
Industrial Control Systems (ICS) Security Market in Energy & Power
Industrial Control Systems (ICS) Security Market in Energy & Power by Solution (Encryption, SIEM, Firewall, IAM, DDoS Mitigation, Antivirus), Security Type (Network, Endpoint, Database), Vertical, and Region - Global Forecast to 2030




OVERVIEW
Source: Secondary Research, Interviews with Experts, MarketsandMarkets Analysis
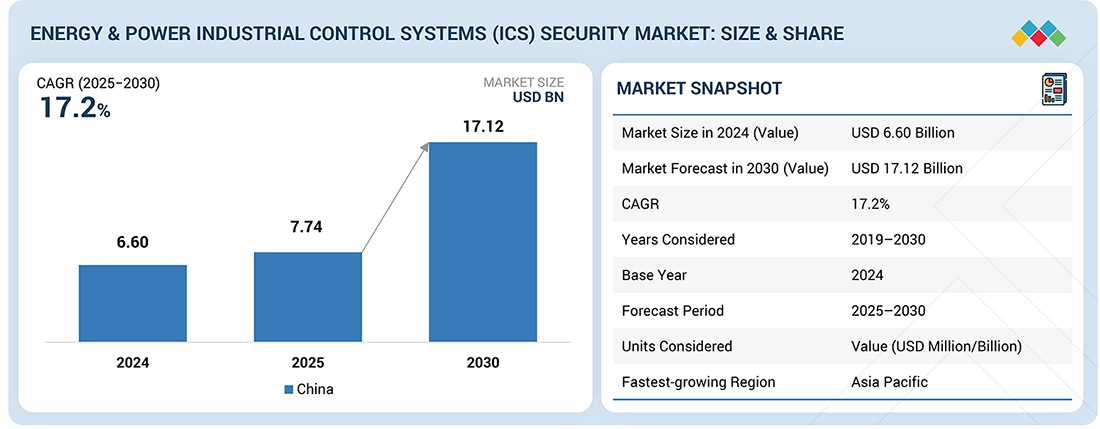
The ICS security market in energy & power is projected to reach USD 17.12 billion by 2030 from USD 7.74 billion in 2025, at a CAGR of 17.2%. Cyber insurance providers are tightening requirements for critical infrastructure. As a result, Utilities adopt stronger ICS security controls to meet coverage conditions and lower premiums, driving the growth of the ICS security market in the energy & power vertical.
KEY TAKEAWAYS
-
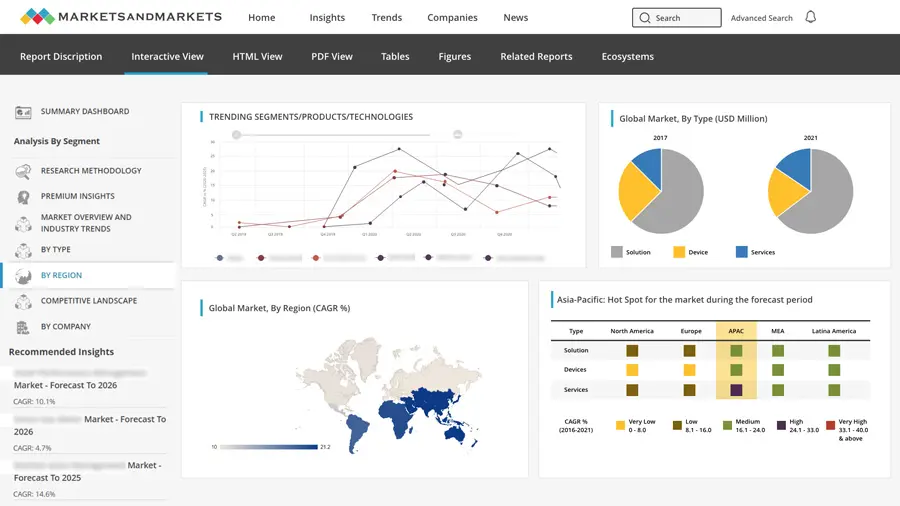
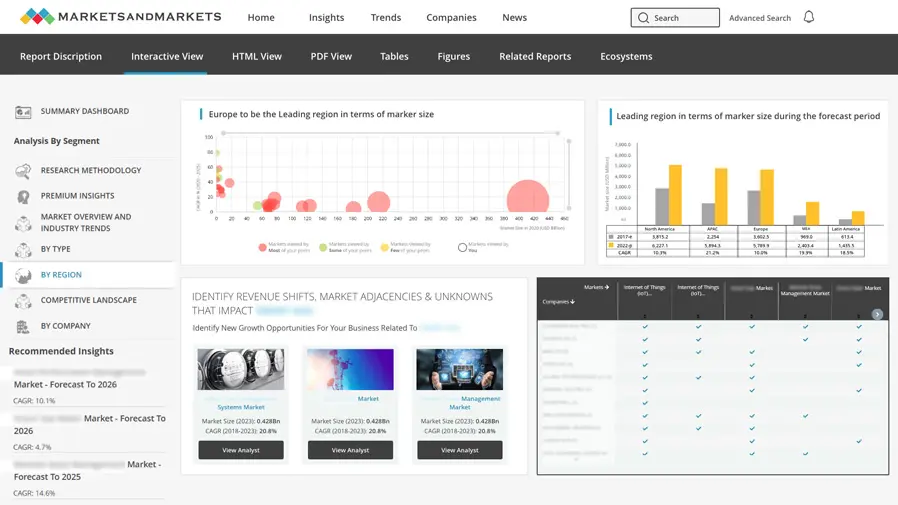
BY REGIONBy region, Asia Pacific is estimated to register the highest CAGR during the forecast period.
-
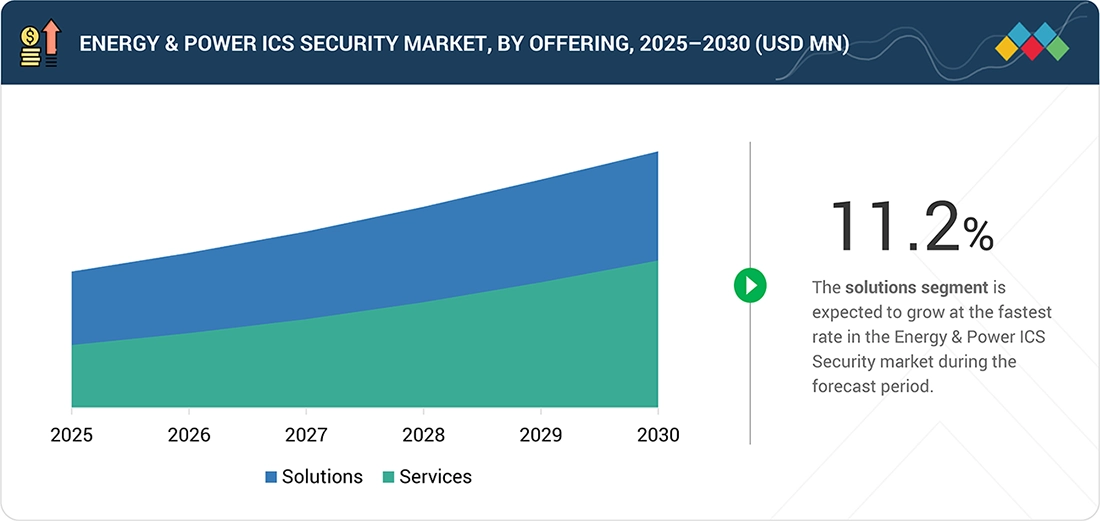
BY OFFERINGBy offering, solutions are projected to register the highest CAGR of 11.2%.
-
BY SOLUTIONBy solution, the IAM segment is set to grow the fastest during the forecast period.
-
BY SERVICEAmong services, the managed services segment is projected to grow at the fastest rate of 13.5% from 2025 to 2030.
-
BY SECURITY TYPEBy security type, the endpoint security segment is projected to dominate the market.
-
BY VERTICALBy vertical, power generation segment is estimated to register the highest CAGR of 10.5%.
-
COMPETITIVE LANDSCAPE - KEY PLAYERSDragos, Nozomi Networks, Siemens, Schneider Electric, ABB, and GE Vernova are key players in the ICS security market in energy & power, supported by advanced OT-security platforms, deep grid-level visibility, and strong domain expertise across substations, generation assets, and transmission networks. Their capabilities align closely with utility modernization and critical-infrastructure protection needs.
-
COMPETITIVE LANDSCAPE - STARTUPSTXOne Networks, Cyolo, SCADAfence, NanoLock Security, and XONA Systems are emerging strongly in the ICS security space of energy & power by delivering OT-native protection, secure remote-access solutions, device-level hardening, and advanced anomaly detection. Their technologies address growing requirements for securing distributed energy assets and modern digital substations.
Stronger Industrial Control Systems Security investments across power networks are driven by the need to avoid unauthorized access, data tampering, and operational disruption. This has become more important as utilities deploy DER (Distributed Energy Resources) platforms, smart inverters, and digital protection systems. These additions increase device diversity and complexity, making secure onboarding, vendor compatibility, and ongoing device monitoring essential.
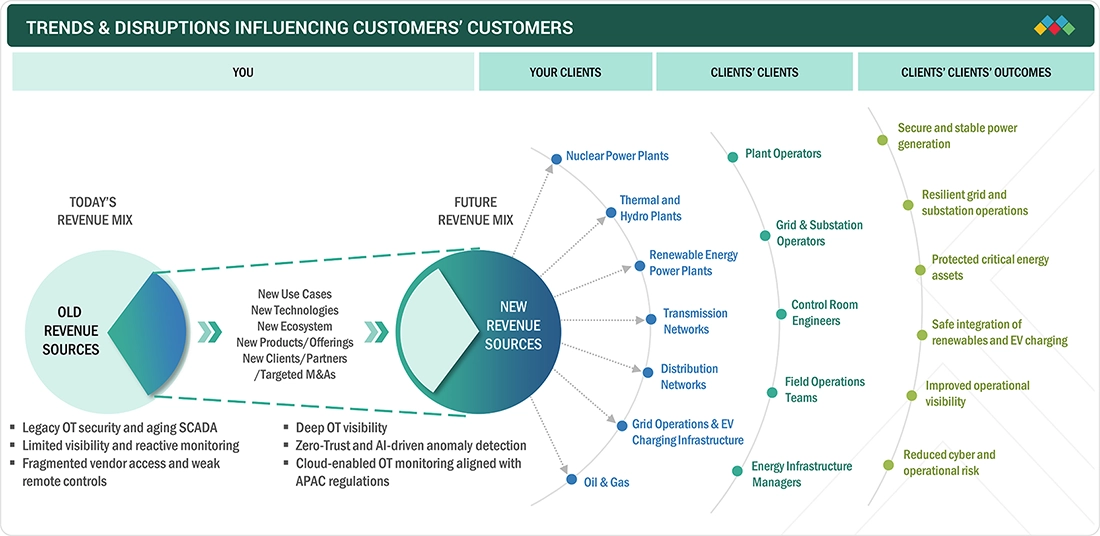
TRENDS & DISRUPTIONS IMPACTING CUSTOMERS' CUSTOMERS
Digital substations, renewable integration, and the expansion of distributed energy assets are changing how power systems must be secured. At the same time, cyber incidents affecting grids and generation sites are increasing. Tighter regulations and wider use of remote operations are pushing utilities to adopt better OT visibility, anomaly detection, network segmentation, and continuous monitoring to protect critical energy infrastructure.
Source: Secondary Research, Interviews with Experts, MarketsandMarkets Analysis
MARKET DYNAMICS
Level
-
Renewables integration increasing security needs

-
Stronger grid-security regulations
Level
-
Slow modernization of legacy infrastructure
-
Budget limitations in smaller utilities
Level
-
Rising demand for OT asset visibility
-
Growth of secure remote operations
Level
-
Mixed OT protocols complicate monitoring and response.
-
Multiple vendors increase third-party access risks
Source: Secondary Research, Interviews with Experts, MarketsandMarkets Analysis
Driver: Renewables integration increasing security needs
The fast growth of renewable energy and distributed generation is adding many new connected devices and control points across the grid. Cyber risks have increased as solar plants, wind farms, and smart inverters connect with older systems. To keep operations stable, utilities are investing in stronger OT security, continuous monitoring, and safer ways to coordinate grid operations.
Restraint: Slow modernization of legacy infrastructure
Many power systems still depend on old control equipment and long-life devices that were never designed with security in mind. Upgrading or securing these assets takes time, costs money, and can disrupt daily operations. Because of this slow progress, utilities struggle to clearly see what is happening across their networks and cannot improve cyber protection as quickly as needed.
Opportunity: Rising demand for OT asset visibility
Utilities need a clearer view of what is happening across substations, power plants, and field networks to spot unusual activity and reduce risk. Many operators now realize they have limited visibility into their OT environments. This is driving demand for tools that show connected devices in real time, track normal behavior, and bring monitoring into one place, helping teams respond faster when issues arise.
Challenge: Mixed OT protocols complicate monitoring and response
Power systems use many different communication methods, including standard and vendor-specific ones. This lack of consistency makes it hard to monitor everything in the same way or connect events across systems. As a result, security teams find it difficult to spot unusual behavior, respond quickly, and apply the same level of protection across complex networks built by multiple vendors.
INDUSTRIAL CONTROL SYSTEMS (ICS) SECURITY MARKET: COMMERCIAL USE CASES ACROSS INDUSTRIES
| COMPANY | USE CASE DESCRIPTION | BENEFITS |
|---|---|---|
 |
Providing OT monitoring for generation plants and substations to detect anomalies, map assets, and identify cyber risks across grid operations | Better OT visibility, quicker threat detection, and improved protection for critical power infrastructure |
 |
Securing power plants and substations through hardened automation systems, secure remote access, and continuous monitoring of critical OT assets | Stronger operational reliability, reduced exposure to cyber threats, and improved compliance with energy-security standards |
 |
Securing digital substations and automation systems with integrated protection, secure communication, and continuous OT monitoring | Enhanced grid reliability, reduced exposure to equipment tampering, and strengthened compliance with energy-sector requirements |
Logos and trademarks shown above are the property of their respective owners. Their use here is for informational and illustrative purposes only.
MARKET ECOSYSTEM
The ICS security ecosystem in the energy & power vertical spans DDOS protection, endpoint defense, identity management, and industrial firewalls that safeguard substations, control centers, and distributed energy assets. Vendors provide OT-aware monitoring, access control, malware prevention, and deep protocol inspection to enhance grid resilience, secure operations, and protect critical power infrastructure.

Logos and trademarks shown above are the property of their respective owners. Their use here is for informational and illustrative purposes only.
MARKET SEGMENTS
Source: Secondary Research, Interviews with Experts, MarketsandMarkets Analysis
Energy & Power ICS Security Market, by Offering
ICS security offerings in the energy & power sector include firewalls, encryption, malware protection, and access control. These tools protect industrial networks and connected devices. They support secure access and real-time monitoring. Identity and access management is the fastest-growing solution as remote access expands across plants, and control of user access is becoming a core security requirement.
Energy & Power ICS Security Market, by Solution
Solutions include antimalware, DDoS mitigation, encryption, firewalls, IAM, IDS/IPS, vulnerability and configuration management, SIEM, and asset-visibility platforms. These tools deliver protocol-aware monitoring, secure communication, segmentation, and real-time anomaly detection to safeguard generation sites, substations, SCADA systems, and field assets, enabling utilities to maintain resilient and secure energy operations.
Energy & Power ICS Security Market, by Service
Services include consulting, integration, training, and ongoing support, without adding internal burden; they help operators manage security. As operators face skill gaps in OT security, managed services are growing the fastest. Many prefer continuous support over building internal teams.
Energy & Power ICS Security Market, by Security Type
The security segment in the energy & power ICS security market includes network, endpoint, application, and data protection. These layers secure devices and system communication. They reduce the risk of unauthorized movement inside plants. Network security is the largest security type because industrial networks are the main attack path. Operators focus first on protecting traffic between control systems.
Energy & PowerICS Security Market, by Vertical
The energy & power ICS security market covers power generation, power transmission and distribution, and energy infrastructure. Power generation includes nuclear, thermal, and renewable plants with a focus on protecting plant operations. Transmission and distribution include grid networks and EV charging infrastructure, where secure and reliable grid operations are critical. The energy segment includes oil and gas activities across upstream, midstream, and downstream operations. Across these verticals, increasing connectivity and operational complexity continue to drive demand for ICS security.
REGION
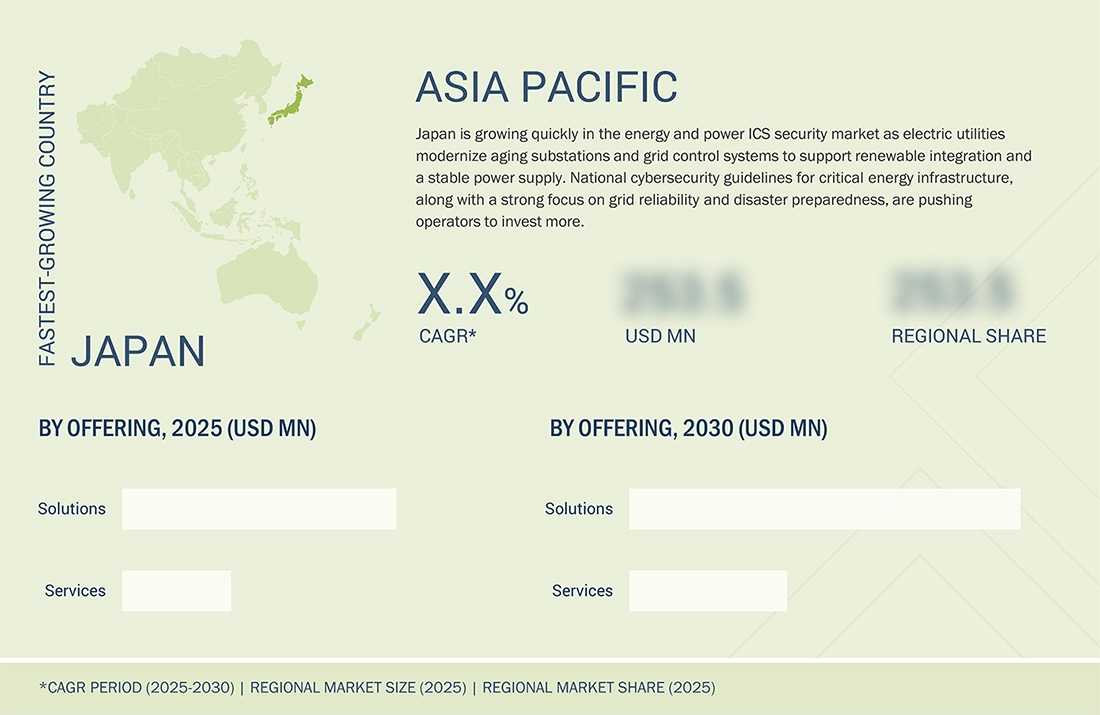
Asia Pacific to be the fastest-growing region in the ICS security market in energy & power
In the Asia Pacific market, Japan is seeing fast growth in the energy and power market as utilities modernize aging grid systems and expand renewable energy like solar and offshore wind. The need to reduce energy imports and strengthen resilience against natural disasters is also pushing operators to invest in better digital systems and security.
INDUSTRIAL CONTROL SYSTEMS (ICS) SECURITY MARKET: COMPANY EVALUATION MATRIX
Siemens (Star) leads the ICS security market with strong capabilities in digital substations, industrial automation, and OT-network protection. Its SCALANCE and Ruggedcom security portfolios deliver deep protocol inspection, secure communication, and grid-resilient architectures that enhance reliability across power, utilities, and critical infrastructure environments. Tenable (Emerging Player) is rapidly expanding its presence with advanced OT asset discovery, vulnerability analytics, and exposure management solutions that improve visibility, strengthen risk prioritization, and support secure operations across diverse industrial sectors.

Source: Secondary Research, Interviews with Experts, MarketsandMarkets Analysis
KEY MARKET PLAYERS
- Dragos (US)
- Nozomi Networks (US)
- Claroty (US)
- Honeywell (US)
- Siemens (Germany)
- Schneider Electric (France)
- ABB (Switzerland)
- Rockwell Automation (US)
- GE Vernova (US)
- Mitsubishi Electric (Japan)
- Palo Alto Networks (US)
- Cisco Systems (US)
- Fortinet (US)
- Check Point Software (US)
- Tenable (US)
MARKET SCOPE
| REPORT METRIC | DETAILS |
|---|---|
| Market Size in 2024 (Value) | USD 6.60 billion |
| Market Forecast in 2030 (Value) | USD 17.12 Billion |
| Growth Rate | CAGR of 17.2% from 2025 to 2030 |
| Years Considered | 2019–2030 |
| Base Year | 2024 |
| Forecast Period | 2025–2030 |
| Units Considered | Value (USD Million/Billion) |
| Report Coverage | Revenue forecast, company ranking, competitive landscape, growth factors, and trends |
| Segments Covered |
|
| Regions Covered | North America, Europe, Asia Pacific, Middle East & Africa, Latin America |
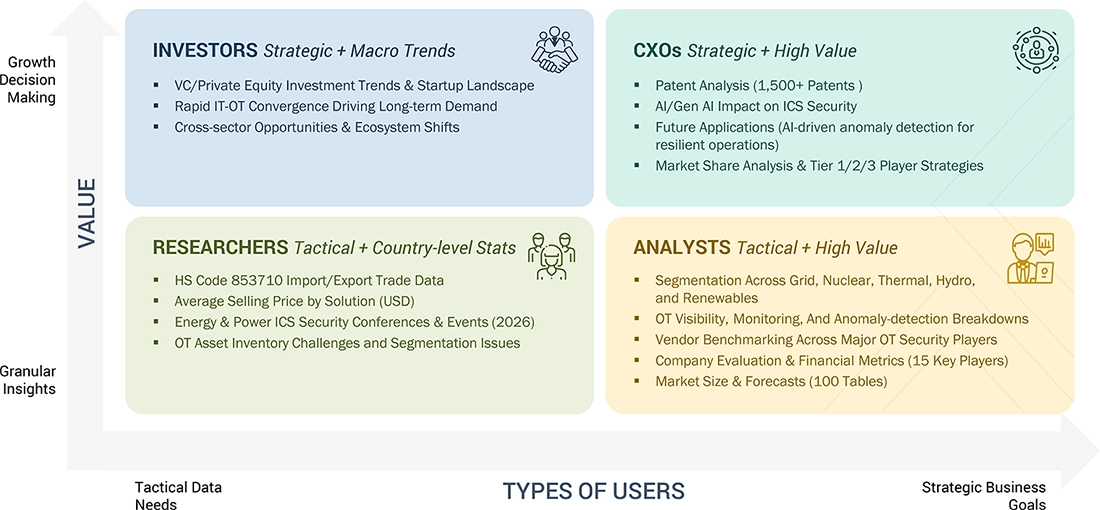
WHAT IS IN IT FOR YOU: INDUSTRIAL CONTROL SYSTEMS (ICS) SECURITY MARKET REPORT CONTENT GUIDE
DELIVERED CUSTOMIZATIONS
We have successfully delivered the following deep-dive customizations:
| CLIENT REQUEST | CUSTOMIZATION DELIVERED | VALUE ADDS |
|---|---|---|
| Leading Solution Provider (US) | Mapped how key vendors collectively shape the energy & power ICS security landscape through OT-focused visibility, substation and grid security, OT-vulnerability management, secure remote operations, AI-driven anomaly detection, and zero-trust IT/OT convergence. Highlighted capabilities supporting the protection of generation assets, transmission networks, distributed energy resources, and critical utility operations | Provides sector-aligned insights showing how major players secure power infrastructure, strengthens competitive analysis for utility cybersecurity initiatives, and enhances client understanding of vendor strengths across nuclear, thermal, hydro, renewables, transmission, and distribution operations. Supports strategic planning for grid modernization, regulatory compliance, and resilient energy-system cyber protection |
RECENT DEVELOPMENTS
- May 2025 : To deliver modernized, secure, and scalable infrastructure for Honeywell’s Integrated Control and Safety System (ICSS), Honeywell partnered with Nutanix, a leading provider of hybrid multi-cloud computing. While enhancing operational efficiency, cybersecurity, and resilience, this collaboration will also enable enterprises across critical sectors to accelerate digital transformation.
- Febraury 2024 : Cisco and Rockwell Automation partnered to accelerate digitalization, automation, cybersecurity, and workforce upskilling in the industrial sector.
- October 2023 : To offer live-fire simulation exercises tailored for OT, IT, IoT, and converged environments, Cloud Range and Fortinet collaborated within the Fortinet Fabric-Ready Technology Alliance Partner Program. This collaboration empowers cybersecurity teams with the capabilities to safeguard critical infrastructure and ICS against cyber threats while ensuring uptime and safety.
Table of Contents

Methodology
This study significantly estimated the current industrial control system (ICS) security market size. Exhaustive secondary research was done to collect information on the Industrial Control System (ICS) Security industry. The next step was to validate these findings, assumptions, and sizing with industry experts across the value chain using primary research. Different approaches, such as top-down and bottom-up, were employed to estimate the total market size. After that, the market breakup and data triangulation procedures were used to estimate the market size of the segments and subsegments of the industrial control system (ICS) security market.
Secondary Research
The market for the companies offering industrial control system (ICS) security solutions and services was arrived at by secondary data available through paid and unpaid sources, analyzing the product portfolios of the major companies in the ecosystem, and rating the companies by their performance and quality. Various sources were referred to in the secondary research process to identify and collect information for this study. The secondary sources included annual reports, press releases, investor presentations of companies, white papers, journals, certified publications, and articles from recognized authors, directories, and databases.
In the secondary research process, various secondary sources were referred to to identify and collect information related to the study. Secondary sources included annual reports, press releases, and investor presentations of industrial control system (ICS) security vendors, forums, certified publications, and whitepapers. The secondary research was used to obtain essential information on the industry’s value chain, the total pool of key players, market classification, and segmentation from the market and technology-oriented perspectives.
Primary Research
In the primary research process, various supply and demand sources were interviewed to obtain qualitative and quantitative information for this report. The primary sources from the supply side included industry experts, such as Chief Executive Officers (CEOs), Vice Presidents (VPs), marketing directors, technology and innovation directors, and related key executives from various key companies and organizations operating in the industrial control system (ICS) security market.
After the complete market engineering (calculations for market statistics, market breakdown, market size estimations, market forecasting, and data triangulation), extensive primary research was conducted to gather information and verify and validate the critical numbers arrived at. Primary research was also undertaken to identify the segmentation types, industry trends, competitive landscape of industrial control system (ICS) security solutions offered by various market players, and fundamental market dynamics, such as drivers, restraints, opportunities, challenges, industry trends, and key player strategies.
In the complete market engineering process, the top-down and bottom-up approaches and several data triangulation methods were extensively used to perform the market estimation and market forecasting for the overall market segments and subsegments listed in this report. Extensive qualitative and quantitative analysis was performed on the complete market engineering process to list the key information/insights throughout the report.
To know about the assumptions considered for the study, download the pdf brochure
Market Size Estimation
Top-down and bottom-up approaches were used to estimate and validate the size of the global industrial control system (ICS) security market and the size of various other dependent sub-segments. The research methodology used to estimate the market size included the following details: key players in the market were identified through secondary research, and their market shares in the respective regions were determined through primary and secondary research. This entire procedure included the study of the annual and financial reports of the top market players, and extensive interviews were conducted for key insights from the industry leaders, such as CEOs, VPs, directors, and marketing executives.
All percentage splits and breakdowns were determined using secondary sources and verified through primary sources. All possible parameters that affect the market covered in this research study were accounted for, viewed in extensive detail, verified through primary research, and analyzed to get the final quantitative and qualitative data. This data was consolidated and added to detailed input and analysis from MarketsandMarkets.
Data Triangulation
After arriving at the overall market size using the market size estimation processes explained above, the market was split into several segments and subsegments. The data triangulation and market breakup procedures were employed, wherever applicable, to complete the overall market engineering process and arrive at the exact statistics of each market segment and subsegment. The data was triangulated by studying various factors and trends from both the demand and supply sides.
Market Definition
According to Forcepoint, industrial control systems can consist of a complex network of interactive control systems or a small number of controllers. These systems receive information from remote sensors that measure and monitor process variables. From control valves to pressure gauges, an ICS sends commands and receives alerts from many different components. ICS security is a security framework that protects these systems against accidental or intentional breaches and risks.
ICS security solutions consist of a comprehensive array of technologies such as Distributed Denial of Service (DDoS), Intrusion Detection and Prevention System (IDPS), anti-malware/antivirus, firewall, virtualization security, Security Information and Event Management (SIEM), SCADA encryption, Unified Threat Management (UTM), Data Loss Prevention (DLP), and Identity and Access Management (IAM).
Stakeholders
- Anticorruption and antibribery heads
- Auditors
- Business resilience specialists
- Chief compliance officers
- Consulting firms
- Cybersecurity vendors
- Due diligence heads
- Ethics directors
- Government agencies
- ICS security solution vendors
- IT security agencies
- Investors and venture capitalists
- Operations officers
- Oversight officers
- Privacy specialists
- Research organizations
- Risk officers
- Software vendors
- Suppliers, distributors, and contractors
- System integrators
- Third-party providers
- Value-Added Resellers (VARs)
Report Objectives
- To define, describe, and forecast the industrial control system (ICS) security market based on offering, solution, service, security type, vertical, and region
- To forecast the market size of the five main regions: North America, Europe, Asia Pacific (APAC), Middle East & Africa (MEA), and Latin America
- To analyze the subsegments of the market concerning individual growth trends, prospects, and contributions to the overall market
- To provide detailed information related to the primary factors (drivers, restraints, opportunities, and challenges) influencing the growth of the market
- To analyze opportunities in the market for stakeholders by identifying high-growth segments of the market
- To profile the key players in the market and comprehensively analyze their market size and core competencies
- To track and analyze competitive developments, such as new product launches, mergers and acquisitions, partnerships, agreements, and collaborations in the industrial control system (ICS) security market
Available Customizations
With the given market data, MarketsandMarkets offers customizations based on company-specific needs. The following customization options are available for the report:
Geographic Analysis as per Feasibility
- Further breakup of the Asia Pacific market into countries contributing 75% to the regional market size
- Further breakup of the North American market into countries contributing 75% to the regional market size
- Further breakup of the Latin American market into countries contributing 75% to the regional market size
- Further breakup of the Middle Eastern and African market into countries contributing 75% to the regional market size
- Further breakup of the European market into countries contributing 75% to the regional market size
Company Information
- Detailed analysis and profiling of additional market players (up to 5)
Need a Tailored Report?
Customize this report to your needs
Get 10% FREE Customization
Customize This ReportPersonalize This Research
- Triangulate with your Own Data
- Get Data as per your Format and Definition
- Gain a Deeper Dive on a Specific Application, Geography, Customer or Competitor
- Any level of Personalization
Let Us Help You
- What are the Known and Unknown Adjacencies Impacting the Industrial Control Systems (ICS) Security Market
- What will your New Revenue Sources be?
- Who will be your Top Customer; what will make them switch?
- Defend your Market Share or Win Competitors
- Get a Scorecard for Target Partners
Custom Market Research Services
We Will Customise The Research For You, In Case The Report Listed Above Does Not Meet With Your Requirements
Get 10% Free CustomisationTESTIMONIALS














Growth opportunities and latent adjacency in Industrial Control Systems (ICS) Security Market