
Middle East Cybersecurity Market
Middle East Cybersecurity Market by Solution Type (IAM, Firewall & VPN, Log Management & SIEM, Antivirus/Antimalware), Service (Professional (Risk & Threat Assessment, Training & Education), Managed)), Security Type (Cloud, Application) - Forecast to 2031




OVERVIEW
Source: Secondary Research, Interviews with Experts, MarketsandMarkets Analysis
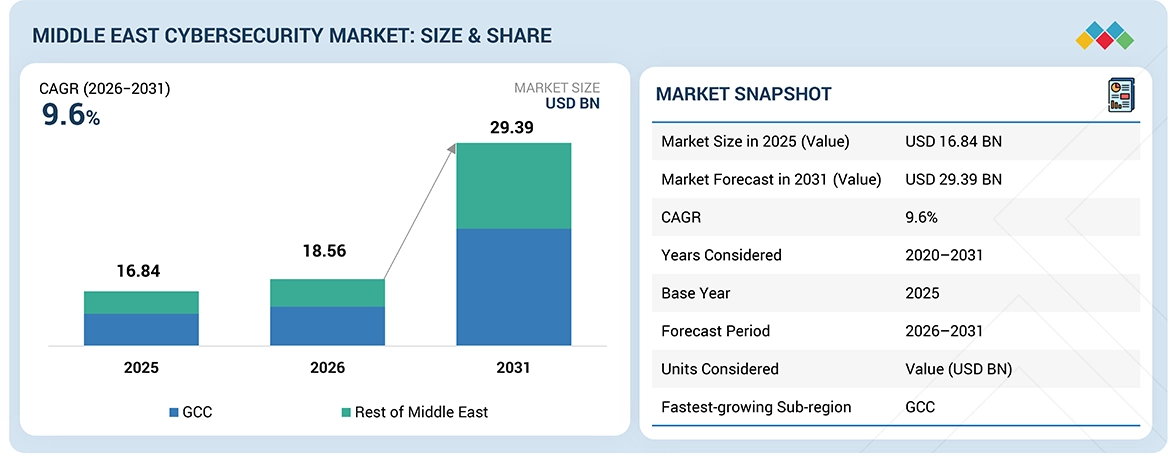
The Middle East cybersecurity market is projected to reach USD 29.39 billion by 2031 from USD 18.56 billion in 2026, at a CAGR of 9.6% from 2026 to 2031. The fast pace of digital transformation in different sectors in the Middle East is increasing the attack surface as organizations are embracing digital technologies such as cloud computing, IoT, and smart technologies. On the other hand, factors such as conflicts in the region, tensions between countries such as Iran and Israel, cyber wars targeting infrastructure such as oil and gas facilities and government infrastructure, are forcing organizations to look for solutions for threat intelligence, critical infrastructure protection, and cyber resilience. This is driving the demand for cybersecurity solutions in the region.
KEY TAKEAWAYS
-
BY COUNTRYGCC countries are estimated to account for the largest market share of 59.9% in 2026.
-
BY OFFERINGBy offering, the solutions segment is estimated to dominate the market in terms of share in 2026.
-
BY SOLUTION TYPEBy solution type, the log management & SIEM segment is expected to lead the market during the forecast period.
-
BY SECURITY TYPEBy security type, the network security segment is expected to have a significant market share during the forecast period.
-
BY DEPLOYMENT MODEBy deployment mode, the hybrid segment is expected to register the highest CAGR of 11.5% during the forecast period.
-
BY ORGANIZATION SIZEBy organizations size, the SMEs segment will exhibit the highest CAGR of 11.6% during the forecast period.
-
BY VERTICALBy vertical, the healthcare & life sciences segment is projected to register the highest CAGR during the forecast period.
-
COMPETITIVE LANDSCAPE - KEY PLAYERSIBM, Palo Alto Networks, and Check Point are leading players in the Middle East cybersecurity market, offering comprehensive security platforms spanning network security, cloud security, threat intelligence, and zero-trust architectures, with strong capabilities in securing critical infrastructure, government systems, and enterprise environments.
-
COMPETITIVE LANDSCAPE - STARTUPS/SMEsHelp AG, sirar, and CPX are emerging regional players providing specialized cybersecurity services focused on managed security, sovereign cloud protection, and advanced threat detection, with strong alignment to regional regulatory requirements and increasing demand for localized cybersecurity capabilities.
Factors such as increased digital connectivity between countries in the region and increased reliance on digital infrastructure in individual countries are forcing organizations to look for solutions to protect digital infrastructure from cyberattacks. Governments are investing in the establishment of cyber operations centers for individual countries. This is driving demand for cybersecurity solutions in the region as there is a continued focus on digital trust and security.
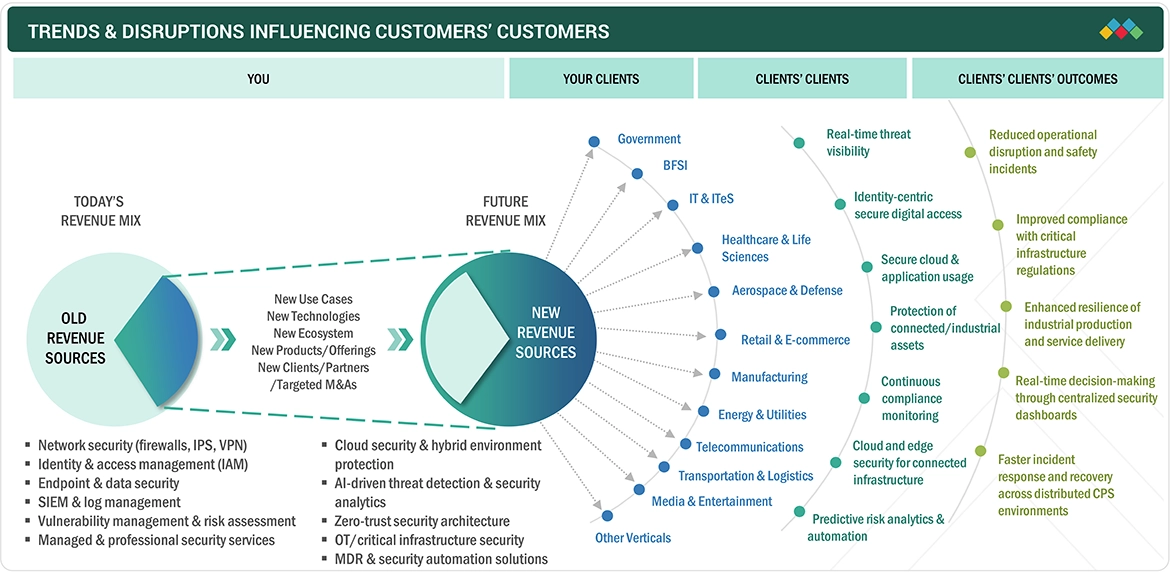
TRENDS & DISRUPTIONS IMPACTING CUSTOMERS' CUSTOMERS
Middle East cybersecurity has seen a significant transformation in recent times because of the expansion of the digital ecosystem and the modernization of critical infrastructure. Organizations are moving from basic security technologies to advanced security technologies. This transformation has changed the way revenue models operate and has impacted the enterprise world. The Middle East cybersecurity market has seen significant changes in recent times because of the expansion of the digital ecosystem. Organizations are moving from basic security technologies to advanced security technologies. This transformation has changed the way revenue models operate and has impacted the enterprise world.
Source: Secondary Research, Interviews with Experts, MarketsandMarkets Analysis
MARKET DYNAMICS
Level
-
Accelerated digital transformation across sectors

-
Geopolitical tensions and rise of state-sponsored cyber threats
Level
-
Budgetary constraints on resource allocations
-
Resistance to emerging security technologies
Level
-
Investments by governments and businesses to enhance cybersecurity infrastructure
-
Burgeoning startup ecosystem
Level
-
Third-party dependencies exposing weaknesses in cybersecurity landscape
-
Shortage of skilled workforce
Source: Secondary Research, Interviews with Experts, MarketsandMarkets Analysis
Driver: Accelerated digital transformation across sectors
The accelerated rate of digital transformation in the BFSI, government, and energy sectors is driving cloud computing, IoT deployments, and smart infrastructure initiatives, thus increasing the regional attack surface. This necessitates the need to invest in robust and sophisticated security platforms. Organizations are focusing on AI-based security and identity-first initiatives to secure their hybrid environment, according to IBM. Regional initiatives like Saudi Vision 2030 are accelerating enterprise-wide cybersecurity investments.
Restraint: Budgetary constraints on resource allocations
Despite the increased risks of cyber threats, budget constraints and competing priorities for digital investments in information technology in terms of cybersecurity spending are being faced by organizations, especially SMEs and public organizations. As per Axios (December 2025), it was highlighted by Palo Alto Networks that organizations are spending more on detection and response rather than upgrading their overall security posture, due to constraints in spending allocation.
Opportunity: Investments by governments and businesses to enhance cybersecurity infrastructure
Middle Eastern governments and enterprises are investing heavily in building stronger cybersecurity infrastructure for the protection of digital assets. Large-scale projects in the UAE and Saudi Arabia are boosting the need for advanced technologies like AI-based threat protection and cloud security. In October 2025, Palo Alto Networks announced its AI-based technology platforms powered by 1.2 billion+ incident responses, highlighting the growing need for enterprise-scale intelligence-based solutions.
Challenge: Third-party dependencies exposing weaknesses in cybersecurity landscape
The reliance on third-party vendors, cloud service providers, and intricate supply chains is resulting in increased cybersecurity risks. The interconnected ecosystems create indirect vulnerabilities that can be exploited by attackers. The lack of visibility in these ecosystems is resulting in difficulties in managing the associated risks. According to IBM (April 2025), the emergence of ‘shadow AI’ is resulting in the introduction of unmanaged external tools that are creating security gaps.
MIDDLE EAST CYBERSECURITY MARKET: COMMERCIAL USE CASES ACROSS INDUSTRIES
| COMPANY | USE CASE DESCRIPTION | BENEFITS |
|---|---|---|
 |
Rising phishing, spam, and targeted cyberattacks increased risk to customer data, intellectual property, and banking infrastructure, requiring scalable data-center-level security visibility and protection. | Implemented integrated deep security and advanced threat protection to enable real-time attack detection, strengthen ransomware defense, and improve network traffic monitoring and control. |
 |
Expansion of airport IT and endpoint infrastructure created challenges in maintaining unified security visibility and protection across networks, email, web, and connected systems. | Deployed integrated endpoint-to-network malware protection platform to enhance threat detection, enable centralized security monitoring, and support scalable infrastructure security during operational growth. |
 |
Security risks in virtualized data center environments hosting critical customer experience applications required automated traffic protection and consistent security policy enforcement. | Implemented virtual firewalls and centralized security management to strengthen threat detection, improve compliance readiness, reduce deployment time, and enhance network segmentation efficiency. |
 |
Need for secure remote access and identity protection for employees and partners across distributed retail operations increased demand for cost-effective authentication controls. | Deployed token-less multi-factor authentication solution to streamline identity provisioning, strengthen access security, enable flexible authentication methods, and reduce operational security costs. |
 |
Smart city initiatives and digital infrastructure modernization increased exposure to cyber threats, requiring consolidated protection across networks, endpoints, and cloud migration initiatives. | Implemented unified cybersecurity platform to enable integrated protection architecture, accelerate secure digital transformation, improve cyber resilience, and optimize security investment efficiency. |
Logos and trademarks shown above are the property of their respective owners. Their use here is for informational and illustrative purposes only.
MARKET ECOSYSTEM
The Middle East cybersecurity market is experiencing the emergence of a diverse range of vendors providing cybersecurity services in the region. These services are especially concentrated in the areas of identity security, network security, endpoint security, data security, and compliance security. Organizations in the Middle East region are moving from basic security technologies to advanced security technologies.

Logos and trademarks shown above are the property of their respective owners. Their use here is for informational and illustrative purposes only.
MARKET SEGMENTS
Source: Secondary Research, Interviews with Experts, MarketsandMarkets Analysis
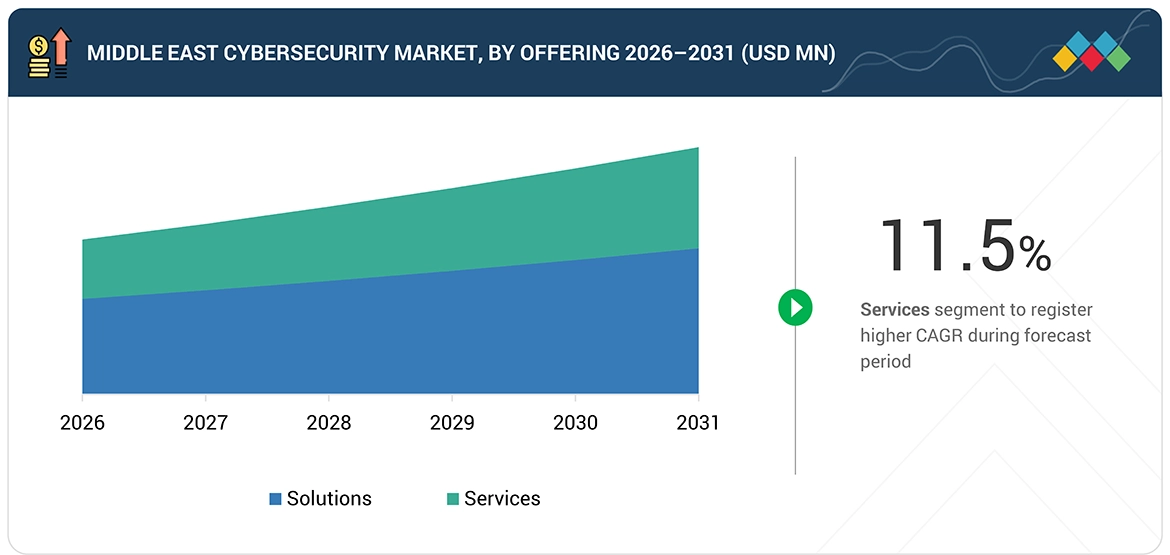
Middle East Cybersecurity Market, by Offering
The solutions segment leads the market as organizations focus on deploying integrated cybersecurity platforms instead of services to manage the increasing complexity of threats. In the Middle Eastern market, enterprises are investing in SIEM, IAM, endpoint, and cloud security solutions for real-time protection. As per IBM (April 2025), enterprises will focus on consolidating security tools into unified platforms, indicating high demand for comprehensive security solutions.
Middle East Cybersecurity Market, by Solution Type
Log management and SIEM tools lead the market due to the rising need for centralized visibility, compliance, and real-time threat detection in hybrid environments. Organizations are focusing on correlating security events from IT and OT systems. According to Microsoft, security teams use AI-powered SIEM tools such as Microsoft Sentinel to automate threat detection and minimize response times.
Middle East Cybersecurity Market, by Security Type
Network security remains the biggest segment as more and more organizations seek to protect the ever-expanding perimeter created by cloud computing, remote access, and other interconnected devices. Firewalls, VPNs, and intrusion prevention systems are a necessity in the protection of sensitive information. According to Palo Alto Networks (October 2025), organizations increasingly use AI-powered network security to stop sophisticated cyber threats and protect the ever-expanding perimeter.
Middle East Cybersecurity Market, by Deployment Mode
On-premises deployment leads the market due to stringent regulatory requirements, data sovereignty, and the need to secure the infrastructure in sectors such as government and energy. Organizations seek to maintain control over data and security processes. According to Check Point (February 2025), regional businesses will maintain the on-premises and hybrid security architecture to fulfill regulatory requirements and maintain high levels of control over cybersecurity infrastructure.
Middle East Cybersecurity Market, by Organization Size
Large enterprises lead in the adoption of cybersecurity in the Middle East because they are more exposed to advanced cyber threats compared to small businesses. They can invest more in advanced security architecture compared to small businesses. According to IBM (April 2025), large enterprises will be at the forefront in the adoption of AI-driven security operations and zero-trust strategies to strengthen the defense against growing cyber threats in their global operations.
Middle East Cybersecurity Market, by Vertical
The BFSI sector is the largest segment in the Middle East cybersecurity market due to the high level of exposure to financial fraud, ransomware, and data breaches, along with stringent regulatory guidelines that need to be followed in the domain of data security. Banks and financial institutions are looking to invest in the domains of identity security, fraud detection, and digital banking. According to IBM (April 2025), financial institutions will continue to be one of the most attacked industries in the world.
REGION
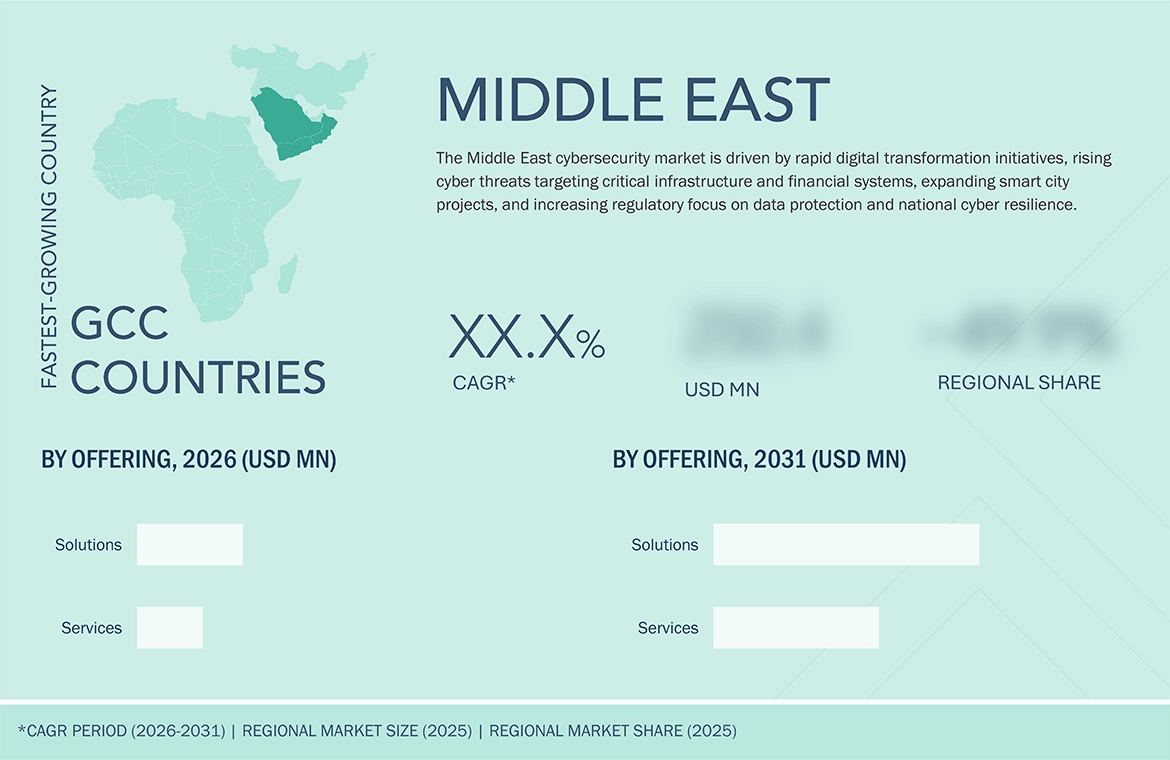
GCC countries to be fastest-growing in Middle East cybersecurity market during forecast period.
In the Middle East, the cybersecurity market in GCC countries is projected to witness significant growth due to strong government-led digital transformation programs, high investments in smart infrastructure, and stringent regulatory frameworks. Countries such as the UAE and Saudi Arabia are actively implementing national cybersecurity strategies and data protection mandates, accelerating enterprise adoption. GCC countries also face high volumes of cyberattacks targeting critical sectors, pushing organizations to invest in advanced security solutions and resilient cyber defense architectures.
MIDDLE EAST CYBERSECURITY MARKET: COMPANY EVALUATION MATRIX
IBM (Key Player) is a leader in the Middle East cybersecurity market due to its AI-driven security platforms, strong threat intelligence, and comprehensive offerings across cloud, identity, and incident response, widely adopted by large enterprises and government organizations. Eviden (Emerging Player) is gaining traction with its focus on sovereign cybersecurity, digital security services, and region-specific solutions tailored to regulatory requirements and critical infrastructure protection in the region.

Source: Secondary Research, Interviews with Experts, MarketsandMarkets Analysis
KEY MARKET PLAYERS
- Palo Alto Networks (US)
- IBM (US)
- Check Point (US)
- Cisco (US)
- Fortinet (US)
- Trend Micro (Japan)
- CrowdStrike (US)
- CPX (UAE)
- sirar by stc (KSA)
- SITE (KSA)
- Help AG (UAE)
- Mandiant (US)
- Eviden (Atos) (France)
- Trellix (US)
- SOCRadar (US)
MARKET SCOPE
| REPORT METRIC | DETAILS |
|---|---|
| Market Size in 2025 (Value) | USD 16.84 Billion |
| Market Forecast in 2026 (Value) | USD 18.56 Billion |
| Market Forecast in 2031 (Value) | USD 29.39 Billion |
| Growth Rate | CAGR of 9.6% from 2026 to 2031 |
| Years Considered | 2020-2031 |
| Base Year | 2025 |
| Forecast Period | 2026-2031 |
| Units Considered | Value (USD Billion) |
| Report Coverage | Revenue forecast, company ranking, competitive landscape, growth factors, and trends |
| Segments Covered |
|
| Countries Covered | GCC Countries, Rest of Middle East |
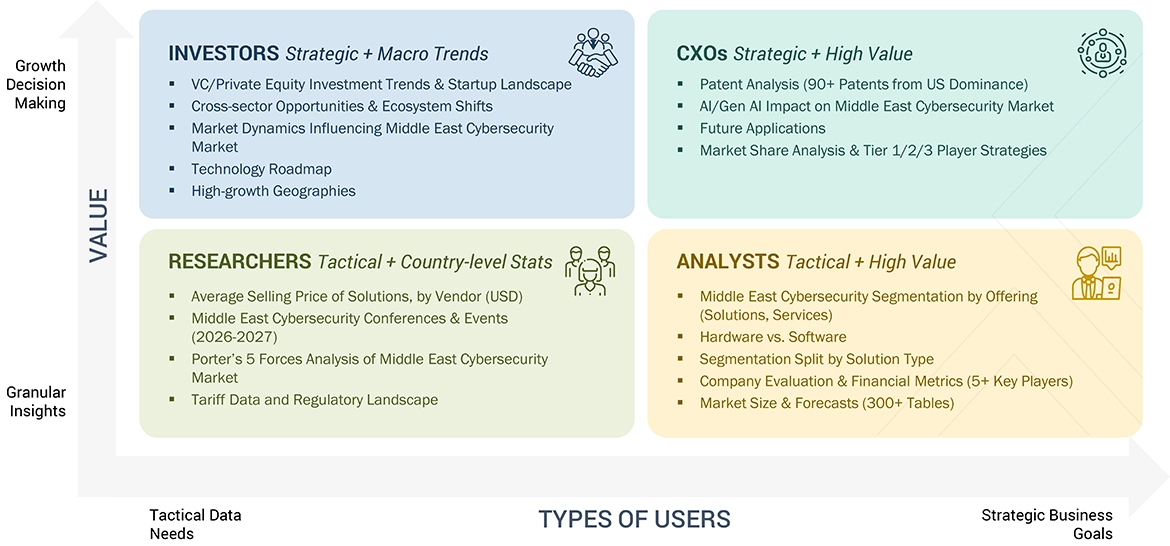
WHAT IS IN IT FOR YOU: MIDDLE EAST CYBERSECURITY MARKET REPORT CONTENT GUIDE
DELIVERED CUSTOMIZATIONS
We have successfully delivered the following deep-dive customizations:
| CLIENT REQUEST | CUSTOMIZATION DELIVERED | VALUE ADDS |
|---|---|---|
| Leading Solution Provider (KSA) | Product Benchmarking: Cybersecurity Solution Matrix offering detailed comparison of major vendors’ offerings in KSA across firewall, XDR, cloud security, IAM, OT/ICS protection and AI-driven threat detection, mapped against NCA compliance requirements and sector-specific deployment priorities. | Clear visibility into competitive positioning, technology differentiation, and regional relevance, enabling stronger go-to-market development and investment decisions for the Saudi cybersecurity landscape. |
| Leading Service Provider (KSA) | Company Intelligence: In-depth profiling of key cybersecurity services players in KSA (up to 5), covering managed SOC, MDR, GRC, digital forensics, offensive security, and cloud security services, along with partnership ecosystems and sovereign-cloud alignment. | Holistic understanding of service-provider strength and expansion opportunities in KSA, identifying white spaces for collaboration, partnership, and capability enhancement across government and enterprise segments. |
RECENT DEVELOPMENTS
- April 2025 : Check Point Software announced a multi-partner strategic partnership with AWS, WIZ, Radware, and TechBridge MEA to improve AI-powered cybersecurity capabilities in the UAE. The collaboration seeks to demonstrate integrated threat intelligence and zero-trust solutions in hybrid contexts, boosting local cyber resilience and creativity.
- February 2025 : Palo Alto Networks introduced Cortex Cloud, a next-generation AI-powered cloud security technology that combines Prisma Cloud with Cortex CDR. Combined with Cortex XSIAM, it provides real-time threat detection, runtime protection, and AI-based remediation across cloud environments, revolutionizing SOC operations and allowing end-to-end cloud security.
- February 2025 : Cisco announced a significant expansion in Saudi Arabia with the launch of cloud security and Webex collaboration data centers, an AI training partnership with KACST, and plans to establish a wireless technology manufacturing facility. These initiatives aim to enhance local cybersecurity resilience, bridge AI talent gaps, and integrate the Kingdom into Cisco’s global supply chain, supporting Vision 2030.
- January 2025 : IBM and Salesforce partnered to establish an AI Innovation Center in Riyadh dedicated to developing safe AI agent solutions. The program, powered by IBM Watsonx and Salesforce Agentforce, aims to improve cybersecurity by deploying trusted, compliant AI across Saudi organizations
Table of Contents

Methodology
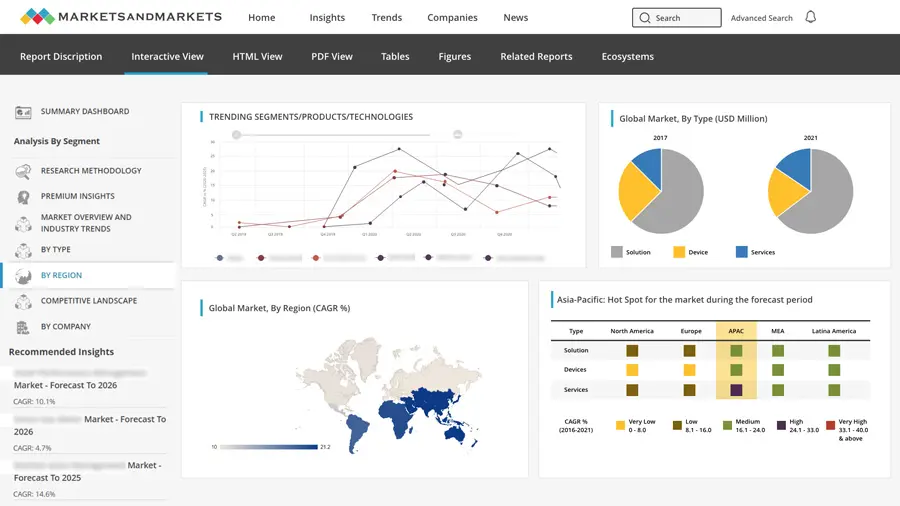
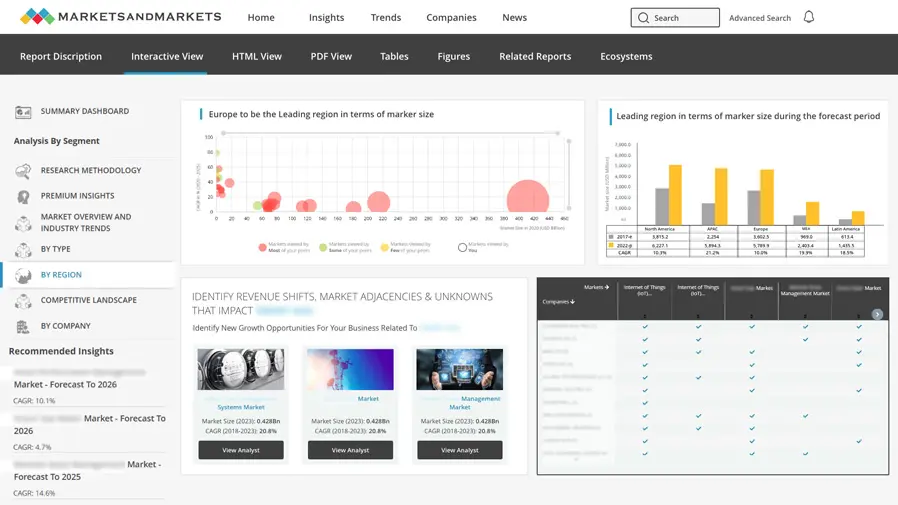
Secondary research was conducted to collect information useful for this technical, market-oriented, and commercial study of the Middle East cybersecurity market. The next step involved validating these findings, assumptions, and sizing with industry experts across the value chain using primary research. Different approaches, including top-down and bottom-up methods, were employed to estimate the total market size. After that, the market breakup and data triangulation procedures were used to estimate the market size of the segments and subsegments of the Middle East cybersecurity market.
Secondary Research
During the secondary research process, various secondary sources were consulted to identify and collect information relevant to the study. The secondary sources included annual reports, press releases, investor presentations of Middle East cybersecurity vendors, forums, certified publications, and whitepapers. The secondary research was mainly used to obtain key information about the industry’s supply chain, the total pool of key players, market classification and segmentation according to industry trends to the bottom-most level, country-level markets, and key developments from both market- and technology-oriented perspectives, all of which were further validated by primary sources.
Primary Research
In the primary research process, various primary sources from both the supply and demand sides were interviewed to obtain qualitative and quantitative information for this report. The primary sources from the supply side included various industry experts, including chief executive officers (CEOs), vice presidents (VPs), marketing directors, technology and innovation directors, and related key executives from various key companies and organizations operating in the Middle East cybersecurity market.
In the market engineering process, top-down and bottom-up approaches were extensively used, along with several data triangulation methods, to perform market estimation and forecasting for the overall market segments and subsegments listed in this report. Extensive qualitative and quantitative analysis was performed on the complete market engineering process to list key information/insights throughout the report.
After the complete market engineering process (including calculations for market statistics, market breakups, market size estimations, market forecasts, and data triangulation), extensive primary research was conducted to gather information and verify & validate the critical numbers arrived at. The primary research was also conducted to identify the segmentation types, industry trends, competitive landscape of Middle East cybersecurity market players, and key market dynamics, such as drivers, restraints, opportunities, challenges, industry trends, and key strategies.
Following is the breakup of the primary study:
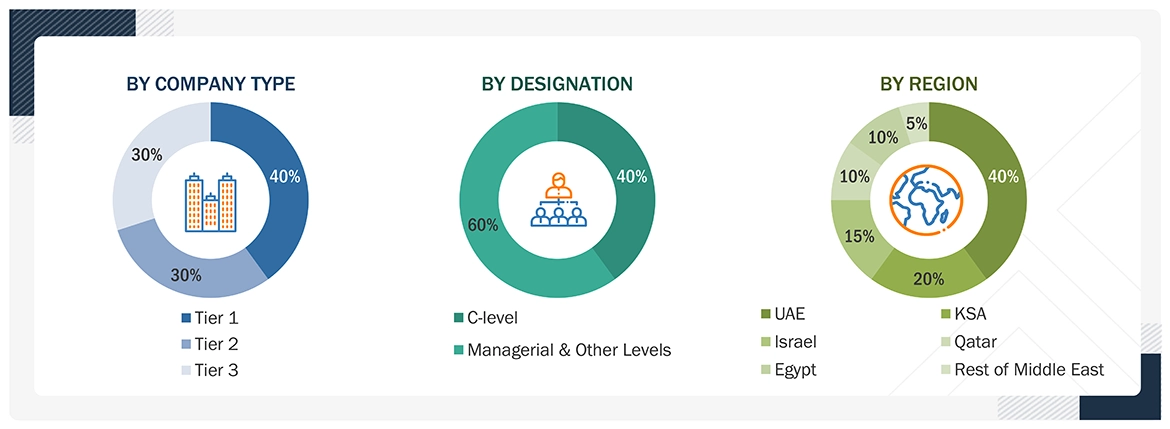
Note: Tier 1 companies receive revenues higher than USD 10 billion; Tier 2 companies' revenues range between USD 1 and 10 billion; and Tier 3 companies' revenues range between USD 500 million and USD 1 billion. Other designations include sales, marketing, and product managers.
To know about the assumptions considered for the study, download the pdf brochure
Market Size Estimation
Top-down and bottom-up approaches were employed to estimate and validate the size of the Middle East cybersecurity market, as well as the size of various dependent sub-segments within the overall Middle East cybersecurity market. The research methodology used to estimate the market size includes the following details: critical players in the market were identified through secondary research, and their market shares in the respective regions were determined through primary and secondary research. This entire procedure involved studying the annual and financial reports of the top market players, and extensive interviews were conducted with key industry leaders, including CEOs, VPs, directors, and marketing executives, to gather valuable insights.
All percentage splits and breakdowns were determined using secondary sources and verified through primary sources. All possible parameters that affect the market covered in this research study were accounted for, viewed in extensive detail, verified through primary research, and analyzed to get the final quantitative and qualitative data. This data was consolidated and added to detailed inputs and analysis from MarketsandMarkets.
INFOGRAPHIC DEPICTING BOTTOM-UP AND TOP-DOWN APPROACHES

Data Triangulation
The market was split into several segments and subsegments after arriving at the overall market size using the market size estimation processes explained above. The data triangulation and market breakup procedures were employed, wherever applicable, to complete the overall market engineering process and arrive at the exact statistics of each market segment and subsegment. The data was triangulated by studying various factors and trends from both the demand and supply sides.
Market Definition
According to MarketsandMarkets, “Cybersecurity encompasses a range of technologies, processes, and practices designed to protect critical systems—including networks, physical devices, programs, and information—from unauthorized access, insider threats, and malicious attacks. These cyberattacks can disrupt data transmission across networks, lead to operational interruptions, and result in financial loss through extortion or ransomware. Cybersecurity, also known as information security, can be achieved through a combination of hardware, software, and services.
In the Middle East, the increasing pace of digitalization, the growing influence of generative AI, and heightened exposure to sophisticated cyberattacks drive the adoption of cybersecurity solutions and services. Countries in the region are developing national cybersecurity strategies and implementing critical infrastructure protection policies to safeguard essential digital assets.”
Key Stakeholders
- Chief Technology and Data Officers
- Consulting Service Providers
- Managed Security Services Professionals
- Business Analysts
- Information Technology (IT) Professionals
- Government Agencies
- Investors And Venture Capitalists
- Small and Medium-sized Enterprises (SMEs) and Large Enterprises
- Third-party Providers
- Consultants/Consultancies/Advisory Firms
- Managed and Professional Service Providers
Report Objectives
- To describe and forecast the security testing market by offering, solution type, security type, deployment mode, organization size, vertical, and region from 2026 to 2031, and analyze the various macroeconomic and microeconomic factors that affect market growth
- To forecast the market size of five major regions: North America, Europe, Asia Pacific, the Middle East & Africa, and Latin America
- To analyze the subsegments of the market concerning individual growth trends, prospects, and contributions to the overall market.
- To provide detailed information related to the primary factors (drivers, restraints, opportunities, and challenges) influencing the growth of the Middle East cybersecurity market.
- To analyze opportunities in the market for stakeholders by identifying high-growth segments of the Middle East cybersecurity market.
- To profile the key players of the Middle East cybersecurity market and comprehensively analyze their market size and core competencies.
- Track and analyze competitive developments, such as new product launches, mergers and acquisitions, partnerships, agreements, and collaborations in the Middle East cybersecurity market.
Available customizations:
With the given market data, MarketsandMarkets offers customizations based on company-specific needs. The following customization options are available for the report:
Company information
- Detailed analysis and profiling of additional market players (up to 5)
Need a Tailored Report?
Customize this report to your needs
Get 10% FREE Customization
Customize This ReportPersonalize This Research
- Triangulate with your Own Data
- Get Data as per your Format and Definition
- Gain a Deeper Dive on a Specific Application, Geography, Customer or Competitor
- Any level of Personalization
Let Us Help You
- What are the Known and Unknown Adjacencies Impacting the Middle East Cybersecurity Market
- What will your New Revenue Sources be?
- Who will be your Top Customer; what will make them switch?
- Defend your Market Share or Win Competitors
- Get a Scorecard for Target Partners
Custom Market Research Services
We Will Customise The Research For You, In Case The Report Listed Above Does Not Meet With Your Requirements
Get 10% Free CustomisationTESTIMONIALS













Growth opportunities and latent adjacency in Middle East Cybersecurity Market