
Perimeter Security Market Size, Share, Growth, Latest Trends
Perimeter Security Market, by Component (Systems and Services), System (Perimeter Intrusion Detection Systems, Video Surveillance Systems, Access Control Systems, Alarm & Notification Systems, Barrier Systems, and Others), Service (Professional Services and Managed Services), End-use Sector, and Region - Global Forecast to 2031




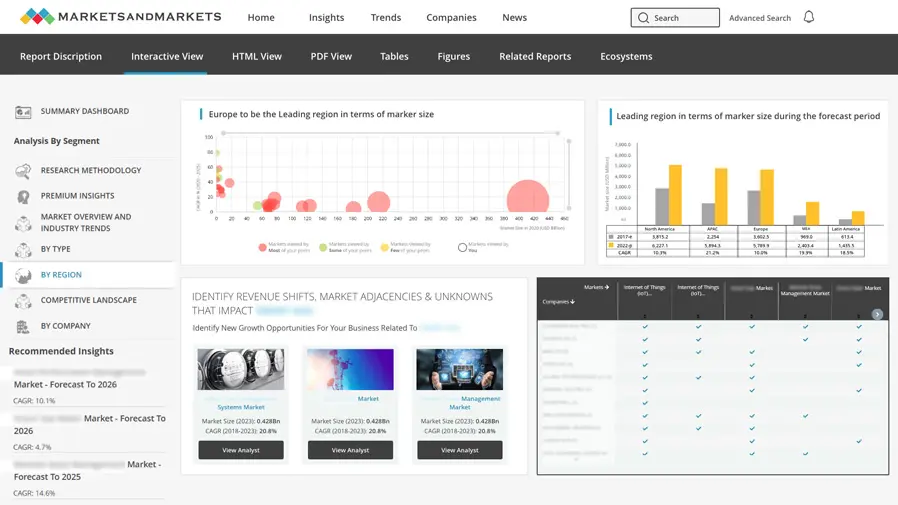
OVERVIEW
Source: Secondary Research, Interviews with Experts, MarketsandMarkets Analysis
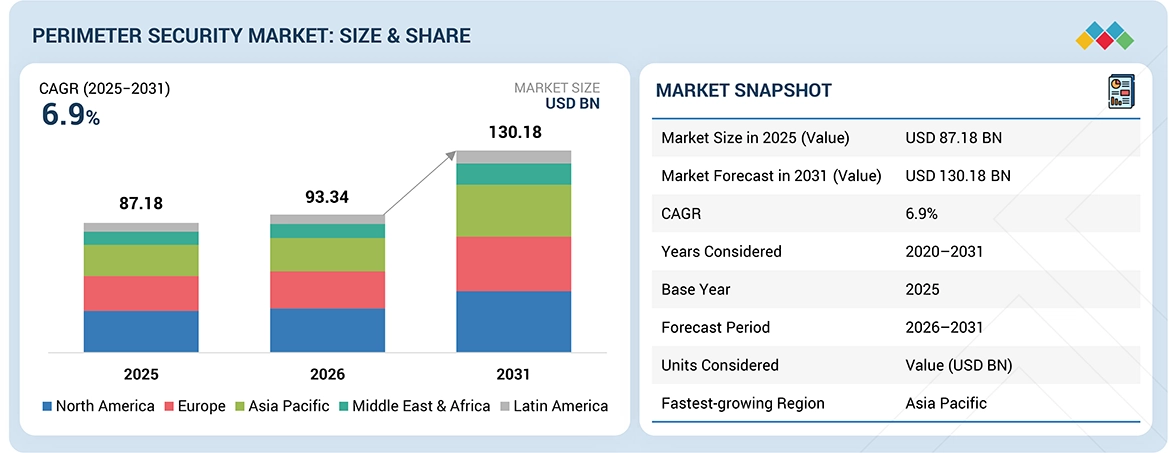
The perimeter security market is projected to reach USD 130.18 billion by 2031 from USD 93.34 billion in 2026, at a CAGR of 6.9% from 2025 to 2031. The growing risks to critical infrastructure, including power plants, airports, transportation hubs, and government facilities, are driving a greater demand of more robust perimeter protection. These environments deal with sensitive operations and high volumes of people moving around and are therefore easy targets to be intruded, sabotaged or disrupted. Consequently, companies are implementing state-of-the-art surveillance, intrusion detection, and access control systems.
KEY TAKEAWAYS
-
BY REGIONNorth America accounted for the largest share of 31.8% of the perimeter testing market in 2025.
-
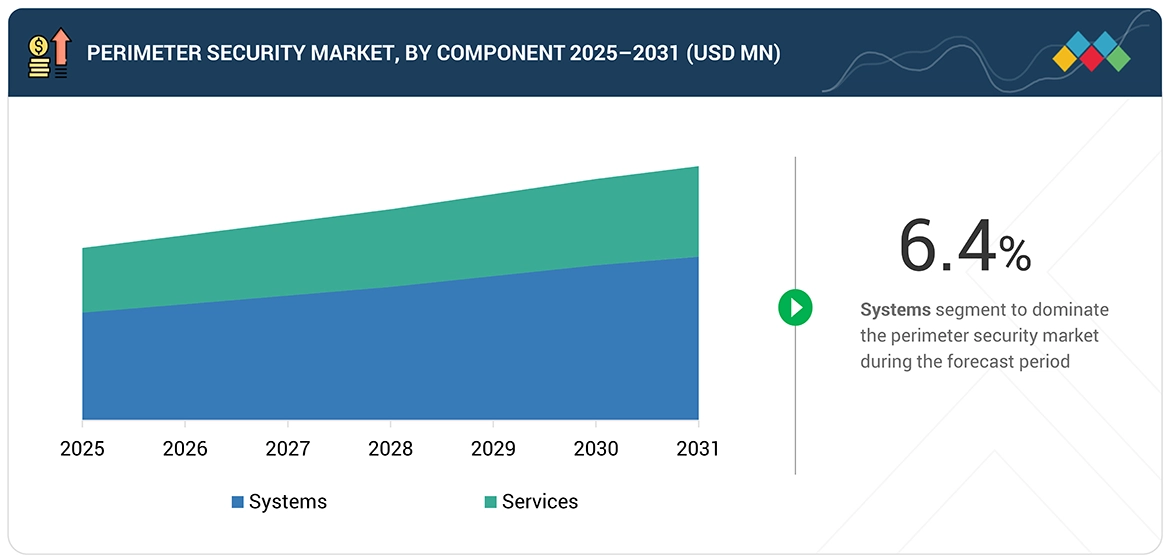
BY OFFERINGBy offering, the systems segment is expected to dominate the market, accounting for the highest market share of 61.2% in 2025.
-
BY SYSTEMBy system, the video surveillance systems segment is expected to dominate the market during the forecast period.
-
BY SERVICESBy service, the professional services segment is expected to account for the largest market share during the forecast period.
-
BY VERTICALBy vertical, the commercial segment will grow at the highest CAGR of 7.3% during the forecast period.
-
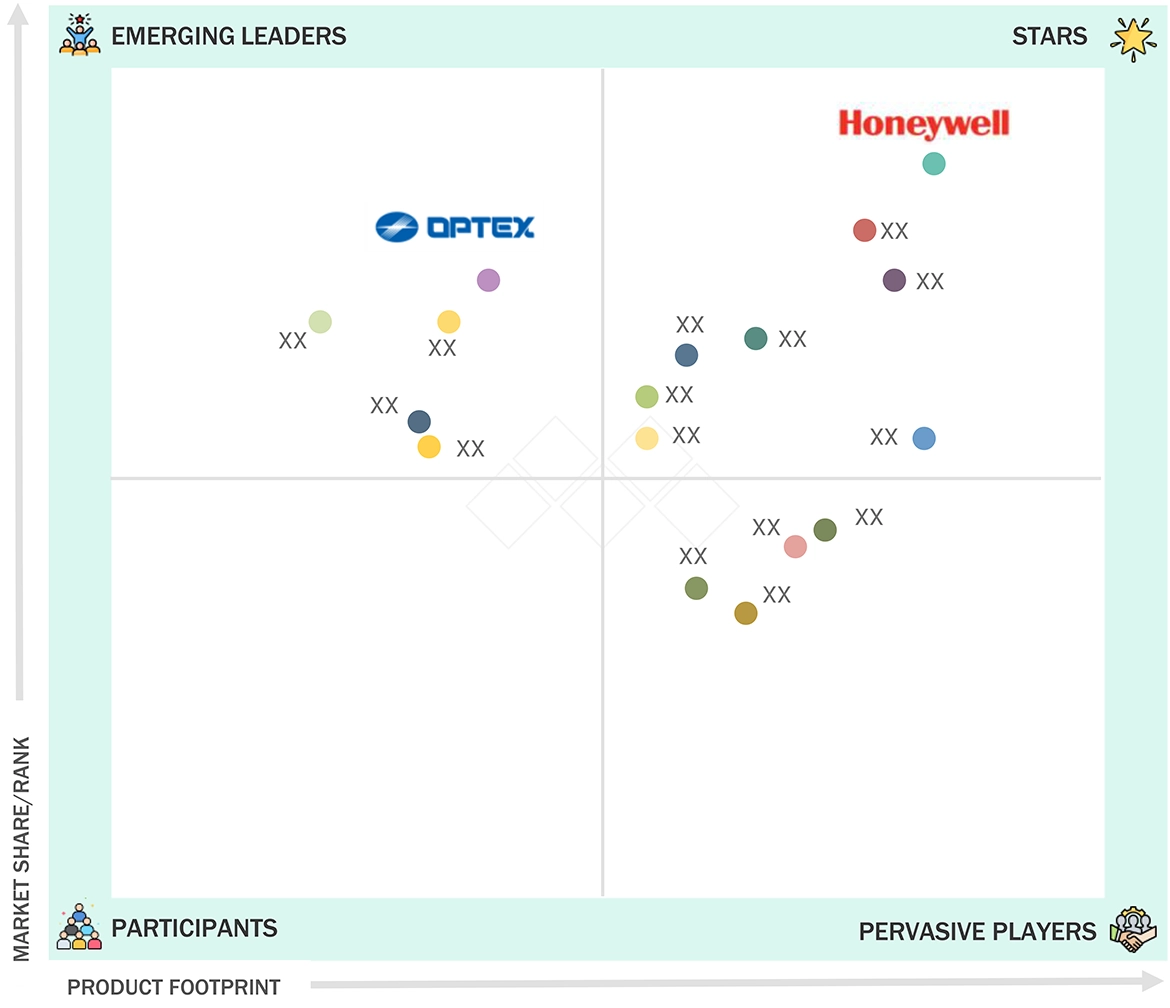
COMPETITIVE LANDSCAPE - KEY PLAYERSKey players in the perimeter security market are Honeywell, Bosch Security Systems, and Optex, which provide features in video surveillance systems, perimeter intrusion detection systems, access control systems, and integrated security monitoring systems. Their products help organizations to identify unauthorized access, track facility perimeters, and enhance security in critical infrastructure, industrial plants, business campuses, and transportation centers.
-
COMPETITIVE LANDSCAPE - STARTUPSNew entrants such as Kisi, Barrier1, and PivotChain are enhancing the perimeter security environment with new access control technology, intelligent barrier systems, and integrated security systems. These solutions assist organizations to enhance access management of their facilities, automate perimeter monitoring and improve security operations to meet the increasing need of flexible and modern perimeter protection in both commercial and enterprise settings.
To secure their assets and operations, enterprises are enhancing perimeter security in corporate campuses, manufacturing plants, data centers, and logistics centers. With the growing physical infrastructure, organizations are implementing surveillance, intrusion detection, and access control systems to enhance monitoring and to avoid unauthorized access.
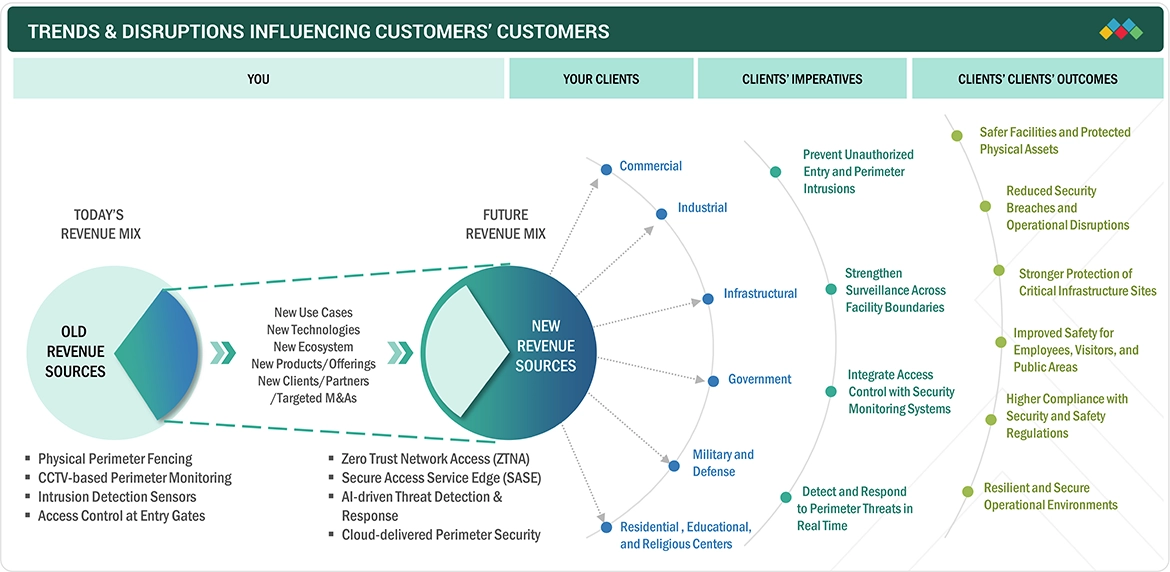
TRENDS & DISRUPTIONS IMPACTING CUSTOMERS' CUSTOMERS
The perimeter security market is evolving as organizations work to enhance security around critical facilities and large campuses. Intelligent surveillance systems, intrusion detection technologies, and integrated access control platforms are increasingly complementing traditional fencing and CCTV systems. Rising security threats are driving demand for real-time monitoring solutions to prevent unauthorized access, protect infrastructure, and improve overall operational safety.
Source: Secondary Research, Interviews with Experts, MarketsandMarkets Analysis
MARKET DYNAMICS
Level
-
Increasing security breaches and perimeter intrusions worldwide

-
Rising demand for perimeter intrusion detection systems
Level
-
Lack of technical expertise.
-
High investment and maintenance costs
Level
-
Increasing rate of automation and industrial deployments
-
Growing focus on smart city projects
Level
-
High installation cost
-
Rising incidents of false alarm triggers
Source: Secondary Research, Interviews with Experts, MarketsandMarkets Analysis
Driver: Increasing security breaches and perimeter intrusions worldwide
The rising number of unauthorized access attempts, vandalism, and security breaches in industrial facilities, commercial complexes, and critical infrastructure is fueling the need to implement more sophisticated perimeter security systems. Companies are implementing surveillance cameras, intrusion detection sensors, and access control systems to enhance the security of their facilities and to identify potential threats before they affect operations.
Restraint: Lack of technical expertise
The effective implementation and operation of advanced perimeter security systems require specialized expertise in surveillance analytics, intrusion detection technologies, and integrated security platforms. Recruiting and retaining qualified professionals who can manage complex security infrastructure is a challenge for many organizations and can delay the implementation and optimal use of current perimeter security solutions.
Opportunity: Increasing rate of automation and industrial deployments
The increasing use of automation in manufacturing plants, logistics centers, and industrial facilities is providing new opportunities for perimeter security solutions. Large industrial environments are increasingly being secured with automated monitoring systems, intelligent surveillance technologies, and sensor-based intrusion detection platforms to provide continuous monitoring, enhanced operational safety, and better protection of high-value assets.
Challenge: High installation cost
The use of perimeter security systems can be costly due to the initial investment in surveillance cameras, intrusion detection devices, access control systems, and monitoring systems. Installation in large facilities or complex infrastructure environments can be expensive, especially when multiple security technologies are used, which may restrict its use by small and mid-sized organizations with limited budgets.
PERIMETER SECURITY MARKET SIZE, SHARE, GROWTH, LATEST TRENDS: COMMERCIAL USE CASES ACROSS INDUSTRIES
| COMPANY | USE CASE DESCRIPTION | BENEFITS |
|---|---|---|
 |
Deployment of AI-enabled perimeter surveillance systems combining video analytics, motion detection, and integrated access control to monitor restricted facilities such as industrial plants, logistics hubs, and critical infrastructure sites. | Early threat detection, reduced unauthorized access incidents, improved operational visibility, and enhanced protection of critical assets. |
 |
Implementation of intelligent perimeter protection using thermal cameras, radar sensors, and AI video analytics to detect intrusions along facility boundaries in sectors such as transportation, commercial campuses, and public infrastructure. | Real-time intrusion detection, reduced false alarms, improved situational awareness, and strengthened perimeter defense. |
 |
Integration of perimeter security with building management systems through smart access control, surveillance cameras, and automated alerting to secure corporate campuses, data centers, and critical facilities. | Centralized security monitoring, faster incident response, improved compliance with safety regulations, and stronger facility protection. |
Logos and trademarks shown above are the property of their respective owners. Their use here is for informational and illustrative purposes only.
MARKET ECOSYSTEM
The perimeter security ecosystem comprises technology vendors that offer solutions in access control, video surveillance, alarm and notification systems, and perimeter intrusion detection. These systems collaborate to track facility boundaries, detect unauthorized access, and enable real-time security responses to help organizations secure critical infrastructure, commercial facilities, and large operating environments.

Logos and trademarks shown above are the property of their respective owners. Their use here is for informational and illustrative purposes only.
MARKET SEGMENTS
Source: Secondary Research, Interviews with Experts, MarketsandMarkets Analysis
Perimeter Security Market, by Component
Systems represent the largest segment within the component category due to the widespread use of surveillance cameras, intrusion detection systems, access control systems, and perimeter barriers in various facilities. Companies are prioritizing these systems to monitor boundaries, detect unauthorized access, and improve the physical protection of critical infrastructure, business campuses, and industrial environments.
Perimeter Security Market, by System
Video surveillance systems constitute the largest segment of perimeter security due to their widespread use for monitoring facility borders and detecting suspicious activity. To improve visibility, support incident response, and enhance overall perimeter security, companies are increasingly deploying smart cameras and analytical solutions in transportation hubs, factories, and business premises.
Perimeter Security Market, by Service
Professional services make up the largest share of the perimeter security services segment. Organizations are increasingly seeking expertise to integrate systems, perform security testing, and install complex security solutions. These services help businesses develop effective perimeter protection strategies, including implementing surveillance and intrusion detection systems and ensuring consistent, reliable security practices.
Perimeter Security Market, by Vertical
The commercial sector holds the largest share of the perimeter security market, with shopping complexes, corporate campuses, data centers, and office buildings investing heavily in advanced security systems. Companies employ surveillance, access control, and intrusion detection systems to prevent unauthorized access, protect assets, and ensure safe conditions for employees and visitors alike.
REGION
Asia Pacific to be fastest-growing region in global perimeter security market during forecast period
The Asia Pacific region is the fastest-growing market for perimeter security, driven by rapid urbanization, infrastructure development, and rising security concerns in public and industrial facilities. The rise in investment in smart cities, transportation hubs, and the protection of critical infrastructure is driving the enhanced implementation of surveillance systems, intrusion detection technologies, and integrated access control solutions across the region.

PERIMETER SECURITY MARKET SIZE, SHARE, GROWTH, LATEST TRENDS: COMPANY EVALUATION MATRIX
Honeywell (Star Player) is a market leader in the perimeter security market with an extensive portfolio of video surveillance systems, access control platforms, perimeter intrusion detection technologies, and integrated security monitoring solutions, and with robust global deployment capabilities. Optex (Emerging Player) is enhancing its presence with superior sensing technologies, outdoor intrusion detection systems, and perimeter monitoring solutions to help protect facilities in commercial, industrial, and critical infrastructure settings.
Source: Secondary Research, Interviews with Experts, MarketsandMarkets Analysis
KEY MARKET PLAYERS
- Honeywell (US)
- Dahua Technology (China)
- Bosch Security Systems (Germany)
- Hikvision (China)
- Axis Communications (Sweden)
- Senstar (Canada)
- Pelco (US)
- Raytheon Technologies (US)
- Teledyne FLIR (US)
- Thales (France)
- Johnson Controls (Ireland)
- Fiber Sensys (US)
- Ameristar Perimeter Security (US)
- Optex (Japan)
- Panasonic (Japan)
- Southwest Microwave (US)
- Avigilon (Canada)
- Advanced Perimeter Systems (UK)
- CIAS (Italy)
- Gallagher (New Zealand)
- Ingersoll Rand (US)
- Infinova (US)
- RBtec Perimeter Security Systems (Israel)
- Sorhea (France)
- PureTech Systems (US)
- SightLogix (US)
- Scylla (US)
- Veesion (France)
- PivotChain (US)
- Prisma Photonics (Israel)
- Openpath (US)
- Density (US)
- Barrier1 Systems (US)
- Alcatraz (US)
- Kisi (US)
MARKET SCOPE
| REPORT METRIC | DETAILS |
|---|---|
| Market Size in 2026 (Value) | USD 93.34 Billion |
| Market Forecast in 2031 (Value) | USD 130.18 Billion |
| Growth Rate | CAGR of 6.9% from 2025–2031 |
| Years Considered | 2019–2031 |
| Base Year | 2025 |
| Forecast Period | 2026–2031 |
| Units Considered | Value (USD Billion) |
| Report Coverage | Revenue Forecast, Company Ranking, Competitive Landscape, Growth Factors, and Trends |
| Segments Covered |
|
| Regions Covered | North America, Europe, Asia Pacific, Middle East & Africa, Latin America |
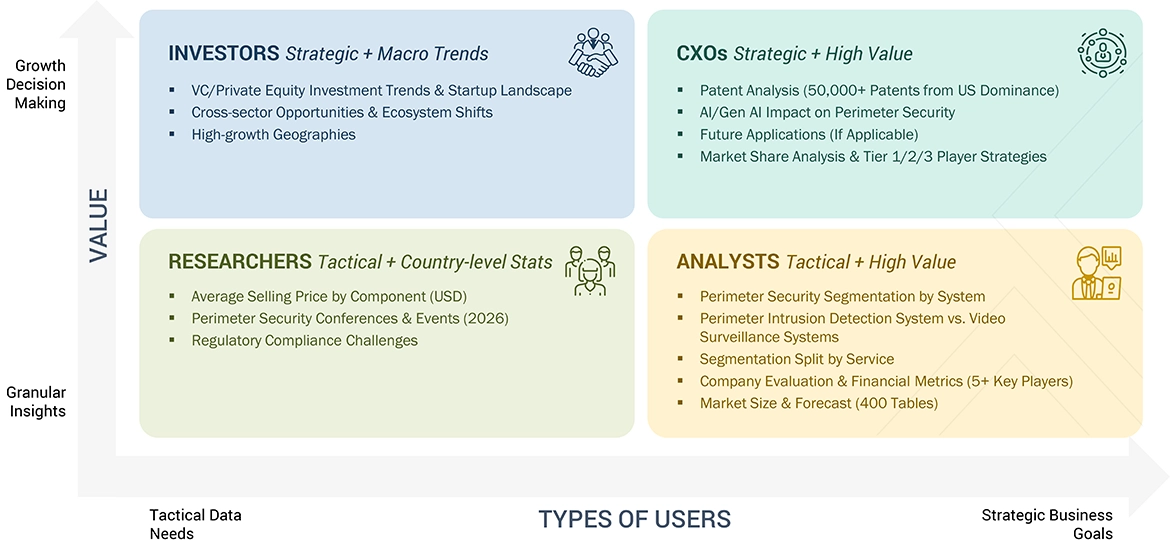
WHAT IS IN IT FOR YOU: PERIMETER SECURITY MARKET SIZE, SHARE, GROWTH, LATEST TRENDS REPORT CONTENT GUIDE
DELIVERED CUSTOMIZATIONS
We have successfully delivered the following deep-dive customizations:
| CLIENT REQUEST | CUSTOMIZATION DELIVERED | VALUE ADDS |
|---|---|---|
| Leading Solution Provider (US) | Product analysis of the perimeter security market, including a detailed comparison of vendors’ capabilities across video surveillance systems, perimeter intrusion detection technologies, access control platforms, alarms and notification systems, automation integration, monitoring capabilities, and deployment flexibility across large facilities and critical infrastructure environments. | Enhanced understanding of competitive positioning in perimeter security technologies, depth of surveillance and intrusion detection capabilities, system integration maturity, and facility level monitoring coverage, supporting strategic investment decisions, product portfolio alignment, and long term physical security strategy development. |
| Leading Service Provider (EU) | Comprehensive profiling and evaluation of perimeter security vendors and system integrators, covering surveillance technologies, intrusion detection solutions, access control systems, infrastructure protection frameworks, regional deployment capabilities, managed security services, and strategic partnerships across industrial facilities, transportation infrastructure, and commercial campuses. | Clear view of the evolving perimeter security solutions landscape, highlighting growth in integrated surveillance systems, increasing demand for intelligent perimeter monitoring technologies, vendor differentiation in facility protection capabilities, and expansion opportunities driven by infrastructure security investments and urban safety initiatives. |
RECENT DEVELOPMENTS
- November 2025 : F5 and CrowdStrike entered into a partnership to make the CrowdStrike Falcon Sensor a direct part of the F5 BIG-IP portfolio of network operations hardware and software. This partnership allows AI-led detection and response features at the network perimeter to assist organizations in securing sensitive API traffic and protecting advanced threats beyond traditional endpoints.
- February 2025 : Genetec has increased its technology collaboration with Bosch to enable Bosch intrusion panels to be used in the Genetec Security Center SaaS platform. The integration allows the management of intrusion detection, video surveillance, and access control systems to be managed on a single cloud-based security platform.
Table of Contents

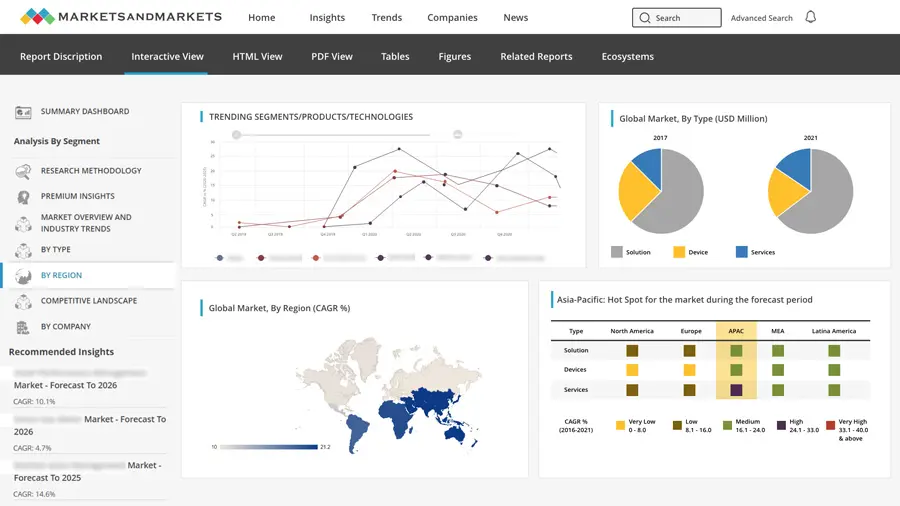
Methodology
The study involved significant activities in estimating the current market size for Perimeter Security. Intensive secondary research was conducted to collect information about perimeter security and related ecosystems. The industry executives validated these findings and assumptions and sized them across the value chain using a primary research process as a next step. Top-down and bottom-up market estimation approaches were used to estimate the market size globally, followed by the market breakup and data triangulation procedures to assess the market segment and sub-segments in perimeter security.
Secondary Research
Various sources were referred to in the secondary research process to identify and collect perimeter security information. These sources include annual reports, press releases, perimeter security software and service vendor investor presentations, forums, vendor-certified publications, and industry/association white papers. These secondary sources were utilized to obtain critical information about perimeter security’s solutions and services supply & value chain, a list of 100+ key players and SMEs, market classification, and segmentation per the industry trends and regional markets. The secondary research also gives us insights into the key developments from market and technology perspectives, which primary respondents further validated.
The factors considered for estimating the regional market size include technological initiatives undertaken by governments of different countries, GDP growth, ICT spending, recent market developments, and market ranking analysis of primary perimeter security solutions and service vendors.
Primary Research
We have conducted primary research with industry executives from both the supply and demand sides. The primary sources from the supply side include chief executive officers (CEOs), vice presidents (VPs), marketing directors, and technology and innovation executives of key companies operating in the perimeter security market. We have conducted primary interviews with the executives to obtain qualitative and quantitative information for perimeter security.
The market engineering process implemented the top-down and bottom-up approaches and various data triangulation methods to estimate and forecast the market segments and subsegments. During the post-market engineering process, we conducted primary research to verify and validate the critical numbers we arrived at. The primary analysis was also undertaken to identify the segmentation types, industry trends, the competitive landscape of the perimeter security market players, and fundamental market dynamics, such as drivers, restraints, opportunities, challenges, industry trends, and key strategies.
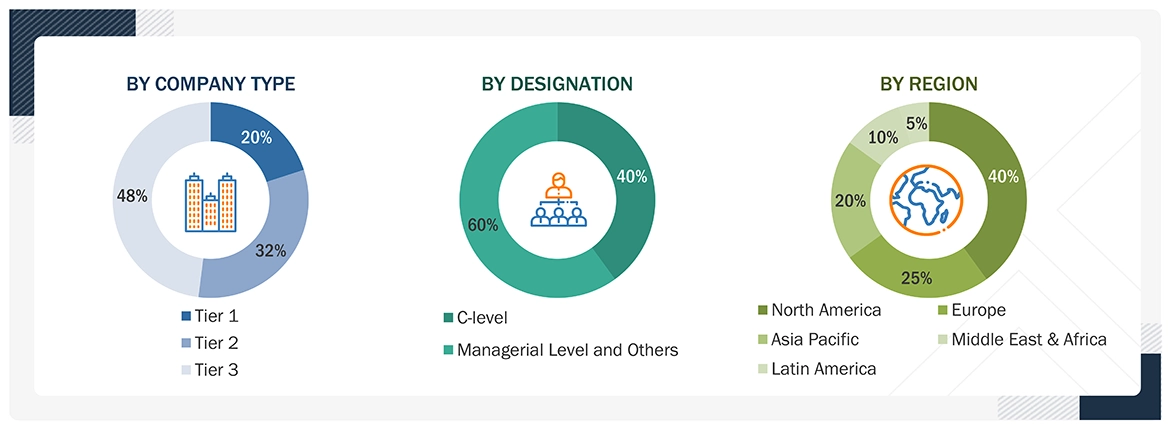
Following is the breakup of the primary research:
To know about the assumptions considered for the study, download the pdf brochure
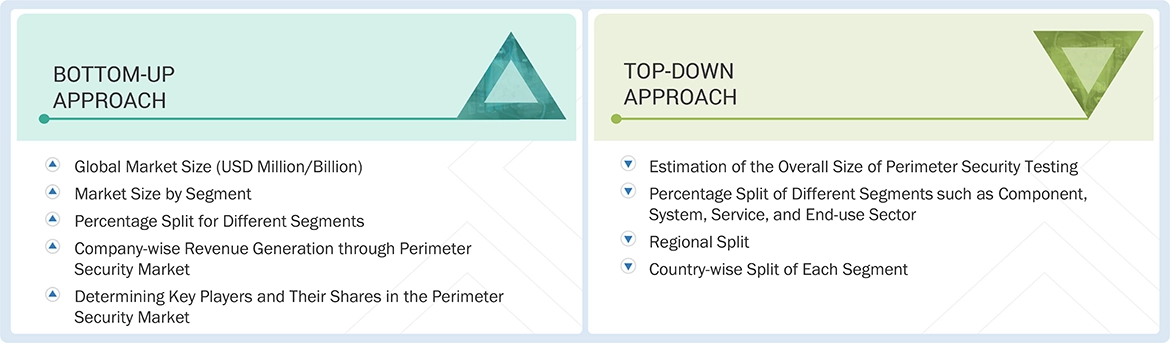
Market Size Estimation
Both top-down and bottom-up approaches were implemented for market size estimation to estimate, project, and forecast the size of the global and other dependent sub-segments in the overall perimeter security market.
The research methodology used to estimate the market size includes these steps:
- The key players, SMEs, and startups were identified through secondary sources. Their revenue contributions in the market were determined through primary and secondary sources.
- Annual and financial reports of the publicly listed market players were considered for the company’s revenue details, and,
- Primary interviews were also conducted with industry leaders to collect information about their companies, competitors, and key players in the market.
- All percentage splits, and breakups were determined using secondary sources and verified through primary sources.
Perimeter Security Market : Top-Down and Bottom-Up Approach
Data Triangulation
Data triangulation is a crucial step in the market engineering process for perimeter security. It involves utilizing multiple data sources and methodologies to validate and cross-reference findings, thereby enhancing the reliability and accuracy of the market segment and subsegment statistics. To conduct data triangulation, various factors and trends related to the perimeter security market are studied from both the demand and supply sides. It includes analyzing data from diverse sources such as market research reports, industry publications, regulatory bodies, financial institutions, and technology providers. By examining data from different perspectives and sources, data triangulation helps mitigate potential biases and discrepancies. It provides a more comprehensive understanding of the market dynamics, including the size, growth rate, market trends, and customer preferences.
Furthermore, data triangulation aids in identifying any inconsistencies or outliers in the data, enabling researchers to refine their analysis and make informed decisions. It strengthens the credibility of the market engineering process by ensuring the conclusions drawn are based on robust and corroborated data. Data triangulation is a rigorous and systematic approach to enhancing the reliability and validity of market segment and subsegment statistics in perimeter security. It provides a solid foundation for informed decision-making and strategic planning within the industry.
Market Definition
Perimeter security refers to the systems and measures implemented to protect an area or property by preventing unauthorized access and detecting intrusions across its boundaries. It is a form of security encompassing physical barriers such as fences, gates, walls, and technological systems, including video surveillance, intrusion detection sensors, access control, and alarms. These components safeguard critical infrastructures, commercial properties, residential areas, and governmental facilities from external threats. Perimeter security solutions are essential in identifying potential security breaches and enabling timely responses to protect people, property, and assets within a designated perimeter.
Key Stakeholders
- Government agencies
- Perimeter security vendors
- Independent software vendors
- Consulting firms
- System integrators
- Value-added resellers (VARs)
- Information technology (IT) security agencies
- Managed security service providers (MSSPs)
- Raw material/component suppliers
- Research organizations and consulting companies
- Government bodies, such as regulating authorities and policymakers
- Venture capitalists and private equity firms
Report Objectives
- To define, describe, and forecast the perimeter security market based on component, system, service, end-use sector, and region:
- To predict and estimate the market size of five central areas: North America, Europe, Asia Pacific, Middle East & Africa, and Latin America
- To analyze the subsegments of the market concerning individual growth trends, prospects, and contributions to the overall market
- To provide detailed information related to the primary factors (drivers, restraints, opportunities, and challenges) influencing the growth of the perimeter security market
- To analyze opportunities in the market for stakeholders by identifying high-growth segments of the market
- To profile the key players of the market and comprehensively analyze their market size and core competencies.
- Track and analyze competitive developments, such as new product launches, mergers and acquisitions, partnerships, agreements, and collaborations in the global perimeter security market.
Available customizations:
With the given market data, MarketsandMarkets offers customizations based on company-specific needs. The following customization options are available for the report:
Regional Analysis
- Further breakup of the Asia Pacific market into countries contributing 75% to the regional market size
- Further breakup of the North American market into countries contributing 75% to the regional market size
- Further breakup of the Latin American market into countries contributing 75% to the regional market size
- Further breakup of the Middle Eastern and African market into countries contributing 75% to the regional market size
- Further breakup of the European market into countries contributing 75% to the regional market size
Company Information
- Detailed analysis and profiling of additional market players (up to 5)
Need a Tailored Report?
Customize this report to your needs
Get 10% FREE Customization
Customize This ReportPersonalize This Research
- Triangulate with your Own Data
- Get Data as per your Format and Definition
- Gain a Deeper Dive on a Specific Application, Geography, Customer or Competitor
- Any level of Personalization
Let Us Help You
- What are the Known and Unknown Adjacencies Impacting the Perimeter Security M
- What will your New Revenue Sources be?
- Who will be your Top Customer; what will make them switch?
- Defend your Market Share or Win Competitors
- Get a Scorecard for Target Partners
Custom Market Research Services
We Will Customise The Research For You, In Case The Report Listed Above Does Not Meet With Your Requirements
Get 10% Free CustomisationTESTIMONIALS














Growth opportunities and latent adjacency in Perimeter Security M