4
MARKET OVERVIEW
Governments prioritize cybersecurity amid rising cyber threats and geopolitical tensions, driving strategic investments and innovations.
63
4.2.1.1
RISING GEOPOLITICAL TENSIONS AND CYBER WARFARE
4.2.1.2
RAPID DIGITAL TRANSFORMATION AND EXPANSION OF E-GOVERNMENT SERVICES
4.2.1.3
RISING FREQUENCY AND SOPHISTICATION OF CYBERATTACKS ON GOVERNMENT SYSTEMS
4.2.1.4
GROWING GOVERNMENT INVESTMENT IN NATIONAL CYBER DEFENSE AND CRITICAL INFRASTRUCTURE PROTECTION
4.2.2.1
COMPLEX GOVERNMENT PROCUREMENT PROCESSES AND LENGTHY CYBERSECURITY IMPLEMENTATION CYCLES
4.2.2.2
BUDGET CONSTRAINTS AND LIMITED FINANCIAL RESOURCES IN PUBLIC SECTOR ORGANIZATIONS
4.2.2.3
FRAGMENTED CYBERSECURITY GOVERNANCE ACROSS GOVERNMENT AGENCIES
4.2.3.1
EMERGENCE OF NATIONAL CYBER DEFENSE COMMANDS AND SOVEREIGN CYBERSECURITY INFRASTRUCTURE
4.2.3.2
PUBLIC-PRIVATE CYBERSECURITY PARTNERSHIPS FOR NATIONAL SECURITY PROGRAM
4.2.3.3
EXPANSION OF AI-POWERED CYBERSECURITY FOR GOVERNMENT SECURITY OPERATIONS CENTERS
4.2.3.4
GROWING DEMAND FOR CYBERSECURITY SOLUTIONS FOR DIGITAL IDENTITY AND CITIZEN DATA PLATFORMS
4.2.4.1
BALANCING CYBERSECURITY WITH PRIVACY AND CIVIL LIBERTIES REGULATIONS
4.2.4.2
MANAGING SECURITY RISKS FROM EXPANDING GOVERNMENT DIGITAL ECOSYSTEMS AND THIRD-PARTY INTEGRATIONS
4.2.4.3
LIMITED REAL-TIME CYBER THREAT INTELLIGENCE SHARING ACROSS GOVERNMENT AGENCIES
4.3
UNMET NEEDS AND WHITE SPACES
4.4
INTERCONNECTED MARKETS AND CROSS-SECTOR OPPORTUNITIES
4.4.1
INTERCONNECTED MARKETS
4.4.2
CROSS-SECTOR OPPORTUNITIES
4.5
STRATEGIC MOVES BY TIER-1/2/3 PLAYERS
4.5.1
CROSS-TIER STRATEGIC PATTERNS
4.5.2.1
DEVELOPMENT OF NATIONAL CYBERSECURITY STRATEGIES AND DECENTRALIZED CYBER DEFENSE PROGRAMS
4.5.2.2
EXPANSION OF ZERO-TRUST AND IDENTITY-CENTRIC SECURITY FOR GOVERNMENT SYSTEMS
4.5.2.3
SOVEREIGN CYBERSECURITY PLATFORMS FOR GOVERNMENTS
5
INDUSTRY TRENDS
Navigate industry shifts with strategic insights from competitive forces and cybersecurity trends.
79
5.1
PORTER’S FIVE FORCES ANALYSIS
5.1.1
THREAT OF NEW ENTRANTS
5.1.2
BARGAINING POWER OF SUPPLIERS
5.1.3
BARGAINING POWER OF BUYERS
5.1.4
THREAT OF SUBSTITUTES
5.1.5
INTENSITY OF COMPETITIVE RIVALRY
5.2
MACROECONOMIC INDICATORS
5.2.2
GDP TRENDS AND FORECAST
5.2.3
TRENDS IN GLOBAL ICT INDUSTRY
5.2.4
TRENDS IN GLOBAL CYBERSECURITY INDUSTRY
5.3.1
STRATEGIC & REGULATORY FOUNDATION
5.3.2
CORE SECURITY INFRASTRUCTURE ENABLEMENT
5.3.3
CYBERSECURITY SOLUTION DEVELOPMENT
5.3.4
SERVICES & INTEGRATION LAYER
5.3.5
DISTRIBUTION & LOCALIZATION ECOSYSTEM
5.3.6
PUBLIC SECTOR DEMAND (END-USER LAYER)
5.5.1
AVERAGE SELLING PRICE TREND OF KEY VENDORS, BY SOLUTION TYPE, 2026
5.5.2
INDICATIVE PRICING ANALYSIS, BY OFFERING
5.6.1
IMPORT SCENARIO (HS CODE 8471)
5.6.2
EXPORT SCENARIO (HS CODE 8517)
5.7
KEY CONFERENCES & EVENTS, 2026
5.8
TRENDS AND DISRUPTIONS IMPACTING CUSTOMER BUSINESS
5.9
INVESTMENT AND FUNDING SCENARIO
5.10.1
PALO ALTO NETWORKS PLATFORMIZES VERMONT JUDICIARY TO SECURE GOVERNMENT OPERATIONS AND ENSURE ZERO TRUST
5.10.2
CITY OF LOS ANGELES ENHANCES THREAT DETECTION AND INCIDENT RESPONSE WITH RECORDED FUTURE CYBER THREAT INTELLIGENCE
5.10.3
CROWDSTRIKE ENABLES FEDERAL GOVERNMENT AGENCIES TO IMPLEMENT ZERO TRUST AND PROTECT MISSION-CRITICAL SYSTEMS
5.10.4
IBM STRENGTHENS CYBERSECURITY RESPONSE CAPABILITIES FOR INTERNATIONAL GOVERNMENT AGENCIES
5.10.5
CYBERARK STRENGTHENS IDENTITY SECURITY FOR BRAZILIAN LABOR COURT TO PROTECT SENSITIVE GOVERNMENT DATA
5.11
IMPACT OF 2025 US TARIFF – GOVERNMENT AND PUBLIC SECTOR CYBERSECURITY MARKET
5.11.3
PRICE IMPACT ANALYSIS
5.11.4
IMPACT ON COUNTRY/REGION
5.11.5
IMPACT ON END-USE INDUSTRIES
6
TECHNOLOGICAL ADVANCEMENTS, AI-DRIVEN IMPACT, PATENTS, INNOVATIONS, AND FUTURE APPLICATIONS
AI-driven innovations redefine cybersecurity with autonomous defense and smart infrastructure applications.
112
6.1.1
KEY EMERGING TECHNOLOGIES
6.1.1.1
ZERO TRUST SECURITY ARCHITECTURE
6.1.1.2
SECURITY INFORMATION AND EVENT MANAGEMENT
6.1.1.3
IDENTITY AND ACCESS MANAGEMENT
6.1.2
COMPLEMENTARY TECHNOLOGIES
6.1.2.2
DIGITAL IDENTITY AND AUTHENTICATION TECHNOLOGIES
6.1.2.3
ARTIFICIAL INTELLIGENCE AND MACHINE LEARNING FOR CYBERSECURITY
6.1.3
ADJACENT TECHNOLOGIES
6.1.3.1
INTERNET OF THINGS (IOT) AND SMART INFRASTRUCTURE
6.1.3.2
CLOUD COMPUTING AND GOVERNMENT DIGITAL PLATFORMS
6.1.3.3
HIGH-PERFORMANCE COMPUTING AND DATA ANALYTICS
6.2
TECHNOLOGY/PRODUCT ROADMAP
6.2.1
SHORT-TERM (2026–2027) | FOUNDATION & EARLY COMMERCIALIZATION
6.2.2
MID-TERM (2027–2030) | SCALING, INTELLIGENCE, AND ECOSYSTEM EXPANSION
6.2.3
LONG-TERM (2030–2035+) | AUTONOMOUS CYBER DEFENSE & NATIONAL CYBER RESILIENCE
6.4.1
AI-DRIVEN THREAT DETECTION AND AUTOMATED INCIDENT RESPONSE
6.4.2
ZERO TRUST ARCHITECTURES ACROSS GOVERNMENT NETWORKS
6.4.3
DIGITAL IDENTITY AND FEDERATED IDENTITY MANAGEMENT
6.4.4
ADVANCED THREAT INTELLIGENCE AND CYBER RISK ANALYTICS
6.4.5
CYBERSECURITY FOR SMART CITIES
6.5
IMPACT OF AI/GEN AI ON GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET
6.5.1
BEST PRACTICES IN GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET
6.5.2
CASE STUDIES OF AI IMPLEMENTATION IN GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET
6.5.3
INTERCONNECTED ADJACENT ECOSYSTEM AND IMPACT ON MARKET PLAYERS
6.5.4
CLIENTS’ READINESS TO ADOPT GENERATIVE AI IN GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET
6.6
SUCCESS STORIES AND REAL-WORLD APPLICATIONS
6.6.1
ESTONIA GOVERNMENT: NATIONAL DIGITAL CYBER RESILIENCE FRAMEWORK
6.6.2
CYBERSECURITY & INFRASTRUCTURE SECURITY AGENCY (CISA): NATIONAL CYBER DEFENSE & THREAT INTELLIGENCE
7
REGULATORY LANDSCAPE
Navigate complex global regulations with insights into regional compliance and industry standards.
130
7.1
REGIONAL REGULATIONS AND COMPLIANCE
7.1.1
REGULATORY BODIES, GOVERNMENT AGENCIES, AND OTHER ORGANIZATIONS
8
CONSUMER LANDSCAPE & BUYER BEHAVIOR
Unlock revenue by addressing unmet needs and key buying criteria across stakeholder-influenced markets.
138
8.1
DECISION-MAKING PROCESS
8.2
BUYER STAKEHOLDERS AND BUYING EVALUATION CRITERIA
8.2.1
KEY STAKEHOLDERS IN BUYING PROCESS
8.3
ADOPTION BARRIERS & INTERNAL CHALLENGES
8.4
UNMET NEEDS IN VARIOUS END-USE INDUSTRIES
8.5.3
MARGIN OPPORTUNITIES IN KEY APPLICATIONS
9
GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY OFFERING
Market Size & Growth Rate Forecast Analysis to 2031 in USD Million | 22 Data Tables
148
9.1.1
OFFERING: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET DRIVERS
9.2.1
GROWING ADOPTION OF ADVANCED SECURITY TECHNOLOGIES TO PROTECT GOVERNMENT NETWORKS AND CRITICAL INFRASTRUCTURE
9.3.1
INCREASING RELIANCE ON SPECIALIZED SECURITY EXPERTISE TO PROTECT GOVERNMENT DIGITAL INFRASTRUCTURE
9.3.2
PROFESSIONAL SERVICES
9.3.2.1
INCREASING DEMAND FOR CONSULTING AND IMPLEMENTATION SUPPORT TO STRENGTHEN GOVERNMENT CYBERSECURITY FRAMEWORKS
9.3.2.2
DESIGN, CONSULTING, AND IMPLEMENTATION
9.3.2.3
RISK & THREAT MANAGEMENT
9.3.2.4
TRAINING & EDUCATION
9.3.2.5
SUPPORT & MAINTENANCE
9.3.3.1
INCREASING ADOPTION OF MANAGED SECURITY SERVICES TO STRENGTHEN GOVERNMENT CYBER DEFENSE
10
GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SOLUTION TYPE
Market Size & Growth Rate Forecast Analysis to 2031 in USD Million | 18 Data Tables
161
10.1.1
SOLUTION TYPE: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET DRIVERS
10.2
IDENTITY & ACCESS MANAGEMENT
10.2.1
GROWING NEED FOR SECURE DIGITAL IDENTITY MANAGEMENT IN GOVERNMENT SYSTEMS DRIVES MARKET
10.3
ANTIVIRUS/ANTIMALWARE
10.3.1
RISE IN THREAT OF MALWARE AND ENDPOINT ATTACKS ACROSS GOVERNMENT NETWORKS TO ACCELERATE MARKET
10.4
LOG MANAGEMENT & SIEM
10.4.1
RISING DEMAND FOR REAL-TIME THREAT MONITORING AND SECURITY ANALYTICS TO DRIVE MARKET
10.5.1
GROWING NEED FOR SECURE NETWORK PROTECTION ACROSS GOVERNMENT INFRASTRUCTURE TO BOOST MARKET GROWTH
10.6
DLP, ENCRYPTION, AND TOKENIZATION
10.6.1
INCREASING FOCUS ON PROTECTING SENSITIVE GOVERNMENT DATA AND PREVENTING DATA BREACHES DRIVES MARKET
10.7
COMPLIANCE & POLICY MANAGEMENT
10.7.1
EMPHASIS ON REGULATORY REQUIREMENTS AND SECURITY GOVERNANCE TO DRIVE MARKET
10.8.1
GROWING NEED FOR CONTINUOUS VULNERABILITY REMEDIATION AND SYSTEM UPDATES TO BOOST MARKET
10.9
OTHER SOLUTION TYPES
11
GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SECURITY TYPE
Market Size & Growth Rate Forecast Analysis to 2031 in USD Million | 10 Data Tables
173
11.1.1
SECURITY TYPE: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET DRIVERS
11.2.1
RISING NEED FOR ADVANCED PROTECTION ACROSS GOVERNMENT INFRASTRUCTURE DRIVES DEMAND
11.3
ENDPOINT & IOT SECURITY
11.3.1
GROWING ADOPTION TO PROTECT CONNECTED GOVERNMENT DEVICES PROPELS MARKET GROWTH
11.4.1
INCREASING MIGRATION OF GOVERNMENT WORKLOADS DRIVES DEMAND
11.5
APPLICATION SECURITY
11.5.1
RISING CYBER THREATS TARGETING GOVERNMENT APPLICATIONS DRIVE MARKET
12
GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY DEPLOYMENT MODE
Market Size & Growth Rate Forecast Analysis to 2031 in USD Million | 8 Data Tables
181
12.1.1
DEPLOYMENT MODE: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET DRIVERS
12.2.1
CONTINUED RELIANCE ON ON-PREMISES SECURITY INFRASTRUCTURE SUSTAINS MARKET DEMAND
12.3.1
MARKET DRIVEN BY GROWING ADOPTION OF CLOUD-BASED SECURITY SOLUTIONS ACROSS DIGITAL GOVERNMENT PLATFORMS
12.4.1
HYBRID SECURITY DEPLOYMENT MODELS ENABLE FLEXIBLE AND SECURE GOVERNMENT CYBERSECURITY ARCHITECTURES
13
GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY OWNERSHIP TYPE
Market Size & Growth Rate Forecast Analysis to 2031 in USD Million | 12 Data Tables
187
13.1.1
OWNERSHIP TYPE: GOVERNMENT AND PUBLIC SECTOR CYBERSECURITY MARKET DRIVERS
13.2
FEDERAL/NATIONAL GOVERNMENT
13.2.1
RISING NEED TO PROTECT NATIONAL DIGITAL INFRASTRUCTURE TO PROPEL SEGMENT GROWTH
13.3
STATE & LOCAL GOVERNMENT
13.3.1
INCREASING DIGITALIZATION OF REGIONAL GOVERNANCE TO BOOST ADOPTION
13.4
DEFENSE & INTELLIGENCE
13.4.1
PROTECTION OF NATIONAL SECURITY SYSTEMS AND CYBERSECURITY INVESTMENT TO DRIVE SEGMENT
13.5
PUBLIC SECTOR ENTERPRISES
13.5.1
EXPANDING DIGITAL OPERATIONS OF PUBLIC SECTOR ENTERPRISES TO DRIVE MARKET
13.6
PUBLIC SERVICE INSTITUTIONS
13.6.1
STRENGTHENING CYBER RESILIENCE FOR EMERGENCY RESPONSE SYSTEMS ACCELERATES ADOPTION
14
GOVERNMENT & PUBLIC SECTOR CYBERSECURITY, BY REGION
Comprehensive coverage of 8 Regions with country-level deep-dive of 17 Countries | 406 Data Tables.
195
14.2.1
NORTH AMERICA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET DRIVERS
14.2.2.1
RISING FEDERAL CYBERSECURITY INVESTMENTS AND NATIONAL SECURITY INITIATIVES DRIVE MARKET GROWTH
14.2.3.1
NATIONAL CYBERSECURITY STRATEGY AND RISING CYBER THREATS ACCELERATING MARKET GROWTH
14.3.1
EUROPE: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET DRIVERS
14.3.2.1
STRENGTHENING OF PUBLIC SECTOR CYBER RESILIENCE THROUGH NATIONAL CYBERSECURITY INITIATIVES TO BOOST GROWTH
14.3.3.1
INCREASING FOCUS ON CRITICAL INFRASTRUCTURE SECURITY AND GOVERNMENT CYBER DEFENSE TO GROW MARKET
14.3.4.1
MARKET DRIVEN BY GROWING INVESTMENTS IN GOVERNMENT CYBER PROTECTION AND CRITICAL INFRASTRUCTURE SECURITY
14.3.5.1
EXPANDING GOVERNMENT CYBER DEFENSE AND DIGITAL INFRASTRUCTURE SECURITY FUEL MARKET GROWTH
14.3.6.1
INCREASING FOCUS ON SOVEREIGN CYBERSECURITY AND PROTECTION OF GOVERNMENT NETWORKS TO DRIVE MARKET
14.4.1
ASIA PACIFIC: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET DRIVERS
14.4.2.1
CYBER SOVEREIGNTY POLICIES AND DATA SECURITY REGULATIONS DRIVE GOVERNMENT CYBERSECURITY INVESTMENTS
14.4.3.1
STRATEGIC CYBER DEFENSE FOR GOVERNMENT SYSTEMS AND SERVICES DRIVES MARKET GROWTH
14.4.4.1
DIGITAL GOVERNANCE EXPANSION AND NATIONAL CYBERSECURITY PROGRAMS TO PROPEL MARKET GROWTH
14.4.5.1
CYBERSECURITY STRATEGY 2030 ACCELERATING GOVERNMENT CYBER DEFENSE MODERNIZATION
14.4.6.1
ADVANCED CYBER GOVERNANCE FOR SECURE DIGITAL PUBLIC SERVICES TO BOOST MARKET
14.4.7
REST OF ASIA PACIFIC
14.5
MIDDLE EAST & AFRICA
14.5.1
MIDDLE EAST & AFRICA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET DRIVERS
14.5.1.1.1
STRONG NATIONAL CYBERSECURITY STRATEGIES ACCELERATING DEMAND FOR GOVERNMENT CYBERSECURITY SOLUTIONS
14.5.1.1.4
OTHER GCC COUNTRIES
14.5.1.2.1
ACCELERATING CYBERSECURITY ADOPTION IN GOVERNMENT SERVICES TO BOOST MARKET
14.5.1.3
REST OF MIDDLE EAST & AFRICA
14.6.1
LATIN AMERICA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET DRIVERS
14.6.2.1
DRIVING PUBLIC SECTOR CYBERSECURITY THROUGH NATIONAL DIGITAL TRANSFORMATION
14.6.3.1
STRENGTHENING GOVERNMENT CYBER RESILIENCE THROUGH ADVANCED DIGITAL SECURITY
14.6.4
REST OF LATIN AMERICA
15
COMPETITIVE LANDSCAPE
Discover which key players dominate market share and strategies through 2025.
344
15.2
KEY PLAYER STRATEGIES/RIGHT TO WIN, 2024-2026
15.3
REVENUE ANALYSIS, 2021-2025
15.4
MARKET SHARE ANALYSIS, 2025
15.5
PRODUCT/BRAND COMPARISON
15.5.3
BOOZ ALLEN HAMILTON
15.6
COMPANY VALUATION AND FINANCIAL METRICS
15.6.2
FINANCIAL METRICS USING EV/EBIDTA
15.7
COMPANY EVALUATION MATRIX: KEY PLAYERS, 2025
15.7.5
COMPANY FOOTPRINT: KEY PLAYERS
15.7.5.1
COMPANY FOOTPRINT
15.7.5.2
REGIONAL FOOTPRINT
15.7.5.3
OFFERING FOOTPRINT
15.7.5.4
DEPLOYMENT MODE FOOTPRINT
15.7.5.5
OWNERSHIP TYPE FOOTPRINT
15.8
COMPANY EVALUATION MATRIX: STARTUPS/SMES, 2025
15.8.1
PROGRESSIVE COMPANIES
15.8.2
RESPONSIVE COMPANIES
15.8.5
COMPETITIVE BENCHMARKING: STARTUPS/SMES, 2025
15.8.5.1
DETAILED LIST OF KEY STARTUPS/SMES
15.8.5.2
COMPETITIVE BENCHMARKING OF KEY STARTUPS/SMES
15.8.5.2.1
REGIONAL FOOTPRINT
15.8.5.2.2
OFFERING FOOTPRINT
15.8.5.2.3
DEPLOYMENT MODE FOOTPRINT
15.8.5.2.4
OWNERSHIP TYPE FOOTPRINT
15.9
COMPETITIVE SCENARIO AND TRENDS
15.9.1
PRODUCT LAUNCHES/ENHANCEMENTS
16
COMPANY PROFILES
In-depth Company Profiles of Leading Market Players with detailed Business Overview, Product and Service Portfolio, Recent Developments, and Unique Analyst Perspective (MnM View)
389
16.1.1.1
BUSINESS OVERVIEW
16.1.1.2
PRODUCTS/SOLUTIONS/SERVICES OFFERED
16.1.1.3
RECENT DEVELOPMENTS
16.1.1.3.1
PRODUCT LAUNCHES/ENHANCEMENTS
16.1.1.4.2
STRATEGIC CHOICES
16.1.1.4.3
WEAKNESSES AND COMPETITIVE THREATS
16.1.3
BOOZ ALLEN HAMILTON
16.1.7
PALO ALTO NETWORKS
17
RESEARCH METHODOLOGY
494
17.1.2.1
BREAKUP OF PRIMARY PROFILES
17.1.2.2
KEY INDUSTRY INSIGHTS
17.3
MARKET SIZE ESTIMATION
17.3.2
BOTTOM-UP APPROACH
17.5
RESEARCH ASSUMPTIONS
17.6
RESEARCH LIMITATIONS
18.2
KNOWLEDGESTORE: MARKETSANDMARKETS’ SUBSCRIPTION PORTAL
18.3
CUSTOMIZATION OPTIONS
TABLE 1
USD EXCHANGE RATES, 2020–2025
TABLE 2
UNMET NEEDS AND WHITE SPACES IN GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET
TABLE 3
STRATEGIC MOVES BY PLAYERS IN GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET
TABLE 4
CROSS-TIER STRATEGIC PATTERNS OF VENDORS
TABLE 5
PORTER’S FIVE FORCES’ IMPACT ON GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET
TABLE 6
GDP PERCENTAGE CHANGE, BY KEY COUNTRY, 2021–2030
TABLE 7
GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET: ECOSYSTEM
TABLE 8
AVERAGE SELLING PRICE OF KEY PLAYERS, BY SOLUTION TYPE, 2026
TABLE 9
INDICATIVE PRICING ANALYSIS OF KEY CYBERSECURITY VENDORS, 2024–2026
TABLE 10
IMPORT DATA FOR HS CODE 8517-COMPLIANT PRODUCTS, BY COUNTRY, 2021–2025 (USD MILLION)
TABLE 11
EXPORT DATA FOR HS CODE 8517-COMPLIANT PRODUCTS, BY COUNTRY, 2021–2025 (USD MILLION)
TABLE 12
GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET: KEY CONFERENCES & EVENTS, 2026
TABLE 13
KEY TARIFF RATES
TABLE 14
GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET: KEY PATENTS, 2024–2026
TABLE 15
TOP USE CASES AND MARKET POTENTIAL
TABLE 16
BEST PRACTICES: COMPANIES IMPLEMENTING USE CASES
TABLE 17
GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET: CASE STUDIES RELATED TO GEN AI IMPLEMENTATION
TABLE 18
INTERCONNECTED ADJACENT ECOSYSTEM AND IMPACT ON MARKET PLAYERS
TABLE 19
NORTH AMERICA: REGULATORY BODIES, GOVERNMENT AGENCIES, AND OTHER ORGANIZATIONS
TABLE 20
EUROPE: REGULATORY BODIES, GOVERNMENT AGENCIES, AND OTHER ORGANIZATIONS
TABLE 21
ASIA PACIFIC: REGULATORY BODIES, GOVERNMENT AGENCIES, AND OTHER ORGANIZATIONS
TABLE 22
MIDDLE EAST & AFRICA: REGULATORY BODIES, GOVERNMENT AGENCIES, AND OTHER ORGANIZATIONS
TABLE 23
LATIN AMERICA: REGULATORY BODIES, GOVERNMENT AGENCIES, AND OTHER ORGANIZATIONS
TABLE 24
GLOBAL INDUSTRY STANDARDS IN GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET
TABLE 25
INFLUENCE OF STAKEHOLDERS ON BUYING PROCESS FOR TOP THREE OWNERSHIP TYPES (%)
TABLE 26
KEY BUYING CRITERIA FOR TOP THREE OWNERSHIP TYPES
TABLE 27
UNMET NEEDS IN GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET BY END-USE INDUSTRY
TABLE 28
GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY OFFERING, 2020–2025 (USD MILLION)
TABLE 29
GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY OFFERING, 2026–2031 (USD MILLION)
TABLE 30
SOLUTIONS: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY REGION, 2020–2025 (USD MILLION)
TABLE 31
SOLUTIONS: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY REGION, 2026–2031 (USD MILLION)
TABLE 32
GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SERVICE, 2020–2025 (USD MILLION)
TABLE 33
GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SERVICE, 2026–2031 (USD MILLION)
TABLE 34
SERVICES: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY REGION, 2020–2025 (USD MILLION)
TABLE 35
SERVICES: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY REGION, 2026–2031 (USD MILLION)
TABLE 36
GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY PROFESSIONAL SERVICE, 2020–2025 (USD MILLION)
TABLE 37
GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY PROFESSIONAL SERVICE, 2026–2031 (USD MILLION)
TABLE 38
PROFESSIONAL SERVICES: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY REGION, 2020–2025 (USD MILLION)
TABLE 39
PROFESSIONAL SERVICES: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY REGION, 2026–2031 (USD MILLION)
TABLE 40
DESIGN, CONSULTING, AND IMPLEMENTATION: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY REGION, 2020–2025 (USD MILLION)
TABLE 41
DESIGN, CONSULTING, AND IMPLEMENTATION: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY REGION, 2026–2031 (USD MILLION)
TABLE 42
RISK & THREAT MANAGEMENT: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY REGION, 2020–2025 (USD MILLION)
TABLE 43
RISK & THREAT MANAGEMENT: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY REGION, 2026–2031(USD MILLION)
TABLE 44
TRAINING & EDUCATION: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY REGION, 2020–2025 (USD MILLION)
TABLE 45
TRAINING & EDUCATION: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY REGION, 2026–2031 (USD MILLION)
TABLE 46
SUPPORT & MAINTENANCE: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY REGION, 2020–2025 (USD MILLION)
TABLE 47
SUPPORT & MAINTENANCE: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY REGION, 2026–2031 (USD MILLION)
TABLE 48
MANAGED SERVICES: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY REGION, 2020–2025 (USD MILLION)
TABLE 49
MANAGED SERVICES: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY REGION, 2026–2031 (USD MILLION)
TABLE 50
GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SOLUTION TYPE, 2020–2025 (USD MILLION)
TABLE 51
GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SOLUTION TYPE, 2026–2031 (USD MILLION)
TABLE 52
IDENTITY & ACCESS MANAGEMENT: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY REGION, 2020–2025 (USD MILLION)
TABLE 53
IDENTITY & ACCESS MANAGEMENT: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY REGION, 2026–2031 (USD MILLION)
TABLE 54
ANTIVIRUS/ANTIMALWARE SOLUTIONS: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY REGION, 2020–2025 (USD MILLION)
TABLE 55
ANTIVIRUS/ANTIMALWARE SOLUTIONS: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY REGION, 2026–2031 (USD MILLION)
TABLE 56
LOG MANAGEMENT & SIEM SOLUTIONS: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY REGION, 2020–2025 (USD MILLION)
TABLE 57
LOG MANAGEMENT & SIEM SOLUTIONS: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY REGION, 2026–2031 (USD MILLION)
TABLE 58
FIREWALL & VPN SOLUTIONS: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY REGION, 2020–2025 (USD MILLION)
TABLE 59
FIREWALL & VPN SOLUTIONS: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY REGION, 2026–2031 (USD MILLION)
TABLE 60
DLP, ENCRYPTION, AND TOKENIZATION SOLUTIONS: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY REGION, 2020–2025 (USD MILLION)
TABLE 61
DLP, ENCRYPTION, AND TOKENIZATION SOLUTIONS: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY REGION, 2026–2031 (USD MILLION)
TABLE 62
COMPLIANCE & POLICY MANAGEMENT: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY REGION, 2020–2025 (USD MILLION)
TABLE 63
COMPLIANCE & POLICY MANAGEMENT: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY REGION, 2026–2031 (USD MILLION)
TABLE 64
PATCH MANAGEMENT: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY REGION, 2020–2025 (USD MILLION)
TABLE 65
PATCH MANAGEMENT: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY REGION, 2026–2031 (USD MILLION)
TABLE 66
OTHER SOLUTION TYPES: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY REGION, 2020–2025 (USD MILLION)
TABLE 67
OTHER SOLUTION TYPES: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY REGION, 2026–2031 (USD MILLION)
TABLE 68
GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SECURITY TYPE, 2020–2025 (USD MILLION)
TABLE 69
GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SECURITY TYPE, 2026–2031 (USD MILLION)
TABLE 70
NETWORK SECURITY: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY REGION, 2020–2025 (USD MILLION)
TABLE 71
NETWORK SECURITY: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY REGION, 2026–2031 (USD MILLION)
TABLE 72
ENDPOINT & IOT SECURITY: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY REGION, 2020–2025 (USD MILLION)
TABLE 73
ENDPOINT & IOT SECURITY: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY REGION, 2026–2031 (USD MILLION)
TABLE 74
CLOUD SECURITY: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY REGION, 2020–2025 (USD MILLION)
TABLE 75
CLOUD SECURITY: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY REGION, 2026–2031 (USD MILLION)
TABLE 76
APPLICATION SECURITY: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY REGION, 2020–2025 (USD MILLION)
TABLE 77
APPLICATION SECURITY: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY REGION, 2026–2031 (USD MILLION)
TABLE 78
GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY DEPLOYMENT MODE, 2020–2025 (USD MILLION)
TABLE 79
GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY DEPLOYMENT MODE, 2026–2031 (USD MILLION)
TABLE 80
ON-PREMISES: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY REGION, 2020–2025 (USD MILLION)
TABLE 81
ON-PREMISES: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY REGION, 2026–2031 (USD MILLION)
TABLE 82
CLOUD: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY REGION, 2020–2025 (USD MILLION)
TABLE 83
CLOUD: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY REGION, 2026–2031 (USD MILLION)
TABLE 84
HYBRID: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY REGION, 2020–2025 (USD MILLION)
TABLE 85
HYBRID: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY REGION, 2026–2031 (USD MILLION)
TABLE 86
GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY OWNERSHIP TYPE, 2020–2025 (USD MILLION)
TABLE 87
GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY OWNERSHIP TYPE, 2026–2031 (USD MILLION)
TABLE 88
FEDERAL/NATIONAL GOVERNMENT: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY REGION, 2020–2025 (USD MILLION)
TABLE 89
FEDERAL/NATIONAL GOVERNMENT: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY REGION, 2026–2031 (USD MILLION)
TABLE 90
STATE & LOCAL GOVERNMENT: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY REGION, 2020–2025 (USD MILLION)
TABLE 91
STATE & LOCAL GOVERNMENT: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY REGION, 2026–2031 (USD MILLION)
TABLE 92
DEFENSE & INTELLIGENCE: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY REGION, 2020–2025 (USD MILLION)
TABLE 93
DEFENSE & INTELLIGENCE: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, 2026–2031 (USD MILLION)
TABLE 94
PUBLIC SECTOR ENTERPRISES: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY REGION, 2020–2025 (USD MILLION)
TABLE 95
PUBLIC SECTOR ENTERPRISES: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY REGION, 2026–2031 (USD MILLION)
TABLE 96
PUBLIC SERVICE INSTITUTIONS: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY REGION, 2020–2025 (USD MILLION)
TABLE 97
PUBLIC SERVICE INSTITUTIONS: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY REGION, 2026–2031 (USD MILLION)
TABLE 98
GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY REGION, 2020–2025 (USD MILLION)
TABLE 99
GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY REGION, 2026–2031 (USD MILLION)
TABLE 100
NORTH AMERICA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY OFFERING, 2020–2025 (USD MILLION)
TABLE 101
NORTH AMERICA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY OFFERING, 2026–2031 (USD MILLION)
TABLE 102
NORTH AMERICA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SERVICE, 2020–2025 (USD MILLION)
TABLE 103
NORTH AMERICA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SERVICE, 2026–2031 (USD MILLION)
TABLE 104
NORTH AMERICA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY PROFESSIONAL SERVICE, 2020–2025 (USD MILLION)
TABLE 105
NORTH AMERICA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY PROFESSIONAL SERVICE, 2026–2031 (USD MILLION)
TABLE 106
NORTH AMERICA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SOLUTION TYPE, 2020–2025 (USD MILLION)
TABLE 107
NORTH AMERICA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SOLUTION TYPE, 2026–2031 (USD MILLION)
TABLE 108
NORTH AMERICA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SECURITY TYPE, 2020–2025 (USD MILLION)
TABLE 109
NORTH AMERICA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SECURITY TYPE, 2026–2031 (USD MILLION)
TABLE 110
NORTH AMERICA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY DEPLOYMENT MODE, 2020–2025 (USD MILLION)
TABLE 111
NORTH AMERICA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY DEPLOYMENT MODE, 2026–2031 (USD MILLION)
TABLE 112
NORTH AMERICA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY OWNERSHIP TYPE, 2020–2025 (USD MILLION)
TABLE 113
NORTH AMERICA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY OWNERSHIP TYPE, 2026–2031 (USD MILLION)
TABLE 114
NORTH AMERICA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY COUNTRY, 2020–2025 (USD MILLION)
TABLE 115
NORTH AMERICA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY COUNTRY, 2026–2031 (USD MILLION)
TABLE 116
US: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY OFFERING, 2020–2025 (USD MILLION)
TABLE 117
US: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY OFFERING, 2026–2031 (USD MILLION)
TABLE 118
US: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SERVICE, 2020–2025 (USD MILLION)
TABLE 119
US: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SERVICE, 2026–2031 (USD MILLION)
TABLE 120
US: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY PROFESSIONAL SERVICE, 2020–2025 (USD MILLION)
TABLE 121
US: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY PROFESSIONAL SERVICE, 2026–2031 (USD MILLION)
TABLE 122
US: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SOLUTION TYPE, 2020–2025 (USD MILLION)
TABLE 123
US: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SOLUTION TYPE, 2026–2031 (USD MILLION)
TABLE 124
US: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SECURITY TYPE, 2020–2025 (USD MILLION)
TABLE 125
US: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SECURITY TYPE, 2026–2031 (USD MILLION)
TABLE 126
US: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY DEPLOYMENT MODE, 2020–2025 (USD MILLION)
TABLE 127
US: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY DEPLOYMENT MODE, 2026–2031 (USD MILLION)
TABLE 128
US: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY OWNERSHIP TYPE, 2020–2025 (USD MILLION)
TABLE 129
US: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY OWNERSHIP TYPE, 2026–2031 (USD MILLION)
TABLE 130
CANADA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY OFFERING, 2020–2025 (USD MILLION)
TABLE 131
CANADA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY OFFERING, 2026–2031 (USD MILLION)
TABLE 132
CANADA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SERVICE, 2020–2025 (USD MILLION)
TABLE 133
CANADA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SERVICE, 2026–2031 (USD MILLION)
TABLE 134
CANADA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY PROFESSIONAL SERVICE, 2020–2025 (USD MILLION)
TABLE 135
CANADA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY PROFESSIONAL SERVICE, 2026–2031 (USD MILLION)
TABLE 136
CANADA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SOLUTION TYPE, 2020–2025 (USD MILLION)
TABLE 137
CANADA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SOLUTION TYPE, 2026–2031 (USD MILLION)
TABLE 138
CANADA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SECURITY TYPE, 2020–2025 (USD MILLION)
TABLE 139
CANADA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SECURITY TYPE, 2026–2031 (USD MILLION)
TABLE 140
CANADA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY DEPLOYMENT MODE, 2020–2025 (USD MILLION)
TABLE 141
CANADA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY DEPLOYMENT MODE, 2026–2031 (USD MILLION)
TABLE 142
CANADA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY OWNERSHIP TYPE, 2020–2025 (USD MILLION)
TABLE 143
CANADA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY OWNERSHIP TYPE, 2026–2031 (USD MILLION)
TABLE 144
EUROPE: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY OFFERING, 2020–2025 (USD MILLION)
TABLE 145
EUROPE: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY OFFERING, 2026–2031 (USD MILLION)
TABLE 146
EUROPE: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SERVICE, 2020–2025 (USD MILLION)
TABLE 147
EUROPE: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SERVICE, 2026–2031 (USD MILLION)
TABLE 148
EUROPE: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY PROFESSIONAL SERVICE, 2020–2025 (USD MILLION)
TABLE 149
EUROPE: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY PROFESSIONAL SERVICE, 2026–2031 (USD MILLION)
TABLE 150
EUROPE: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SOLUTION TYPE, 2020–2025 (USD MILLION)
TABLE 151
EUROPE: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SOLUTION TYPE, 2026–2031 (USD MILLION)
TABLE 152
EUROPE: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SECURITY TYPE, 2020–2025 (USD MILLION)
TABLE 153
EUROPE: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SECURITY TYPE, 2026–2031 (USD MILLION)
TABLE 154
EUROPE: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY DEPLOYMENT MODE, 2020–2025 (USD MILLION)
TABLE 155
EUROPE: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY DEPLOYMENT MODE, 2026–2031 (USD MILLION)
TABLE 156
EUROPE: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY OWNERSHIP TYPE, 2020–2025 (USD MILLION)
TABLE 157
EUROPE: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY OWNERSHIP TYPE, 2026–2031 (USD MILLION)
TABLE 158
EUROPE: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY COUNTRY, 2020–2025 (USD MILLION)
TABLE 159
EUROPE: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY COUNTRY, 2026–2031 (USD MILLION)
TABLE 160
UK: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY OFFERING, 2020–2025 (USD MILLION)
TABLE 161
UK: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY OFFERING, 2026–2031 (USD MILLION)
TABLE 162
UK: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SERVICE, 2020–2025 (USD MILLION)
TABLE 163
UK: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SERVICE, 2026–2031 (USD MILLION)
TABLE 164
UK: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY PROFESSIONAL SERVICE, 2020–2025 (USD MILLION)
TABLE 165
UK: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY PROFESSIONAL SERVICE, 2026–2031 (USD MILLION)
TABLE 166
UK: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SOLUTION TYPE, 2020–2025 (USD MILLION)
TABLE 167
UK: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SOLUTION TYPE, 2026–2031 (USD MILLION)
TABLE 168
UK: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SECURITY TYPE, 2020–2025 (USD MILLION)
TABLE 169
UK: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SECURITY TYPE, 2026–2031 (USD MILLION)
TABLE 170
UK: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY DEPLOYMENT MODE, 2020–2025 (USD MILLION)
TABLE 171
UK: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY DEPLOYMENT MODE, 2026–2031 (USD MILLION)
TABLE 172
UK: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY OWNERSHIP TYPE, 2020–2025 (USD MILLION)
TABLE 173
UK: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY OWNERSHIP TYPE, 2026–2031 (USD MILLION)
TABLE 174
GERMANY: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY OFFERING, 2020–2025 (USD MILLION)
TABLE 175
GERMANY: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY OFFERING, 2026–2031 (USD MILLION)
TABLE 176
GERMANY: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SERVICE, 2020–2025 (USD MILLION)
TABLE 177
GERMANY: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SERVICE, 2026–2031 (USD MILLION)
TABLE 178
GERMANY: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY PROFESSIONAL SERVICE, 2020–2025 (USD MILLION)
TABLE 179
GERMANY: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY PROFESSIONAL SERVICE, 2026–2031 (USD MILLION)
TABLE 180
GERMANY: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SOLUTION TYPE, 2020–2025 (USD MILLION)
TABLE 181
GERMANY: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SOLUTION TYPE, 2026–2031 (USD MILLION)
TABLE 182
GERMANY: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SECURITY TYPE, 2020–2025 (USD MILLION)
TABLE 183
GERMANY: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SECURITY TYPE, 2026–2031 (USD MILLION)
TABLE 184
GERMANY: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY DEPLOYMENT MODE, 2020–2025 (USD MILLION)
TABLE 185
GERMANY: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY DEPLOYMENT MODE, 2026–2031 (USD MILLION)
TABLE 186
GERMANY: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY OWNERSHIP TYPE, 2020–2025 (USD MILLION)
TABLE 187
GERMANY: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY OWNERSHIP TYPE, 2026–2031 (USD MILLION)
TABLE 188
FRANCE: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY OFFERING, 2020–2025 (USD MILLION)
TABLE 189
FRANCE: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY OFFERING, 2026–2031 (USD MILLION)
TABLE 190
FRANCE: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SERVICE, 2020–2025 (USD MILLION)
TABLE 191
FRANCE: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SERVICE, 2026–2031 (USD MILLION)
TABLE 192
FRANCE: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY PROFESSIONAL SERVICE, 2020–2025 (USD MILLION)
TABLE 193
FRANCE: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY PROFESSIONAL SERVICE, 2026–2031 (USD MILLION)
TABLE 194
FRANCE: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SOLUTION TYPE, 2020–2025 (USD MILLION)
TABLE 195
FRANCE: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SOLUTION TYPE, 2026–2031 (USD MILLION)
TABLE 196
FRANCE: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SECURITY TYPE, 2020–2025 (USD MILLION)
TABLE 197
FRANCE: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SECURITY TYPE, 2026–2031 (USD MILLION)
TABLE 198
FRANCE: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY DEPLOYMENT MODE, 2020–2025 (USD MILLION)
TABLE 199
FRANCE: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY DEPLOYMENT MODE, 2026–2031 (USD MILLION)
TABLE 200
FRANCE: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY OWNERSHIP TYPE, 2020–2025 (USD MILLION)
TABLE 201
FRANCE: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY OWNERSHIP TYPE, 2026–2031 (USD MILLION)
TABLE 202
ITALY: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY OFFERING, 2020–2025 (USD MILLION)
TABLE 203
ITALY: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY OFFERING, 2026–2031 (USD MILLION)
TABLE 204
ITALY: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SERVICE, 2020–2025 (USD MILLION)
TABLE 205
ITALY: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SERVICE, 2026–2031 (USD MILLION)
TABLE 206
ITALY: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY PROFESSIONAL SERVICE, 2020–2025 (USD MILLION)
TABLE 207
ITALY: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY PROFESSIONAL SERVICE, 2026–2031 (USD MILLION)
TABLE 208
ITALY: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SOLUTION TYPE, 2020–2025 (USD MILLION)
TABLE 209
ITALY: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SOLUTION TYPE, 2026–2031 (USD MILLION)
TABLE 210
ITALY: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SECURITY TYPE, 2020–2025 (USD MILLION)
TABLE 211
ITALY: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SECURITY TYPE, 2026–2031 (USD MILLION)
TABLE 212
ITALY: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY DEPLOYMENT MODE, 2020–2025 (USD MILLION)
TABLE 213
ITALY: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY DEPLOYMENT MODE, 2026–2031 (USD MILLION)
TABLE 214
ITALY: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY OWNERSHIP TYPE, 2020–2025 (USD MILLION)
TABLE 215
ITALY: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY OWNERSHIP TYPE, 2026–2031 (USD MILLION)
TABLE 216
RUSSIA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY OFFERING, 2020–2025 (USD MILLION)
TABLE 217
RUSSIA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY OFFERING, 2026–2031 (USD MILLION)
TABLE 218
RUSSIA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SERVICE, 2020–2025 (USD MILLION)
TABLE 219
RUSSIA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SERVICE, 2026–2031 (USD MILLION)
TABLE 220
RUSSIA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY PROFESSIONAL SERVICE, 2020–2025 (USD MILLION)
TABLE 221
RUSSIA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY PROFESSIONAL SERVICE, 2026–2031 (USD MILLION)
TABLE 222
RUSSIA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SOLUTION TYPE, 2020–2025 (USD MILLION)
TABLE 223
RUSSIA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SOLUTION TYPE, 2026–2031 (USD MILLION)
TABLE 224
RUSSIA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SECURITY TYPE, 2020–2025 (USD MILLION)
TABLE 225
RUSSIA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SECURITY TYPE, 2026–2031 (USD MILLION)
TABLE 226
RUSSIA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY DEPLOYMENT MODE, 2020–2025 (USD MILLION)
TABLE 227
RUSSIA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY DEPLOYMENT MODE, 2026–2031 (USD MILLION)
TABLE 228
RUSSIA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY OWNERSHIP TYPE, 2020–2025 (USD MILLION)
TABLE 229
RUSSIA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY OWNERSHIP TYPE, 2026–2031 (USD MILLION)
TABLE 230
REST OF EUROPE: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY OFFERING, 2020–2025 (USD MILLION)
TABLE 231
REST OF EUROPE: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY OFFERING, 2026–2031 (USD MILLION)
TABLE 232
REST OF EUROPE: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SERVICE, 2020–2025 (USD MILLION)
TABLE 233
REST OF EUROPE: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SERVICE, 2026–2031 (USD MILLION)
TABLE 234
REST OF EUROPE: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY PROFESSIONAL SERVICE, 2020–2025 (USD MILLION)
TABLE 235
REST OF EUROPE: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY PROFESSIONAL SERVICE, 2026–2031 (USD MILLION)
TABLE 236
REST OF EUROPE: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SOLUTION TYPE, 2020–2025 (USD MILLION)
TABLE 237
REST OF EUROPE: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SOLUTION TYPE, 2026–2031 (USD MILLION)
TABLE 238
REST OF EUROPE: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SECURITY TYPE, 2020–2025 (USD MILLION)
TABLE 239
REST OF EUROPE: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SECURITY TYPE, 2026–2031 (USD MILLION)
TABLE 240
REST OF EUROPE: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY DEPLOYMENT MODE, 2020–2025 (USD MILLION)
TABLE 241
REST OF EUROPE: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY DEPLOYMENT MODE, 2026–2031 (USD MILLION)
TABLE 242
REST OF EUROPE: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY OWNERSHIP TYPE, 2020–2025 (USD MILLION)
TABLE 243
REST OF EUROPE: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY OWNERSHIP TYPE, 2026–2031 (USD MILLION)
TABLE 244
ASIA PACIFIC: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY OFFERING, 2020–2025 (USD MILLION)
TABLE 245
ASIA PACIFIC: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY OFFERING, 2026–2031 (USD MILLION)
TABLE 246
ASIA PACIFIC: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SERVICE, 2020–2025 (USD MILLION)
TABLE 247
ASIA PACIFIC: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SERVICE, 2026–2031 (USD MILLION)
TABLE 248
ASIA PACIFIC: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY PROFESSIONAL SERVICE, 2020–2025 (USD MILLION)
TABLE 249
ASIA PACIFIC: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY PROFESSIONAL SERVICE, 2026–2031 (USD MILLION)
TABLE 250
ASIA PACIFIC: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SOLUTION TYPE, 2020–2025 (USD MILLION)
TABLE 251
ASIA PACIFIC: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SOLUTION TYPE, 2026–2031 (USD MILLION)
TABLE 252
ASIA PACIFIC: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SECURITY TYPE, 2020–2025 (USD MILLION)
TABLE 253
ASIA PACIFIC: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SECURITY TYPE, 2026–2031 (USD MILLION)
TABLE 254
ASIA PACIFIC: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY DEPLOYMENT MODE, 2020–2025 (USD MILLION)
TABLE 255
ASIA PACIFIC: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY DEPLOYMENT MODE, 2026–2031 (USD MILLION)
TABLE 256
ASIA PACIFIC: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY OWNERSHIP TYPE, 2020–2025 (USD MILLION)
TABLE 257
ASIA PACIFIC: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY OWNERSHIP TYPE, 2026–2031 (USD MILLION)
TABLE 258
ASIA PACIFIC: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY COUNTRY, 2020–2025 (USD MILLION)
TABLE 259
ASIA PACIFIC: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY COUNTRY, 2026–2031 (USD MILLION)
TABLE 260
CHINA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY OFFERING, 2020–2025 (USD MILLION)
TABLE 261
CHINA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY OFFERING, 2026–2031 (USD MILLION)
TABLE 262
CHINA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SERVICE, 2020–2025 (USD MILLION)
TABLE 263
CHINA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SERVICE, 2026–2031 (USD MILLION)
TABLE 264
CHINA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY PROFESSIONAL SERVICE, 2020–2025 (USD MILLION)
TABLE 265
CHINA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY PROFESSIONAL SERVICE, 2026–2031 (USD MILLION)
TABLE 266
CHINA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SOLUTION TYPE, 2020–2025 (USD MILLION)
TABLE 267
CHINA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SOLUTION TYPE, 2026–2031 (USD MILLION)
TABLE 268
CHINA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SECURITY TYPE, 2020–2025 (USD MILLION)
TABLE 269
CHINA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SECURITY TYPE, 2026–2031 (USD MILLION)
TABLE 270
CHINA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY DEPLOYMENT MODE, 2020–2025 (USD MILLION)
TABLE 271
CHINA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY DEPLOYMENT MODE, 2026–2031 (USD MILLION)
TABLE 272
CHINA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY OWNERSHIP TYPE, 2020–2025 (USD MILLION)
TABLE 273
CHINA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY OWNERSHIP TYPE, 2026–2031 (USD MILLION)
TABLE 274
JAPAN: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY OFFERING, 2020–2025 (USD MILLION)
TABLE 275
JAPAN: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY OFFERING, 2026–2031 (USD MILLION)
TABLE 276
JAPAN: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SERVICE, 2020–2025 (USD MILLION)
TABLE 277
JAPAN: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SERVICE, 2026–2031 (USD MILLION)
TABLE 278
JAPAN: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY PROFESSIONAL SERVICE, 2020–2025 (USD MILLION)
TABLE 279
JAPAN: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY PROFESSIONAL SERVICE, 2026–2031 (USD MILLION)
TABLE 280
JAPAN: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SOLUTION TYPE, 2020–2025 (USD MILLION)
TABLE 281
JAPAN: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SOLUTION TYPE, 2026–2031 (USD MILLION)
TABLE 282
JAPAN: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SECURITY TYPE, 2020–2025 (USD MILLION)
TABLE 283
JAPAN: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SECURITY TYPE, 2026–2031 (USD MILLION)
TABLE 284
JAPAN: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY DEPLOYMENT MODE, 2020–2025 (USD MILLION)
TABLE 285
JAPAN: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY DEPLOYMENT MODE, 2026–2031 (USD MILLION)
TABLE 286
JAPAN: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY OWNERSHIP TYPE, 2020–2025 (USD MILLION)
TABLE 287
JAPAN: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY OWNERSHIP TYPE, 2026–2031 (USD MILLION)
TABLE 288
INDIA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY OFFERING, 2020–2025 (USD MILLION)
TABLE 289
INDIA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY OFFERING, 2026–2031 (USD MILLION)
TABLE 290
INDIA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SERVICE, 2020–2025 (USD MILLION)
TABLE 291
INDIA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SERVICE, 2026–2031 (USD MILLION)
TABLE 292
INDIA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY PROFESSIONAL SERVICE, 2020–2025 (USD MILLION)
TABLE 293
INDIA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY PROFESSIONAL SERVICE, 2026–2031 (USD MILLION)
TABLE 294
INDIA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SOLUTION TYPE, 2020–2025 (USD MILLION)
TABLE 295
INDIA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SOLUTION TYPE, 2026–2031 (USD MILLION)
TABLE 296
INDIA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SECURITY TYPE, 2020–2025 (USD MILLION)
TABLE 297
INDIA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SECURITY TYPE, 2026–2031 (USD MILLION)
TABLE 298
INDIA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY DEPLOYMENT MODE, 2020–2025 (USD MILLION)
TABLE 299
INDIA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY DEPLOYMENT MODE, 2026–2031 (USD MILLION)
TABLE 300
INDIA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY OWNERSHIP TYPE, 2020–2025 (USD MILLION)
TABLE 301
INDIA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY OWNERSHIP TYPE, 2026–2031 (USD MILLION)
TABLE 302
AUSTRALIA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY OFFERING, 2020–2025 (USD MILLION)
TABLE 303
AUSTRALIA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY OFFERING, 2026–2031 (USD MILLION)
TABLE 304
AUSTRALIA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SERVICE, 2020–2025 (USD MILLION)
TABLE 305
AUSTRALIA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SERVICE, 2026–2031 (USD MILLION)
TABLE 306
AUSTRALIA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY PROFESSIONAL SERVICE, 2020–2025 (USD MILLION)
TABLE 307
AUSTRALIA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY PROFESSIONAL SERVICE, 2026–2031 (USD MILLION)
TABLE 308
AUSTRALIA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SOLUTION TYPE, 2020–2025 (USD MILLION)
TABLE 309
AUSTRALIA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SOLUTION TYPE, 2026–2031 (USD MILLION)
TABLE 310
AUSTRALIA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SECURITY TYPE, 2020–2025 (USD MILLION)
TABLE 311
AUSTRALIA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SECURITY TYPE, 2026–2031 (USD MILLION)
TABLE 312
AUSTRALIA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY DEPLOYMENT MODE, 2020–2025 (USD MILLION)
TABLE 313
AUSTRALIA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY DEPLOYMENT MODE, 2026–2031 (USD MILLION)
TABLE 314
AUSTRALIA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY OWNERSHIP TYPE, 2020–2025 (USD MILLION)
TABLE 315
AUSTRALIA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY OWNERSHIP TYPE, 2026–2031 (USD MILLION)
TABLE 316
SINGAPORE: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY OFFERING, 2020–2025 (USD MILLION)
TABLE 317
SINGAPORE: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY OFFERING, 2026–2031 (USD MILLION)
TABLE 318
SINGAPORE: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SERVICE, 2020–2025 (USD MILLION)
TABLE 319
SINGAPORE: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SERVICE, 2026–2031 (USD MILLION)
TABLE 320
SINGAPORE: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY PROFESSIONAL SERVICE, 2020–2025 (USD MILLION)
TABLE 321
SINGAPORE: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY PROFESSIONAL SERVICE, 2026–2031 (USD MILLION)
TABLE 322
SINGAPORE: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SOLUTION TYPE, 2020–2025 (USD MILLION)
TABLE 323
SINGAPORE: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SOLUTION TYPE, 2026–2031 (USD MILLION)
TABLE 324
SINGAPORE: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SECURITY TYPE, 2020–2025 (USD MILLION)
TABLE 325
SINGAPORE: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SECURITY TYPE, 2026–2031 (USD MILLION)
TABLE 326
SINGAPORE: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY DEPLOYMENT MODE, 2020–2025 (USD MILLION)
TABLE 327
SINGAPORE: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY DEPLOYMENT MODE, 2026–2031 (USD MILLION)
TABLE 328
SINGAPORE: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY OWNERSHIP TYPE, 2020–2025 (USD MILLION)
TABLE 329
SINGAPORE: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY OWNERSHIP TYPE, 2026–2031 (USD MILLION)
TABLE 330
REST OF ASIA PACIFIC: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY OFFERING, 2020–2025 (USD MILLION)
TABLE 331
REST OF ASIA PACIFIC: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY OFFERING, 2026–2031 (USD MILLION)
TABLE 332
REST OF ASIA PACIFIC: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SERVICE, 2020–2025 (USD MILLION)
TABLE 333
REST OF ASIA PACIFIC: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SERVICE, 2026–2031 (USD MILLION)
TABLE 334
REST OF ASIA PACIFIC: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY PROFESSIONAL SERVICE, 2020–2025 (USD MILLION)
TABLE 335
REST OF ASIA PACIFIC: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY PROFESSIONAL SERVICE, 2026–2031 (USD MILLION)
TABLE 336
REST OF ASIA PACIFIC: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SOLUTION TYPE, 2020–2025 (USD MILLION)
TABLE 337
REST OF ASIA PACIFIC: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SOLUTION TYPE, 2026–2031 (USD MILLION)
TABLE 338
REST OF ASIA PACIFIC: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SECURITY TYPE, 2020–2025 (USD MILLION)
TABLE 339
REST OF ASIA PACIFIC: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SECURITY TYPE, 2026–2031 (USD MILLION)
TABLE 340
REST OF ASIA PACIFIC: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY DEPLOYMENT MODE, 2020–2025 (USD MILLION)
TABLE 341
REST OF ASIA PACIFIC: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY DEPLOYMENT MODE, 2026–2031 (USD MILLION)
TABLE 342
REST OF ASIA PACIFIC: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY OWNERSHIP TYPE, 2020–2025 (USD MILLION)
TABLE 343
REST OF ASIA PACIFIC: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY OWNERSHIP TYPE, 2026–2031 (USD MILLION)
TABLE 344
MIDDLE EAST & AFRICA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY OFFERING, 2020–2025 (USD MILLION)
TABLE 345
MIDDLE EAST & AFRICA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY OFFERING, 2026–2031 (USD MILLION)
TABLE 346
MIDDLE EAST & AFRICA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SERVICE, 2020–2025 (USD MILLION)
TABLE 347
MIDDLE EAST & AFRICA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SERVICE, 2026–2031 (USD MILLION)
TABLE 348
MIDDLE EAST & AFRICA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY PROFESSIONAL SERVICE, 2020–2025 (USD MILLION)
TABLE 349
MIDDLE EAST & AFRICA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY PROFESSIONAL SERVICE, 2026–2031 (USD MILLION)
TABLE 350
MIDDLE EAST & AFRICA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SOLUTION TYPE, 2020–2025 (USD MILLION)
TABLE 351
MIDDLE EAST & AFRICA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SOLUTION TYPE, 2026–2031 (USD MILLION)
TABLE 352
MIDDLE EAST & AFRICA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SECURITY TYPE, 2020–2025 (USD MILLION)
TABLE 353
MIDDLE EAST & AFRICA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SECURITY TYPE, 2026–2031 (USD MILLION)
TABLE 354
MIDDLE EAST & AFRICA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY DEPLOYMENT MODE, 2020–2025 (USD MILLION)
TABLE 355
MIDDLE EAST & AFRICA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY DEPLOYMENT MODE, 2026–2031 (USD MILLION)
TABLE 356
MIDDLE EAST & AFRICA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY OWNERSHIP TYPE, 2020–2025 (USD MILLION)
TABLE 357
MIDDLE EAST & AFRICA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY OWNERSHIP TYPE, 2026–2031 (USD MILLION)
TABLE 358
MIDDLE EAST & AFRICA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY COUNTRY, 2020–2025 (USD MILLION)
TABLE 359
MIDDLE EAST & AFRICA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY COUNTRY, 2026–2031 (USD MILLION)
TABLE 360
GCC COUNTRIES: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY OFFERING, 2020–2025 (USD MILLION)
TABLE 361
GCC COUNTRIES: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY OFFERING, 2026–2031 (USD MILLION)
TABLE 362
GCC COUNTRIES : GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SERVICE, 2020–2025 (USD MILLION)
TABLE 363
GCC COUNTRIES: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SERVICE, 2026–2031 (USD MILLION)
TABLE 364
GCC COUNTRIES: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY PROFESSIONAL SERVICE, 2020–2025 (USD MILLION)
TABLE 365
GCC COUNTRIES: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY PROFESSIONAL SERVICE, 2026–2031 (USD MILLION)
TABLE 366
GCC COUNTRIES: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SOLUTION TYPE, 2020–2025 (USD MILLION)
TABLE 367
GCC COUNTRIES: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SOLUTION TYPE, 2026–2031 (USD MILLION)
TABLE 368
GCC COUNTRIES: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SECURITY TYPE, 2020–2025 (USD MILLION)
TABLE 369
GCC COUNTRIES: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SECURITY TYPE, 2026–2031 (USD MILLION)
TABLE 370
GCC COUNTRIES: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY DEPLOYMENT MODE, 2020–2025 (USD MILLION)
TABLE 371
GCC COUNTRIES: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY DEPLOYMENT MODE, 2026–2031 (USD MILLION)
TABLE 372
GCC COUNTRIES: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY OWNERSHIP TYPE, 2020–2025 (USD MILLION)
TABLE 373
GCC COUNTRIES: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY OWNERSHIP TYPE, 2026–2031 (USD MILLION)
TABLE 374
GCC COUNTRIES: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY COUNTRY, 2020–2025 (USD MILLION)
TABLE 375
GCC COUNTRIES: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY COUNTRY, 2026–2031 (USD MILLION)
TABLE 376
KSA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY OFFERING, 2020–2025 (USD MILLION)
TABLE 377
KSA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY OFFERING, 2026–2031 (USD MILLION)
TABLE 378
KSA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SERVICE, 2020–2025 (USD MILLION)
TABLE 379
KSA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SERVICE, 2026–2031 (USD MILLION)
TABLE 380
KSA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY PROFESSIONAL SERVICE, 2020–2025 (USD MILLION)
TABLE 381
KSA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY PROFESSIONAL SERVICE, 2026–2031 (USD MILLION)
TABLE 382
KSA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SOLUTION TYPE, 2020–2025 (USD MILLION)
TABLE 383
KSA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SOLUTION TYPE, 2026–2031 (USD MILLION)
TABLE 384
KSA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SECURITY TYPE, 2020–2025 (USD MILLION)
TABLE 385
KSA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SECURITY TYPE, 2026–2031 (USD MILLION)
TABLE 386
KSA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY DEPLOYMENT MODE, 2020–2025 (USD MILLION)
TABLE 387
KSA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY DEPLOYMENT MODE, 2026–2031 (USD MILLION)
TABLE 388
KSA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY OWNERSHIP TYPE, 2020–2025 (USD MILLION)
TABLE 389
KSA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY OWNERSHIP TYPE, 2026–2031 (USD MILLION)
TABLE 390
UAE: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY OFFERING, 2020–2025 (USD MILLION)
TABLE 391
UAE: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY OFFERING, 2026–2031 (USD MILLION)
TABLE 392
UAE: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SERVICE, 2020–2025 (USD MILLION)
TABLE 393
UAE: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SERVICE, 2026–2031 (USD MILLION)
TABLE 394
UAE: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY PROFESSIONAL SERVICE, 2020–2025 (USD MILLION)
TABLE 395
UAE: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY PROFESSIONAL SERVICE, 2026–2031 (USD MILLION)
TABLE 396
UAE: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SOLUTION TYPE, 2020–2025 (USD MILLION)
TABLE 397
UAE: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SOLUTION TYPE, 2026–2031 (USD MILLION)
TABLE 398
UAE: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SECURITY TYPE, 2020–2025 (USD MILLION)
TABLE 399
UAE: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SECURITY TYPE, 2026–2031 (USD MILLION)
TABLE 400
UAE: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY DEPLOYMENT MODE, 2020–2025 (USD MILLION)
TABLE 401
UAE: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY DEPLOYMENT MODE, 2026–2031 (USD MILLION)
TABLE 402
UAE: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY OWNERSHIP TYPE, 2020–2025 (USD MILLION)
TABLE 403
UAE: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY OWNERSHIP TYPE, 2026–2031 (USD MILLION)
TABLE 404
OTHER GCC COUNTRIES: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY OFFERING, 2020–2025 (USD MILLION)
TABLE 405
OTHER GCC COUNTRIES: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY OFFERING, 2026–2031 (USD MILLION)
TABLE 406
OTHER GCC COUNTRIES: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SERVICE, 2020–2025 (USD MILLION)
TABLE 407
OTHER GCC COUNTRIES: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SERVICE, 2026–2031 (USD MILLION)
TABLE 408
OTHER GCC COUNTRIES: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY PROFESSIONAL SERVICE, 2020–2025 (USD MILLION)
TABLE 409
OTHER GCC COUNTRIES: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY PROFESSIONAL SERVICE, 2026–2031 (USD MILLION)
TABLE 410
OTHER GCC COUNTRIES: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SOLUTION TYPE, 2020–2025 (USD MILLION)
TABLE 411
OTHER GCC COUNTRIES: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SOLUTION TYPE, 2026–2031 (USD MILLION)
TABLE 412
OTHER GCC COUNTRIES: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SECURITY TYPE, 2020–2025 (USD MILLION)
TABLE 413
OTHER GCC COUNTRIES: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SECURITY TYPE, 2026–2031 (USD MILLION)
TABLE 414
OTHER GCC COUNTRIES: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY DEPLOYMENT MODE, 2020–2025 (USD MILLION)
TABLE 415
OTHER GCC COUNTRIES: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY DEPLOYMENT MODE, 2026–2031 (USD MILLION)
TABLE 416
OTHER GCC COUNTRIES: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY OWNERSHIP TYPE, 2020–2025 (USD MILLION)
TABLE 417
OTHER GCC COUNTRIES: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY OWNERSHIP TYPE, 2026–2031 (USD MILLION)
TABLE 418
SOUTH AFRICA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY OFFERING, 2020–2025 (USD MILLION)
TABLE 419
SOUTH AFRICA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY OFFERING, 2026–2031 (USD MILLION)
TABLE 420
SOUTH AFRICA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SERVICE, 2020–2025 (USD MILLION)
TABLE 421
SOUTH AFRICA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SERVICE, 2026–2031 (USD MILLION)
TABLE 422
SOUTH AFRICA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY PROFESSIONAL SERVICE, 2020–2025 (USD MILLION)
TABLE 423
SOUTH AFRICA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY PROFESSIONAL SERVICE, 2026–2031 (USD MILLION)
TABLE 424
SOUTH AFRICA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SOLUTION TYPE, 2020–2025 (USD MILLION)
TABLE 425
SOUTH AFRICA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SOLUTION TYPE, 2026–2031 (USD MILLION)
TABLE 426
SOUTH AFRICA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SECURITY TYPE, 2020–2025 (USD MILLION)
TABLE 427
SOUTH AFRICA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SECURITY TYPE, 2026–2031 (USD MILLION)
TABLE 428
SOUTH AFRICA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY DEPLOYMENT MODE, 2020–2025 (USD MILLION)
TABLE 429
SOUTH AFRICA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY DEPLOYMENT MODE, 2026–2031 (USD MILLION)
TABLE 430
SOUTH AFRICA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY OWNERSHIP TYPE, 2020–2025 (USD MILLION)
TABLE 431
SOUTH AFRICA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY OWNERSHIP TYPE, 2026–2031 (USD MILLION)
TABLE 432
REST OF MIDDLE EAST & AFRICA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY OFFERING, 2020–2025 (USD MILLION)
TABLE 433
REST OF MIDDLE EAST & AFRICA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY OFFERING, 2026–2031 (USD MILLION)
TABLE 434
REST OF MIDDLE EAST & AFRICA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SERVICE, 2020–2025 (USD MILLION)
TABLE 435
REST OF MIDDLE EAST & AFRICA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SERVICE, 2026–2031 (USD MILLION)
TABLE 436
REST OF MIDDLE EAST & AFRICA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY PROFESSIONAL SERVICE, 2020–2025 (USD MILLION)
TABLE 437
REST OF MIDDLE EAST & AFRICA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY PROFESSIONAL SERVICE, 2026–2031 (USD MILLION)
TABLE 438
REST OF MIDDLE EAST & AFRICA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SOLUTION TYPE, 2020–2025 (USD MILLION)
TABLE 439
REST OF MIDDLE EAST & AFRICA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SOLUTION TYPE, 2026–2031 (USD MILLION)
TABLE 440
REST OF MIDDLE EAST & AFRICA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SECURITY TYPE, 2020–2025 (USD MILLION)
TABLE 441
REST OF MIDDLE EAST & AFRICA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SECURITY TYPE, 2026–2031 (USD MILLION)
TABLE 442
REST OF MIDDLE EAST & AFRICA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY DEPLOYMENT MODE, 2020–2025 (USD MILLION)
TABLE 443
REST OF MIDDLE EAST & AFRICA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY DEPLOYMENT MODE, 2026–2031 (USD MILLION)
TABLE 444
REST OF MIDDLE EAST & AFRICA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY OWNERSHIP TYPE, 2020–2025 (USD MILLION)
TABLE 445
REST OF MIDDLE EAST & AFRICA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY OWNERSHIP TYPE, 2026–2031 (USD MILLION)
TABLE 446
LATIN AMERICA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY OFFERING, 2020–2025 (USD MILLION)
TABLE 447
LATIN AMERICA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY OFFERING, 2026–2031 (USD MILLION)
TABLE 448
LATIN AMERICA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SERVICE, 2020–2025 (USD MILLION)
TABLE 449
LATIN AMERICA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SERVICE, 2026–2031 (USD MILLION)
TABLE 450
LATIN AMERICA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY PROFESSIONAL SERVICE, 2020–2025 (USD MILLION)
TABLE 451
LATIN AMERICA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY PROFESSIONAL SERVICE, 2026–2031 (USD MILLION)
TABLE 452
LATIN AMERICA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SOLUTION TYPE, 2020–2025 (USD MILLION)
TABLE 453
LATIN AMERICA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SOLUTION TYPE, 2026–2031 (USD MILLION)
TABLE 454
LATIN AMERICA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SECURITY TYPE, 2020–2025 (USD MILLION)
TABLE 455
LATIN AMERICA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SECURITY TYPE, 2026–2031 (USD MILLION)
TABLE 456
LATIN AMERICA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY DEPLOYMENT MODE, 2020–2025 (USD MILLION)
TABLE 457
LATIN AMERICA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY DEPLOYMENT MODE, 2026–2031 (USD MILLION)
TABLE 458
LATIN AMERICA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY OWNERSHIP TYPE, 2020–2025 (USD MILLION)
TABLE 459
LATIN AMERICA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY OWNERSHIP TYPE, 2026–2031 (USD MILLION)
TABLE 460
LATIN AMERICA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY COUNTRY, 2020–2025 (USD MILLION)
TABLE 461
LATIN AMERICA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY COUNTRY, 2026–2031 (USD MILLION)
TABLE 462
BRAZIL: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY OFFERING, 2020–2025 (USD MILLION)
TABLE 463
BRAZIL: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY OFFERING, 2026–2031 (USD MILLION)
TABLE 464
BRAZIL: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SERVICE, 2020–2025 (USD MILLION)
TABLE 465
BRAZIL: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SERVICE, 2026–2031 (USD MILLION)
TABLE 466
BRAZIL: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY PROFESSIONAL SERVICE, 2020–2025 (USD MILLION)
TABLE 467
BRAZIL: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY PROFESSIONAL SERVICE, 2026–2031 (USD MILLION)
TABLE 468
BRAZIL: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SOLUTION TYPE, 2020–2025 (USD MILLION)
TABLE 469
BRAZIL: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SOLUTION TYPE, 2026–2031 (USD MILLION)
TABLE 470
BRAZIL: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SECURITY TYPE, 2020–2025 (USD MILLION)
TABLE 471
BRAZIL: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SECURITY TYPE, 2026–2031 (USD MILLION)
TABLE 472
BRAZIL: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY DEPLOYMENT MODE, 2020–2025 (USD MILLION)
TABLE 473
BRAZIL: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY DEPLOYMENT MODE, 2026–2031 (USD MILLION)
TABLE 474
BRAZIL: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY OWNERSHIP TYPE, 2020–2025 (USD MILLION)
TABLE 475
BRAZIL: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY OWNERSHIP TYPE, 2026–2031 (USD MILLION)
TABLE 476
MEXICO: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY OFFERING, 2020–2025 (USD MILLION)
TABLE 477
MEXICO: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY OFFERING, 2026–2031 (USD MILLION)
TABLE 478
MEXICO: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SERVICE, 2020–2025 (USD MILLION)
TABLE 479
MEXICO: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SERVICE, 2026–2031 (USD MILLION)
TABLE 480
MEXICO: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY PROFESSIONAL SERVICE, 2020–2025 (USD MILLION)
TABLE 481
MEXICO: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY PROFESSIONAL SERVICE, 2026–2031 (USD MILLION)
TABLE 482
MEXICO: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SOLUTION TYPE, 2020–2025 (USD MILLION)
TABLE 483
MEXICO: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SOLUTION TYPE, 2026–2031 (USD MILLION)
TABLE 484
MEXICO: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SECURITY TYPE, 2020–2025 (USD MILLION)
TABLE 485
MEXICO: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SECURITY TYPE, 2026–2031 (USD MILLION)
TABLE 486
MEXICO: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY DEPLOYMENT MODE, 2020–2025 (USD MILLION)
TABLE 487
MEXICO: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY DEPLOYMENT MODE, 2026–2031 (USD MILLION)
TABLE 488
MEXICO: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY OWNERSHIP TYPE, 2020–2025 (USD MILLION)
TABLE 489
MEXICO: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY OWNERSHIP TYPE, 2026–2031 (USD MILLION)
TABLE 490
REST OF LATIN AMERICA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY OFFERING, 2020–2025 (USD MILLION)
TABLE 491
REST OF LATIN AMERICA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY OFFERING, 2026–2031 (USD MILLION)
TABLE 492
REST OF LATIN AMERICA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SERVICE, 2020–2025 (USD MILLION)
TABLE 493
REST OF LATIN AMERICA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SERVICE, 2026–2031 (USD MILLION)
TABLE 494
REST OF LATIN AMERICA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY PROFESSIONAL SERVICE, 2020–2025 (USD MILLION)
TABLE 495
REST OF LATIN AMERICA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY PROFESSIONAL SERVICE, 2026–2031 (USD MILLION)
TABLE 496
REST OF LATIN AMERICA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SOLUTION TYPE, 2020–2025 (USD MILLION)
TABLE 497
REST OF LATIN AMERICA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SOLUTION TYPE, 2026–2031 (USD MILLION)
TABLE 498
REST OF LATIN AMERICA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SECURITY TYPE, 2020–2025 (USD MILLION)
TABLE 499
REST OF LATIN AMERICA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY SECURITY TYPE, 2026–2031 (USD MILLION)
TABLE 500
REST OF LATIN AMERICA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY DEPLOYMENT MODE, 2020–2025 (USD MILLION)
TABLE 501
REST OF LATIN AMERICA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY DEPLOYMENT MODE, 2026–2031 (USD MILLION)
TABLE 502
REST OF LATIN AMERICA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY OWNERSHIP TYPE, 2020–2025 (USD MILLION)
TABLE 503
REST OF LATIN AMERICA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, BY OWNERSHIP TYPE, 2026–2031 (USD MILLION)
TABLE 504
OVERVIEW OF STRATEGIES ADOPTED BY KEY GOVERNMENT & PUBLIC SECTOR CYBERSECURITY VENDORS
TABLE 505
GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET: DEGREE OF COMPETITION
TABLE 506
GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET: REGIONAL FOOTPRINT
TABLE 507
GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET: OFFERING FOOTPRINT
TABLE 508
GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET: DEPLOYMENT MODE FOOTPRINT
TABLE 509
GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET: OWNERSHIP TYPE FOOTPRINT
TABLE 510
GOVERNMENT & PUBLIC SECTOR CYBERSECURITY: KEY STARTUPS/SMES, 2025
TABLE 511
GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET: COMPETITIVE BENCHMARKING OF STARTUPS/SMES, BY REGION
TABLE 512
GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET: COMPETITIVE BENCHMARKING OF STARTUPS/SMES, BY OFFERING
TABLE 513
GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET: COMPETITIVE BENCHMARKING OF STARTUPS/SMES, BY DEPLOYMENT MODE
TABLE 514
GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET: OWNERSHIP TYPE FOOTPRINT
TABLE 515
GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET: PRODUCT LAUNCHES/ENHANCEMENTS, JANUARY 2024–MARCH 2026
TABLE 516
GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET: DEALS, JANUARY 2024–MARCH 2026
TABLE 517
GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET: EXPANSIONS, JANUARY 2024–MARCH 2026
TABLE 518
MICROSOFT: COMPANY OVERVIEW
TABLE 519
MICROSOFT: PRODUCTS/SOLUTIONS/SERVICES OFFERED
TABLE 520
MICROSOFT: PRODUCT LAUNCHES/ENHANCEMENTS
TABLE 521
MICROSOFT: DEALS
TABLE 522
MICROSOFT: EXPANSIONS
TABLE 523
LEIDOS: COMPANY OVERVIEW
TABLE 524
LEIDOS: PRODUCTS/SOLUTIONS/SERVICES OFFERED
TABLE 525
LEIDOS: PRODUCT LAUNCHES/ENHANCEMENTS
TABLE 527
LEIDOS: OTHER DEVELOPMENTS
TABLE 528
BOOZ ALLEN HAMILTON: COMPANY OVERVIEW
TABLE 529
BOOZ ALLEN HAMILTON: PRODUCTS/SOLUTIONS/SERVICES OFFERED
TABLE 530
BOOZ ALLEN HAMILTON: PRODUCT LAUNCHES/ENHANCEMENTS
TABLE 531
BOOZ ALLEN HAMILTON: DEALS
TABLE 532
BOOZ ALLEN HAMILTON: EXPANSIONS
TABLE 533
CACI: COMPANY OVERVIEW
TABLE 534
CACI: PRODUCTS/SOLUTIONS/SERVICES OFFERED
TABLE 535
CACI: PRODUCT LAUNCHES/ENHANCEMENTS
TABLE 537
CACI: OTHER DEVELOPMENTS
TABLE 538
ACCENTURE: COMPANY OVERVIEW
TABLE 539
ACCENTURE: PRODUCTS/SOLUTIONS/SERVICES OFFERED
TABLE 540
ACCENTURE: PRODUCT LAUNCHES/ENHANCEMENTS
TABLE 541
ACCENTURE: DEALS
TABLE 542
ACCENTURE: EXPANSIONS
TABLE 543
IBM: COMPANY OVERVIEW
TABLE 544
IBM: PRODUCTS/SOLUTIONS/SERVICES OFFERED
TABLE 545
IBM: PRODUCT LAUNCHES/ENHANCEMENTS
TABLE 547
IBM: OTHER DEVELOPMENTS
TABLE 548
PALO ALTO NETWORKS: COMPANY OVERVIEW
TABLE 549
PALO ALTO NETWORKS: PRODUCTS/SOLUTIONS/SERVICES OFFERED
TABLE 550
PALO ALTO NETWORKS: PRODUCT LAUNCHES/ENHANCEMENTS
TABLE 551
PALO ALTO NETWORKS: DEALS
TABLE 552
FORTINET: COMPANY OVERVIEW
TABLE 553
FORTINET: PRODUCTS/SOLUTIONS/SERVICES OFFERED
TABLE 554
FORTINET: PRODUCT ENHANCEMENTS
TABLE 555
FORTINET: DEALS
TABLE 556
FORTINET: EXPANSIONS
TABLE 557
CISCO: COMPANY OVERVIEW
TABLE 558
CISCO: PRODUCTS/SOLUTIONS/SERVICES OFFERED
TABLE 559
CISCO: PRODUCT LAUNCHES/ENHANCEMENTS
TABLE 561
CISCO: EXPANSIONS
TABLE 562
CROWDSTRIKE: COMPANY OVERVIEW
TABLE 563
CROWDSTRIKE: PRODUCTS/SOLUTIONS/SERVICES OFFERED
TABLE 564
CROWDSTRIKE: PRODUCT LAUNCHES/ENHANCEMENTS
TABLE 565
CROWDSTRIKE: DEALS
TABLE 566
CROWDSTRIKE: EXPANSIONS
TABLE 567
CHECK POINT: COMPANY OVERVIEW
TABLE 568
CHECK POINT: PRODUCTS/SOLUTIONS/SERVICES OFFERED
TABLE 569
CHECK POINT: PRODUCT LAUNCHES/ENHANCEMENTS
TABLE 570
CHECK POINT: DEALS
TABLE 571
CHECK POINT: EXPANSIONS
TABLE 572
ZSCALER: COMPANY OVERVIEW
TABLE 573
ZSCALER: PRODUCTS/SOLUTIONS/SERVICES OFFERED
TABLE 574
ZSCALER: PRODUCT LAUNCHES/ENHANCEMENTS
TABLE 576
ZSCALER: EXPANSIONS
TABLE 577
TENABLE: COMPANY OVERVIEW
TABLE 578
TENABLE: PRODUCTS/SOLUTIONS/SERVICES OFFERED
TABLE 579
TENABLE: PRODUCT LAUNCHES/ENHANCEMENTS
TABLE 581
CYBERARK: COMPANY OVERVIEW
TABLE 582
CYBERARK: PRODUCTS/SOLUTIONS/SERVICES OFFERED
TABLE 583
CYBERARK: PRODUCT LAUNCHES/ENHANCEMENTS
TABLE 584
CYBERARK: DEALS
TABLE 585
BAE SYSTEMS: COMPANY OVERVIEW
TABLE 586
BAE SYSTEMS: PRODUCTS/SOLUTIONS/SERVICES OFFERED
TABLE 587
BAE SYSTEMS: PRODUCT LAUNCHES/ENHANCEMENTS
TABLE 588
BAE SYSTEMS: DEALS
TABLE 589
BAE SYSTEMS: EXPANSIONS
TABLE 590
HONEYWELL: COMPANY OVERVIEW
TABLE 591
HONEYWELL: PRODUCTS/SOLUTIONS/SERVICES OFFERED
TABLE 592
HONEYWELL: PRODUCT LAUNCHES/ENHANCEMENTS
TABLE 593
HONEYWELL: DEALS
TABLE 594
HONEYWELL: EXPANSIONS
TABLE 595
DRAGOS: COMPANY OVERVIEW
TABLE 596
DRAGOS: PRODUCTS/SOLUTIONS/SERVICES OFFERED
TABLE 597
DRAGOS: PRODUCT LAUNCHES/ENHANCEMENTS
TABLE 599
DRAGOS: EXPANSIONS
TABLE 600
CLAROTY: COMPANY OVERVIEW
TABLE 601
CLAROTY: PRODUCTS/SOLUTIONS/SERVICES OFFERED
TABLE 602
CLAROTY: PRODUCT LAUNCHES & ENHANCEMENTS
TABLE 604
FORESCOUT: COMPANY OVERVIEW
TABLE 605
FORESCOUT: PRODUCTS/SOLUTIONS/SERVICES OFFERED
TABLE 606
FORESCOUT: PRODUCT LAUNCHES/ENHANCEMENTS
TABLE 607
FORESCOUT: DEALS
TABLE 608
VECTRA AI: COMPANY OVERVIEW
TABLE 609
VECTRA AI: PRODUCTS/SOLUTIONS/SERVICES OFFERED
TABLE 610
VECTRA AI: PRODUCT LAUNCHES/ENHANCEMENTS
TABLE 611
VECTRA AI: DEALS
TABLE 612
FACTOR ANALYSIS
FIGURE 2
GLOBAL GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, 2020-2031
FIGURE 3
MAJOR STRATEGIES ADOPTED BY KEY PLAYERS IN GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET 2020–2026
FIGURE 4
DISRUPTIVE TRENDS IMPACTING GROWTH OF GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET
FIGURE 5
HIGH-GROWTH SEGMENTS & EMERGING FRONTIERS IN GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, 2026
FIGURE 6
ASIA PACIFIC TO REGISTER HIGHEST GROWTH RATE DURING FORECAST PERIOD
FIGURE 7
RISING CYBER THREATS, DIGITAL GOVERNMENT INITIATIVES, AND AI-DRIVEN SECURITY SOLUTIONS TO DRIVE MARKET
FIGURE 8
SOLUTIONS SEGMENT TO ACCOUNT FOR LARGER MARKET SHARE DURING FORECAST PERIOD
FIGURE 9
PROFESSIONAL SERVICES SEGMENT TO DOMINATE MARKET DURING FORECAST PERIOD
FIGURE 10
DESIGN, CONSULTING, AND IMPLEMENTATION TO HOLD SIGNIFICANT SHARE DURING FORECAST PERIOD
FIGURE 11
LOG MANAGEMENT & SIEM TO HOLD MAJOR MARKET SHARE DURING FORECAST PERIOD
FIGURE 12
NETWORK SECURITY TO DOMINATE DURING FORECAST PERIOD
FIGURE 13
ON-PREMISES DEPLOYMENT TO COMMAND LARGEST SHARE DURING FORECAST PERIOD
FIGURE 14
DEFENSE & INTELLIGENCE AGENCIES TO HOLD MAJOR SHARE DURING FORECAST PERIOD
FIGURE 15
NORTH AMERICA TO EMERGE AS MOST SIGNIFICANT MARKET
FIGURE 16
KEY CYBERSECURITY DOMAINS IN GOVERNMENT & PUBLIC SECTOR
FIGURE 17
GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET: DRIVERS, RESTRAINTS, OPPORTUNITIES, AND CHALLENGES
FIGURE 18
GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET: PORTER’S FIVE FORCES ANALYSIS
FIGURE 19
GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET: VALUE CHAIN ANALYSIS
FIGURE 20
GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET: ECOSYSTEM ANALYSIS
FIGURE 21
AVERAGE SELLING PRICE TREND OF KEY VENDORS, BY SOLUTION TYPE, 2026
FIGURE 22
IMPORT DATA FOR HS CODE 8517-COMPLIANT PRODUCTS, BY COUNTRY, 2021–2025 (USD MILLION)
FIGURE 23
EXPORT DATA FOR HS CODE 8517-COMPLIANT PRODUCTS, BY COUNTRY, 2021–2025 (USD MILLION)
FIGURE 24
TRENDS/DISRUPTIONS INFLUENCING CUSTOMER BUSINESS
FIGURE 25
LEADING GOVERNMENT & PUBLIC SECTOR CYBERSECURITY VENDORS BY TOTAL FUNDING VALUE AND NUMBER OF FUNDING ROUNDS
FIGURE 26
PATENTS GRANTED IN GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, 2016–2026
FIGURE 27
REGIONAL ANALYSIS OF PATENTS GRANTED IN GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET
FIGURE 28
FUTURE APPLICATIONS OF GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET
FIGURE 29
SUCCESS STORIES AND REAL-WORLD APPLICATIONS IN GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET
FIGURE 30
GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET: DECISION-MAKING FACTORS
FIGURE 31
INFLUENCE OF STAKEHOLDERS ON BUYING PROCESS FOR TOP THREE OWNERSHIP TYPES
FIGURE 32
KEY BUYING CRITERIA FOR TOP THREE OWNERSHIP TYPES
FIGURE 33
ADOPTION BARRIERS AND INTERNAL CHALLENGES
FIGURE 34
SERVICES SEGMENT TO LEAD MARKET DURING FORECAST PERIOD
FIGURE 35
MANAGED SERVICES SEGMENT TO WITNESS FASTEST GROWTH DURING FORECAST PERIOD
FIGURE 36
RISK & THREAT MANAGEMENT SEGMENT TO ACHIEVE FASTEST GROWTH DURING FORECAST PERIOD
FIGURE 37
LOG MANAGEMENT & SIEM SEGMENT TO LEAD MARKET DURING FORECAST PERIOD
FIGURE 38
ENDPOINT & IOT SECURITY SEGMENT TO GROW FASTEST DURING FORECAST PERIOD
FIGURE 39
ON-PREMISES SEGMENT TO LEAD MARKET DURING FORECAST PERIOD
FIGURE 40
DEFENSE & INTELLIGENCE SEGMENT TO ACHIEVE FASTEST GROWTH DURING FORECAST PERIOD
FIGURE 41
ASIA PACIFIC TO REGISTER HIGHEST CAGR DURING FORECAST PERIOD
FIGURE 42
NORTH AMERICA: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET SNAPSHOT
FIGURE 43
ASIA PACIFIC: GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET SNAPSHOT
FIGURE 44
SEGMENTAL REVENUE ANALYSIS OF KEY MARKET PLAYERS, 2021–2025 (USD MILLION)
FIGURE 45
SHARE OF LEADING COMPANIES IN GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET, 2025
FIGURE 46
BRAND COMPARISON
FIGURE 47
GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET: COMPANY VALUATION OF KEY VENDORS, 2026 (USD BILLION)
FIGURE 48
GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET: FINANCIAL METRICS OF KEY VENDORS, 2026
FIGURE 49
GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET: COMPANY EVALUATION MATRIX (KEY PLAYERS), 2025
FIGURE 50
GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET: COMPANY FOOTPRINT
FIGURE 51
GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET: COMPANY EVALUATION MATRIX (STARTUPS/SMES), 2025
FIGURE 52
MICROSOFT: COMPANY SNAPSHOT
FIGURE 53
LEIDOS: COMPANY SNAPSHOT
FIGURE 54
BOOZ ALLEN HAMILTON: COMPANY SNAPSHOT
FIGURE 55
CACI: COMPANY SNAPSHOT
FIGURE 56
ACCENTURE: COMPANY SNAPSHOT
FIGURE 57
IBM: COMPANY SNAPSHOT
FIGURE 58
PALO ALTO NETWORKS: COMPANY SNAPSHOT
FIGURE 59
FORTINET: COMPANY SNAPSHOT
FIGURE 60
CISCO: COMPANY SNAPSHOT
FIGURE 61
CROWDSTRIKE: COMPANY SNAPSHOT
FIGURE 62
CHECK POINT: COMPANY SNAPSHOT
FIGURE 63
ZSCALER: COMPANY SNAPSHOT
FIGURE 64
TENABLE: COMPANY SNAPSHOT
FIGURE 65
CYBERARK: COMPANY SNAPSHOT
FIGURE 66
BAE SYSTEMS: COMPANY SNAPSHOT
FIGURE 67
HONEYWELL: COMPANY SNAPSHOT
FIGURE 68
GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET: RESEARCH DESIGN
FIGURE 69
APPROACH 1 (SUPPLY-SIDE): REVENUE FROM SOLUTIONS AND SERVICES IN GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET
FIGURE 70
SUPPLY-SIDE ANALYSIS: MARKET SIZE ESTIMATION METHODOLOGY
FIGURE 71
APPROACH 2: BOTTOM-UP (DEMAND SIDE)
FIGURE 72
GOVERNMENT & PUBLIC SECTOR CYBERSECURITY MARKET: RESEARCH FLOW





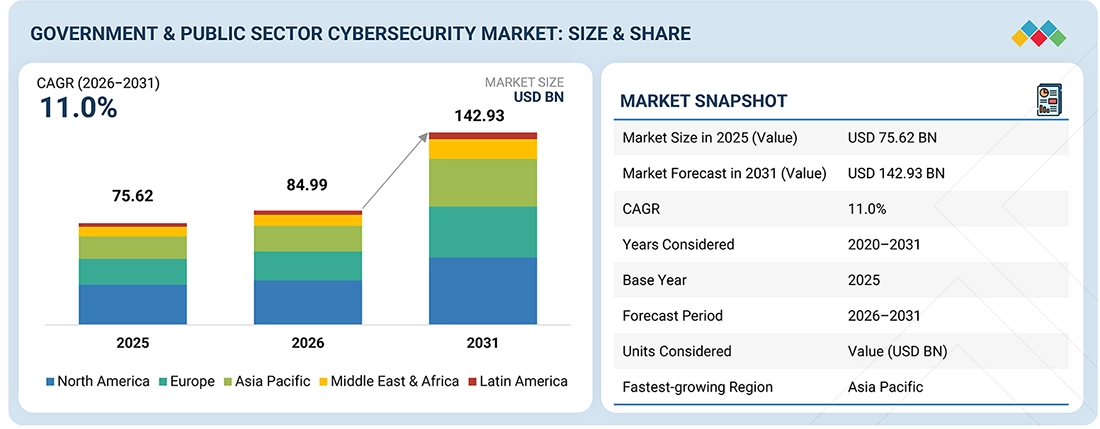
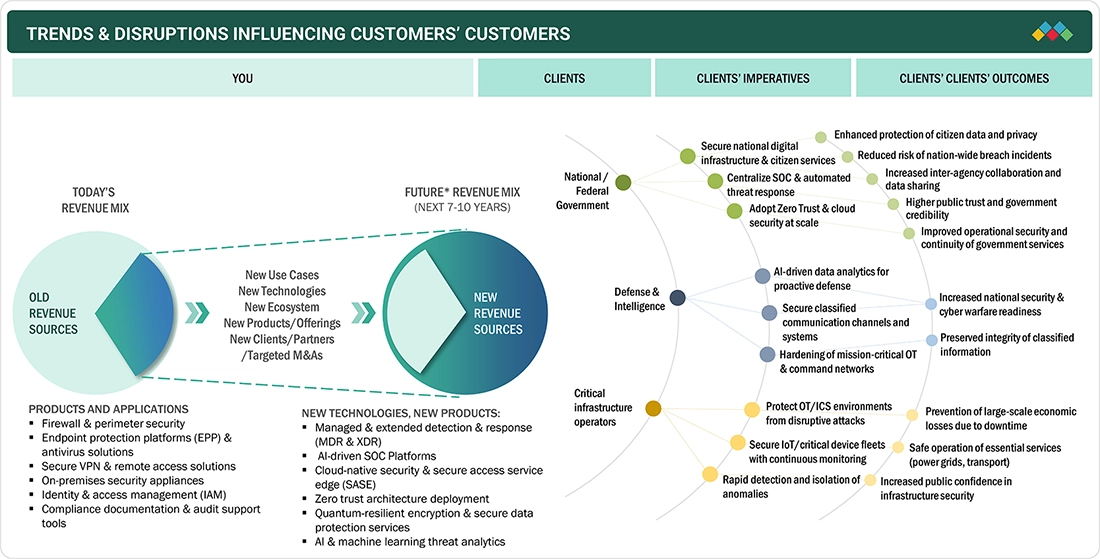





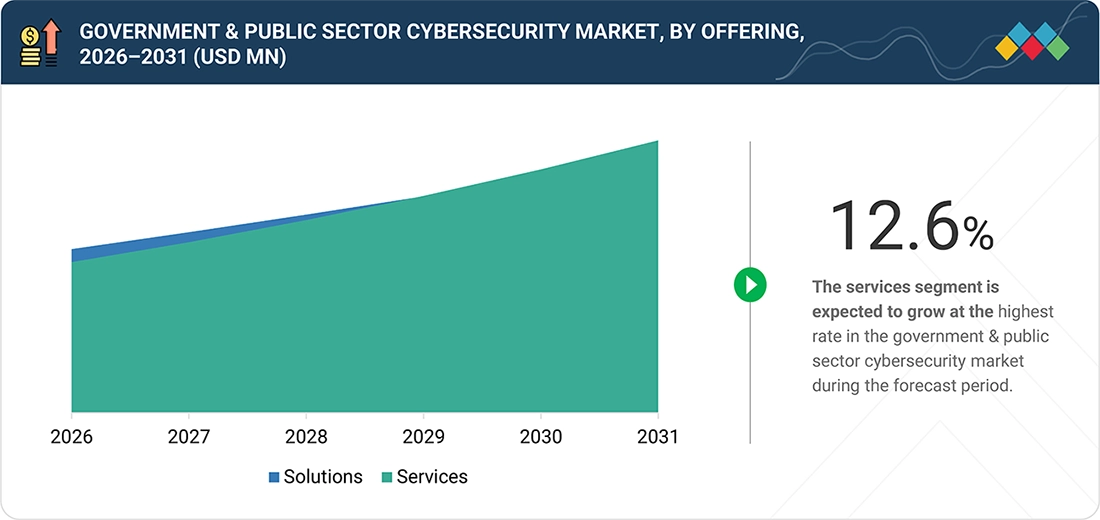
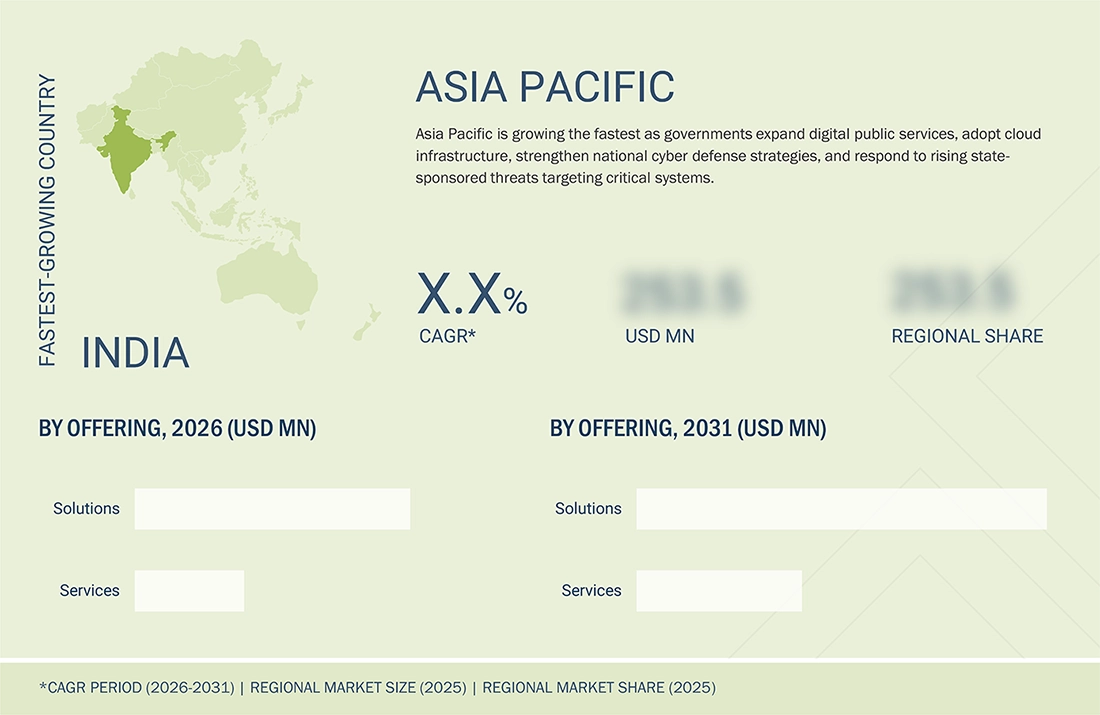

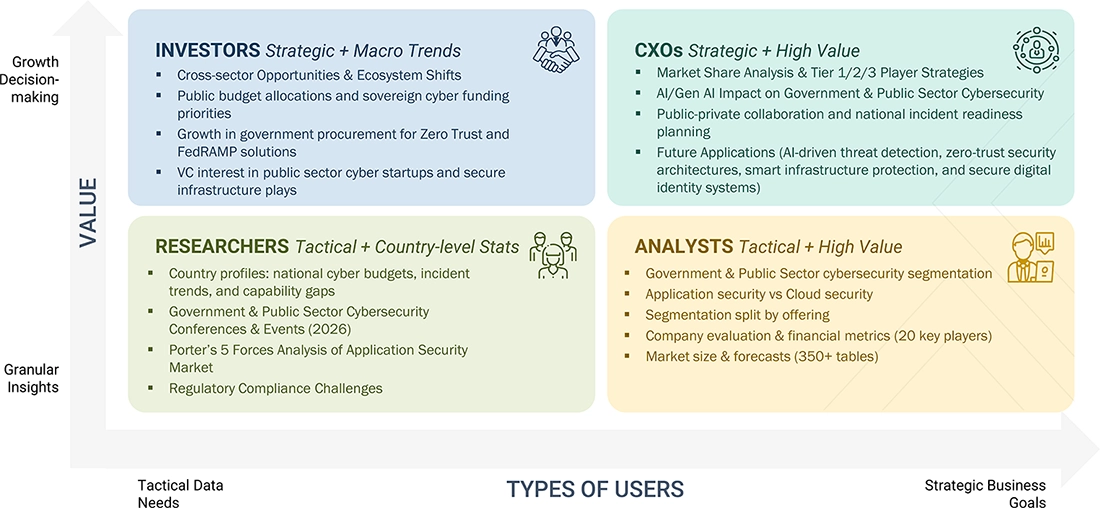

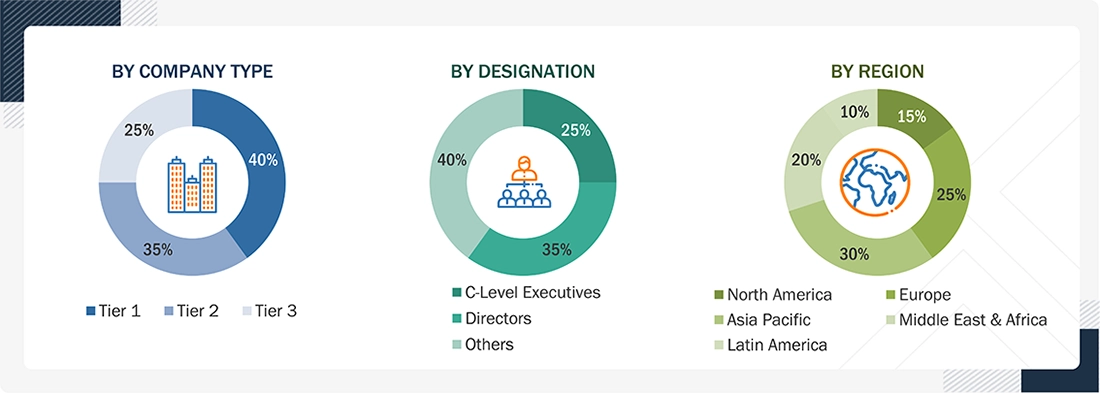
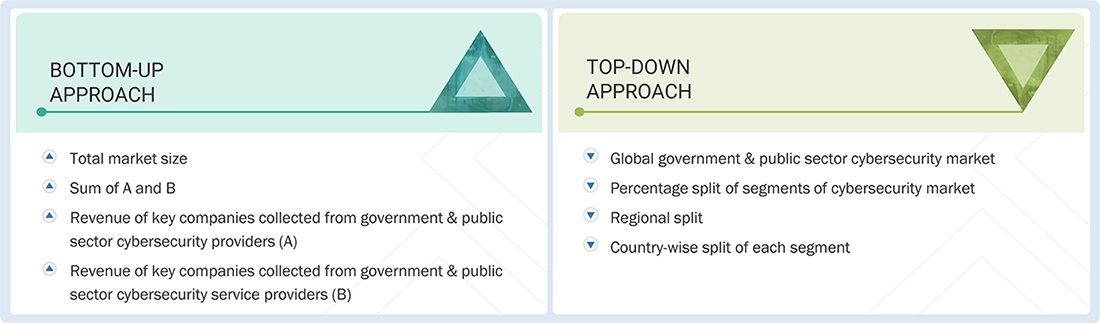














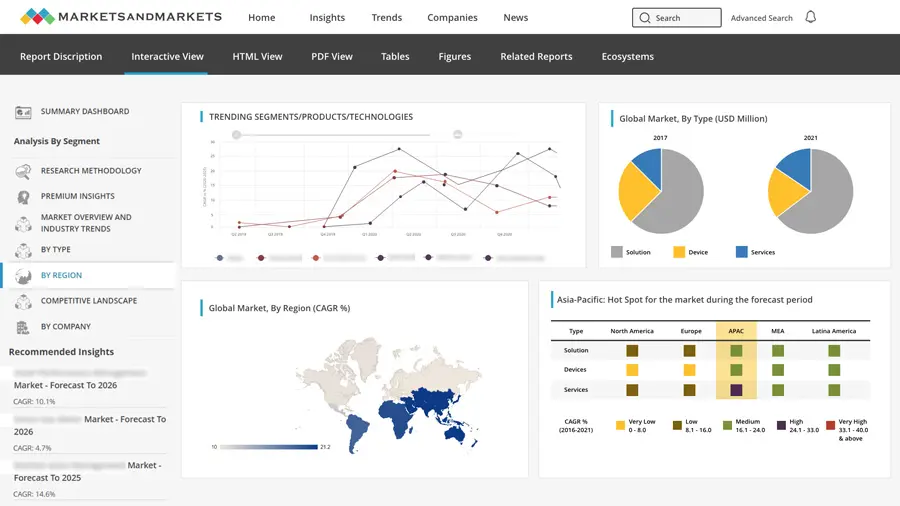
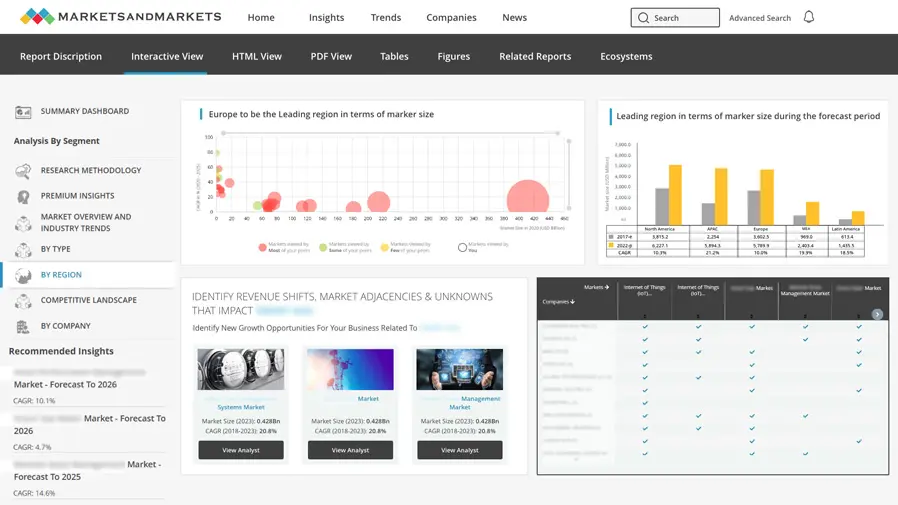
Growth opportunities and latent adjacency in Government & Public Sector Cybersecurity Market