKET, BY PROFESSIONAL SERVICE, 2025–2031 (USD MILLION)
TABLE 37
TRAINING & CONSULTING: GENERATIVE AI CYBERSECURITY MARKET, BY REGION, 2020–2024 (USD MILLION)
TABLE 38
TRAINING & CONSULTING: GENERATIVE AI CYBERSECURITY MARKET, BY REGION, 2025–2031 (USD MILLION)
TABLE 39
SYSTEM INTEGRATION & IMPLEMENTATION: GENERATIVE AI CYBERSECURITY MARKET, BY REGION, 2020–2024 (USD MILLION)
TABLE 40
SYSTEM INTEGRATION & IMPLEMENTATION: GENERATIVE AI CYBERSECURITY MARKET, BY REGION, 2025–2031 (USD MILLION)
TABLE 41
SUPPORT & MAINTENANCE: GENERATIVE AI CYBERSECURITY MARKET, BY REGION, 2020–2024 (USD MILLION)
TABLE 42
SUPPORT & MAINTENANCE: GENERATIVE AI CYBERSECURITY MARKET, BY REGION, 2025–2031 (USD MILLION)
TABLE 43
MANAGED SERVICES: GENERATIVE AI CYBERSECURITY MARKET, BY REGION, 2020–2024 (USD MILLION)
TABLE 44
MANAGED SERVICES: GENERATIVE AI CYBERSECURITY MARKET, BY REGION, 2025–2031 (USD MILLION)
TABLE 45
CYBERSECURITY SOFTWARE MARKET FOR GENERATIVE AI, BY TYPE, 2020–2024 (USD MILLION)
TABLE 46
CYBERSECURITY SOFTWARE MARKET FOR GENERATIVE AI, BY TYPE, 2025–2031 (USD MILLION)
TABLE 47
GENERATIVE AI TRAINING DATA SECURITY SOFTWARE MARKET, BY REGION, 2020–2024 (USD MILLION)
TABLE 48
GENERATIVE AI TRAINING DATA SECURITY SOFTWARE MARKET, BY REGION, 2025–2031 (USD MILLION)
TABLE 49
GENERATIVE AI MODEL SECURITY SOFTWARE MARKET, BY REGION, 2020–2024 (USD MILLION)
TABLE 50
GENERATIVE AI MODEL SECURITY SOFTWARE MARKET, BY REGION, 2025–2031 (USD MILLION)
TABLE 51
GENERATIVE AI INFRASTRUCTURE SECURITY SOFTWARE MARKET, BY REGION, 2020–2024 (USD MILLION)
TABLE 52
GENERATIVE AI INFRASTRUCTURE SECURITY SOFTWARE MARKET, BY REGION, 2025–2031 (USD MILLION)
TABLE 53
GENERATIVE AI APPLICATION SECURITY SOFTWARE MARKET, BY REGION, 2020–2024 (USD MILLION)
TABLE 54
GENERATIVE AI APPLICATION SECURITY SOFTWARE MARKET, BY REGION, 2025–2031 (USD MILLION)
TABLE 55
GENERATIVE AI CYBERSECURITY MARKET, BY END USER, 2020–2024 (USD MILLION)
TABLE 56
GENERATIVE AI CYBERSECURITY MARKET, BY END USER, 2025–2031 (USD MILLION)
TABLE 57
END USERS: GENERATIVE AI-BASED CYBERSECURITY MARKET, BY VERTICAL, 2020–2024 (USD MILLION)
TABLE 58
END USERS: GENERATIVE-BASED AI CYBERSECURITY MARKET, BY VERTICAL, 2025–2031 (USD MILLION)
TABLE 59
GOVERNMENT & DEFENSE: GENERATIVE AI CYBERSECURITY MARKET, BY REGION, 2020–2024 (USD MILLION)
TABLE 60
GOVERNMENT & DEFENSE: GENERATIVE AI CYBERSECURITY MARKET, BY REGION, 2025–2031 (USD MILLION)
TABLE 61
BFSI: GENERATIVE AI CYBERSECURITY MARKET, BY REGION, 2020–2024 (USD MILLION)
TABLE 62
BFSI: GENERATIVE AI CYBERSECURITY MARKET, BY REGION, 2025–2031 (USD MILLION)
TABLE 63
IT & ITES: GENERATIVE AI CYBERSECURITY MARKET, BY REGION, 2020–2024 (USD MILLION)
TABLE 64
IT & ITES: GENERATIVE AI CYBERSECURITY MARKET, BY REGION, 2025–2031 (USD MILLION)
TABLE 65
HEALTHCARE & LIFE SCIENCES: GENERATIVE AI CYBERSECURITY MARKET, BY REGION, 2020–2024 (USD MILLION)
TABLE 66
HEALTHCARE & LIFE SCIENCES: GENERATIVE AI CYBERSECURITY MARKET, BY REGION, 2025–2031 (USD MILLION)
TABLE 67
RETAIL & ECOMMERCE: GENERATIVE AI CYBERSECURITY MARKET, BY REGION, 2020–2024 (USD MILLION)
TABLE 68
RETAIL & ECOMMERCE: GENERATIVE AI CYBERSECURITY MARKET, BY REGION, 2025–2031 (USD MILLION)
TABLE 69
MANUFACTURING: GENERATIVE AI CYBERSECURITY MARKET, BY REGION, 2020–2024 (USD MILLION)
TABLE 70
MANUFACTURING: GENERATIVE AI CYBERSECURITY MARKET, BY REGION, 2025–2031 (USD MILLION)
TABLE 71
ENERGY & UTILITIES: GENERATIVE AI CYBERSECURITY MARKET, BY REGION, 2020–2024 (USD MILLION)
TABLE 72
ENERGY & UTILITIES: GENERATIVE AI CYBERSECURITY MARKET, BY REGION, 2025–2031 (USD MILLION)
TABLE 73
TELECOMMUNICATIONS: GENERATIVE AI CYBERSECURITY MARKET, BY REGION, 2020–2024 (USD MILLION)
TABLE 74
TELECOMMUNICATIONS: GENERATIVE AI CYBERSECURITY MARKET, BY REGION, 2025–2031 (USD MILLION)
TABLE 75
AUTOMOTIVE, TRANSPORTATION, AND LOGISTICS: GENERATIVE AI CYBERSECURITY MARKET, BY REGION, 2020–2024 (USD MILLION)
TABLE 76
AUTOMOTIVE, TRANSPORTATION, AND LOGISTICS: GENERATIVE AI CYBERSECURITY MARKET, BY REGION, 2025–2031 (USD MILLION)
TABLE 77
MEDIA & ENTERTAINMENT: GENERATIVE AI CYBERSECURITY MARKET, BY REGION, 2020–2024 (USD MILLION)
TABLE 78
MEDIA & ENTERTAINMENT: GENERATIVE AI CYBERSECURITY MARKET, BY REGION, 2025–2031 (USD MILLION)
TABLE 79
OTHER END USERS: GENERATIVE AI CYBERSECURITY MARKET, BY REGION, 2020–2024 (USD MILLION)
TABLE 80
OTHER END USERS: GENERATIVE AI CYBERSECURITY MARKET, BY REGION, 2025–2031 (USD MILLION)
TABLE 81
END USERS: CYBERSECURITY FOR GENERATIVE AI MARKET, BY TYPE, 2020–2024 (USD MILLION)
TABLE 82
END USERS: CYBERSECURITY FOR GENERATIVE AI MARKET, BY TYPE, 2025–2031 (USD MILLION)
TABLE 83
CLOUD HYPERSCALERS: GENERATIVE AI CYBERSECURITY MARKET, BY REGION, 2020–2024 (USD MILLION)
TABLE 84
CLOUD HYPERSCALERS: GENERATIVE AI CYBERSECURITY MARKET, BY REGION, 2025–2031 (USD MILLION)
TABLE 85
MANAGED SECURITY SERVICE PROVIDERS: GENERATIVE AI CYBERSECURITY MARKET, BY REGION, 2020–2024 (USD MILLION)
TABLE 86
MANAGED SECURITY SERVICE PROVIDERS: GENERATIVE AI CYBERSECURITY MARKET, BY REGION, 2025–2031 (USD MILLION)
TABLE 87
GENERATIVE AI CYBERSECURITY MARKET, BY GENERATIVE AI PROVIDER, 2020–2024 (USD MILLION)
TABLE 88
GENERATIVE AI CYBERSECURITY MARKET, BY GENERATIVE AI PROVIDER, 2025–2031 (USD MILLION)
TABLE 89
FOUNDATION MODEL/LLM DEVELOPERS: GENERATIVE AI CYBERSECURITY MARKET, BY REGION, 2020–2024 (USD MILLION)
TABLE 90
FOUNDATION MODEL/LLM DEVELOPERS: GENERATIVE AI CYBERSECURITY MARKET, BY REGION, 2025–2031 (USD MILLION)
TABLE 91
DATA ANNOTATORS: GENERATIVE AI CYBERSECURITY MARKET, BY REGION, 2020–2024 (USD MILLION)
TABLE 92
DATA ANNOTATORS: GENERATIVE AI CYBERSECURITY MARKET, BY REGION, 2025–2031 (USD MILLION)
TABLE 93
CONTENT CREATION PLATFORM PROVIDERS: GENERATIVE AI CYBERSECURITY MARKET, BY REGION, 2020–2024 (USD MILLION)
TABLE 94
CONTENT CREATION PLATFORM PROVIDERS: GENERATIVE AI CYBERSECURITY MARKET, BY REGION, 2025–2031 (USD MILLION)
TABLE 95
GENERATIVE AI-AS-A-SERVICE PROVIDERS: GENERATIVE AI CYBERSECURITY MARKET, BY REGION, 2020–2024 (USD MILLION)
TABLE 96
GENERATIVE AI-AS-A-SERVICE PROVIDERS: GENERATIVE AI CYBERSECURITY MARKET, BY REGION, 2025–2031 (USD MILLION)
TABLE 97
GENERATIVE AI-BASED CYBERSECURITY SOFTWARE MARKET, BY TYPE, 2020–2024 (USD MILLION)
TABLE 98
GENERATIVE AI-BASED CYBERSECURITY SOFTWARE MARKET, BY TYPE, 2025–2031 (USD MILLION)
TABLE 99
THREAT DETECTION & INTELLIGENCE SOFTWARE: GENERATIVE AI CYBERSECURITY MARKET, BY REGION, 2020–2024 (USD MILLION)
TABLE 100
THREAT DETECTION & INTELLIGENCE SOFTWARE: GENERATIVE AI CYBERSECURITY MARKET, BY REGION, 2025–2031 (USD MILLION)
TABLE 101
RISK ASSESSMENT SOFTWARE: GENERATIVE AI CYBERSECURITY MARKET, BY REGION, 2020–2024 (USD MILLION)
TABLE 102
RISK ASSESSMENT SOFTWARE: GENERATIVE AI CYBERSECURITY MARKET, BY REGION, 2025–2031 (USD MILLION)
TABLE 103
EXPOSURE MANAGEMENT SOFTWARE: GENERATIVE AI CYBERSECURITY MARKET, BY REGION, 2020–2024 (USD MILLION)
TABLE 104
EXPOSURE MANAGEMENT SOFTWARE: GENERATIVE AI CYBERSECURITY MARKET, BY REGION, 2025–2031 (USD MILLION)
TABLE 105
PHISHING SIMULATION & PREVENTION SOFTWARE: GENERATIVE AI CYBERSECURITY MARKET, BY REGION, 2020–2024 (USD MILLION)
TABLE 106
PHISHING SIMULATION & PREVENTION SOFTWARE: GENERATIVE AI CYBERSECURITY MARKET, BY REGION, 2025–2031 (USD MILLION)
TABLE 107
REMEDIATION GUIDANCE SOFTWARE: GENERATIVE AI CYBERSECURITY MARKET, BY REGION, 2020–2024 (USD MILLION)
TABLE 108
REMEDIATION GUIDANCE SOFTWARE: GENERATIVE AI CYBERSECURITY MARKET, BY REGION, 2025–2031 (USD MILLION)
TABLE 109
THREAT HUNTING PLATFORMS: GENERATIVE AI CYBERSECURITY MARKET, BY REGION, 2020–2024 (USD MILLION)
TABLE 110
THREAT HUNTING PLATFORMS: GENERATIVE AI CYBERSECURITY MARKET, BY REGION, 2025–2031 (USD MILLION)
TABLE 111
CODE ANALYSIS SOFTWARE: GENERATIVE AI CYBERSECURITY MARKET, BY REGION, 2020–2024 (USD MILLION)
TABLE 112
CODE ANALYSIS SOFTWARE: GENERATIVE AI CYBERSECURITY MARKET, BY REGION, 2025–2031 (USD MILLION)
TABLE 113
GENERATIVE AI CYBERSECURITY MARKET, BY SECURITY TYPE, 2020–2024 (USD MILLION)
TABLE 114
GENERATIVE AI CYBERSECURITY MARKET, BY SECURITY TYPE, 2025–2031 (USD MILLION)
TABLE 115
GENERATIVE AI CYBERSECURITY MARKET, BY DATABASE SECURITY, 2020–2024 (USD MILLION)
TABLE 116
GENERATIVE AI CYBERSECURITY MARKET, BY DATABASE SECURITY, 2025–2031 (USD MILLION)
TABLE 117
DATA LOSS PREVENTION: GENERATIVE AI CYBERSECURITY MARKET, BY REGION, 2020–2024 (USD MILLION)
TABLE 118
DATA LOSS PREVENTION: GENERATIVE AI CYBERSECURITY MARKET, BY REGION, 2025–2031 (USD MILLION)
TABLE 119
DATA USAGE MONITORING: GENERATIVE AI CYBERSECURITY MARKET, BY REGION, 2020–2024 (USD MILLION)
TABLE 120
DATA USAGE MONITORING: GENERATIVE AI CYBERSECURITY MARKET, BY REGION, 2025–2031 (USD MILLION)
TABLE 121
DATA COMPLIANCE & GOVERNANCE: GENERATIVE AI CYBERSECURITY MARKET, BY REGION, 2020–2024 (USD MILLION)
TABLE 122
DATA COMPLIANCE & GOVERNANCE: GENERATIVE AI CYBERSECURITY MARKET, BY REGION, 2025–2031 (USD MILLION)
TABLE 123
DATA ENCRYPTION: GENERATIVE AI CYBERSECURITY MARKET, BY REGION, 2020–2024 (USD MILLION)
TABLE 124
DATA ENCRYPTION: GENERATIVE AI CYBERSECURITY MARKET, BY REGION, 2025–2031 (USD MILLION)
TABLE 125
DATA MASKING & TOKENIZATION: GENERATIVE AI CYBERSECURITY MARKET, BY REGION, 2020–2024 (USD MILLION)
TABLE 126
DATA MASKING & TOKENIZATION: GENERATIVE AI CYBERSECURITY MARKET, BY REGION, 2025–2031 (USD MILLION)
TABLE 127
ACCESS CONTROL: GENERATIVE AI CYBERSECURITY MARKET, BY REGION, 2020–2024 (USD MILLION)
TABLE 128
ACCESS CONTROL: GENERATIVE AI CYBERSECURITY MARKET, BY REGION, 2025–2031 (USD MILLION)
TABLE 129
GENERATIVE AI CYBERSECURITY MARKET, BY NETWORK SECURITY, 2020–2024 (USD MILLION)
TABLE 130
GENERATIVE AI CYBERSECURITY MARKET, BY NETWORK SECURITY, 2025–2031 (USD MILLION)
TABLE 131
NETWORK TRAFFIC ANALYSIS: GENERATIVE AI CYBERSECURITY MARKET, BY REGION, 2020–2024 (USD MILLION)
TABLE 132
NETWORK TRAFFIC ANALYSIS: GENERATIVE AI CYBERSECURITY MARKET, BY REGION, 2025–2031 (USD MILLION)
TABLE 133
SECURE ACCESS SERVICE EDGE: GENERATIVE AI CYBERSECURITY MARKET, BY REGION, 2020–2024 (USD MILLION)
TABLE 134
SECURE ACCESS SERVICE EDGE: GENERATIVE AI CYBERSECURITY MARKET, BY REGION, 2025–2031 (USD MILLION)
TABLE 135
ZERO TRUST NETWORK ACCESS: GENERATIVE AI CYBERSECURITY MARKET, BY REGION, 2020–2024 (USD MILLION)
TABLE 136
ZERO TRUST NETWORK ACCESS: GENERATIVE AI CYBERSECURITY MARKET, BY REGION, 2025–2031 (USD MILLION)
TABLE 137
FIREWALLS: GENERATIVE AI CYBERSECURITY MARKET, BY REGION, 2020–2024 (USD MILLION)
TABLE 138
FIREWALLS: GENERATIVE AI CYBERSECURITY MARKET, BY REGION, 2025–2031 (USD MILLION)
TABLE 139
INTRUSION DETECTION/PREVENTION SYSTEMS: GENERATIVE AI CYBERSECURITY MARKET, BY REGION, 2020–2024 (USD MILLION)
TABLE 140
INTRUSION DETECTION/PREVENTION SYSTEMS: GENERATIVE AI CYBERSECURITY MARKET, BY REGION, 2025–2031 (USD MILLION)
TABLE 141
VPNS & SECURE TUNNELING: GENERATIVE AI CYBERSECURITY MARKET, BY REGION, 2020–2024 (USD MILLION)
TABLE 142
VPNS & SECURE TUNNELING: GENERATIVE AI CYBERSECURITY MARKET, BY REGION, 2025–2031 (USD MILLION)
TABLE 143
GENERATIVE AI CYBERSECURITY MARKET, BY ENDPOINT SECURITY, 2020–2024 (USD MILLION)
TABLE 144
GENERATIVE AI CYBERSECURITY MARKET, BY ENDPOINT SECURITY, 2025–2031 (USD MILLION)
TABLE 145
ENDPOINT DETECTION & RESPONSE: GENERATIVE AI CYBERSECURITY MARKET, BY REGION, 2020–2024 (USD MILLION)
TABLE 146
ENDPOINT DETECTION & RESPONSE: GENERATIVE AI CYBERSECURITY MARKET, BY REGION, 2025–2031 (USD MILLION)
TABLE 147
ENDPOINT PROTECTION PLATFORMS: GENERATIVE AI CYBERSECURITY MARKET, BY REGION, 2020–2024 (USD MILLION)
TABLE 148
ENDPOINT PROTECTION PLATFORMS: GENERATIVE AI CYBERSECURITY MARKET, BY REGION, 2025–2031 (USD MILLION)
TABLE 149
GENERATIVE AI CYBERSECURITY MARKET, BY APPLICATION SECURITY, 2020–2024 (USD MILLION)
TABLE 150
GENERATIVE AI CYBERSECURITY MARKET, BY APPLICATION SECURITY, 2025–2031 (USD MILLION)
TABLE 151
STATIC APPLICATION SECURITY TESTING: GENERATIVE AI CYBERSECURITY MARKET, BY REGION, 2020–2024 (USD MILLION)
TABLE 152
STATIC APPLICATION SECURITY TESTING: GENERATIVE AI CYBERSECURITY MARKET, BY REGION, 2025–2031 (USD MILLION)
TABLE 153
DYNAMIC APPLICATION SECURITY TESTING: GENERATIVE AI CYBERSECURITY MARKET, BY REGION, 2020–2024 (USD MILLION)
TABLE 154
DYNAMIC APPLICATION SECURITY TESTING: GENERATIVE AI CYBERSECURITY MARKET, BY REGION, 2025–2031 (USD MILLION)
TABLE 155
LLM SECURITY: GENERATIVE AI CYBERSECURITY MARKET, BY REGION, 2020–2024 (USD MILLION)
TABLE 156
LLM SECURITY: GENERATIVE AI CYBERSECURITY MARKET, BY REGION, 2025–2031 (USD MILLION)
TABLE 157
RUNTIME PROTECTION: GENERATIVE AI CYBERSECURITY MARKET, BY REGION, 2020–2024 (USD MILLION)
TABLE 158
RUNTIME PROTECTION: GENERATIVE AI CYBERSECURITY MARKET, BY REGION, 2025–2031 (USD MILLION)
TABLE 159
INCIDENT RESPONSE & RECOVERY: GENERATIVE AI CYBERSECURITY MARKET, BY REGION, 2020–2024 (USD MILLION)
TABLE 160
INCIDENT RESPONSE & RECOVERY: GENERATIVE AI CYBERSECURITY MARKET, BY REGION, 2025–2031 (USD MILLION)
TABLE 161
GOVERNANCE, RISK, AND COMPLIANCE: GENERATIVE AI CYBERSECURITY MARKET, BY REGION, 2020–2024 (USD MILLION)
TABLE 162
GOVERNANCE, RISK, AND COMPLIANCE: GENERATIVE AI CYBERSECURITY MARKET, BY REGION, 2025–2031 (USD MILLION)
TABLE 163
GENERATIVE AI CYBERSECURITY MARKET, BY REGION, 2020–2024 (USD MILLION)
TABLE 164
GENERATIVE AI CYBERSECURITY MARKET, BY REGION, 2025–2031 (USD MILLION)
TABLE 165
NORTH AMERICA: GENERATIVE AI CYBERSECURITY MARKET, BY OFFERING, 2020–2024 (USD MILLION)
TABLE 166
NORTH AMERICA: GENERATIVE AI CYBERSECURITY MARKET, BY OFFERING, 2025–2031 (USD MILLION)
TABLE 167
NORTH AMERICA: GENERATIVE AI CYBERSECURITY MARKET, BY SOFTWARE TYPE, 2020–2024 (USD MILLION)
TABLE 168
NORTH AMERICA: GENERATIVE AI CYBERSECURITY MARKET, BY SOFTWARE TYPE, 2025–2031 (USD MILLION)
TABLE 169
NORTH AMERICA: GENERATIVE AI CYBERSECURITY MARKET, BY SOFTWARE DEPLOYMENT MODE, 2020–2024 (USD MILLION)
TABLE 170
NORTH AMERICA: GENERATIVE AI CYBERSECURITY MARKET, BY SOFTWARE DEPLOYMENT MODE, 2025–2031 (USD MILLION)
TABLE 171
NORTH AMERICA: GENERATIVE AI CYBERSECURITY MARKET, BY SERVICE, 2020–2024 (USD MILLION)
TABLE 172
NORTH AMERICA: GENERATIVE AI CYBERSECURITY MARKET, BY SERVICE, 2025–2031 (USD MILLION)
TABLE 173
NORTH AMERICA: GENERATIVE AI CYBERSECURITY MARKET, BY PROFESSIONAL SERVICE, 2020–2024 (USD MILLION)
TABLE 174
NORTH AMERICA: GENERATIVE AI CYBERSECURITY MARKET, BY PROFESSIONAL SERVICE, 2025–2031 (USD MILLION)
TABLE 175
NORTH AMERICA: GENERATIVE AI-BASED CYBERSECURITY SOFTWARE MARKET, BY TYPE, 2020–2024 (USD MILLION)
TABLE 176
NORTH AMERICA: GENERATIVE AI-BASED CYBERSECURITY SOFTWARE MARKET, BY TYPE, 2025–2031 (USD MILLION)
TABLE 177
NORTH AMERICA: CYBERSECURITY SOFTWARE MARKET FOR GENERATIVE AI, BY TYPE, 2020–2024 (USD MILLION)
TABLE 178
NORTH AMERICA: CYBERSECURITY SOFTWARE MARKET FOR GENERATIVE AI, BY TYPE, 2025–2031 (USD MILLION)
TABLE 179
NORTH AMERICA: GENERATIVE AI CYBERSECURITY MARKET, BY SECURITY TYPE, 2020–2024 (USD MILLION)
TABLE 180
NORTH AMERICA: GENERATIVE AI CYBERSECURITY MARKET, BY SECURITY TYPE, 2025–2031 (USD MILLION)
TABLE 181
NORTH AMERICA: GENERATIVE AI CYBERSECURITY MARKET, BY END USER, 2020–2024 (USD MILLION)
TABLE 182
NORTH AMERICA: GENERATIVE AI CYBERSECURITY MARKET, BY END USER, 2025–2031 (USD MILLION)
TABLE 183
NORTH AMERICA: GENERATIVE AI-BASED CYBERSECURITY END USERS, BY VERTICAL, 2020–2024 (USD MILLION)
TABLE 184
NORTH AMERICA: GENERATIVE AI-BASED CYBERSECURITY END USERS, BY VERTICAL, 2025–2031 (USD MILLION)
TABLE 185
NORTH AMERICA: CYBERSECURITY SOFTWARE MARKET FOR GENERATIVE AI, BY END USER, 2020–2024 (USD MILLION)
TABLE 186
NORTH AMERICA: CYBERSECURITY SOFTWARE MARKET FOR GENERATIVE AI, BY END USER, 2025–2031 (USD MILLION)
TABLE 187
NORTH AMERICA: GENERATIVE AI CYBERSECURITY MARKET, BY COUNTRY, 2020–2024 (USD MILLION)
TABLE 188
NORTH AMERICA: GENERATIVE AI CYBERSECURITY MARKET, BY COUNTRY, 2025–2031 (USD MILLION)
TABLE 189
US: GENERATIVE AI CYBERSECURITY MARKET, BY OFFERING, 2020–2024 (USD MILLION)
TABLE 190
US: GENERATIVE AI CYBERSECURITY MARKET, BY OFFERING, 2025–2031 (USD MILLION)
TABLE 191
US: GENERATIVE AI CYBERSECURITY MARKET, BY SOFTWARE TYPE, 2020–2024 (USD MILLION)
TABLE 192
US: GENERATIVE AI CYBERSECURITY MARKET, BY SOFTWARE TYPE, 2025–2031 (USD MILLION)
TABLE 193
US: GENERATIVE AI CYBERSECURITY MARKET, BY SOFTWARE DEPLOYMENT MODE, 2020–2024 (USD MILLION)
TABLE 194
US: GENERATIVE AI CYBERSECURITY MARKET, BY SOFTWARE DEPLOYMENT MODE, 2025–2031 (USD MILLION)
TABLE 195
US: GENERATIVE AI CYBERSECURITY MARKET, BY SERVICE, 2020–2024 (USD MILLION)
TABLE 196
US: GENERATIVE AI CYBERSECURITY MARKET, BY SERVICE, 2025–2031 (USD MILLION)
TABLE 197
US: GENERATIVE AI CYBERSECURITY MARKET, BY PROFESSIONAL SERVICE, 2020–2024 (USD MILLION)
TABLE 198
US: GENERATIVE AI CYBERSECURITY MARKET, BY PROFESSIONAL SERVICE, 2025–2031 (USD MILLION)
TABLE 199
US: GENERATIVE AI-BASED CYBERSECURITY SOFTWARE MARKET, BY TYPE, 2020–2024 (USD MILLION)
TABLE 200
US: GENERATIVE AI-BASED CYBERSECURITY SOFTWARE MARKET, BY TYPE, 2025–2031 (USD MILLION)
TABLE 201
US: CYBERSECURITY SOFTWARE MARKET FOR GENERATIVE AI, BY TYPE, 2020–2024 (USD MILLION)
TABLE 202
US: CYBERSECURITY SOFTWARE MARKET FOR GENERATIVE AI, BY TYPE, 2025–2031 (USD MILLION)
TABLE 203
US: GENERATIVE AI CYBERSECURITY MARKET, BY SECURITY TYPE, 2020–2024 (USD MILLION)
TABLE 204
US: GENERATIVE AI CYBERSECURITY MARKET, BY SECURITY TYPE, 2025–2031 (USD MILLION)
TABLE 205
US: GENERATIVE AI CYBERSECURITY MARKET, BY END USER, 2020–2024 (USD MILLION)
TABLE 206
US: GENERATIVE AI CYBERSECURITY MARKET, BY END USER, 2025–2031 (USD MILLION)
TABLE 207
US: GENERATIVE AI-BASED CYBERSECURITY END USERS, BY VERTICAL, 2020–2024 (USD MILLION)
TABLE 208
US: GENERATIVE AI-BASED CYBERSECURITY END USERS, BY VERTICAL, 2025–2031 (USD MILLION)
TABLE 209
US: CYBERSECURITY SOFTWARE MARKET FOR GENERATIVE AI, BY END USER, 2020–2024 (USD MILLION)
TABLE 210
US: CYBERSECURITY SOFTWARE MARKET FOR GENERATIVE AI, BY END USER, 2025–2031 (USD MILLION)
TABLE 211
CANADA: GENERATIVE AI CYBERSECURITY MARKET, BY OFFERING, 2020–2024 (USD MILLION)
TABLE 212
CANADA: GENERATIVE AI CYBERSECURITY MARKET, BY OFFERING, 2025–2031 (USD MILLION)
TABLE 213
CANADA: GENERATIVE AI CYBERSECURITY MARKET, BY SOFTWARE TYPE, 2020–2024 (USD MILLION)
TABLE 214
CANADA: GENERATIVE AI CYBERSECURITY MARKET, BY SOFTWARE TYPE, 2025–2031 (USD MILLION)
TABLE 215
CANADA: GENERATIVE AI CYBERSECURITY MARKET, BY SOFTWARE DEPLOYMENT MODE, 2020–2024 (USD MILLION)
TABLE 216
CANADA: GENERATIVE AI CYBERSECURITY MARKET, BY SOFTWARE DEPLOYMENT MODE, 2025–2031 (USD MILLION)
TABLE 217
CANADA: GENERATIVE AI CYBERSECURITY MARKET, BY SERVICE, 2020–2024 (USD MILLION)
TABLE 218
CANADA: GENERATIVE AI CYBERSECURITY MARKET, BY SERVICE, 2025–2031 (USD MILLION)
TABLE 219
CANADA: GENERATIVE AI CYBERSECURITY MARKET, BY PROFESSIONAL SERVICE, 2020–2024 (USD MILLION)
TABLE 220
CANADA: GENERATIVE AI CYBERSECURITY MARKET, BY PROFESSIONAL SERVICE, 2025–2031 (USD MILLION)
TABLE 221
CANADA: GENERATIVE AI-BASED CYBERSECURITY SOFTWARE MARKET, BY TYPE, 2020–2024 (USD MILLION)
TABLE 222
CANADA: GENERATIVE AI-BASED CYBERSECURITY SOFTWARE MARKET, BY TYPE, 2025–2031 (USD MILLION)
TABLE 223
CANADA: CYBERSECURITY SOFTWARE MARKET FOR GENERATIVE AI, BY TYPE, 2020–2024 (USD MILLION)
TABLE 224
CANADA: CYBERSECURITY SOFTWARE MARKET FOR GENERATIVE AI, BY TYPE, 2025–2031 (USD MILLION)
TABLE 225
CANADA: GENERATIVE AI CYBERSECURITY MARKET, BY SECURITY TYPE, 2020–2024 (USD MILLION)
TABLE 226
CANADA: GENERATIVE AI CYBERSECURITY MARKET, BY SECURITY TYPE, 2025–2031 (USD MILLION)
TABLE 227
CANADA: GENERATIVE AI CYBERSECURITY MARKET, BY END USER, 2020–2024 (USD MILLION)
TABLE 228
CANADA: GENERATIVE AI CYBERSECURITY MARKET, BY END USER, 2025–2031 (USD MILLION)
TABLE 229
CANADA: GENERATIVE AI-BASED CYBERSECURITY END USERS, BY VERTICAL, 2020–2024 (USD MILLION)
TABLE 230
CANADA: GENERATIVE AI-BASED CYBERSECURITY END USERS, BY VERTICAL, 2025–2031 (USD MILLION)
TABLE 231
CANADA: CYBERSECURITY SOFTWARE MARKET FOR GENERATIVE AI, BY END USER, 2020–2024 (USD MILLION)
TABLE 232
CANADA: CYBERSECURITY SOFTWARE MARKET FOR GENERATIVE AI, BY END USER, 2025–2031 (USD MILLION)
TABLE 233
EUROPE: GENERATIVE AI CYBERSECURITY MARKET, BY OFFERING, 2020–2024 (USD MILLION)
TABLE 234
EUROPE: GENERATIVE AI CYBERSECURITY MARKET, BY OFFERING, 2025–2031 (USD MILLION)
TABLE 235
EUROPE: GENERATIVE AI CYBERSECURITY MARKET, BY SOFTWARE TYPE, 2020–2024 (USD MILLION)
TABLE 236
EUROPE: GENERATIVE AI CYBERSECURITY MARKET, BY SOFTWARE TYPE, 2025–2031 (USD MILLION)
TABLE 237
EUROPE: GENERATIVE AI CYBERSECURITY MARKET, BY SOFTWARE DEPLOYMENT MODE, 2020–2024 (USD MILLION)
TABLE 238
EUROPE: GENERATIVE AI CYBERSECURITY MARKET, BY SOFTWARE DEPLOYMENT MODE, 2025–2031 (USD MILLION)
TABLE 239
EUROPE: GENERATIVE AI CYBERSECURITY MARKET, BY SERVICE, 2020–2024 (USD MILLION)
TABLE 240
EUROPE: GENERATIVE AI CYBERSECURITY MARKET, BY SERVICE, 2025–2031 (USD MILLION)
TABLE 241
EUROPE: GENERATIVE AI CYBERSECURITY MARKET, BY PROFESSIONAL SERVICE, 2020–2024 (USD MILLION)
TABLE 242
EUROPE: GENERATIVE AI CYBERSECURITY MARKET, BY PROFESSIONAL SERVICE, 2025–2031 (USD MILLION)
TABLE 243
EUROPE: GENERATIVE AI-BASED CYBERSECURITY SOFTWARE MARKET, BY TYPE, 2020–2024 (USD MILLION)
TABLE 244
EUROPE: GENERATIVE AI-BASED CYBERSECURITY SOFTWARE MARKET, BY TYPE 2025–2031 (USD MILLION)
TABLE 245
EUROPE: CYBERSECURITY SOFTWARE MARKET FOR GENERATIVE AI, BY TYPE, 2020–2024 (USD MILLION)
TABLE 246
EUROPE: CYBERSECURITY SOFTWARE MARKET FOR GENERATIVE AI, BY TYPE, 2025–2031 (USD MILLION)
TABLE 247
EUROPE: GENERATIVE AI CYBERSECURITY MARKET, BY SECURITY TYPE, 2020–2024 (USD MILLION)
TABLE 248
EUROPE: GENERATIVE AI CYBERSECURITY MARKET, BY SECURITY TYPE, 2025–2031 (USD MILLION)
TABLE 249
EUROPE: GENERATIVE AI CYBERSECURITY MARKET, BY END USER, 2020–2024 (USD MILLION)
TABLE 250
EUROPE: GENERATIVE AI CYBERSECURITY MARKET, BY END USER, 2025–2031 (USD MILLION)
TABLE 251
EUROPE: GENERATIVE AI-BASED CYBERSECURITY END USERS, BY VERTICAL, 2020–2024 (USD MILLION)
TABLE 252
EUROPE: GENERATIVE AI-BASED CYBERSECURITY END USERS, BY VERTICAL, 2025–2031 (USD MILLION)
TABLE 253
EUROPE: CYBERSECURITY SOFTWARE MARKET FOR GENERATIVE AI, BY END USER, 2020–2024 (USD MILLION)
TABLE 254
EUROPE: CYBERSECURITY SOFTWARE MARKET FOR GENERATIVE AI, BY END USER, 2025–2031 (USD MILLION)
TABLE 255
EUROPE: GENERATIVE AI CYBERSECURITY MARKET, BY COUNTRY, 2020–2024 (USD MILLION)
TABLE 256
EUROPE: GENERATIVE AI CYBERSECURITY MARKET, BY COUNTRY, 2025–2031 (USD MILLION)
TABLE 257
UK: GENERATIVE AI CYBERSECURITY MARKET, BY OFFERING, 2020–2024 (USD MILLION)
TABLE 258
UK: GENERATIVE AI CYBERSECURITY MARKET, BY OFFERING, 2025–2031 (USD MILLION)
TABLE 259
UK: GENERATIVE AI CYBERSECURITY MARKET, BY SOFTWARE TYPE, 2020–2024 (USD MILLION)
TABLE 260
UK: GENERATIVE AI CYBERSECURITY MARKET, BY SOFTWARE TYPE, 2025–2031 (USD MILLION)
TABLE 261
UK: GENERATIVE AI CYBERSECURITY MARKET, BY SOFTWARE DEPLOYMENT MODE, 2020–2024 (USD MILLION)
TABLE 262
UK: GENERATIVE AI CYBERSECURITY MARKET, BY SOFTWARE DEPLOYMENT MODE, 2025–2031 (USD MILLION)
TABLE 263
UK: GENERATIVE AI CYBERSECURITY MARKET, BY SERVICE, 2020–2024 (USD MILLION)
TABLE 264
UK: GENERATIVE AI CYBERSECURITY MARKET, BY SERVICE, 2025–2031 (USD MILLION)
TABLE 265
UK: GENERATIVE AI CYBERSECURITY MARKET, BY PROFESSIONAL SERVICE, 2020–2024 (USD MILLION)
TABLE 266
UK: GENERATIVE AI CYBERSECURITY MARKET, BY PROFESSIONAL SERVICE, 2025–2031 (USD MILLION)
TABLE 267
UK: GENERATIVE AI-BASED CYBERSECURITY SOFTWARE MARKET, BY TYPE, 2020–2024 (USD MILLION)
TABLE 268
UK: GENERATIVE AI-BASED CYBERSECURITY SOFTWARE MARKET, BY TYPE, 2025–2031 (USD MILLION)
TABLE 269
UK: CYBERSECURITY SOFTWARE MARKET FOR GENERATIVE AI, BY TYPE, 2020–2024 (USD MILLION)
TABLE 270
UK: CYBERSECURITY SOFTWARE MARKET FOR GENERATIVE AI, BY TYPE, 2025–2031 (USD MILLION)
TABLE 271
UK: GENERATIVE AI CYBERSECURITY MARKET, BY SECURITY TYPE, 2020–2024 (USD MILLION)
TABLE 272
UK: GENERATIVE AI CYBERSECURITY MARKET, BY SECURITY TYPE, 2025–2031 (USD MILLION)
TABLE 273
UK: GENERATIVE AI CYBERSECURITY MARKET, BY END USER, 2020–2024 (USD MILLION)
TABLE 274
UK: GENERATIVE AI CYBERSECURITY MARKET, BY END USER, 2025–2031 (USD MILLION)
TABLE 275
UK: GENERATIVE AI-BASED CYBERSECURITY END USERS, BY VERTICAL, 2020–2024 (USD MILLION)
TABLE 276
UK: GENERATIVE AI-BASED CYBERSECURITY END USERS, BY VERTICAL, 2025–2031 (USD MILLION)
TABLE 277
UK: CYBERSECURITY SOFTWARE MARKET FOR GENERATIVE AI, BY END USER, 2020–2024 (USD MILLION)
TABLE 278
UK: CYBERSECURITY SOFTWARE MARKET FOR GENERATIVE AI, BY END USER, 2025–2031 (USD MILLION)
TABLE 279
GERMANY: GENERATIVE AI CYBERSECURITY MARKET, BY OFFERING, 2020–2024 (USD MILLION)
TABLE 280
GERMANY: GENERATIVE AI CYBERSECURITY MARKET, BY OFFERING, 2025–2031 (USD MILLION)
TABLE 281
GERMANY: GENERATIVE AI CYBERSECURITY MARKET, BY SOFTWARE TYPE, 2020–2024 (USD MILLION)
TABLE 282
GERMANY: GENERATIVE AI CYBERSECURITY MARKET, BY SOFTWARE TYPE, 2025–2031 (USD MILLION)
TABLE 283
GERMANY: GENERATIVE AI CYBERSECURITY MARKET, BY SOFTWARE DEPLOYMENT MODE, 2020–2024 (USD MILLION)
TABLE 284
GERMANY: GENERATIVE AI CYBERSECURITY MARKET, BY SOFTWARE DEPLOYMENT MODE, 2025–2031 (USD MILLION)
TABLE 285
GERMANY: GENERATIVE AI CYBERSECURITY MARKET, BY SERVICE, 2020–2024 (USD MILLION)
TABLE 286
GERMANY: GENERATIVE AI CYBERSECURITY MARKET, BY SERVICE, 2025–2031 (USD MILLION)
TABLE 287
GERMANY: GENERATIVE AI CYBERSECURITY MARKET, BY PROFESSIONAL SERVICE, 2020–2024 (USD MILLION)
TABLE 288
GERMANY: GENERATIVE AI CYBERSECURITY MARKET, BY PROFESSIONAL SERVICE, 2025–2031 (USD MILLION)
TABLE 289
GERMANY: GENERATIVE AI-BASED CYBERSECURITY SOFTWARE MARKET, BY TYPE, 2020–2024 (USD MILLION)
TABLE 290
GERMANY: GENERATIVE AI-BASED CYBERSECURITY SOFTWARE MARKET, BY TYPE, 2025–2031 (USD MILLION)
TABLE 291
GERMANY: CYBERSECURITY SOFTWARE MARKET FOR GENERATIVE AI, BY TYPE, 2020–2024 (USD MILLION)
TABLE 292
GERMANY: CYBERSECURITY SOFTWARE MARKET FOR GENERATIVE AI, BY TYPE, 2025–2031 (USD MILLION)
TABLE 293
GERMANY: GENERATIVE AI CYBERSECURITY MARKET, BY SECURITY TYPE, 2020–2024 (USD MILLION)
TABLE 294
GERMANY: GENERATIVE AI CYBERSECURITY MARKET, BY SECURITY TYPE, 2025–2031 (USD MILLION)
TABLE 295
GERMANY: GENERATIVE AI CYBERSECURITY MARKET, BY END USER, 2020–2024 (USD MILLION)
TABLE 296
GERMANY: GENERATIVE AI CYBERSECURITY MARKET, BY END USER, 2025–2031 (USD MILLION)
TABLE 297
GERMANY: GENERATIVE AI-BASED CYBERSECURITY END USERS, BY VERTICAL, 2020–2024 (USD MILLION)
TABLE 298
GERMANY: GENERATIVE AI-BASED CYBERSECURITY END USERS, BY VERTICAL, 2025–2031 (USD MILLION)
TABLE 299
GERMANY: CYBERSECURITY SOFTWARE MARKET FOR GENERATIVE AI, BY END USER, 2020–2024 (USD MILLION)
TABLE 300
GERMANY: CYBERSECURITY SOFTWARE MARKET FOR GENERATIVE AI, BY END USER, 2025–2031 (USD MILLION)
TABLE 301
FRANCE: GENERATIVE AI CYBERSECURITY MARKET, BY OFFERING, 2020–2024 (USD MILLION)
TABLE 302
FRANCE: GENERATIVE AI CYBERSECURITY MARKET, BY OFFERING, 2025–2031 (USD MILLION)
TABLE 303
FRANCE: GENERATIVE AI CYBERSECURITY MARKET, BY SOFTWARE TYPE, 2020–2024 (USD MILLION)
TABLE 304
FRANCE: GENERATIVE AI CYBERSECURITY MARKET, BY SOFTWARE TYPE, 2025–2031 (USD MILLION)
TABLE 305
FRANCE: GENERATIVE AI CYBERSECURITY MARKET, BY SOFTWARE DEPLOYMENT MODE, 2020–2024 (USD MILLION)
TABLE 306
FRANCE: GENERATIVE AI CYBERSECURITY MARKET, BY SOFTWARE DEPLOYMENT MODE, 2025–2031 (USD MILLION)
TABLE 307
FRANCE: GENERATIVE AI CYBERSECURITY MARKET, BY SERVICE, 2020–2024 (USD MILLION)
TABLE 308
FRANCE: GENERATIVE AI CYBERSECURITY MARKET, BY SERVICE, 2025–2031 (USD MILLION)
TABLE 309
FRANCE: GENERATIVE AI CYBERSECURITY MARKET, BY PROFESSIONAL SERVICE, 2020–2024 (USD MILLION)
TABLE 310
FRANCE: GENERATIVE AI CYBERSECURITY MARKET, BY PROFESSIONAL SERVICE, 2025–2031 (USD MILLION)
TABLE 311
FRANCE: GENERATIVE AI-BASED CYBERSECURITY SOFTWARE MARKET, BY TYPE, 2020–2024 (USD MILLION)
TABLE 312
FRANCE: GENERATIVE AI-BASED CYBERSECURITY SOFTWARE MARKET, BY TYPE, 2025–2031 (USD MILLION)
TABLE 313
FRANCE: CYBERSECURITY SOFTWARE MARKET FOR GENERATIVE AI, BY TYPE, 2020–2024 (USD MILLION)
TABLE 314
FRANCE: CYBERSECURITY SOFTWARE MARKET FOR GENERATIVE AI, BY TYPE, 2025–2031 (USD MILLION)
TABLE 315
FRANCE: GENERATIVE AI CYBERSECURITY MARKET, BY SECURITY TYPE, 2020–2024 (USD MILLION)
TABLE 316
FRANCE: GENERATIVE AI CYBERSECURITY MARKET, BY SECURITY TYPE, 2025–2031 (USD MILLION)
TABLE 317
FRANCE: GENERATIVE AI CYBERSECURITY MARKET, BY END USER, 2020–2024 (USD MILLION)
TABLE 318
FRANCE: GENERATIVE AI CYBERSECURITY MARKET, BY END USER, 2025–2031 (USD MILLION)
TABLE 319
FRANCE: GENERATIVE AI-BASED CYBERSECURITY END USERS, BY VERTICAL, 2020–2024 (USD MILLION)
TABLE 320
FRANCE: GENERATIVE AI-BASED CYBERSECURITY END USERS, BY VERTICAL, 2025–2031 (USD MILLION)
TABLE 321
FRANCE: CYBERSECURITY SOFTWARE MARKET FOR GENERATIVE AI, BY END USER, 2020–2024 (USD MILLION)
TABLE 322
FRANCE: CYBERSECURITY SOFTWARE MARKET FOR GENERATIVE AI, BY END USER, 2025–2031 (USD MILLION)
TABLE 323
REST OF EUROPE: GENERATIVE AI CYBERSECURITY MARKET, BY OFFERING, 2020–2024 (USD MILLION)
TABLE 324
REST OF EUROPE: GENERATIVE AI CYBERSECURITY MARKET, BY OFFERING, 2025–2031 (USD MILLION)
TABLE 325
REST OF EUROPE: GENERATIVE AI CYBERSECURITY MARKET, BY SOFTWARE TYPE, 2020–2024 (USD MILLION)
TABLE 326
REST OF EUROPE: GENERATIVE AI CYBERSECURITY MARKET, BY SOFTWARE TYPE, 2025–2031 (USD MILLION)
TABLE 327
REST OF EUROPE: GENERATIVE AI CYBERSECURITY MARKET, BY SOFTWARE DEPLOYMENT MODE, 2020–2024 (USD MILLION)
TABLE 328
REST OF EUROPE: GENERATIVE AI CYBERSECURITY MARKET, BY SOFTWARE DEPLOYMENT MODE, 2025–2031 (USD MILLION)
TABLE 329
REST OF EUROPE: GENERATIVE AI CYBERSECURITY MARKET, BY SERVICE, 2020–2024 (USD MILLION)
TABLE 330
REST OF EUROPE: GENERATIVE AI CYBERSECURITY MARKET, BY SERVICE, 2025–2031 (USD MILLION)
TABLE 331
REST OF EUROPE: GENERATIVE AI CYBERSECURITY MARKET, BY PROFESSIONAL SERVICE, 2020–2024 (USD MILLION)
TABLE 332
REST OF EUROPE: GENERATIVE AI CYBERSECURITY MARKET, BY PROFESSIONAL SERVICE, 2025–2031 (USD MILLION)
TABLE 333
REST OF EUROPE: GENERATIVE AI-BASED CYBERSECURITY SOFTWARE MARKET, BY TYPE, 2020–2024 (USD MILLION)
TABLE 334
REST OF EUROPE: GENERATIVE AI-BASED CYBERSECURITY SOFTWARE MARKET, BY TYPE, 2025–2031 (USD MILLION)
TABLE 335
REST OF EUROPE: CYBERSECURITY SOFTWARE MARKET FOR GENERATIVE AI, BY TYPE, 2020–2024 (USD MILLION)
TABLE 336
REST OF EUROPE: CYBERSECURITY SOFTWARE MARKET FOR GENERATIVE AI, BY TYPE, 2025–2031 (USD MILLION)
TABLE 337
REST OF EUROPE: GENERATIVE AI CYBERSECURITY MARKET, BY SECURITY TYPE, 2020–2024 (USD MILLION)
TABLE 338
REST OF EUROPE: GENERATIVE AI CYBERSECURITY MARKET, BY SECURITY TYPE, 2025–2031 (USD MILLION)
TABLE 339
REST OF EUROPE: GENERATIVE AI CYBERSECURITY MARKET, BY END USER, 2020–2024 (USD MILLION)
TABLE 340
REST OF EUROPE: GENERATIVE AI CYBERSECURITY MARKET, BY END USER, 2025–2031 (USD MILLION)
TABLE 341
REST OF EUROPE: GENERATIVE AI-BASED CYBERSECURITY END USERS, BY VERTICAL, 2020–2024 (USD MILLION)
TABLE 342
REST OF EUROPE: GENERATIVE AI-BASED CYBERSECURITY END USERS, BY VERTICAL, 2025–2031 (USD MILLION)
TABLE 343
REST OF EUROPE: CYBERSECURITY SOFTWARE MARKET FOR GENERATIVE AI, BY END USER, 2020–2024 (USD MILLION)
TABLE 344
REST OF EUROPE: CYBERSECURITY SOFTWARE MARKET FOR GENERATIVE AI, BY END USER, 2025–2031 (USD MILLION)
TABLE 345
ASIA PACIFIC: GENERATIVE AI CYBERSECURITY MARKET, BY OFFERING, 2020–2024 (USD MILLION)
TABLE 346
ASIA PACIFIC: GENERATIVE AI CYBERSECURITY MARKET, BY OFFERING, 2025–2031 (USD MILLION)
TABLE 347
ASIA PACIFIC: GENERATIVE AI CYBERSECURITY MARKET, BY SOFTWARE TYPE, 2020–2024 (USD MILLION)
TABLE 348
ASIA PACIFIC: GENERATIVE AI CYBERSECURITY MARKET, BY SOFTWARE TYPE, 2025–2031 (USD MILLION)
TABLE 349
ASIA PACIFIC: GENERATIVE AI CYBERSECURITY MARKET, BY SOFTWARE DEPLOYMENT MODE, 2020–2024 (USD MILLION)
TABLE 350
ASIA PACIFIC: GENERATIVE AI CYBERSECURITY MARKET, BY SOFTWARE DEPLOYMENT MODE, 2025–2031 (USD MILLION)
TABLE 351
ASIA PACIFIC: GENERATIVE AI CYBERSECURITY MARKET, BY SERVICE, 2020–2024 (USD MILLION)
TABLE 352
ASIA PACIFIC: GENERATIVE AI CYBERSECURITY MARKET, BY SERVICE, 2025–2031 (USD MILLION)
TABLE 353
ASIA PACIFIC: GENERATIVE AI CYBERSECURITY MARKET, BY PROFESSIONAL SERVICE, 2020–2024 (USD MILLION)
TABLE 354
ASIA PACIFIC: GENERATIVE AI CYBERSECURITY MARKET, BY PROFESSIONAL SERVICE, 2025–2031 (USD MILLION)
TABLE 355
ASIA PACIFIC: GENERATIVE AI-BASED CYBERSECURITY SOFTWARE MARKET, BY TYPE, 2020–2024 (USD MILLION)
TABLE 356
ASIA PACIFIC: GENERATIVE AI-BASED CYBERSECURITY SOFTWARE MARKET, BY TYPE, 2025–2031 (USD MILLION)
TABLE 357
ASIA PACIFIC: CYBERSECURITY SOFTWARE MARKET FOR GENERATIVE AI, BY TYPE, 2020–2024 (USD MILLION)
TABLE 358
ASIA PACIFIC: CYBERSECURITY SOFTWARE MARKET FOR GENERATIVE AI, BY TYPE, 2025–2031 (USD MILLION)
TABLE 359
ASIA PACIFIC: GENERATIVE AI CYBERSECURITY MARKET, BY SECURITY TYPE, 2020–2024 (USD MILLION)
TABLE 360
ASIA PACIFIC: GENERATIVE AI CYBERSECURITY MARKET, BY SECURITY TYPE, 2025–2031 (USD MILLION)
TABLE 361
ASIA PACIFIC: GENERATIVE AI CYBERSECURITY MARKET, BY END USER, 2020–2024 (USD MILLION)
TABLE 362
ASIA PACIFIC: GENERATIVE AI CYBERSECURITY MARKET, BY END USER, 2025–2031 (USD MILLION)
TABLE 363
ASIA PACIFIC: GENERATIVE AI-BASED CYBERSECURITY END USERS, BY VERTICAL, 2020–2024 (USD MILLION)
TABLE 364
ASIA PACIFIC: GENERATIVE AI-BASED CYBERSECURITY END USERS, BY VERTICAL, 2025–2031 (USD MILLION)
TABLE 365
ASIA PACIFIC: CYBERSECURITY SOFTWARE MARKET FOR GENERATIVE AI, BY END USER, 2020–2024 (USD MILLION)
TABLE 366
ASIA PACIFIC: CYBERSECURITY SOFTWARE MARKET FOR GENERATIVE AI, BY END USER, 2025–2031 (USD MILLION)
TABLE 367
ASIA PACIFIC: GENERATIVE AI CYBERSECURITY MARKET, BY COUNTRY, 2020–2024 (USD MILLION)
TABLE 368
ASIA PACIFIC: GENERATIVE AI CYBERSECURITY MARKET, BY COUNTRY, 2025–2031 (USD MILLION)
TABLE 369
CHINA: GENERATIVE AI CYBERSECURITY MARKET, BY OFFERING, 2020–2024 (USD MILLION)
TABLE 370
CHINA: GENERATIVE AI CYBERSECURITY MARKET, BY OFFERING, 2025–2031 (USD MILLION)
TABLE 371
CHINA: GENERATIVE AI CYBERSECURITY MARKET, BY SOFTWARE TYPE, 2020–2024 (USD MILLION)
TABLE 372
CHINA: GENERATIVE AI CYBERSECURITY MARKET, BY SOFTWARE TYPE, 2025–2031 (USD MILLION)
TABLE 373
CHINA: GENERATIVE AI CYBERSECURITY MARKET, BY SOFTWARE DEPLOYMENT MODE, 2020–2024 (USD MILLION)
TABLE 374
CHINA: GENERATIVE AI CYBERSECURITY MARKET, BY SOFTWARE DEPLOYMENT MODE, 2025–2031 (USD MILLION)
TABLE 375
CHINA: GENERATIVE AI CYBERSECURITY MARKET, BY SERVICE, 2020–2024 (USD MILLION)
TABLE 376
CHINA: GENERATIVE AI CYBERSECURITY MARKET, BY SERVICE, 2025–2031 (USD MILLION)
TABLE 377
CHINA: GENERATIVE AI CYBERSECURITY MARKET, BY PROFESSIONAL SERVICE, 2020–2024 (USD MILLION)
TABLE 378
CHINA: GENERATIVE AI CYBERSECURITY MARKET, BY PROFESSIONAL SERVICE, 2025–2031 (USD MILLION)
TABLE 379
CHINA: GENERATIVE AI-BASED CYBERSECURITY SOFTWARE MARKET, BY TYPE, 2020–2024 (USD MILLION)
TABLE 380
CHINA: GENERATIVE AI-BASED CYBERSECURITY SOFTWARE MARKET, BY TYPE, 2025–2031 (USD MILLION)
TABLE 381
CHINA: CYBERSECURITY SOFTWARE MARKET FOR GENERATIVE AI, BY TYPE, 2020–2024 (USD MILLION)
TABLE 382
CHINA: CYBERSECURITY SOFTWARE MARKET FOR GENERATIVE AI, BY TYPE, 2025–2031 (USD MILLION)
TABLE 383
CHINA: GENERATIVE AI CYBERSECURITY MARKET, BY SECURITY TYPE, 2020–2024 (USD MILLION)
TABLE 384
CHINA: GENERATIVE AI CYBERSECURITY MARKET, BY SECURITY TYPE, 2025–2031 (USD MILLION)
TABLE 385
CHINA: GENERATIVE AI CYBERSECURITY MARKET, BY END USER, 2020–2024 (USD MILLION)
TABLE 386
CHINA: GENERATIVE AI CYBERSECURITY MARKET, BY END USER, 2025–2031 (USD MILLION)
TABLE 387
CHINA: GENERATIVE AI-BASED CYBERSECURITY END USERS, BY VERTICAL, 2020–2024 (USD MILLION)
TABLE 388
CHINA: GENERATIVE AI-BASED CYBERSECURITY END USERS, BY VERTICAL, 2025–2031 (USD MILLION)
TABLE 389
CHINA: CYBERSECURITY SOFTWARE MARKET FOR GENERATIVE AI, BY END USER, 2020–2024 (USD MILLION)
TABLE 390
CHINA: CYBERSECURITY SOFTWARE MARKET FOR GENERATIVE AI, BY END USER, 2025–2031 (USD MILLION)
TABLE 391
INDIA: GENERATIVE AI CYBERSECURITY MARKET, BY OFFERING, 2020–2024 (USD MILLION)
TABLE 392
INDIA: GENERATIVE AI CYBERSECURITY MARKET, BY OFFERING, 2025–2031 (USD MILLION)
TABLE 393
INDIA: GENERATIVE AI CYBERSECURITY MARKET, BY SOFTWARE TYPE, 2020–2024 (USD MILLION)
TABLE 394
INDIA: GENERATIVE AI CYBERSECURITY MARKET, BY SOFTWARE TYPE, 2025–2031 (USD MILLION)
TABLE 395
INDIA: GENERATIVE AI CYBERSECURITY MARKET, BY SOFTWARE DEPLOYMENT MODE, 2020–2024 (USD MILLION)
TABLE 396
INDIA: GENERATIVE AI CYBERSECURITY MARKET, BY SOFTWARE DEPLOYMENT MODE, 2025–2031 (USD MILLION)
TABLE 397
INDIA: GENERATIVE AI CYBERSECURITY MARKET, BY SERVICE, 2020–2024 (USD MILLION)
TABLE 398
INDIA: GENERATIVE AI CYBERSECURITY MARKET, BY SERVICE, 2025–2031 (USD MILLION)
TABLE 399
INDIA: GENERATIVE AI CYBERSECURITY MARKET, BY PROFESSIONAL SERVICE, 2020–2024 (USD MILLION)
TABLE 400
INDIA: GENERATIVE AI CYBERSECURITY MARKET, BY PROFESSIONAL SERVICE, 2025–2031 (USD MILLION)
TABLE 401
INDIA: GENERATIVE AI-BASED CYBERSECURITY SOFTWARE MARKET, BY TYPE, 2020–2024 (USD MILLION)
TABLE 402
INDIA: GENERATIVE AI-BASED CYBERSECURITY SOFTWARE MARKET, BY TYPE, 2025–2031 (USD MILLION)
TABLE 403
INDIA: CYBERSECURITY SOFTWARE MARKET FOR GENERATIVE AI, BY TYPE, 2020–2024 (USD MILLION)
TABLE 404
INDIA: CYBERSECURITY SOFTWARE MARKET FOR GENERATIVE AI, BY TYPE, 2025–2031 (USD MILLION)
TABLE 405
INDIA: GENERATIVE AI CYBERSECURITY MARKET, BY SECURITY TYPE, 2020–2024 (USD MILLION)
TABLE 406
INDIA: GENERATIVE AI CYBERSECURITY MARKET, BY SECURITY TYPE, 2025–2031 (USD MILLION)
TABLE 407
INDIA: GENERATIVE AI CYBERSECURITY MARKET, BY END USER, 2020–2024 (USD MILLION)
TABLE 408
INDIA: GENERATIVE AI CYBERSECURITY MARKET, BY END USER, 2025–2031 (USD MILLION)
TABLE 409
INDIA: GENERATIVE AI-BASED CYBERSECURITY END USERS, BY VERTICAL, 2020–2024 (USD MILLION)
TABLE 410
INDIA: GENERATIVE AI-BASED CYBERSECURITY END USERS, BY VERTICAL, 2025–2031 (USD MILLION)
TABLE 411
INDIA: CYBERSECURITY SOFTWARE MARKET FOR GENERATIVE AI, BY END USER, 2020–2024 (USD MILLION)
TABLE 412
INDIA: CYBERSECURITY SOFTWARE MARKET FOR GENERATIVE AI, BY END USER, 2025–2031 (USD MILLION)
TABLE 413
JAPAN: GENERATIVE AI CYBERSECURITY MARKET, BY OFFERING, 2020–2024 (USD MILLION)
TABLE 414
JAPAN: GENERATIVE AI CYBERSECURITY MARKET, BY OFFERING, 2025–2031 (USD MILLION)
TABLE 415
JAPAN: GENERATIVE AI CYBERSECURITY MARKET, BY SOFTWARE TYPE, 2020–2024 (USD MILLION)
TABLE 416
JAPAN: GENERATIVE AI CYBERSECURITY MARKET, BY SOFTWARE TYPE, 2025–2031 (USD MILLION)
TABLE 417
JAPAN: GENERATIVE AI CYBERSECURITY MARKET, BY SOFTWARE DEPLOYMENT MODE, 2020–2024 (USD MILLION)
TABLE 418
JAPAN: GENERATIVE AI CYBERSECURITY MARKET, BY SOFTWARE DEPLOYMENT MODE, 2025–2031 (USD MILLION)
TABLE 419
JAPAN: GENERATIVE AI CYBERSECURITY MARKET, BY SERVICE, 2020–2024 (USD MILLION)
TABLE 420
JAPAN: GENERATIVE AI CYBERSECURITY MARKET, BY SERVICE, 2025–2031 (USD MILLION)
TABLE 421
JAPAN: GENERATIVE AI CYBERSECURITY MARKET, BY PROFESSIONAL SERVICE, 2020–2024 (USD MILLION)
TABLE 422
JAPAN: GENERATIVE AI CYBERSECURITY MARKET, BY PROFESSIONAL SERVICE, 2025–2031 (USD MILLION)
TABLE 423
JAPAN: GENERATIVE AI-BASED CYBERSECURITY SOFTWARE MARKET, BY TYPE, 2020–2024 (USD MILLION)
TABLE 424
JAPAN: GENERATIVE AI-BASED CYBERSECURITY SOFTWARE MARKET, BY TYPE, 2025–2031 (USD MILLION)
TABLE 425
JAPAN: CYBERSECURITY SOFTWARE MARKET FOR GENERATIVE AI, BY TYPE, 2020–2024 (USD MILLION)
TABLE 426
JAPAN: CYBERSECURITY SOFTWARE MARKET FOR GENERATIVE AI, BY TYPE, 2025–2031 (USD MILLION)
TABLE 427
JAPAN: GENERATIVE AI CYBERSECURITY MARKET, BY SECURITY TYPE, 2020–2024 (USD MILLION)
TABLE 428
JAPAN: GENERATIVE AI CYBERSECURITY MARKET, BY SECURITY TYPE, 2025–2031 (USD MILLION)
TABLE 429
JAPAN: GENERATIVE AI CYBERSECURITY MARKET, BY END USER, 2020–2024 (USD MILLION)
TABLE 430
JAPAN: GENERATIVE AI CYBERSECURITY MARKET, BY END USER, 2025–2031 (USD MILLION)
TABLE 431
JAPAN: GENERATIVE AI-BASED CYBERSECURITY END USERS, BY VERTICAL, 2020–2024 (USD MILLION)
TABLE 432
JAPAN: GENERATIVE AI-BASED CYBERSECURITY END USERS, BY VERTICAL, 2025–2031 (USD MILLION)
TABLE 433
JAPAN: CYBERSECURITY SOFTWARE MARKET FOR GENERATIVE AI, BY END USER, 2020–2024 (USD MILLION)
TABLE 434
JAPAN: CYBERSECURITY SOFTWARE MARKET FOR GENERATIVE AI, BY END USER, 2025–2031 (USD MILLION)
TABLE 435
REST OF ASIA PACIFIC: GENERATIVE AI CYBERSECURITY MARKET, BY OFFERING, 2020–2024 (USD MILLION)
TABLE 436
REST OF ASIA PACIFIC: GENERATIVE AI CYBERSECURITY MARKET, BY OFFERING, 2025–2031 (USD MILLION)
TABLE 437
REST OF ASIA PACIFIC: GENERATIVE AI CYBERSECURITY MARKET, BY SOFTWARE TYPE, 2020–2024 (USD MILLION)
TABLE 438
REST OF ASIA PACIFIC: GENERATIVE AI CYBERSECURITY MARKET, BY SOFTWARE TYPE, 2025–2031 (USD MILLION)
TABLE 439
REST OF ASIA PACIFIC: GENERATIVE AI CYBERSECURITY MARKET, BY SOFTWARE DEPLOYMENT MODE, 2020–2024 (USD MILLION)
TABLE 440
REST OF ASIA PACIFIC: GENERATIVE AI CYBERSECURITY MARKET, BY SOFTWARE DEPLOYMENT MODE, 2025–2031 (USD MILLION)
TABLE 441
REST OF ASIA PACIFIC: GENERATIVE AI CYBERSECURITY MARKET, BY SERVICE, 2020–2024 (USD MILLION)
TABLE 442
REST OF ASIA PACIFIC: GENERATIVE AI CYBERSECURITY MARKET, BY SERVICE, 2025–2031 (USD MILLION)
TABLE 443
REST OF ASIA PACIFIC: GENERATIVE AI CYBERSECURITY MARKET, BY PROFESSIONAL SERVICE, 2020–2024 (USD MILLION)
TABLE 444
REST OF ASIA PACIFIC: GENERATIVE AI CYBERSECURITY MARKET, BY PROFESSIONAL SERVICE, 2025–2031 (USD MILLION)
TABLE 445
REST OF ASIA PACIFIC: GENERATIVE AI-BASED CYBERSECURITY SOFTWARE MARKET, BY TYPE, 2020–2024 (USD MILLION)
TABLE 446
REST OF ASIA PACIFIC: GENERATIVE AI-BASED CYBERSECURITY SOFTWARE MARKET, BY TYPE, 2025–2031 (USD MILLION)
TABLE 447
REST OF ASIA PACIFIC: CYBERSECURITY SOFTWARE MARKET FOR GENERATIVE AI, BY TYPE, 2020–2024 (USD MILLION)
TABLE 448
REST OF ASIA PACIFIC: CYBERSECURITY SOFTWARE MARKET FOR GENERATIVE AI, BY TYPE, 2025–2031 (USD MILLION)
TABLE 449
REST OF ASIA PACIFIC: GENERATIVE AI CYBERSECURITY MARKET, BY SECURITY TYPE, 2020–2024 (USD MILLION)
TABLE 450
REST OF ASIA PACIFIC: GENERATIVE AI CYBERSECURITY MARKET, BY SECURITY TYPE, 2025–2031 (USD MILLION)
TABLE 451
REST OF ASIA PACIFIC: GENERATIVE AI CYBERSECURITY MARKET, BY END USER, 2020–2024 (USD MILLION)
TABLE 452
REST OF ASIA PACIFIC: GENERATIVE AI CYBERSECURITY MARKET, BY END USER, 2025–2031 (USD MILLION)
TABLE 453
REST OF ASIA PACIFIC: GENERATIVE AI-BASED CYBERSECURITY END USERS, BY VERTICAL, 2020–2024 (USD MILLION)
TABLE 454
REST OF ASIA PACIFIC: GENERATIVE AI-BASED CYBERSECURITY END USERS, BY VERTICAL, 2025–2031 (USD MILLION)
TABLE 455
REST OF ASIA PACIFIC: CYBERSECURITY SOFTWARE MARKET FOR GENERATIVE AI, BY END USER, 2020–2024 (USD MILLION)
TABLE 456
REST OF ASIA PACIFIC: CYBERSECURITY SOFTWARE MARKET FOR GENERATIVE AI, BY END USER, 2025–2031 (USD MILLION)
TABLE 457
MIDDLE EAST & AFRICA: GENERATIVE AI CYBERSECURITY MARKET, BY OFFERING, 2020–2024 (USD MILLION)
TABLE 458
MIDDLE EAST & AFRICA: GENERATIVE AI CYBERSECURITY MARKET, BY OFFERING, 2025–2031 (USD MILLION)
TABLE 459
MIDDLE EAST & AFRICA: GENERATIVE AI CYBERSECURITY MARKET, BY SOFTWARE TYPE, 2020–2024 (USD MILLION)
TABLE 460
MIDDLE EAST & AFRICA: GENERATIVE AI CYBERSECURITY MARKET, BY SOFTWARE TYPE, 2025–2031 (USD MILLION)
TABLE 461
MIDDLE EAST & AFRICA: GENERATIVE AI CYBERSECURITY MARKET, BY SOFTWARE DEPLOYMENT MODE, 2020–2024 (USD MILLION)
TABLE 462
MIDDLE EAST & AFRICA: GENERATIVE AI CYBERSECURITY MARKET, BY SOFTWARE DEPLOYMENT MODE, 2025–2031 (USD MILLION)
TABLE 463
MIDDLE EAST & AFRICA: GENERATIVE AI CYBERSECURITY MARKET, BY SERVICE, 2020–2024 (USD MILLION)
TABLE 464
MIDDLE EAST & AFRICA: GENERATIVE AI CYBERSECURITY MARKET, BY SERVICE, 2025–2031 (USD MILLION)
TABLE 465
MIDDLE EAST & AFRICA: GENERATIVE AI CYBERSECURITY MARKET, BY PROFESSIONAL SERVICE, 2020–2024 (USD MILLION)
TABLE 466
MIDDLE EAST & AFRICA: GENERATIVE AI CYBERSECURITY MARKET, BY PROFESSIONAL SERVICE, 2025–2031 (USD MILLION)
TABLE 467
MIDDLE EAST & AFRICA: GENERATIVE AI-BASED CYBERSECURITY SOFTWARE MARKET, BY TYPE, 2020–2024 (USD MILLION)
TABLE 468
MIDDLE EAST & AFRICA: GENERATIVE AI-BASED CYBERSECURITY SOFTWARE MARKET, BY TYPE, 2025–2031 (USD MILLION)
TABLE 469
MIDDLE EAST & AFRICA: CYBERSECURITY SOFTWARE MARKET FOR GENERATIVE AI, BY TYPE, 2020–2024 (USD MILLION)
TABLE 470
MIDDLE EAST & AFRICA: CYBERSECURITY SOFTWARE MARKET FOR GENERATIVE AI, BY TYPE, 2025–2031 (USD MILLION)
TABLE 471
MIDDLE EAST & AFRICA: GENERATIVE AI CYBERSECURITY MARKET, BY SECURITY TYPE, 2020–2024 (USD MILLION)
TABLE 472
MIDDLE EAST & AFRICA: GENERATIVE AI CYBERSECURITY MARKET, BY SECURITY TYPE, 2025–2031 (USD MILLION)
TABLE 473
MIDDLE EAST & AFRICA: GENERATIVE AI CYBERSECURITY MARKET, BY END USER, 2020–2024 (USD MILLION)
TABLE 474
MIDDLE EAST & AFRICA: GENERATIVE AI CYBERSECURITY MARKET, BY END USER, 2025–2031 (USD MILLION)
TABLE 475
MIDDLE EAST & AFRICA: GENERATIVE AI-BASED CYBERSECURITY END USERS, BY VERTICAL, 2020–2024 (USD MILLION)
TABLE 476
MIDDLE EAST & AFRICA: GENERATIVE AI-BASED CYBERSECURITY END USERS, BY VERTICAL, 2025–2031 (USD MILLION)
TABLE 477
MIDDLE EAST & AFRICA: CYBERSECURITY SOFTWARE MARKET FOR GENERATIVE AI, BY END USER, 2020–2024 (USD MILLION)
TABLE 478
MIDDLE EAST & AFRICA: CYBERSECURITY SOFTWARE MARKET FOR GENERATIVE AI, BY END USER, 2025–2031 (USD MILLION)
TABLE 479
MIDDLE EAST & AFRICA: GENERATIVE AI CYBERSECURITY MARKET, BY COUNTRY, 2020–2024 (USD MILLION)
TABLE 480
MIDDLE EAST & AFRICA: GENERATIVE AI CYBERSECURITY MARKET, BY COUNTRY, 2025–2031 (USD MILLION)
TABLE 481
SAUDI ARABIA: GENERATIVE AI CYBERSECURITY MARKET, BY OFFERING, 2020–2024 (USD MILLION)
TABLE 482
SAUDI ARABIA: GENERATIVE AI CYBERSECURITY MARKET, BY OFFERING, 2025–2031 (USD MILLION)
TABLE 483
SAUDI ARABIA: GENERATIVE AI CYBERSECURITY MARKET, BY SOFTWARE TYPE, 2020–2024 (USD MILLION)
TABLE 484
SAUDI ARABIA: GENERATIVE AI CYBERSECURITY MARKET, BY SOFTWARE TYPE, 2025–2031 (USD MILLION)
TABLE 485
SAUDI ARABIA: GENERATIVE AI CYBERSECURITY MARKET, BY SOFTWARE DEPLOYMENT MODE, 2020–2024 (USD MILLION)
TABLE 486
SAUDI ARABIA: GENERATIVE AI CYBERSECURITY MARKET, BY SOFTWARE DEPLOYMENT MODE, 2025–2031 (USD MILLION)
TABLE 487
SAUDI ARABIA: GENERATIVE AI CYBERSECURITY MARKET, BY SERVICE, 2020–2024 (USD MILLION)
TABLE 488
SAUDI ARABIA: GENERATIVE AI CYBERSECURITY MARKET, BY SERVICE, 2025–2031 (USD MILLION)
TABLE 489
SAUDI ARABIA: GENERATIVE AI CYBERSECURITY MARKET, BY PROFESSIONAL SERVICE, 2020–2024 (USD MILLION)
TABLE 490
SAUDI ARABIA: GENERATIVE AI CYBERSECURITY MARKET, BY PROFESSIONAL SERVICE, 2025–2031 (USD MILLION)
TABLE 491
SAUDI ARABIA: GENERATIVE AI-BASED CYBERSECURITY SOFTWARE MARKET, BY TYPE, 2020–2024 (USD MILLION)
TABLE 492
SAUDI ARABIA: GENERATIVE AI-BASED CYBERSECURITY SOFTWARE MARKET, BY TYPE, 2025–2031 (USD MILLION)
TABLE 493
SAUDI ARABIA: CYBERSECURITY SOFTWARE MARKET FOR GENERATIVE AI, BY TYPE, 2020–2024 (USD MILLION)
TABLE 494
SAUDI ARABIA: CYBERSECURITY SOFTWARE MARKET FOR GENERATIVE AI, BY TYPE, 2025–2031 (USD MILLION)
TABLE 495
SAUDI ARABIA: GENERATIVE AI CYBERSECURITY MARKET, BY SECURITY TYPE, 2020–2024 (USD MILLION)
TABLE 496
SAUDI ARABIA: GENERATIVE AI CYBERSECURITY MARKET, BY SECURITY TYPE, 2025–2031 (USD MILLION)
TABLE 497
SAUDI ARABIA: GENERATIVE AI CYBERSECURITY MARKET, BY END USER, 2020–2024 (USD MILLION)
TABLE 498
SAUDI ARABIA: GENERATIVE AI CYBERSECURITY MARKET, BY END USER, 2025–2031 (USD MILLION)
TABLE 499
SAUDI ARABIA: GENERATIVE AI-BASED CYBERSECURITY END USERS, BY VERTICAL, 2020–2024 (USD MILLION)
TABLE 500
SAUDI ARABIA: GENERATIVE AI-BASED CYBERSECURITY END USERS, BY VERTICAL, 2025–2031 (USD MILLION)
TABLE 501
SAUDI ARABIA: CYBERSECURITY SOFTWARE MARKET FOR GENERATIVE AI, BY END USER, 2020–2024 (USD MILLION)
TABLE 502
SAUDI ARABIA: CYBERSECURITY SOFTWARE MARKET FOR GENERATIVE AI, BY END USER, 2025–2031 (USD MILLION)
TABLE 503
UAE: GENERATIVE AI CYBERSECURITY MARKET, BY OFFERING, 2020–2024 (USD MILLION)
TABLE 504
UAE: GENERATIVE AI CYBERSECURITY MARKET, BY OFFERING, 2025–2031 (USD MILLION)
TABLE 505
UAE: GENERATIVE AI CYBERSECURITY MARKET, BY SOFTWARE TYPE, 2020–2024 (USD MILLION)
TABLE 506
UAE: GENERATIVE AI CYBERSECURITY MARKET, BY SOFTWARE TYPE, 2025–2031 (USD MILLION)
TABLE 507
UAE: GENERATIVE AI CYBERSECURITY MARKET, BY SOFTWARE DEPLOYMENT MODE, 2020–2024 (USD MILLION)
TABLE 508
UAE: GENERATIVE AI CYBERSECURITY MARKET, BY SOFTWARE DEPLOYMENT MODE, 2025–2031 (USD MILLION)
TABLE 509
UAE: GENERATIVE AI CYBERSECURITY MARKET, BY SERVICE, 2020–2024 (USD MILLION)
TABLE 510
UAE: GENERATIVE AI CYBERSECURITY MARKET, BY SERVICE, 2025–2031 (USD MILLION)
TABLE 511
UAE: GENERATIVE AI CYBERSECURITY MARKET, BY PROFESSIONAL SERVICE, 2020–2024 (USD MILLION)
TABLE 512
UAE: GENERATIVE AI CYBERSECURITY MARKET, BY PROFESSIONAL SERVICE, 2025–2031 (USD MILLION)
TABLE 513
UAE: GENERATIVE AI-BASED CYBERSECURITY SOFTWARE MARKET, BY TYPE, 2020–2024 (USD MILLION)
TABLE 514
UAE: GENERATIVE AI-BASED CYBERSECURITY SOFTWARE MARKET, BY TYPE, 2025–2031 (USD MILLION)
TABLE 515
UAE: CYBERSECURITY SOFTWARE MARKET FOR GENERATIVE AI, BY TYPE, 2020–2024 (USD MILLION)
TABLE 516
UAE: CYBERSECURITY SOFTWARE MARKET FOR GENERATIVE AI, BY TYPE, 2025–2031 (USD MILLION)
TABLE 517
UAE: GENERATIVE AI CYBERSECURITY MARKET, BY SECURITY TYPE, 2020–2024 (USD MILLION)
TABLE 518
UAE: GENERATIVE AI CYBERSECURITY MARKET, BY SECURITY TYPE, 2025–2031 (USD MILLION)
TABLE 519
UAE: GENERATIVE AI CYBERSECURITY MARKET, BY END USER, 2020–2024 (USD MILLION)
TABLE 520
UAE: GENERATIVE AI CYBERSECURITY MARKET, BY END USER, 2025–2031 (USD MILLION)
TABLE 521
UAE: GENERATIVE AI-BASED CYBERSECURITY END USERS, BY VERTICAL, 2020–2024 (USD MILLION)
TABLE 522
UAE: GENERATIVE AI-BASED CYBERSECURITY END USERS, BY VERTICAL, 2025–2031 (USD MILLION)
TABLE 523
UAE: CYBERSECURITY SOFTWARE MARKET FOR GENERATIVE AI, BY END USER, 2020–2024 (USD MILLION)
TABLE 524
UAE: CYBERSECURITY SOFTWARE MARKET FOR GENERATIVE AI, BY END USER, 2025–2031 (USD MILLION)
TABLE 525
REST OF MIDDLE EAST: GENERATIVE AI CYBERSECURITY MARKET, BY OFFERING, 2020–2024 (USD MILLION)
TABLE 526
REST OF MIDDLE EAST: GENERATIVE AI CYBERSECURITY MARKET, BY OFFERING, 2025–2031 (USD MILLION)
TABLE 527
REST OF MIDDLE EAST: GENERATIVE AI CYBERSECURITY MARKET, BY SOFTWARE TYPE, 2020–2024 (USD MILLION)
TABLE 528
REST OF MIDDLE EAST: GENERATIVE AI CYBERSECURITY MARKET, BY SOFTWARE TYPE, 2025–2031 (USD MILLION)
TABLE 529
REST OF MIDDLE EAST: GENERATIVE AI CYBERSECURITY MARKET, BY SOFTWARE DEPLOYMENT MODE, 2020–2024 (USD MILLION)
TABLE 530
REST OF MIDDLE EAST: GENERATIVE AI CYBERSECURITY MARKET, BY SOFTWARE DEPLOYMENT MODE, 2025–2031 (USD MILLION)
TABLE 531
REST OF MIDDLE EAST: GENERATIVE AI CYBERSECURITY MARKET, BY SERVICE, 2020–2024 (USD MILLION)
TABLE 532
REST OF MIDDLE EAST: GENERATIVE AI CYBERSECURITY MARKET, BY SERVICE, 2025–2031 (USD MILLION)
TABLE 533
REST OF MIDDLE EAST: GENERATIVE AI CYBERSECURITY MARKET, BY PROFESSIONAL SERVICE, 2020–2024 (USD MILLION)
TABLE 534
REST OF MIDDLE EAST: GENERATIVE AI CYBERSECURITY MARKET, BY PROFESSIONAL SERVICE, 2025–2031 (USD MILLION)
TABLE 535
REST OF MIDDLE EAST: GENERATIVE AI-BASED CYBERSECURITY SOFTWARE MARKET, BY TYPE, 2020–2024 (USD MILLION)
TABLE 536
REST OF MIDDLE EAST: GENERATIVE AI-BASED CYBERSECURITY SOFTWARE MARKET, BY TYPE, 2025–2031 (USD MILLION)
TABLE 537
REST OF MIDDLE EAST: CYBERSECURITY SOFTWARE MARKET FOR GENERATIVE AI, BY TYPE, 2020–2024 (USD MILLION)
TABLE 538
REST OF MIDDLE EAST: CYBERSECURITY SOFTWARE MARKET FOR GENERATIVE AI, BY TYPE, 2025–2031 (USD MILLION)
TABLE 539
REST OF MIDDLE EAST: GENERATIVE AI CYBERSECURITY MARKET, BY SECURITY TYPE, 2020–2024 (USD MILLION)
TABLE 540
REST OF MIDDLE EAST: GENERATIVE AI CYBERSECURITY MARKET, BY SECURITY TYPE, 2025–2031 (USD MILLION)
TABLE 541
REST OF MIDDLE EAST: GENERATIVE AI CYBERSECURITY MARKET, BY END USER, 2020–2024 (USD MILLION)
TABLE 542
REST OF MIDDLE EAST: GENERATIVE AI CYBERSECURITY MARKET, BY END USER, 2025–2031 (USD MILLION)
TABLE 543
REST OF MIDDLE EAST: GENERATIVE AI-BASED CYBERSECURITY END USERS, BY VERTICAL, 2020–2024 (USD MILLION)
TABLE 544
REST OF MIDDLE EAST: GENERATIVE AI-BASED CYBERSECURITY END USERS, BY VERTICAL, 2025–2031 (USD MILLION)
TABLE 545
REST OF MIDDLE EAST: CYBERSECURITY SOFTWARE MARKET FOR GENERATIVE AI, BY END USER, 2020–2024 (USD MILLION)
TABLE 546
REST OF MIDDLE EAST: CYBERSECURITY SOFTWARE MARKET FOR GENERATIVE AI, BY END USER, 2025–2031 (USD MILLION)
TABLE 547
AFRICA: GENERATIVE AI CYBERSECURITY MARKET, BY OFFERING, 2020–2024 (USD MILLION)
TABLE 548
AFRICA: GENERATIVE AI CYBERSECURITY MARKET, BY OFFERING, 2025–2031 (USD MILLION)
TABLE 549
AFRICA: GENERATIVE AI CYBERSECURITY MARKET, BY SOFTWARE TYPE, 2020–2024 (USD MILLION)
TABLE 550
AFRICA: GENERATIVE AI CYBERSECURITY MARKET, BY SOFTWARE TYPE, 2025–2031 (USD MILLION)
TABLE 551
AFRICA: GENERATIVE AI CYBERSECURITY MARKET, BY SOFTWARE DEPLOYMENT MODE, 2020–2024 (USD MILLION)
TABLE 552
AFRICA: GENERATIVE AI CYBERSECURITY MARKET, BY SOFTWARE DEPLOYMENT MODE, 2025–2031 (USD MILLION)
TABLE 553
AFRICA: GENERATIVE AI CYBERSECURITY MARKET, BY SERVICE, 2020–2024 (USD MILLION)
TABLE 554
AFRICA: GENERATIVE AI CYBERSECURITY MARKET, BY SERVICE, 2025–2031 (USD MILLION)
TABLE 555
AFRICA: GENERATIVE AI CYBERSECURITY MARKET, BY PROFESSIONAL SERVICE, 2020–2024 (USD MILLION)
TABLE 556
AFRICA: GENERATIVE AI CYBERSECURITY MARKET, BY PROFESSIONAL SERVICE, 2025–2031 (USD MILLION)
TABLE 557
AFRICA: GENERATIVE AI-BASED CYBERSECURITY SOFTWARE MARKET, BY TYPE, 2020–2024 (USD MILLION)
TABLE 558
AFRICA: GENERATIVE AI-BASED CYBERSECURITY SOFTWARE MARKET, BY TYPE, 2025–2031 (USD MILLION)
TABLE 559
AFRICA: CYBERSECURITY SOFTWARE MARKET FOR GENERATIVE AI, BY TYPE, 2020–2024 (USD MILLION)
TABLE 560
AFRICA: CYBERSECURITY SOFTWARE MARKET FOR GENERATIVE AI, BY TYPE, 2025–2031 (USD MILLION)
TABLE 561
AFRICA: GENERATIVE AI CYBERSECURITY MARKET, BY SECURITY TYPE, 2020–2024 (USD MILLION)
TABLE 562
AFRICA: GENERATIVE AI CYBERSECURITY MARKET, BY SECURITY TYPE, 2025–2031 (USD MILLION)
TABLE 563
AFRICA: GENERATIVE AI CYBERSECURITY MARKET, BY END USER, 2020–2024 (USD MILLION)
TABLE 564
AFRICA: GENERATIVE AI CYBERSECURITY MARKET, BY END USER, 2025–2031 (USD MILLION)
TABLE 565
AFRICA: GENERATIVE AI-BASED CYBERSECURITY END USERS, BY VERTICAL, 2020–2024 (USD MILLION)
TABLE 566
AFRICA: GENERATIVE AI-BASED CYBERSECURITY END USERS, BY VERTICAL, 2025–2031 (USD MILLION)
TABLE 567
AFRICA: CYBERSECURITY SOFTWARE MARKET FOR GENERATIVE AI, BY END USER, 2020–2024 (USD MILLION)
TABLE 568
AFRICA: CYBERSECURITY SOFTWARE MARKET FOR GENERATIVE AI, BY END USER, 2025–2031 (USD MILLION)
TABLE 569
LATIN AMERICA: GENERATIVE AI CYBERSECURITY MARKET, BY OFFERING, 2020–2024 (USD MILLION)
TABLE 570
LATIN AMERICA: GENERATIVE AI CYBERSECURITY MARKET, BY OFFERING, 2025–2031 (USD MILLION)
TABLE 571
LATIN AMERICA: GENERATIVE AI CYBERSECURITY MARKET, BY SOFTWARE TYPE, 2020–2024 (USD MILLION)
TABLE 572
LATIN AMERICA: GENERATIVE AI CYBERSECURITY MARKET, BY SOFTWARE TYPE, 2025–2031 (USD MILLION)
TABLE 573
LATIN AMERICA: GENERATIVE AI CYBERSECURITY MARKET, BY SOFTWARE DEPLOYMENT MODE, 2020–2024 (USD MILLION)
TABLE 574
LATIN AMERICA: GENERATIVE AI CYBERSECURITY MARKET, BY SOFTWARE DEPLOYMENT MODE, 2025–2031 (USD MILLION)
TABLE 575
LATIN AMERICA: GENERATIVE AI CYBERSECURITY MARKET, BY SERVICE, 2020–2024 (USD MILLION)
TABLE 576
LATIN AMERICA: GENERATIVE AI CYBERSECURITY MARKET, BY SERVICE, 2025–2031 (USD MILLION)
TABLE 577
LATIN AMERICA: GENERATIVE AI CYBERSECURITY MARKET, BY PROFESSIONAL SERVICE, 2020–2024 (USD MILLION)
TABLE 578
LATIN AMERICA: GENERATIVE AI CYBERSECURITY MARKET, BY PROFESSIONAL SERVICE, 2025–2031 (USD MILLION)
TABLE 579
LATIN AMERICA: GENERATIVE AI-BASED CYBERSECURITY SOFTWARE MARKET, BY TYPE, 2020–2024 (USD MILLION)
TABLE 580
ATIN AMERICA: GENERATIVE AI-BASED CYBERSECURITY SOFTWARE MARKET, BY TYPE, 2025–2031 (USD MILLION)
TABLE 581
LATIN AMERICA: CYBERSECURITY SOFTWARE MARKET FOR GENERATIVE AI, BY TYPE, 2020–2024 (USD MILLION)
TABLE 582
LATIN AMERICA: CYBERSECURITY SOFTWARE MARKET FOR GENERATIVE AI, BY TYPE, 2025–2031 (USD MILLION)
TABLE 583
LATIN AMERICA: GENERATIVE AI CYBERSECURITY MARKET, BY SECURITY TYPE, 2020–2024 (USD MILLION)
TABLE 584
LATIN AMERICA: GENERATIVE AI CYBERSECURITY MARKET, BY SECURITY TYPE, 2025–2031 (USD MILLION)
TABLE 585
LATIN AMERICA: GENERATIVE AI CYBERSECURITY MARKET, BY END USER, 2020–2024 (USD MILLION)
TABLE 586
LATIN AMERICA: GENERATIVE AI CYBERSECURITY MARKET, BY END USER, 2025–2031 (USD MILLION)
TABLE 587
LATIN AMERICA: GENERATIVE AI-BASED CYBERSECURITY END USERS, BY VERTICAL, 2020–2024 (USD MILLION)
TABLE 588
LATIN AMERICA: GENERATIVE AI-BASED CYBERSECURITY END USERS, BY VERTICAL, 2025–2031 (USD MILLION)
TABLE 589
LATIN AMERICA: CYBERSECURITY SOFTWARE MARKET FOR GENERATIVE AI, BY END USER, 2020–2024 (USD MILLION)
TABLE 590
LATIN AMERICA: CYBERSECURITY SOFTWARE MARKET FOR GENERATIVE AI, BY END USER, 2025–2031 (USD MILLION)
TABLE 591
LATIN AMERICA: GENERATIVE AI CYBERSECURITY MARKET, BY COUNTRY, 2020–2024 (USD MILLION)
TABLE 592
LATIN AMERICA: GENERATIVE AI CYBERSECURITY MARKET, BY COUNTRY, 2025–2031 (USD MILLION)
TABLE 593
BRAZIL: GENERATIVE AI CYBERSECURITY MARKET, BY OFFERING, 2020–2024 (USD MILLION)
TABLE 594
BRAZIL: GENERATIVE AI CYBERSECURITY MARKET, BY OFFERING, 2025–2031 (USD MILLION)
TABLE 595
BRAZIL: GENERATIVE AI CYBERSECURITY MARKET, BY SOFTWARE TYPE, 2020–2024 (USD MILLION)
TABLE 596
BRAZIL: GENERATIVE AI CYBERSECURITY MARKET, BY SOFTWARE TYPE, 2025–2031 (USD MILLION)
TABLE 597
BRAZIL: GENERATIVE AI CYBERSECURITY MARKET, BY SOFTWARE DEPLOYMENT MODE, 2020–2024 (USD MILLION)
TABLE 598
BRAZIL: GENERATIVE AI CYBERSECURITY MARKET, BY SOFTWARE DEPLOYMENT MODE, 2025–2031 (USD MILLION)
TABLE 599
BRAZIL: GENERATIVE AI CYBERSECURITY MARKET, BY SERVICE, 2020–2024 (USD MILLION)
TABLE 600
BRAZIL: GENERATIVE AI CYBERSECURITY MARKET, BY SERVICE, 2025–2031 (USD MILLION)
TABLE 601
BRAZIL: GENERATIVE AI CYBERSECURITY MARKET, BY PROFESSIONAL SERVICE, 2020–2024 (USD MILLION)
TABLE 602
BRAZIL: GENERATIVE AI CYBERSECURITY MARKET, BY PROFESSIONAL SERVICE, 2025–2031 (USD MILLION)
TABLE 603
BRAZIL: GENERATIVE AI-BASED CYBERSECURITY SOFTWARE MARKET, BY TYPE, 2020–2024 (USD MILLION)
TABLE 604
BRAZIL: GENERATIVE AI-BASED CYBERSECURITY SOFTWARE MARKET, BY TYPE, 2025–2031 (USD MILLION)
TABLE 605
BRAZIL: CYBERSECURITY SOFTWARE MARKET FOR GENERATIVE AI, BY TYPE, 2020–2024 (USD MILLION)
TABLE 606
BRAZIL: CYBERSECURITY SOFTWARE MARKET FOR GENERATIVE AI, BY TYPE, 2025–2031 (USD MILLION)
TABLE 607
BRAZIL: GENERATIVE AI CYBERSECURITY MARKET, BY SECURITY TYPE, 2020–2024 (USD MILLION)
TABLE 608
BRAZIL: GENERATIVE AI CYBERSECURITY MARKET, BY SECURITY TYPE, 2025–2031 (USD MILLION)
TABLE 609
BRAZIL: GENERATIVE AI CYBERSECURITY MARKET, BY END USER, 2020–2024 (USD MILLION)
TABLE 610
BRAZIL: GENERATIVE AI CYBERSECURITY MARKET, BY END USER, 2025–2031 (USD MILLION)
TABLE 611
BRAZIL: GENERATIVE AI-BASED CYBERSECURITY END USERS, BY VERTICAL, 2020–2024 (USD MILLION)
TABLE 612
BRAZIL: GENERATIVE AI-BASED CYBERSECURITY END USERS, BY VERTICAL, 2025–2031 (USD MILLION)
TABLE 613
BRAZIL: CYBERSECURITY SOFTWARE MARKET FOR GENERATIVE AI, BY END USER, 2020–2024 (USD MILLION)
TABLE 614
BRAZIL: CYBERSECURITY SOFTWARE MARKET FOR GENERATIVE AI, BY END USER, 2025–2031 (USD MILLION)
TABLE 615
MEXICO: GENERATIVE AI CYBERSECURITY MARKET, BY OFFERING, 2020–2024 (USD MILLION)
TABLE 616
MEXICO: GENERATIVE AI CYBERSECURITY MARKET, BY OFFERING, 2025–2031 (USD MILLION)
TABLE 617
MEXICO: GENERATIVE AI CYBERSECURITY MARKET, BY SOFTWARE TYPE, 2020–2024 (USD MILLION)
TABLE 618
MEXICO: GENERATIVE AI CYBERSECURITY MARKET, BY SOFTWARE TYPE, 2025–2031 (USD MILLION)
TABLE 619
MEXICO: GENERATIVE AI CYBERSECURITY MARKET, BY SOFTWARE DEPLOYMENT MODE, 2020–2024 (USD MILLION)
TABLE 620
MEXICO: GENERATIVE AI CYBERSECURITY MARKET, BY SOFTWARE DEPLOYMENT MODE, 2025–2031 (USD MILLION)
TABLE 621
MEXICO: GENERATIVE AI CYBERSECURITY MARKET, BY SERVICE, 2020–2024 (USD MILLION)
TABLE 622
MEXICO: GENERATIVE AI CYBERSECURITY MARKET, BY SERVICE, 2025–2031 (USD MILLION)
TABLE 623
MEXICO: GENERATIVE AI CYBERSECURITY MARKET, BY PROFESSIONAL SERVICE, 2020–2024 (USD MILLION)
TABLE 624
MEXICO: GENERATIVE AI CYBERSECURITY MARKET, BY PROFESSIONAL SERVICE, 2025–2031 (USD MILLION)
TABLE 625
MEXICO: GENERATIVE AI-BASED CYBERSECURITY SOFTWARE MARKET, BY TYPE, 2020–2024 (USD MILLION)
TABLE 626
MEXICO: GENERATIVE AI-BASED CYBERSECURITY SOFTWARE MARKET, BY TYPE, 2025–2031 (USD MILLION)
TABLE 627
MEXICO: CYBERSECURITY SOFTWARE MARKET FOR GENERATIVE AI, BY TYPE, 2020–2024 (USD MILLION)
TABLE 628
MEXICO: CYBERSECURITY SOFTWARE MARKET FOR GENERATIVE AI, BY TYPE, 2025–2031 (USD MILLION)
TABLE 629
MEXICO: GENERATIVE AI CYBERSECURITY MARKET, BY SECURITY TYPE, 2020–2024 (USD MILLION)
TABLE 630
MEXICO: GENERATIVE AI CYBERSECURITY MARKET, BY SECURITY TYPE, 2025–2031 (USD MILLION)
TABLE 631
MEXICO: GENERATIVE AI CYBERSECURITY MARKET, BY END USER, 2020–2024 (USD MILLION)
TABLE 632
MEXICO: GENERATIVE AI CYBERSECURITY MARKET, BY END USER, 2025–2031 (USD MILLION)
TABLE 633
MEXICO: GENERATIVE AI-BASED CYBERSECURITY END USERS, BY VERTICAL, 2020–2024 (USD MILLION)
TABLE 634
MEXICO: GENERATIVE AI-BASED CYBERSECURITY END USERS, BY VERTICAL, 2025–2031 (USD MILLION)
TABLE 635
MEXICO: CYBERSECURITY SOFTWARE MARKET FOR GENERATIVE AI, BY END USER, 2020–2024 (USD MILLION)
TABLE 636
MEXICO: CYBERSECURITY SOFTWARE MARKET FOR GENERATIVE AI, BY END USER, 2025–2031 (USD MILLION)
TABLE 637
REST OF LATIN AMERICA: GENERATIVE AI CYBERSECURITY MARKET, BY OFFERING, 2020–2024 (USD MILLION)
TABLE 638
REST OF LATIN AMERICA: GENERATIVE AI CYBERSECURITY MARKET, BY OFFERING, 2025–2031 (USD MILLION)
TABLE 639
REST OF LATIN AMERICA: GENERATIVE AI CYBERSECURITY MARKET, BY SOFTWARE TYPE, 2020–2024 (USD MILLION)
TABLE 640
REST OF LATIN AMERICA: GENERATIVE AI CYBERSECURITY MARKET, BY SOFTWARE TYPE, 2025–2031 (USD MILLION)
TABLE 641
REST OF LATIN AMERICA: GENERATIVE AI CYBERSECURITY MARKET, BY SOFTWARE DEPLOYMENT MODE, 2020–2024 (USD MILLION)
TABLE 642
REST OF LATIN AMERICA: GENERATIVE AI CYBERSECURITY MARKET, BY SOFTWARE DEPLOYMENT MODE, 2025–2031 (USD MILLION)
TABLE 643
REST OF LATIN AMERICA: GENERATIVE AI CYBERSECURITY MARKET, BY SERVICE, 2020–2024 (USD MILLION)
TABLE 644
REST OF LATIN AMERICA: GENERATIVE AI CYBERSECURITY MARKET, BY SERVICE, 2025–2031 (USD MILLION)
TABLE 645
REST OF LATIN AMERICA: GENERATIVE AI CYBERSECURITY MARKET, BY PROFESSIONAL SERVICE, 2020–2024 (USD MILLION)
TABLE 646
REST OF LATIN AMERICA: GENERATIVE AI CYBERSECURITY MARKET, BY PROFESSIONAL SERVICE, 2025–2031 (USD MILLION)
TABLE 647
REST OF LATIN AMERICA: GENERATIVE AI-BASED CYBERSECURITY SOFTWARE MARKET, BY TYPE, 2020–2024 (USD MILLION)
TABLE 648
REST OF LATIN AMERICA: GENERATIVE AI-BASED CYBERSECURITY SOFTWARE MARKET, BY TYPE, 2025–2031 (USD MILLION)
TABLE 649
REST OF LATIN AMERICA: CYBERSECURITY SOFTWARE MARKET FOR GENERATIVE AI, BY TYPE, 2020–2024 (USD MILLION)
TABLE 650
REST OF LATIN AMERICA: CYBERSECURITY SOFTWARE MARKET FOR GENERATIVE AI, BY TYPE, 2025–2031 (USD MILLION)
TABLE 651
REST OF LATIN AMERICA: GENERATIVE AI CYBERSECURITY MARKET, BY SECURITY TYPE, 2020–2024 (USD MILLION)
TABLE 652
REST OF LATIN AMERICA: GENERATIVE AI CYBERSECURITY MARKET, BY SECURITY TYPE, 2025–2031 (USD MILLION)
TABLE 653
REST OF LATIN AMERICA: GENERATIVE AI CYBERSECURITY MARKET, BY END USER, 2020–2024 (USD MILLION)
TABLE 654
REST OF LATIN AMERICA: GENERATIVE AI CYBERSECURITY MARKET, BY END USER, 2025–2031 (USD MILLION)
TABLE 655
REST OF LATIN AMERICA: GENERATIVE AI-BASED CYBERSECURITY END USERS, BY VERTICAL, 2020–2024 (USD MILLION)
TABLE 656
REST OF LATIN AMERICA: GENERATIVE AI-BASED CYBERSECURITY END USERS, BY VERTICAL, 2025–2031 (USD MILLION)
TABLE 657
REST OF LATIN AMERICA: CYBERSECURITY SOFTWARE MARKET FOR GENERATIVE AI, BY END USER, 2020–2024 (USD MILLION)
TABLE 658
REST OF LATIN AMERICA: CYBERSECURITY SOFTWARE MARKET FOR GENERATIVE AI, BY END USER, 2025–2031 (USD MILLION)
TABLE 659
OVERVIEW OF STRATEGIES ADOPTED BY KEY GENERATIVE AI CYBERSECURITY VENDORS
TABLE 660
GENERATIVE AI CYBERSECURITY MARKET: DEGREE OF COMPETITION
TABLE 661
REGION FOOTPRINT (25 COMPANIES)
TABLE 662
OFFERING FOOTPRINT (25 COMPANIES)
TABLE 663
SECURITY TYPE FOOTPRINT (25 COMPANIES)
TABLE 664
END USER FOOTPRINT (25 COMPANIES)
TABLE 665
REGIONAL FOOTPRINT (13 COMPANIES)
TABLE 666
OFFERING FOOTPRINT (13 COMPANIES)
TABLE 667
SECURITY TYPE FOOTPRINT (13 COMPANIES)
TABLE 668
END USER FOOTPRINT (13 COMPANIES)
TABLE 669
GENERATIVE AI-BASED CYBERSECURITY SOFTWARE: DETAILED LIST OF KEY STARTUPS/SMES
TABLE 670
GENERATIVE AI-BASED CYBERSECURITY SOFTWARE: COMPETITIVE BENCHMARKING OF KEY STARTUPS/SMES
TABLE 671
CYBERSECURITY SOFTWARE FOR GENERATIVE AI: DETAILED LIST OF KEY STARTUPS/SMES
TABLE 672
CYBERSECURITY SOFTWARE FOR GENERATIVE AI: COMPETITIVE BENCHMARKING OF KEY STARTUPS/SMES
TABLE 673
GENERATIVE AI CYBERSECURITY MARKET: PRODUCT LAUNCHES AND ENHANCEMENTS, JANUARY 2023–AUGUST 2025
TABLE 674
GENERATIVE AI CYBERSECURITY MARKET: DEALS, MAY 2023–JUNE 2024
TABLE 675
MICROSOFT: COMPANY OVERVIEW
TABLE 676
MICROSOFT: PRODUCTS/SOLUTIONS/SERVICES OFFERED
TABLE 677
MICROSOFT: PRODUCT LAUNCHES AND ENHANCEMENTS
TABLE 678
MICROSOFT: DEALS
TABLE 679
IBM: COMPANY OVERVIEW
TABLE 680
IBM: PRODUCTS/SOLUTIONS/SERVICES OFFERED
TABLE 681
IBM: PRODUCT LAUNCHES AND ENHANCEMENTS
TABLE 683
GOOGLE: COMPANY OVERVIEW
TABLE 684
GOOGLE: PRODUCTS/SOLUTIONS/SERVICES OFFERED
TABLE 685
GOOGLE: PRODUCT LAUNCHES AND ENHANCEMENTS
TABLE 687
SENTINELONE: COMPANY OVERVIEW
TABLE 688
SENTINELONE: PRODUCTS/SOLUTIONS/SERVICES OFFERED
TABLE 689
SENTINELONE: PRODUCT LAUNCHES AND ENHANCEMENTS
TABLE 690
SENTINELONE: DEALS
TABLE 691
NVIDIA: COMPANY OVERVIEW
TABLE 692
NVIDIA: PRODUCTS/SOLUTIONS/SERVICES OFFERED
TABLE 693
NVIDIA: PRODUCT LAUNCHES AND ENHANCEMENTS
TABLE 695
NEURALTRUST: COMPANY OVERVIEW
TABLE 696
NEURALTRUST: PRODUCTS/SOLUTIONS/SERVICES OFFERED
TABLE 697
AWS: COMPANY OVERVIEW
TABLE 698
AWS: PRODUCTS/SOLUTIONS/SERVICES OFFERED
TABLE 700
CISCO: COMPANY OVERVIEW
TABLE 701
CISCO: PRODUCTS/SOLUTIONS/SERVICES OFFERED
TABLE 702
CISCO: PRODUCT LAUNCHES AND ENHANCEMENTS
TABLE 704
CROWDSTRIKE: COMPANY OVERVIEW
TABLE 705
CROWDSTRIKE: PRODUCTS/SOLUTIONS/SERVICES OFFERED
TABLE 706
CROWDSTRIKE: PRODUCT LAUNCHES AND ENHANCEMENTS
TABLE 707
CROWDSTRIKE: DEALS
TABLE 708
FORTINET: COMPANY OVERVIEW
TABLE 709
FORTINET: PRODUCTS/PRODUCTS/SOLUTIONS/SERVICES OFFERED
TABLE 710
FORTINET: PRODUCT LAUNCHES AND ENHANCEMENTS
TABLE 711
FORTINET: DEALS
TABLE 712
ZSCALER: COMPANY OVERVIEW
TABLE 713
ZSCALER: PRODUCTS/SOLUTIONS/SERVICES OFFERED
TABLE 714
ZSCALER: PRODUCT LAUNCHES AND ENHANCEMENTS
TABLE 716
GENERATIVE AI MARKET, BY OFFERING, 2020–2024 (USD MILLION)
TABLE 717
GENERATIVE AI MARKET, BY OFFERING, 2025–2032 (USD MILLION)
TABLE 718
GENERATIVE AI MARKET, BY DATA MODALITY, 2020–2024 (USD MILLION)
TABLE 719
GENERATIVE AI MARKET, BY DATA MODALITY, 2025–2032 (USD MILLION)
TABLE 720
GENERATIVE AI MARKET, BY APPLICATION, 2020–2024 (USD MILLION)
TABLE 721
GENERATIVE AI MARKET, BY APPLICATION, 2025–2032 (USD MILLION)
TABLE 722
GENERATIVE AI MARKET, BY END USER, 2020–2024 (USD MILLION)
TABLE 723
GENERATIVE AI MARKET, BY END USER, 2025–2032 (USD MILLION)
TABLE 724
GENERATIVE AI MARKET, BY REGION, 2020–2024 (USD MILLION)
TABLE 725
GENERATIVE AI MARKET, BY REGION, 2025–2032 (USD MILLION)
TABLE 726
AI IN CYBERSECURITY MARKET, BY OFFERING, 2019–2022 (USD MILLION)
TABLE 727
AI IN CYBERSECURITY MARKET, BY OFFERING, 2023–2028 (USD MILLION)
TABLE 728
AI IN CYBERSECURITY MARKET, BY SECURITY TYPE, 2019–2022 (USD MILLION)
TABLE 729
AI IN CYBERSECURITY MARKET, BY SECURITY TYPE, 2023–2028 (USD MILLION)
TABLE 730
AI IN CYBERSECURITY MARKET, BY TECHNOLOGY, 2019–2022 (USD MILLION)
TABLE 731
AI IN CYBERSECURITY MARKET, BY TECHNOLOGY, 2023–2028 (USD MILLION)
TABLE 732
AI IN CYBERSECURITY MARKET, BY APPLICATION, 2019–2022 (USD MILLION)
TABLE 733
AI IN CYBERSECURITY MARKET, BY APPLICATION, 2023–2028 (USD MILLION)
TABLE 734
AI IN CYBERSECURITY MARKET, BY VERTICAL, 2019–2022 (USD MILLION)
TABLE 735
AI IN CYBERSECURITY MARKET, BY VERTICAL, 2023–2028 (USD MILLION)
TABLE 736
AI IN CYBERSECURITY MARKET, BY REGION, 2019–2022 (USD MILLION)
TABLE 737
AI IN CYBERSECURITY MARKET, BY REGION, 2023–2028 (USD MILLION)
FIGURE 1
GENERATIVE AI CYBERSECURITY MARKET: RESEARCH DESIGN
FIGURE 2
GENERATIVE AI CYBERSECURITY MARKET: DATA TRIANGULATION
FIGURE 3
GENERATIVE AI CYBERSECURITY MARKET: TOP-DOWN AND BOTTOM-UP APPROACHES
FIGURE 4
MARKET SIZE ESTIMATION METHODOLOGY—APPROACH 1, BOTTOM-UP (SUPPLY-SIDE): REVENUE FROM SOLUTION AND SERVICE PROVIDERS IN GENERATIVE AI CYBERSECURITY MARKET
FIGURE 5
MARKET SIZE ESTIMATION METHODOLOGY—APPROACH 2, BOTTOM-UP (SUPPLY-SIDE): COLLECTIVE REVENUE FROM KEY COMPANIES IN GENERATIVE AI CYBERSECURITY MARKET
FIGURE 6
MARKET SIZE ESTIMATION METHODOLOGY—APPROACH 3, BOTTOM-UP (SUPPLY-SIDE): COLLECTIVE REVENUE FROM BUSINESS UNITS (BU) OF KEY VENDORS IN GENERATIVE AI CYBERSECURITY MARKET
FIGURE 7
MARKET SIZE ESTIMATION METHODOLOGY—APPROACH 4, BOTTOM-UP (DEMAND-SIDE): SHARE OF GENERATIVE AI CYBERSECURITY THROUGH OVERALL IT SPENDING ON GENERATIVE AI CYBERSECURITY SOLUTIONS
FIGURE 8
GENERATIVE AI-BASED CYBERSECURITY SOFTWARE SEGMENT TO HOLD LARGEST MARKET SIZE IN 2025
FIGURE 9
NETWORK SECURITY SEGMENT TO HOLD MAJOR MARKET SHARE IN 2025
FIGURE 10
THREAT DETECTION & INTELLIGENCE SOFTWARE SEGMENT TO LEAD MARKET IN 2025
FIGURE 11
GENERATIVE AI APPLICATION SECURITY SEGMENT TO HOLD LARGEST MARKET SIZE IN 2025
FIGURE 12
GENERATIVE AI-BASED END USERS TO BE LARGEST SEGMENT IN 2025
FIGURE 13
HEALTHCARE & LIFE SCIENCES PROVIDERS TO WITNESS HIGHEST GROWTH RATE DURING FORECAST PERIOD
FIGURE 14
ASIA PACIFIC TO REGISTER FASTEST GROWTH BETWEEN 2025 AND 2031
FIGURE 15
SAAS ADOPTION AND REGULATORY PUSH TO FUEL GENERATIVE AI CYBERSECURITY DEMAND
FIGURE 16
DATABASE SECURITY SEGMENT TO HAVE HIGHEST GROWTH RATE DURING FORECAST PERIOD
FIGURE 17
SOFTWARE AND DATABASE SECURITY TO BE LARGEST SEGMENT IN NORTH AMERICA GENERATIVE AI CYBERSECURITY MARKET IN 2025
FIGURE 18
NORTH AMERICA TO HOLD LARGEST MARKET SHARE IN 2025
FIGURE 19
DRIVERS, RESTRAINTS, OPPORTUNITIES, AND CHALLENGES: GENERATIVE AI CYBERSECURITY MARKET
FIGURE 20
EVOLUTION OF GENERATIVE AI CYBERSECURITY
FIGURE 21
GENERATIVE AI CYBERSECURITY MARKET: SUPPLY CHAIN ANALYSIS
FIGURE 22
KEY PLAYERS IN GENERATIVE AI CYBERSECURITY MARKET ECOSYSTEM
FIGURE 23
GENERATIVE AI CYBERSECURITY MARKET: INVESTMENT LANDSCAPE AND FUNDING SCENARIO
FIGURE 24
NUMBER OF PATENTS GRANTED, 2019–2025
FIGURE 25
REGIONAL ANALYSIS OF PATENTS GRANTED, 2019–2025
FIGURE 26
GENERATIVE AI CYBERSECURITY MARKET: PORTER’S FIVE FORCES ANALYSIS
FIGURE 27
INFLUENCE OF STAKEHOLDERS ON BUYING PROCESS FOR TOP THREE GENERATIVE AI-BASED CYBERSECURITY VERTICALS
FIGURE 28
KEY BUYING CRITERIA FOR TOP THREE GENERATIVE AI-BASED CYBERSECURITY VERTICALS
FIGURE 29
TRENDS/DISRUPTIONS IMPACTING CUSTOMER BUSINESS
FIGURE 30
SOFTWARE SEGMENT TO DOMINATE MARKET IN 2025 AND 2030
FIGURE 31
APPLICATION SECURITY SEGMENT TO DOMINATE MARKET IN 2025
FIGURE 32
GENERATIVE AI-BASED CYBERSECURITY END USERS TO LEAD MARKET IN 2025
FIGURE 33
THREAT DETECTION & INTELLIGENCE SOFTWARE TO HOLD LARGEST MARKET IN 2025
FIGURE 34
NETWORK SECURITY SEGMENT TO HOLD LARGER MARKET IN 2025
FIGURE 35
INDIA TO WITNESS HIGHEST CAGR DURING FORECAST PERIOD
FIGURE 36
NORTH AMERICA TO LEAD MARKET IN 2025
FIGURE 37
NORTH AMERICA: MARKET SNAPSHOT
FIGURE 38
ASIA PACIFIC: MARKET SNAPSHOT
FIGURE 39
TOP FIVE PLAYERS DOMINATED MARKET FOR LAST FIVE YEARS
FIGURE 40
SHARE OF LEADING COMPANIES IN GENERATIVE AI CYBERSECURITY MARKET, 2024
FIGURE 41
PRODUCT COMPARATIVE ANALYSIS: GENERATIVE AI-BASED CYBERSECURITY
FIGURE 42
PRODUCT COMPARATIVE ANALYSIS: CYBERSECURITY FOR GENERATIVE AI
FIGURE 43
COMPANY VALUATION AND FINANCIAL METRICS OF KEY VENDORS
FIGURE 44
YEAR-TO-DATE (YTD) PRICE TOTAL RETURN AND 5-YEAR STOCK BETA OF KEY VENDORS
FIGURE 45
GENERATIVE AI CYBERSECURITY MARKET: COMPANY EVALUATION MATRIX (KEY PLAYERS), 2024
FIGURE 46
COMPANY FOOTPRINT (25 COMPANIES)
FIGURE 47
GENERATIVE AI CYBERSECURITY MARKET: COMPANY EVALUATION MATRIX (KEY PLAYERS OFFERING CYBERSECURITY SOLUTIONS FOR GEN AI), 2024
FIGURE 48
COMPANY FOOTPRINT (13 COMPANIES)
FIGURE 49
GENERATIVE AI CYBERSECURITY MARKET: COMPANY EVALUATION MATRIX (STARTUPS/SMES), 2024
FIGURE 50
GENERATIVE AI CYBERSECURITY MARKET: COMPANY EVALUATION MATRIX (STARTUPS/SMES OFFERING CYBERSECURITY SOLUTIONS FOR GENERATIVE AI), 2024
FIGURE 51
MICROSOFT: COMPANY SNAPSHOT
FIGURE 52
IBM: COMPANY SNAPSHOT
FIGURE 53
GOOGLE: COMPANY SNAPSHOT
FIGURE 54
SENTINELONE: COMPANY SNAPSHOT
FIGURE 55
NVIDIA: COMPANY SNAPSHOT
FIGURE 56
AWS: COMPANY SNAPSHOT
FIGURE 57
CISCO: COMPANY SNAPSHOT
FIGURE 58
CROWDSTRIKE: COMPANY SNAPSHOT
FIGURE 59
FORTINET: COMPANY SNAPSHOT
FIGURE 60
ZSCALER: COMPANY SNAPSHOT





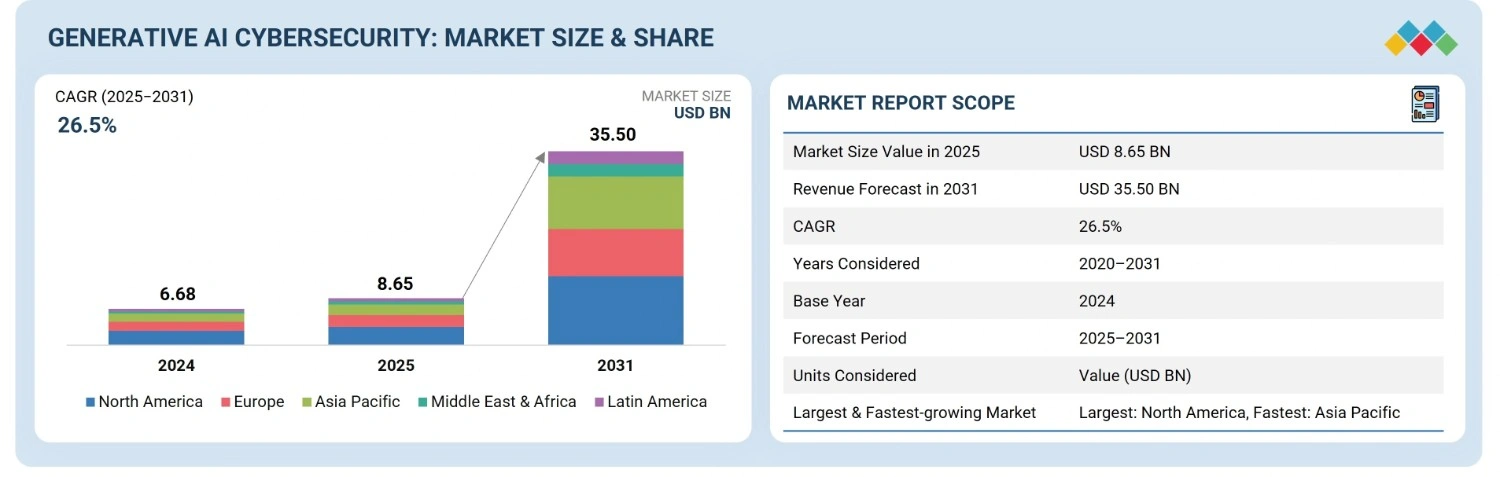








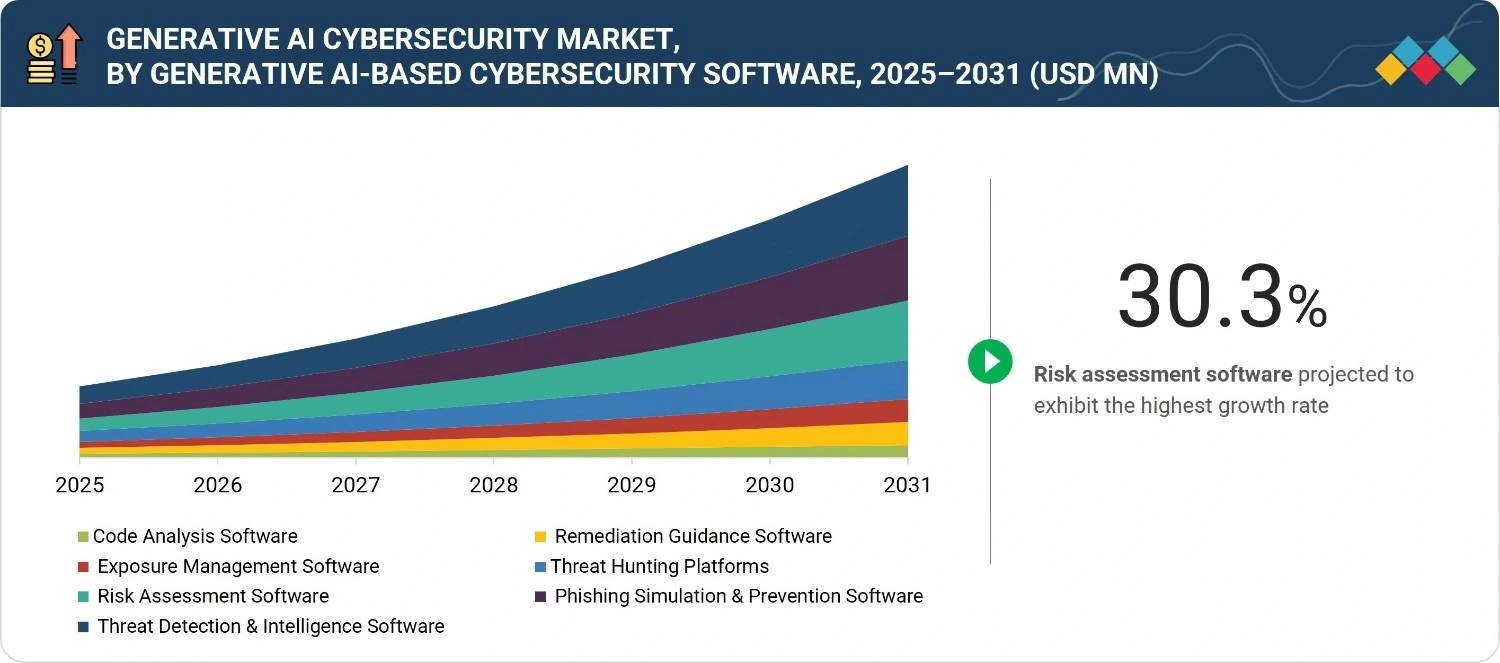




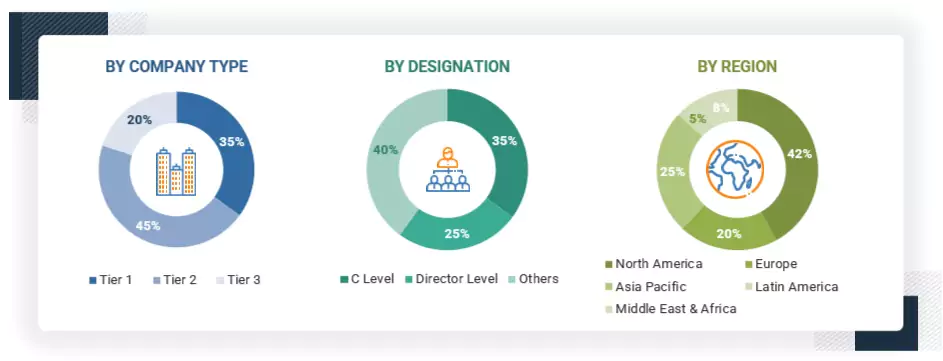














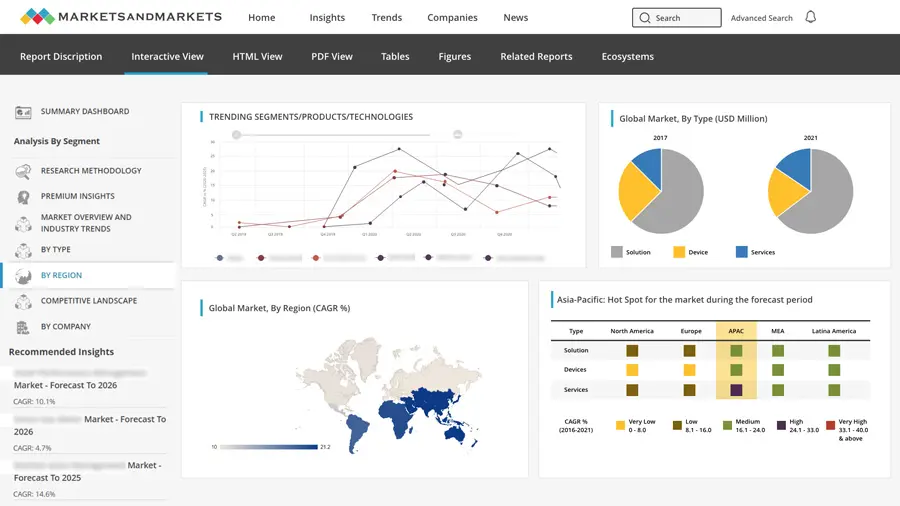
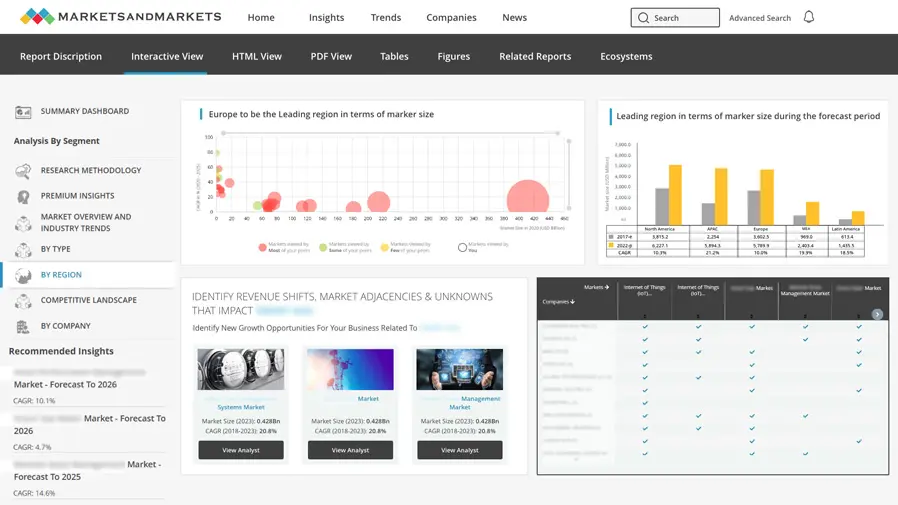
Growth opportunities and latent adjacency in Generative AI Cybersecurity Market