
Manufacturing Cybersecurity Market
Manufacturing Cybersecurity Market by Solution (IAM, Firewall, Log Management & SIEM, DLP, Compliance), Service (Professional, Managed), Security Type (Cloud, Application, Network), Manufacturing Type (Automotive, Chemicals) - Global Forecast to 2030




OVERVIEW

Source: Secondary Research, Interviews with Experts, MarketsandMarkets Analysis
The manufacturing cybersecurity market size is projected to grow from USD 10.97 billion in 2025 to USD 17.39 billion by 2030, at a compound annual growth rate (CAGR) of 9.7% during the forecast period. The increase in cyberattacks in industrial and OT systems is compelling manufacturers to enhance their protection against ransomware, espionage, and operational interruptions. Meanwhile, the adoption of Industry 4.0 and IIoT is fueling the connectivity between machines, systems, and supply chains, enlarging the attack surface. The integration of IT and OT space is driving the need to have sophisticated, real-time, and interconnected cybersecurity solutions.
KEY TAKEAWAYS
-
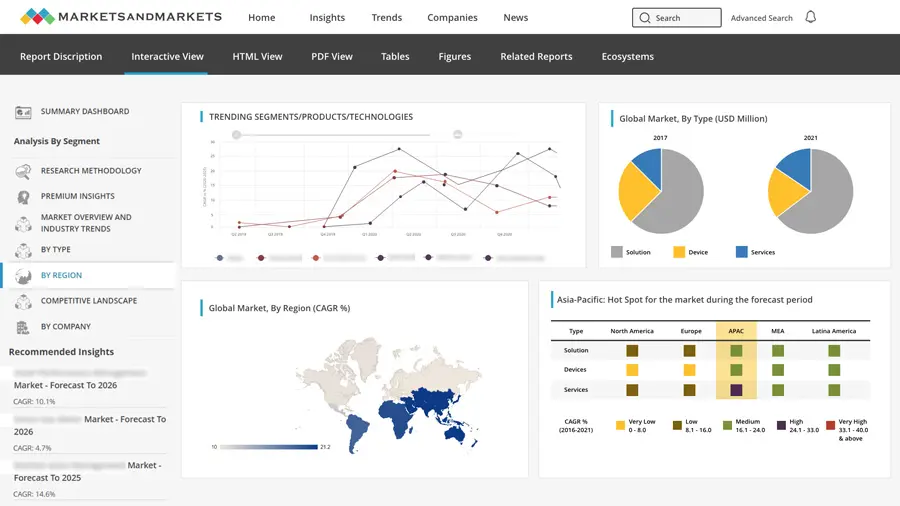
BY REGIONNorth America is estimated to account for a ~36% share of the manufacturing cybersecurity market in 2025.
-
BY OFFERINGThe services segment is expected to register the highest CAGR of 11.1% during the forecast period.
-
BY SOLUTION TYPEThe log management & SIEM segment is dominating the market.
-
BY SECURITY TYPEThe endpoint & IoT segment is expected to register the highest CAGR of 11.1% during the forecast period.
-
BY DEPLOYMENT MODECloud deployment of cybersecurity is projected to grow the fastest from 2025 to 2030.
-
BY MANUFACTURING TYPEThe pharmaceuticals and life sciences segment is projected to grow the fastest during the forecast period.
-
COMPETITIVE LANDSCAPE - KEY PLAYERSIBM, Cisco, Palo Alto Networks, Fortinet, Check Point, Microsoft, and Honeywell lead the manufacturing cybersecurity market, driven by strong IT–OT security portfolios and global presence.
-
COMPETITIVE LANDSCAPE - STARTUPSStartups such as Claroty, Dragos, Nozomi Networks, Xage Security, and Radiflow focus on OT and IIoT security, gaining traction in niche industrial segments.
The increasing exposure to risk is driving manufacturers to go beyond perimeter security to include continuous monitoring, identity of threats, and response capabilities. Organizations are giving priority to visibility of interrelated assets and investing in zero-trust and OT-specific solutions. Due to the rapid digital transformation, cybersecurity is increasingly necessary to provide continuity in production, secure intellectual property, and ensure trust in an increasingly interconnected manufacturing ecosystem.
TRENDS & DISRUPTIONS IMPACTING CUSTOMERS' CUSTOMERS
The manufacturing cybersecurity market is undergoing a shift from traditional, perimeter-based security toward integrated, intelligence-driven protection across IT, OT, and IIoT environments. As digital transformation accelerates, manufacturers are adopting advanced solutions such as identity security, threat detection, and OT-specific monitoring. Emerging use cases, new technologies, and ecosystem partnerships are reshaping revenue streams. This transition is driven by the need to ensure operational resilience, secure supply chains, and enable safe, connected, and data-driven manufacturing operations.

Source: Secondary Research, Interviews with Experts, MarketsandMarkets Analysis
MARKET DYNAMICS
Level
-
Rising cyberattacks on industrial and OT environments

-
Industry 4.0 and IIoT adoption
Level
-
Legacy systems and complex OT environments
-
High implementation costs and budget constraints
Level
-
Growth of managed security services (MSS) for manufacturing
-
Cloud-based security adoption in manufacturing
Level
-
Ensuring zero downtime in production environments
-
Supply chain and third-party risks
Source: Secondary Research, Interviews with Experts, MarketsandMarkets Analysis
Driver: Rising cyberattacks on industrial and OT environments
Manufacturing continues to be one of the most targeted sectors for cyberattacks, particularly ransomware and ICS-focused intrusions. Vendors such as Palo Alto Networks and IBM highlight increasing attacks on OT networks and production systems. Recent reports indicate manufacturing accounts for the largest share of ransomware incidents globally. Attackers exploit IT–OT convergence and legacy systems, pushing manufacturers to invest in real-time monitoring, threat detection, and incident response capabilities.
Restraint: Legacy systems and complex OT environments
Manufacturing facilities are based on the old industrial control systems that do not have built-in security and can be easily patched or updated. Vendors such as Cisco and Fortinet highlight that a significant portion of OT assets operate using older protocols with little visibility and control. The modern cybersecurity solutions are complicated to integrate because of proprietary systems and operational barriers. This fragmentation makes adoption slow, implementation costly, and makes it difficult to attain unified security in the IT and OT environments.
Opportunity: Growth of managed security services (MSS) for manufacturing
The lack of qualified OT cybersecurity experts and the growing complexity of threats are fueling the demand for managed security services. Manufacturing-focused industrial SOC and MDR offerings are being expanded by vendors like IBM and Atos. A large number of manufacturers are moving towards outsourced monitoring and incident response in order to have round-the-clock protection. This trend is allowing the rapid implementation of advanced security features and burdening internal teams with less operational work.
Challenge: Ensuring zero downtime in production environments
The manufacturing processes need constant uptime; it is not easy to implement security measures that can interrupt production. Vendors like Honeywell and Nozomi Networks emphasize that even regular patching or network modifications might affect safety and production. Security solutions should be passive with the ability to blend with the industrial processes without introducing any latency. The need to balance between high security and continuous production is a key issue, particularly in well-automated and time-driven production systems.
MANUFACTURING CYBERSECURITY MARKET: COMMERCIAL USE CASES ACROSS INDUSTRIES
| COMPANY | USE CASE DESCRIPTION | BENEFITS |
|---|---|---|
 |
Lack of real-time threat visibility, ransomware risks in production systems, lateral movement across IT-OT networks, and fragmented security monitoring. | Faster threat detection, reduced dwell time, improved incident response, enhanced operational resilience |
 |
Unauthorized access to industrial systems, insecure remote access to plant operations, poor network segmentation, and identity management gaps. | Reduced unauthorized access, secure remote connectivity, improved segmentation, stronger access control, enhanced compliance |
 |
Unsecured industrial networks, lack of segmentation across plants, complex distributed infrastructure, and limited threat visibility. | Unified visibility, improved threat prevention, reduced operational complexity, enhanced compliance, secure production environments |
 |
Lack of asset visibility in OT environments, unknown vulnerabilities in ICS systems, limited monitoring of industrial networks, and high operational risk. | Enhanced asset visibility, reduced attack surface, improved risk management, secure OT operations, minimized disruptions |
 |
Limited visibility into IIoT devices, inability to detect anomalies in real time, lack of network monitoring, and exposure to cyber-physical risks. | Real-time anomaly detection, improved operational visibility, reduced downtime, stronger security posture, proactive risk mitigation |
Logos and trademarks shown above are the property of their respective owners. Their use here is for informational and illustrative purposes only.
MARKET ECOSYSTEM
The manufacturing cybersecurity market ecosystem is a combination of the IT security vendors across the world, OT-based experts, and service integrators to deal with emerging industrial risks. Solutions to secure converged IT-OT environments are offered by vendors in identity management, threat protection, SIEM, network security, and data protection. With the increased adoption of Industry 4.0 and IIoT, the ecosystem is expanding to encompass dedicated players that provide asset visibility, threat detection, and resilience to critical manufacturing processes.

Logos and trademarks shown above are the property of their respective owners. Their use here is for informational and illustrative purposes only.
MARKET SEGMENTS

Source: Secondary Research, Interviews with Experts, MarketsandMarkets Analysis
Manufacturing Cybersecurity Market, by Offering
The solutions segment occupies the largest market share since manufacturers are more focused on investing in more sophisticated technologies like AI-assisted threat detection, OT security, and industrial asset visibility. As Industry 4.0 emerges, companies are moving to integrated IT-OT security platforms to achieve real-time monitoring and resiliency. Moreover, rising cyber threats and business continuity are leading to an increase in investment in security tools in production settings.
Manufacturing Cybersecurity Market, by Solution Type
Log management and SIEM is the leading segment due to the need for centralized visibility across IT and OT environments. Manufacturers need to monitor the industry processes in real-time, identify anomalies, and meet the industry standards. Since operations are ongoing, SIEM solutions allow a single view of the network, endpoint, and industrial assets. This helps to detect and respond to threats more quickly in distributed manufacturing facilities.
Manufacturing Cybersecurity Market, by Security Type
Network security remains the leading category of expenditure among manufacturing enterprises that are concerned with the protection of converged IT-OT systems and secure communication between the industrial systems. Firewalls, secure gateways, and Zero Trust architectures are in demand because of the need to segment, provide secure remote access, and prevent ransomware. Ongoing cyber threats and supply chain risks also strengthen the importance of robust network security solutions.
Manufacturing Cybersecurity Market, by Deployment Mode
On-premises holds the largest market share, since critical OT environments require low latency, high reliability, and strict control over operations. Industrial systems are usually highly intolerant of disruptions, requiring on-premise deployment. As digital deployments grow, hybrid and cloud-based solutions are becoming increasingly popular, allowing manufacturers to create a balance between operational control and scalability as well as centralized security control.
Manufacturing Cybersecurity Market, by Organization Size
Large manufacturing enterprises hold the largest share of the market as they operate complex, highly automated environments with extensive IT–OT integration and global supply chains. These companies are more vulnerable to cybercrime, such as ransomware and industrial espionage, which leads to large-scale investments in highly sophisticated security systems, real-time surveillance, and compliance systems. Besides, big businesses can afford to use integrated security platforms and managed services.
Manufacturing Cybersecurity Market, by Manufacturing Type
Automotive and transportation equipment manufacturing holds a significant share of cybersecurity spending due to high automation, connected systems, and complex supply chains. Such environments are very vulnerable to ransomware, theft of intellectual property, and disruption of operations. In turn, manufacturers are shifting the focus to investments in OT security, real-time monitoring, and supply chain risk management to maintain production stability and secure the assets.
REGION
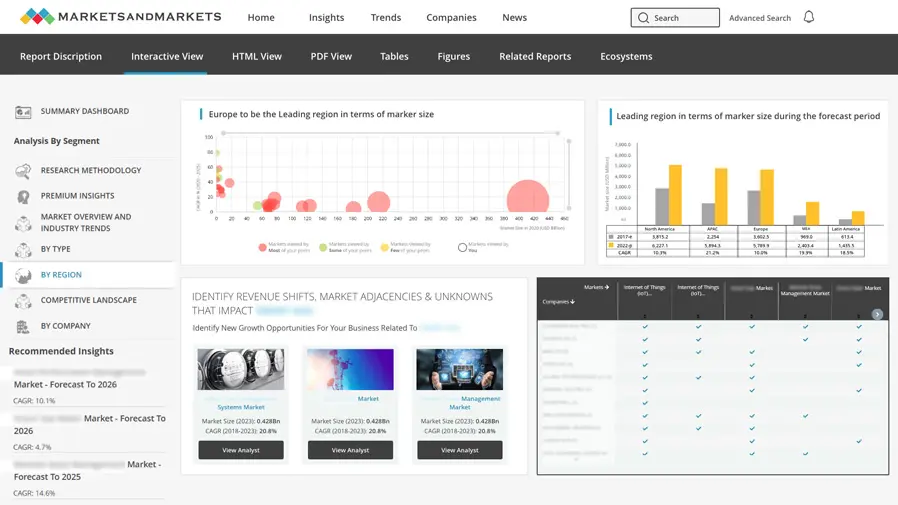
Asia Pacific is the fastest-growing region in the global manufacturing cybersecurity market during the forecast period
The fastest-growing market in manufacturing cybersecurity is Asia Pacific due to the high rate of industrialization, the growth of smart factory programs, and the high rates of Industry 4.0 technology adoption in China, Japan, South Korea, and India. Governments are enhancing regulations on critical infrastructure protection and cybersecurity, which are encouraging investments. The high manufacturing infrastructure and the rising cyberattacks on industrial systems are driving the need of OT and IIoT security, real-time monitoring, and managed security services in various industries.
MANUFACTURING CYBERSECURITY MARKET: COMPANY EVALUATION MATRIX
The manufacturing cybersecurity market features a mix of established IT security vendors and specialized OT-focused players addressing industrial risks. Leaders such as Palo Alto Networks and Claroty deliver comprehensive capabilities across threat detection, network visibility, and OT security monitoring, while other vendors expand portfolios across identity, data, and cloud security. Market momentum is driven by IT-OT convergence, AI-driven threat detection, and the need for continuous monitoring and operational resilience across connected industrial environments.

Source: Secondary Research, Interviews with Experts, MarketsandMarkets Analysis
KEY MARKET PLAYERS
- Cisco (US)
- Microsoft (US)
- IBM (US)
- Palo Alto Networks (US)
- Fortinet (US)
- Microsoft (US)
- CrowdStrike (US)
- Check Point (Israel)
- Fujitsu (Japan)
- Trend Micro (Japan)
- Hexagon AB (Sweden)
- Honeywell (US)
- Claroty (US)
- Dragos (US)
- Nozomi Networks (Switzerland)
- SCADAfence (Israel)
- Xage Security (US)
MARKET SCOPE
| REPORT METRIC | DETAILS |
|---|---|
| Market Size, 2024 (Value) | USD 9.93 Billion |
| Market Forecast, 2030 (Value) | USD 17.39 Billion |
| Growth Rate | CAGR of 9.7% from 2025 to 2030 |
| Years Considered | 2019–2030 |
| Base Year | 2024 |
| Forecast Period | 2025–2030 |
| Units Considered | Value (USD Million/Billion) |
| Report Coverage | Revenue Forecast, Company Ranking, Competitive Landscape, Growth Factors, and Trends |
| Segments Covered |
|
| Regions Covered | North America, Asia Pacific, Europe, Middle East & Africa, Latin America |
WHAT IS IN IT FOR YOU: MANUFACTURING CYBERSECURITY MARKET REPORT CONTENT GUIDE

DELIVERED CUSTOMIZATIONS
We have successfully delivered the following deep-dive customizations:
| CLIENT REQUEST | CUSTOMIZATION DELIVERED | VALUE ADDS |
|---|---|---|
| Leading Solution Provider (US) | Product Analysis: Manufacturing Cybersecurity Solution Matrix - comparing vendors across network, cloud, endpoint, identity, data security, SIEM/log management, XDR, threat intelligence, Zero Trust, OT/IoT security, vulnerability analytics, and SOC automation, along with deployment flexibility across cloud, hybrid, and on-premise models | Enabled clearer visibility into competitive positioning, product breadth, integration maturity, and automation strength to support strategic portfolio decisions, roadmap planning, and multi-year cybersecurity modernization initiatives across manufacturing sectors |
RECENT DEVELOPMENTS
- November 2025 : Claroty expanded its industrial visibility portfolio with advanced risk analytics and automated remediation to strengthen OT security and operational resilience.
- September 2025 : Dragos enhanced its OT security platform with improved incident response, cloud telemetry, and real-time threat intelligence to support industrial and manufacturing environments.
- April 2025 : Cisco introduced upgraded industrial security capabilities, extending OT telemetry and asset visibility across connected production systems and supply chains to improve monitoring and governance.
- March 2024 : Nozomi Networks partnered with Mitsubishi Electric to integrate its OT and IIoT cybersecurity capabilities into industrial automation systems, strengthening real-time monitoring and protection for manufacturing environments.
Table of Contents

Methodology
Secondary research was conducted to collect information useful for this technical, market-oriented, and commercial study of the global Manufacturing Cybersecurity Market. The next step was to validate these findings, assumptions, and sizing with industry experts across the value chain using primary research. Different approaches, such as top-down and bottom-up, were employed to estimate the total market size. After that, the market breakup and data triangulation procedures were used to estimate the market size of the segments and subsegments of the Manufacturing Cybersecurity Market.
Secondary Research
In the secondary research process, various secondary sources were referred to for identifying and collecting information regarding the study. The secondary sources included annual reports, press releases, investor presentations of cybersecurity solution and service vendors, forums, certified publications, and whitepapers. The secondary research was mainly used to obtain key information about the industry’s supply chain, the total pool of key players, market classification and segmentation according to industry trends to the bottom-most level, regional markets, and key developments from both market- and technology-oriented perspectives, all of which were further validated by primary sources.
Primary Research
In the primary research process, various primary sources from both the supply and demand sides were interviewed to obtain qualitative and quantitative information for this report. The primary sources from the supply side included various industry experts, including Chief Executive Officers (CEOs), Vice Presidents (VPs), marketing directors, technology and innovation directors, and related key executives from various key companies and organizations operating in the Manufacturing Cybersecurity Market.
In the market engineering process, top-down and bottom-up approaches were extensively used, along with several data triangulation methods, to perform the market estimation and market forecasting for the overall market segments and subsegments listed in this report. Extensive qualitative and quantitative analysis was performed on the complete market engineering process to list key information/insights throughout the report.
After the complete market engineering process (including calculations for market statistics, market breakups, market size estimations, market forecasts, and data triangulation), extensive primary research was conducted to gather information and verify & validate the critical numbers arrived at. The primary research was also conducted to identify the segmentation, industry trends, competitive landscape of Manufacturing Cybersecurity Market players, and key market dynamics, such as drivers, restraints, opportunities, challenges, industry trends, and key strategies.

To know about the assumptions considered for the study, download the pdf brochure
Market Size Estimation
Top-down and bottom-up approaches were used to estimate and validate the size of the Manufacturing Cybersecurity Market and the size of various dependent sub-segments in the overall Manufacturing Cybersecurity Market. The research methodology used to estimate the market size includes the following details: critical players in the market were identified through secondary research, and their market shares in the respective regions were determined through primary and secondary research. This entire procedure included the study of the annual and financial reports of the top market players, and extensive interviews were conducted for key insights from the industry leaders, such as CEOs, VPs, directors, and marketing executives.
All percentage splits and breakdowns were determined using secondary sources and verified through primary sources. All possible parameters that affect the market covered in this research study have been accounted for, viewed in extensive detail, verified through primary research, and analyzed to get the final quantitative and qualitative data. This data is consolidated and added to detailed input and analysis from MarketsandMarkets.

Data Triangulation
The market was split into several segments and subsegments after arriving at the overall market size using the market size estimation processes explained above. The data triangulation and market breakup procedures were employed, wherever applicable, to complete the overall market engineering process and arrive at the exact statistics of each market segment and subsegment. The data was triangulated by studying various factors and trends from both the demand and supply sides.
Market Definition
According to MarketsandMarkets, cybersecurity is a set of technologies, processes, and practices to fortify critical systems, such as networks, physical devices, programs, and information, from unauthorized access, insider threats, and malicious attacks. These cyberattacks can affect data transmission across the networks, cause operational disruptions, and result in money extortion/ransomware. Cybersecurity, or information security, can be provided through hardware, software, and services.
Stakeholders
- Chief Technology and Data Officers
- Consulting Service Providers
- Managed Security Services Professionals
- Business Analysts
- Information Technology (IT) Professionals
- Government Agencies
- Investors and Venture Capitalists
- Small and Medium-sized Enterprises (SMEs) and Large Enterprises
- Third-party Providers
- Consultants/Consultancies/Advisory Firms
- Managed and Professional Service Providers
Report Objectives
- To describe and forecast the global Manufacturing Cybersecurity Market by offering, solution type, security type, deployment mode, organization size, vertical, and region from 2025 to 2030, and analyze the various macroeconomic and microeconomic factors that affect Manufacturing Cybersecurity Market growth
- To forecast the market size of five main regions: North America, Europe, Asia Pacific, the Middle East & Africa, and Latin America
- To analyze the subsegments of the market with respect to individual growth trends, prospects, and contributions to the overall market
- To provide detailed information regarding major factors (drivers, restraints, opportunities, and challenges) influencing the growth of the market
- To analyze opportunities in the market for stakeholders and provide details of the competitive landscape of major players
- To profile key market players; provide a comparative analysis based on the business overviews, regional presence, product offerings, business strategies, and key financials; and illustrate the competitive landscape of the marketTo analyze competitive developments, such as mergers & acquisitions, product developments, partnerships and collaborations, and research & development (R&D) activities, in the market
Available Customizations
With the given market data, MarketsandMarkets offers customizations based on company-specific needs. The following customization options are available for the report:
Geographic Analysis as per Feasibility
- Further breakup of the Asia Pacific Manufacturing Cybersecurity Market into countries contributes to the rest of the regional market size
- Further breakup of the North American Manufacturing Cybersecurity Market into countries contributes to the rest of the regional market size
- Further breakup of the Latin American Manufacturing Cybersecurity Market into countries contributing to the rest of the regional market size
- Further breakup of the Middle East & African Manufacturing Cybersecurity Market into countries contributing to the rest of the regional market size
- Further breakup of the European Manufacturing Cybersecurity Market into countries contributes to the rest of the regional market size
Company Information
- Detailed analysis and profiling of additional market players (up to 5)
Need a Tailored Report?
Customize this report to your needs
Get 10% FREE Customization
Customize This ReportPersonalize This Research
- Triangulate with your Own Data
- Get Data as per your Format and Definition
- Gain a Deeper Dive on a Specific Application, Geography, Customer or Competitor
- Any level of Personalization
Let Us Help You
- What are the Known and Unknown Adjacencies Impacting the Manufacturing Cybersecurity Market
- What will your New Revenue Sources be?
- Who will be your Top Customer; what will make them switch?
- Defend your Market Share or Win Competitors
- Get a Scorecard for Target Partners
Custom Market Research Services
We Will Customise The Research For You, In Case The Report Listed Above Does Not Meet With Your Requirements
Get 10% Free CustomisationTESTIMONIALS













Growth opportunities and latent adjacency in Manufacturing Cybersecurity Market